Running WordPress on Azure for secure, fast and global content deliveryLearn about Microsoft's WordPress on Azure App Service, as well as an interesting alternative from WP...
Month: March 2023
Google Pixel flaw allowed recovery of redacted, cropped images
Google Pixel flaw allowed recovery of redacted, cropped imagesAn 'Acropalypse' flaw in Google Pixel's Markup tool made it possible to partially recover edited or redacted screenshots...
Hackers mostly targeted Microsoft, Google, Apple zero-days in 2022
Hackers mostly targeted Microsoft, Google, Apple zero-days in 2022Hackers continue to target zero-day vulnerabilities in malicious campaigns, with researchers reporting that 55 zero-days were actively exploited...
Is your organization among the 1 in 10 with malware traffic? DNS data reveals scary truth
Is your organization among the 1 in 10 with malware traffic? DNS data reveals scary truthEXECUTIVE SUMMARY: In a new report, cyber security researchers have highlighted...
GUEST ESSAY: Scammers leverage social media, clever con games to carry out digital exploitation
GUEST ESSAY: Scammers leverage social media, clever con games to carry out digital exploitationOne common misconception is that scammers usually possess a strong command of computer...
How an AI voice clone fooled Centrelink – video
How an AI voice clone fooled Centrelink – videoAn investigation by Guardian Australia has found that AI technology is able to fool a voice identification system...
Is Your Identity Management Comprehensive Enough? Are You Just Tipping Your Toes?
Is Your Identity Management Comprehensive Enough? Are You Just Tipping Your Toes?Post ContentRead MoreDataBreachToday.com RSS Syndication
Impact of Technology Deployments on Privacy: Striking the Right Balance
Impact of Technology Deployments on Privacy: Striking the Right BalancePost ContentRead MoreDataBreachToday.com RSS Syndication
Future of Cybersecurity: Threats and Opportunities
Future of Cybersecurity: Threats and OpportunitiesPost ContentRead MoreDataBreachToday.com RSS Syndication
It’s Raining Zero-Days in Cyberspace
It's Raining Zero-Days in CyberspaceChinese Hackers and Others Increasingly Favor Unpatched VulnerabilitiesLast year was another bonanza in zero-days for Chinese state hackers, say security researchers in...
Roseville, Calif., CIO Brings Global Background to Local Gov
Roseville, Calif., CIO Brings Global Background to Local GovHong Sae is the CIO for the city of Roseville, Calif., and he has a tremendous track record...
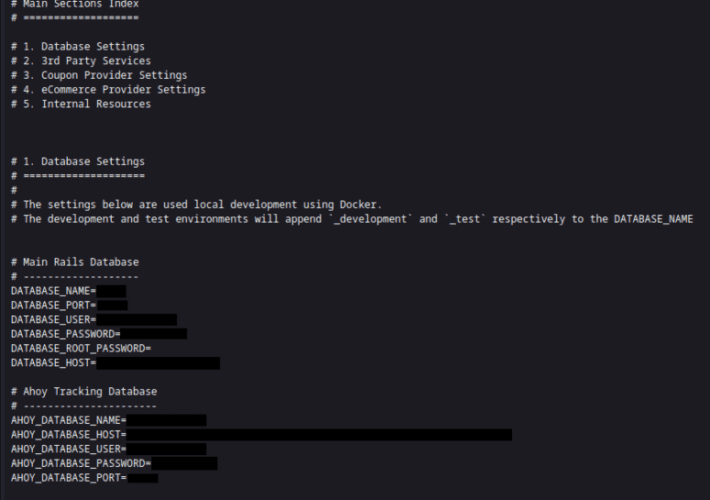
Lowe’s Market chain leaves client data up for grabs
Lowe’s Market chain leaves client data up for grabsA misconfiguration on a website owned by the US-based Lowe’s Market grocery store chain could have allowed threat...
Security Affairs newsletter Round 411 by Pierluigi Paganini
Security Affairs newsletter Round 411 by Pierluigi PaganiniA new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are...
New ‘HinataBot’ botnet could launch massive 3.3 Tbps DDoS attacks
New ‘HinataBot’ botnet could launch massive 3.3 Tbps DDoS attacksA new malware botnet was discovered targeting Realtek SDK, Huawei routers, and Hadoop YARN servers to recruit...
Cybersecurity funds should go towards beefing up Centrelink voice authentication, Greens say
Cybersecurity funds should go towards beefing up Centrelink voice authentication, Greens sayDavid Shoebridge says some of the $10bn allocated to Redspice program should counter misuse of...
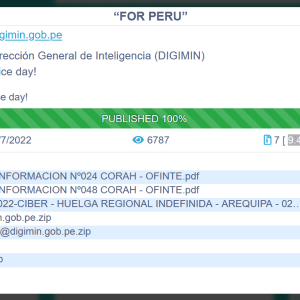
Who Wants to Fuel Independent and High Quality OSINT/Cybercrime and Threat Intelligence Research? Accepting BitCoin Donations
Who Wants to Fuel Independent and High Quality OSINT/Cybercrime and Threat Intelligence Research? Accepting BitCoin Donations Dear blog readers, Did you already grab a copy of...
URGENT ACTION RECOMMENDED – Microsoft Outlook Vulnerability (CVE-2023-23397)
URGENT ACTION RECOMMENDED – Microsoft Outlook Vulnerability (CVE-2023-23397)Summary: Microsoft disclosed a Microsoft Outlook Vulnerability (an RCE – remote code execution) titled “Microsoft Outlook Elevation of Privilege...
COURT DOC: US Federal Agents Arrest Alleged Administrator of Breach Forums “pompompurin”
COURT DOC: US Federal Agents Arrest Alleged Administrator of Breach Forums “pompompurin”On March 17, 2023, US federal agents arrested a New York individual for computer crimes...
What’s New in Cyolo 4.0
What’s New in Cyolo 4.0 2 min read Cyolo 4.0 has officially arrived! Discover all the details of this latest release, including (spoiler alert!) a simplified...
USENIX Security ’22 – Mohsen Minaei, Mainack Mondal, Aniket Kate – ‘Empirical Understanding Of Deletion Privacy: Experiences, Expectations, And Measures’
USENIX Security ’22 – Mohsen Minaei, Mainack Mondal, Aniket Kate – ‘Empirical Understanding Of Deletion Privacy: Experiences, Expectations, And Measures’Our thanks to USENIX for publishing their...
NBA is warning fans of a data breach after a third-party newsletter service hack
NBA is warning fans of a data breach after a third-party newsletter service hackThe NBA (National Basketball Association) disclosed a data breach after a third-party firm...
USENIX Security ’22 – David G. Balash, Xiaoyuan Wu, Miles Grant, Irwin Reyes, Adam J. Aviv – ‘Security And Privacy Perceptions Of Third-Party Application Access For Google Accounts’
USENIX Security ’22 – David G. Balash, Xiaoyuan Wu, Miles Grant, Irwin Reyes, Adam J. Aviv – ‘Security And Privacy Perceptions Of Third-Party Application Access For...
No More Missed Opportunities: Maximizing Your Threat Hunting Efforts
No More Missed Opportunities: Maximizing Your Threat Hunting EffortsThreat hunting has become an essential component of modern cybersecurity defenses. With the threat landscape constantly evolving, organizations...
Kaspersky released a new decryptor for Conti-based ransomware
Kaspersky released a new decryptor for Conti-based ransomwareKaspersky released a new version of the decryptor for the Conti ransomware that is based on the previously leaked...
Solving The AppSec Dilemma Across the Entire SDLC
Solving The AppSec Dilemma Across the Entire SDLCWhy organizations should adopt an integrated and continuous approach to application security education By Amy Baker, Security Education Evangelist,...
The Biggest Cyber Threats For The Financial Industry In 2023
The Biggest Cyber Threats For The Financial Industry In 2023By Ben Herzberg, Chief Scientist of Satori According to external market data, the financial sector was the...
The California Consumer Privacy Act (CCPA) and the American Data Privacy Protection Act: The Good, The Bad and The Ugly
The California Consumer Privacy Act (CCPA) and the American Data Privacy Protection Act: The Good, The Bad and The UglyBy Dr. Eric Cole, Advisor – Theon...
“The Impact of Mobile Threats on SMBs: 10 Simple Ways to Empower Your Company.”
“The Impact of Mobile Threats on SMBs: 10 Simple Ways to Empower Your Company.”By Wendy Taccetta, SVP, Small and Medium Business for Verizon Business The shift...
Emotet malware now distributed in Microsoft OneNote files to evade defenses
Emotet malware now distributed in Microsoft OneNote files to evade defensesThe Emotet malware is now distributed using Microsoft OneNote email attachments, aiming to bypass Microsoft security...
Hitachi Energy Latest Victim of Clop GoAnywhere Attacks
Hitachi Energy Latest Victim of Clop GoAnywhere AttacksAttackers Exploit Zero-Day Vulnerability in Fortra's Managed File Transfer SoftwareHitachi Energy joined the ranks of victims hit by the...