Outlook app to get built-in Microsoft 365 MFA on Android, iOSMicrosoft will soon fast-track multi-factor authentication (MFA) adoption for its Microsoft 365 cloud productivity platform by...
Month: March 2023
CISA now warns critical infrastructure of ransomware-vulnerable devices
CISA now warns critical infrastructure of ransomware-vulnerable devicesToday, the U.S. Cybersecurity & Infrastructure Security Agency (CISA) announced a new pilot program designed to help critical infrastructure entities...
Kali Linux 2023.1 introduces ‘Purple’ distro for defensive security
Kali Linux 2023.1 introduces 'Purple' distro for defensive securityOffensive Security has released Kali Linux 2023.1, the first version of 2023 and the project's 10th anniversary, with...
LA housing authority discloses data breach after ransomware attack
LA housing authority discloses data breach after ransomware attackThe Housing Authority of the City of Los Angeles (HACLA) is warning of a "data security event" after...
Fortinet: New FortiOS bug used as zero-day to attack govt networks
Fortinet: New FortiOS bug used as zero-day to attack govt networksUnknown attackers used zero-day exploits to abuse a new FortiOS bug patched this month in attacks...
NordVPN makes its Meshnet private tunnel free for everyone
NordVPN makes its Meshnet private tunnel free for everyoneNordVPN's Meshnet private tunnel feature for Windows, macOS, and Linux is now free for everyone, even users who...
The 2 biggest regulatory challenges for the internet of “any” thing (IoT)
The 2 biggest regulatory challenges for the internet of “any” thing (IoT)By Antoinette Hodes, a Check Point Global Solutions Architect for the EMEA region and an...
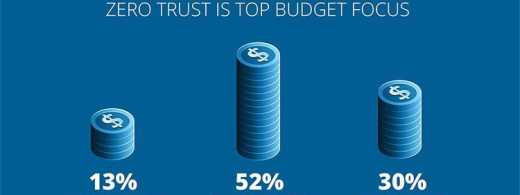
A shocking truth: One in five government employees, indifferent to workplace hacks
A shocking truth: One in five government employees, indifferent to workplace hacksEXECUTIVE SUMMARY: Around the globe, cyber risks are intensifying. Responding to these growing challenges requires...
GUEST ESSAY: Could CISOs be on the verge of disproving the ‘security-as-a-cost-center’ fallacy?
GUEST ESSAY: Could CISOs be on the verge of disproving the ‘security-as-a-cost-center’ fallacy?This year has kicked off with a string of high-profile layoffs — particularly in...
Ukraine Tracks Increased Russian Focus on Cyberespionage
Ukraine Tracks Increased Russian Focus on CyberespionageMilitary Stalemate Has Driven Moscow to Also Pursue Data Theft, Psychological OpsAs Russia's full-scale invasion of Ukraine last year stalled,...
North Korean Hackers Find Value in LinkedIn
North Korean Hackers Find Value in LinkedInGroup Lures Victims Into Opening Phishing Payload Disguised as Job-Related InfoBusiness social media platform LinkedIn continues to pay dividends for...
Heart Device Maker Says Hack Affected 1 Million Patients
Heart Device Maker Says Hack Affected 1 Million PatientsPHI of Former and Current Patients Using Wearable Cardiac Defibrillator CompromisedEmergency medical device provider Zoll Medical Corp. is...
Dark Pink APT Group ‘Very Likely’ Back in Action
Dark Pink APT Group 'Very Likely' Back in ActionRecently-Emerged Threat Actor Focuses on Asia PacificCybersecurity researchers say they've almost certainly spotted traces of the recently-emerged advanced...
Acer sufre una brecha de datos que se ponen a la venta
Acer sufre una brecha de datos que se ponen a la ventaAcer, el fabricante de productos electrónicos y gigante informático con sede en Taiwán, confirmó recientemente...
Hacker Steals $200 Million From Euler Finance
Hacker Steals $200 Million From Euler FinanceThief Off-Ramps Some Funds to Tornado Cash; DeFi Firm Probes IncidentHackers are draining millions of dollars from decentralized finance protocol...
SVB Dominoes Fall: HSBC Buys UK Arm, Feds Grab Canadian Arm
SVB Dominoes Fall: HSBC Buys UK Arm, Feds Grab Canadian ArmFirst Republic Bank Stock Nosedives After Accessing Liquidity from Federal ReserveEurope's largest bank acquired the United...
Advertencia: tutoriales en video de YouTube generados por IA propagan software malicioso
Advertencia: tutoriales en video de YouTube generados por IA propagan software maliciosoSe ha observado cada vez más que los actores de amenazas usan videos de YouTube...
New FiXS ATM Malware Targeting Mexican Banks
New FiXS ATM Malware Targeting Mexican BanksA new ATM malware strain dubbed FiXS has been observed targeting Mexican banks since the start of February 2023. "The ATM malware...
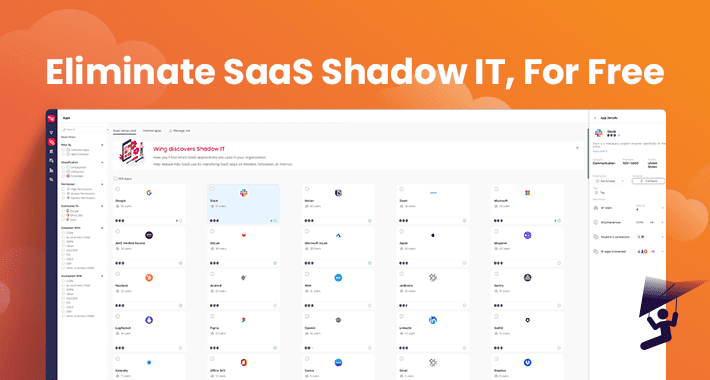
Security and IT Teams No Longer Need To Pay For SaaS-Shadow IT Discovery
Security and IT Teams No Longer Need To Pay For SaaS-Shadow IT DiscoveryThis past January, a SaaS Security Posture Management (SSPM) company named Wing Security (Wing)...
Experts Reveal Google Cloud Platform’s Blind Spot for Data Exfiltration Attacks
Experts Reveal Google Cloud Platform's Blind Spot for Data Exfiltration AttacksMalicious actors can take advantage of "insufficient" forensic visibility into Google Cloud Platform (GCP) to exfiltrate...
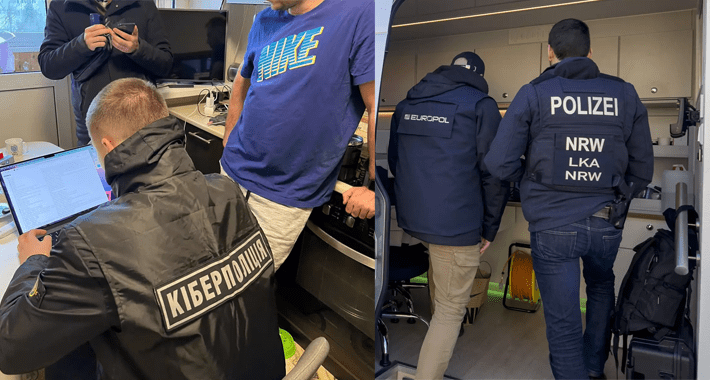
Core Members of DoppelPaymer Ransomware Gang Targeted in Germany and Ukraine
Core Members of DoppelPaymer Ransomware Gang Targeted in Germany and UkraineLaw enforcement authorities from Germany and Ukraine have targeted suspected core members of a cybercrime group...
From Disinformation to Deep Fakes: How Threat Actors Manipulate Reality
From Disinformation to Deep Fakes: How Threat Actors Manipulate RealityDeep fakes are expected to become a more prominent attack vector. Here's how to identify them. What...
Almost Bare Bones WebR Starter App
Almost Bare Bones WebR Starter AppLet’s walk through how to set up a ~minimal HTML/JS/CS + WebR-powered “app” on a server you own. This will be...
Hyperview Appoints Digital Infrastructure Leader Bill Kleyman to Advisory Board
Hyperview Appoints Digital Infrastructure Leader Bill Kleyman to Advisory BoardAward-winning data center, cloud, and digital infrastructure leader, Bill Kleyman is announced to Hyperview advisory board Vancouver,...
Unveiling the Shadow AI: The Rise of AI Reliance in Cybersecurity
Unveiling the Shadow AI: The Rise of AI Reliance in CybersecurityArtificial Intelligence (AI) has been touted as the future of cybersecurity, and rightly so. With the...
Top Changes in the OWASP API Security Top 10 2023RC
Top Changes in the OWASP API Security Top 10 2023RCThe OWASP API project has recently decided to refresh the popular API Security Top 10 threat map....
Best and worst data breach responses highlight the do’s and don’ts of IR
Best and worst data breach responses highlight the do's and don'ts of IRIn theory, enterprises should not only have security measures in place to prevent a...
Unpatched old vulnerabilities continue to be exploited: Report
Unpatched old vulnerabilities continue to be exploited: ReportKnown vulnerabilities as old as 2017 are still being successfully exploited in wide-ranging attacks as organizations fail to patch...
Microsoft Intune Suite consolidates endpoint management and protection
Microsoft Intune Suite consolidates endpoint management and protectionIntune Suite will streamline endpoint management with added features for controlled and secure access.Read MoreCSO OnlineIntune Suite will streamline...
Security Affairs newsletter Round 410 by Pierluigi Paganini
Security Affairs newsletter Round 410 by Pierluigi PaganiniA new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are...