Army of pro-Trump bots attack 2024 rivals and manipulate informationThousands of Twitter accounts post stream of praise for former president and ridicule his critics, including Haley...
Month: March 2023
Minimizing Privacy Risk From Web Tracking Technologies
Minimizing Privacy Risk From Web Tracking Technologies7 Tips to Reduce Risk to Patients, Beneficiaries and the OrganizationAs healthcare becomes increasingly interconnected, web tracking is easy to...
Fake Emails From Russian Duo Lead to Propaganda Videos
Fake Emails From Russian Duo Lead to Propaganda VideosVovan and Lexus Pose as Ukrainian Officials to Play Pranks on Kremlin CriticsA Russian threat actor headed by...
SYS01stealer: Nueva amenaza que utiliza anuncios de Facebook para apuntar a empresas de infraestructura crítica
SYS01stealer: Nueva amenaza que utiliza anuncios de Facebook para apuntar a empresas de infraestructura críticaLos investigadores de seguridad cibernética han descubierto un nuevo ladrón de información...
U.S. Cybersecurity Agency Raises Alarm Over Royal Ransomware’s Deadly Capabilities
U.S. Cybersecurity Agency Raises Alarm Over Royal Ransomware's Deadly CapabilitiesThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) has released a new advisory about Royal ransomware, which emerged in the...
DoppelPaymer ransomware supsects arrested in Germany and Ukraine
DoppelPaymer ransomware supsects arrested in Germany and UkraineDevices seized, suspects interrogated and arrested, allegedly connected to devastating cyberattack on University Hospital in Düsseldorf.Read MoreNaked SecurityDevices seized,...
USENIX Security ’22 – Fangming Gu, Qingli Guo, Lian Li, Zhiniang Peng, Wei Lin, Xiaobo Yang, Xiaorui Gong – ‘COMRace: Detecting Data Race Vulnerabilities in COM Objects’
USENIX Security ’22 – Fangming Gu, Qingli Guo, Lian Li, Zhiniang Peng, Wei Lin, Xiaobo Yang, Xiaorui Gong – ‘COMRace: Detecting Data Race Vulnerabilities in COM...
Building smarter DevSecOps with Intelligent Orchestration
Building smarter DevSecOps with Intelligent Orchestration Intelligent Orchestration takes the complexity out of DevSecOps by delivering the right tests, at the right time, to the right...
Private Malware for Sale: A Closer Look at AresLoader
Private Malware for Sale: A Closer Look at AresLoaderIn December 2022, a private loader named "AresLoader" was advertised for sale on the top-tier Russian-language hacking forum...
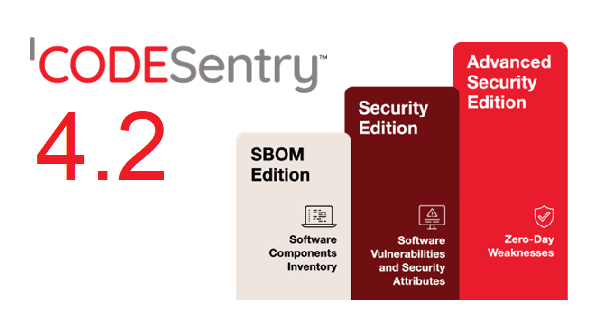
Announcing CodeSentry 4.2 with New Editions and Component Search
Announcing CodeSentry 4.2 with New Editions and Component Search GrammaTech’s leading binary Software Composition Technology (SCA) solution, CodeSentry, provides valuable insights to open-source software (OSS) components...
New Report “State of Cloud Threat Detection and Response”
New Report “State of Cloud Threat Detection and Response”Cloud D&R Report (2023) One of the mysteries of detection and response (D&R) is about how companies really approach...
Your Guide to Secure Code Signing: Four Steps to Get Started
Your Guide to Secure Code Signing: Four Steps to Get StartedWithout code signing – or checks within the software download to confirm code signatures – users...
#LifeAtLogRhythm Spotlight – Diversity, Equity, and Inclusion (DEI) Collective
#LifeAtLogRhythm Spotlight – Diversity, Equity, and Inclusion (DEI) CollectiveIt’s time for round two of our blog posts highlighting #LifeAtLogRhythm! This month, we are spotlighting a group...
Shared Responsibility Model: What It Means for Cloud Security
Shared Responsibility Model: What It Means for Cloud SecurityThe shared responsibility model is a cloud security framework that defines how responsibilities are divided between cloud service...
Marriott Hosts “I love Hitler” Rally in Washington DC
Marriott Hosts “I love Hitler” Rally in Washington DCMarriott has a long and sordid history of promoting hate groups by giving them a platform. 2023 is...
At least one open source vulnerability found in 84% of code bases: Report
At least one open source vulnerability found in 84% of code bases: ReportAt a time when almost all software contains open source code, at least one...
Companies urged to patch critical vulnerability in Fortinet FortiNAC
Companies urged to patch critical vulnerability in Fortinet FortiNACProof-of-concept exploit code is now available for a critical vulnerability in Fortinet FortiNAC appliances and attackers have already...
PayPal sued for negligence in data breach that affected 35,000 users
PayPal sued for negligence in data breach that affected 35,000 usersA pending class action lawsuit accuses online payments giant PayPal of failing to adequately safeguard the...
Ransom House ransomware attack hit Hospital Clinic de Barcelona
Ransom House ransomware attack hit Hospital Clinic de BarcelonaHospital Clinic de Barcelona, one of the main hospitals in the Spanish city, suffered a cyber attack that...
New National Cybersecurity Strategy: resilience, regs, collaboration and pain (for attackers)
New National Cybersecurity Strategy: resilience, regs, collaboration and pain (for attackers)The Biden administration’s National Cybersecurity Strategy aims to go after attackers, cultivate a resilience-first defensive posture...
This 18-course ethical hacking bundle is under $50
This 18-course ethical hacking bundle is under $50Ethical hacking is a great skill to learn with new cyber threats on the rise. Learn how to fight...
New malware infects business routers for data theft, surveillance
New malware infects business routers for data theft, surveillanceAn ongoing hacking campaign called 'Hiatus' targets DrayTek Vigor router models 2960 and 3900 to steal data from...
Sandbox blockchain game breached to send emails linking to malware
Sandbox blockchain game breached to send emails linking to malwareThe Sandbox blockchain game is warnings its community that a security incident caused some users to receive...
Microsoft: New Windows Canary channel has most cutting-edge features
Microsoft: New Windows Canary channel has most cutting-edge featuresMicrosoft is adding a new Canary channel to its nine-year-old Windows Insider Program to let the most fearless...
Proof-of-Concept released for critical Microsoft Word RCE bug
Proof-of-Concept released for critical Microsoft Word RCE bugA proof-of-concept for CVE-2023-21716, a critical vulnerability in Microsoft Word that allows remote code execution, has been published over...
Outlook for Mac now free, Microsoft 365 subscription not needed
Outlook for Mac now free, Microsoft 365 subscription not neededMicrosoft says its Outlook for Mac email and calendar client is now available for free, and it...
Old Windows ‘Mock Folders’ UAC bypass used to drop malware
Old Windows ‘Mock Folders’ UAC bypass used to drop malwareA new phishing campaign targets organizations in Eastern European countries with the Remcos RAT malware with aid...
Nvidia working on driver fix for Windows BSOD, high CPU usage
Nvidia working on driver fix for Windows BSOD, high CPU usageNvidia confirmed today that it's working to fix a driver issue causing high CPU usage and...
CISA red-teamed a ‘large critical infrastructure’ organization, no one noticed
CISA red-teamed a ‘large critical infrastructure’ organization, no one noticedEXECUTIVE SUMMARY: In recent years, protecting critical infrastructure entities has been synonymous with ensuring the continued operations...
The evolving sophistication of social engineering attacks
The evolving sophistication of social engineering attacksBy Anas Baig, product manager and cyber security expert with Securiti. A social engineering attack is a type of cyber...