Australian financial services company, Latitude Financial, has suffered a large-scale data break that exposed the personal information for more than 14 million customers. The breach was...
Day: April 1, 2023
Twitter source code leaked via GitHub
Part of the source code for social media site Twitter has been leaked via source code repository GitHub, according to a DMCA takedown request. The DMCA...
IOTW: BreachForums shuts down after FBI arrests its top admin
Notorious dark web hacking forum BreachForums is reportedly shutting down following the arrest of one of its top administrators by the United States’ Federal Bureau of...
Top seven hacks and cyber security threats in APAC
In 2022, 59 percent of business in the Asia-Pacific region reported being the victim of a cyber attack, 32 percent reported being the victim of multiple...
What is phishing?
Phishing is a social engineering tactic that sees hackers attempt to gain access to personal or confidential information by posing as a legitimate company. In this...
IOTW: Ransomware gang allegedly hacks Ring doorbells
Russia-linked ransomware gang ALPHV has claimed to have launched a cyber attack against Amazon-owned domestic security company, Ring. Ring, which makes doorbells with video and sound...
What are DDoS attacks?
Distributed denial of service attacks, or DDoS attacks, see malicious actors attempt to disrupt a site by overwhelming its infrastructure with a large amount of internet...
IOTW: US Marshals Service suffers ransomware attack
The US Marshals Service (USMS), a federal law enforcement agency within the US Department of Justice (DoJ) has announced that it was the victim of a...
IOTW: Russian hackers target NATO sites with DDoS attack
The North Atlantic Treaty Organization (NATO) has been the victim of a series of distributed denial of service (DDoS) attacks, causing temporary disruption to some of...
Why healthcare providers are focusing on cyber resilience
The healthcare industry, especially within the Asia-Pacific region, has been the victim of a number of cyber attacks and data breaches within the last six months...
How Covid-19 impacted cyber security challenges, focus and spends
Survey methodology and respondent profiles The results in this report are from the Cyber Security Hub survey which we fielded to subscribers from May and June...
German airports hit with DDoS attack
Seven German airports have had their websites targeted by a suspected distributed denial of service (DDoS) attack. The attack, which took place on February 16, saw...
Microsoft Fixes New Azure AD Vulnerability Impacting Bing Search and Major Apps
Microsoft Fixes New Azure AD Vulnerability Impacting Bing Search and Major AppsMicrosoft has patched a misconfiguration issue impacting the Azure Active Directory (AAD) identity and access...
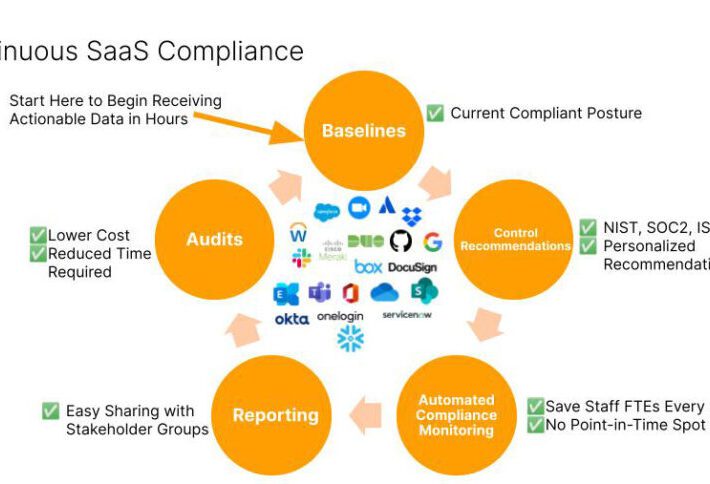
Reducing Risks and Threats with Continuous SaaS Compliance
Reducing Risks and Threats with Continuous SaaS ComplianceCISOs and GRC officers are quickly recognizing the growing threats posed by misconfigured SaaS applications and integrations between SaaS...
3CX Supply Chain Attack Campaign
3CX Supply Chain Attack CampaignOn March 29th 2023, CrowdStrike published a blog outlining a supply chain attack leveraging the 3CXDesktopApp - a softphone application from 3CX....
What is the impact of AI on cyber security awareness?
What is the impact of AI on cyber security awareness?The post What is the impact of AI on cyber security awareness? appeared first on Click Armor....
Avoiding data backup failures – Week in security with Tony Anscombe
Avoiding data backup failures – Week in security with Tony AnscombeToday is World Backup Day, but maybe we also need a "did you test your backups"...
DISH slapped with multiple lawsuits after ransomware cyber attack
DISH slapped with multiple lawsuits after ransomware cyber attackDish Network has been slapped with multiple class action lawsuits after it suffered a ransomware incident that was behind...
Fake ransomware gang targets U.S. orgs with empty data leak threats
Fake ransomware gang targets U.S. orgs with empty data leak threatsFake extortionists are piggybacking on data breaches and ransomware incidents, threatening U.S. companies with publishing or...
3CX Supply Chain Attack — Here’s What We Know So Far
3CX Supply Chain Attack — Here's What We Know So FarEnterprise communications software maker 3CX on Thursday confirmed that multiple versions of its desktop app for...
Deep Dive Into 6 Key Steps to Accelerate Your Incident Response
Deep Dive Into 6 Key Steps to Accelerate Your Incident ResponseOrganizations rely on Incident response to ensure they are immediately aware of security incidents, allowing for quick action...
Cyber Police of Ukraine Busted Phishing Gang Responsible for $4.33 Million Scam
Cyber Police of Ukraine Busted Phishing Gang Responsible for $4.33 Million ScamThe Cyber Police of Ukraine, in collaboration with law enforcement officials from Czechia, has arrested...
Winter Vivern APT Targets European Government Entities with Zimbra Vulnerability
Winter Vivern APT Targets European Government Entities with Zimbra VulnerabilityThe advanced persistent threat (APT) actor known as Winter Vivern is now targeting officials in Europe and...
Hackers Exploiting WordPress Elementor Pro Vulnerability: Millions of Sites at Risk!
Hackers Exploiting WordPress Elementor Pro Vulnerability: Millions of Sites at Risk!Unknown threat actors are actively exploiting a recently patched security vulnerability in the Elementor Pro website...
Cacti, Realtek, and IBM Aspera Faspex Vulnerabilities Under Active Exploitation
Cacti, Realtek, and IBM Aspera Faspex Vulnerabilities Under Active ExploitationCritical security flaws in Cacti, Realtek, and IBM Aspera Faspex are being exploited by various threat actors...
World Backup Day is here again – 5 tips to keep your precious data safe
World Backup Day is here again – 5 tips to keep your precious data safeThe only backup you will ever regret is the one you didn't...
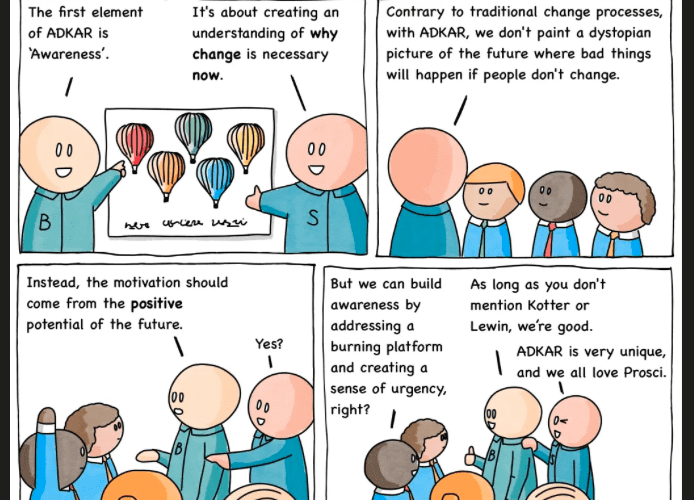
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnarav – #233 — Burning Platform
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnarav – #233 — Burning Platform via the respected Software Engineering expertise of Mikkel Noe-Nygaard as well as the lauded...
Post-Conference Tech Spec: Why Building Your Ship (Application) with Raw Materials is a Bad Idea
Post-Conference Tech Spec: Why Building Your Ship (Application) with Raw Materials is a Bad Idea The post Post-Conference Tech Spec: Why Building Your Ship (Application)...
Challenges of Securing the Modern Workforce
Challenges of Securing the Modern WorkforceAs the world continues to evolve and adopt new technologies, the modern workforce has changed significantly, and so have the opportunities...
German Police Raid DDoS-Friendly Host ‘FlyHosting’
German Police Raid DDoS-Friendly Host ‘FlyHosting’Authorities in Germany this week seized Internet servers that powered FlyHosting, a dark web service that catered to cybercriminals operating DDoS-for-hire...