NAPLISTENER: New Malware in REF2924 Group's Arsenal for Bypassing DetectionThe threat group tracked as REF2924 has been observed deploying previously unseen malware in its attacks aimed at entities...
Month: March 2023
Rogue NuGet Packages Infect .NET Developers with Crypto-Stealing Malware
Rogue NuGet Packages Infect .NET Developers with Crypto-Stealing MalwareThe NuGet repository is the target of a new "sophisticated and highly-malicious attack" aiming to infect .NET developer systems with...
Preventing Insider Threats in Your Active Directory
Preventing Insider Threats in Your Active DirectoryActive Directory (AD) is a powerful authentication and directory service used by organizations worldwide. With this ubiquity and power comes...
ScarCruft’s Evolving Arsenal: Researchers Reveal New Malware Distribution Techniques
ScarCruft's Evolving Arsenal: Researchers Reveal New Malware Distribution TechniquesThe North Korean advanced persistent threat (APT) actor dubbed ScarCruft is using weaponized Microsoft Compiled HTML Help (CHM)...
CISA Alerts on Critical Security Vulnerabilities in Industrial Control Systems
CISA Alerts on Critical Security Vulnerabilities in Industrial Control SystemsThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) has released eight Industrial Control Systems (ICS) advisories on Tuesday, warning...
German and South Korean Agencies Warn of Kimsuky’s Expanding Cyber Attack Tactics
German and South Korean Agencies Warn of Kimsuky's Expanding Cyber Attack TacticsGerman and South Korean government agencies have warned about cyber attacks mounted by a threat...
Operation Soft Cell: Chinese Hackers Breach Middle East Telecom Providers
Operation Soft Cell: Chinese Hackers Breach Middle East Telecom ProvidersTelecommunication providers in the Middle East are the subject of new cyber attacks that commenced in the...
2023 Cybersecurity Maturity Report Reveals Organizational Unpreparedness for Cyberattacks
2023 Cybersecurity Maturity Report Reveals Organizational Unpreparedness for CyberattacksIn 2022 alone, global cyberattacks increased by 38%, resulting in substantial business loss, including financial and reputational damage....
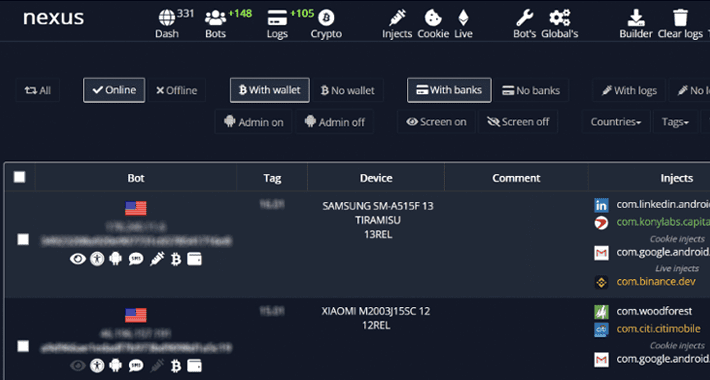
Nexus: A New Rising Android Banking Trojan Targeting 450 Financial Apps
Nexus: A New Rising Android Banking Trojan Targeting 450 Financial AppsAn emerging Android banking trojan dubbed Nexus has already been adopted by several threat actors to target 450...
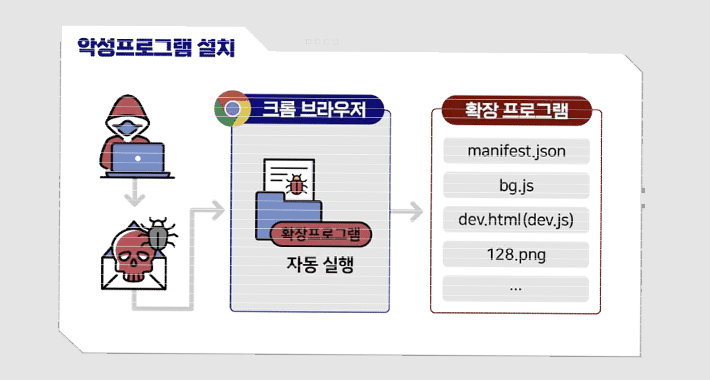
Fake ChatGPT Chrome Browser Extension Caught Hijacking Facebook Accounts
Fake ChatGPT Chrome Browser Extension Caught Hijacking Facebook AccountsGoogle has stepped in to remove a bogus Chrome browser extension from the official Web Store that masqueraded...
Critical WooCommerce Payments Plugin Flaw Patched for 500,000+ WordPress Sites
Critical WooCommerce Payments Plugin Flaw Patched for 500,000+ WordPress SitesPatches have been released for a critical security flaw impacting the WooCommerce Payments plugin for WordPress, which...
Researchers Uncover Chinese Nation State Hackers’ Deceptive Attack Strategies
Researchers Uncover Chinese Nation State Hackers' Deceptive Attack StrategiesA recent campaign undertaken by Earth Preta indicates that nation-state groups aligned with China are getting increasingly proficient at bypassing...
GitHub Swiftly Replaces Exposed RSA SSH Key to Protect Git Operations
GitHub Swiftly Replaces Exposed RSA SSH Key to Protect Git OperationsCloud-based repository hosting service GitHub said it took the step of replacing its RSA SSH host...
THN Webinar: Inside the High Risk of 3rd-Party SaaS Apps
THN Webinar: Inside the High Risk of 3rd-Party SaaS AppsAny app that can improve business operations is quickly added to the SaaS stack. However, employees don't...
Malicious Python Package Uses Unicode Trickery to Evade Detection and Steal Data
Malicious Python Package Uses Unicode Trickery to Evade Detection and Steal DataA malicious Python package on the Python Package Index (PyPI) repository has been found to...
OpenAI Reveals Redis Bug Behind ChatGPT User Data Exposure Incident
OpenAI Reveals Redis Bug Behind ChatGPT User Data Exposure IncidentOpenAI on Friday disclosed that a bug in the Redis open source library was responsible for the...
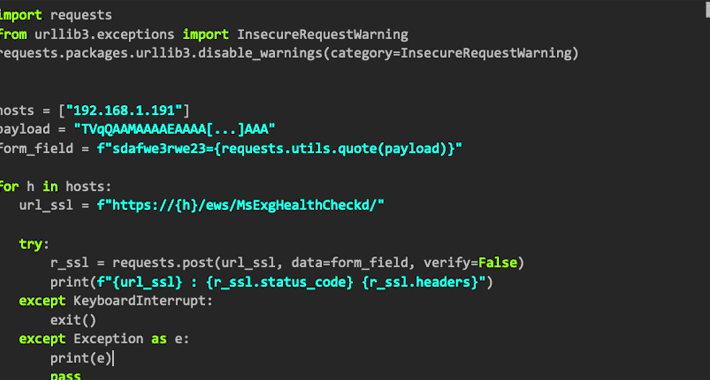
Microsoft Warns of Stealthy Outlook Vulnerability Exploited by Russian Hackers
Microsoft Warns of Stealthy Outlook Vulnerability Exploited by Russian HackersMicrosoft on Friday shared guidance to help customers discover indicators of compromise (IoCs) associated with a recently...
U.K. National Crime Agency Sets Up Fake DDoS-For-Hire Sites to Catch Cybercriminals
U.K. National Crime Agency Sets Up Fake DDoS-For-Hire Sites to Catch CybercriminalsIn what's a case of setting a thief to catch a thief, the U.K. National...
Windows 11 also vulnerable to “aCropalypse” image data leakage
Windows 11 also vulnerable to “aCropalypse” image data leakageTurns out that the Windows 11 Snipping Tool has the same "aCropalypse" data leakage bug as Pixel phones....
Google Pixel phones had a serious data leakage bug – here’s what to do!
Google Pixel phones had a serious data leakage bug – here’s what to do!What if the "safe" images you shared after carefully cropping them... had some...
WooCommerce Payments plugin for WordPress has an admin-level hole – patch now!
WooCommerce Payments plugin for WordPress has an admin-level hole – patch now!Admin-level holes in websites are always a bad thing... and for "bad", read "worse" if...
S3 Ep127: When you chop someone out of a photo, but there they are anyway…
S3 Ep127: When you chop someone out of a photo, but there they are anyway…Listen now - latest episode. Full transcript inside.Read MoreNaked SecurityListen now -...
Randall Munroe’s XKCD ‘Air Handler’
Randall Munroe’s XKCD ‘Air Handler’ via the comic artistry and dry wit of Randall Munroe, resident at XKCD! Permalink The post Randall Munroe’s XKCD ‘Air Handler’...
The Power of Open-Source Security: A Deep Dive
The Power of Open-Source Security: A Deep DiveOpen-source software (OSS) is increasingly becoming foundational to security strategies for cutting-edge security teams. In a recent webinar hosted...
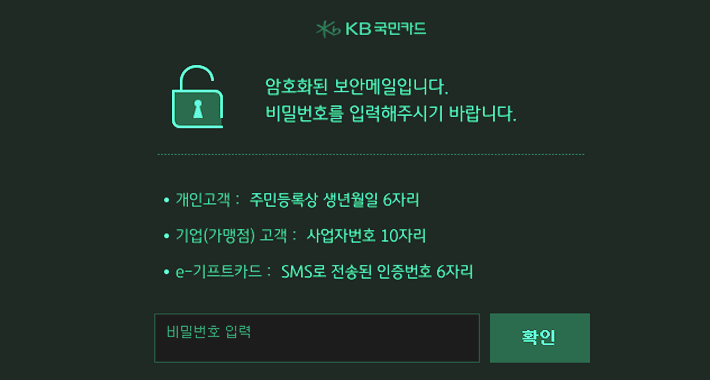
The Cost of Tax Season Fraud: How Threat Actors Target Your Data and Money
The Cost of Tax Season Fraud: How Threat Actors Target Your Data and MoneyThe IRS identified a staggering $5.7 billion in tax fraud schemes last year,...
USENIX Security ’22 – Yufei Chen, Xi’an Chao Shen, Cong Wang, Yang Zhang – ‘Teacher Model Fingerprinting Attacks Against Transfer Learning’
USENIX Security ’22 – Yufei Chen, Xi’an Chao Shen, Cong Wang, Yang Zhang – ‘Teacher Model Fingerprinting Attacks Against Transfer Learning’Our thanks to USENIX for publishing...
Trust Assurance: The Movement that’s Reviving GRC & Relationships
Trust Assurance: The Movement that’s Reviving GRC & RelationshipsIn business, we measure everything. Like the saying goes, “What gets measured gets done,” and most companies pay...
How to Distinguish Bot vs. Human Traffic
How to Distinguish Bot vs. Human TrafficNot so long ago, bots were considered a modern-day convenience. Understandably so, bots have the potential to make enterprises more...
Microsoft Outlook Remote Hash Vulnerability (CVE-2023-23397)
Microsoft Outlook Remote Hash Vulnerability (CVE-2023-23397)The post Microsoft Outlook Remote Hash Vulnerability (CVE-2023-23397) appeared first on Fidelis Cybersecurity. The post Microsoft Outlook Remote Hash Vulnerability (CVE-2023-23397)...
USENIX Security ’22 – Xudong Pan, Mi Zhang, Beina Sheng, Jiaming Zhu, Min Yang – ‘Hidden Trigger Backdoor Attack On NLP Models Via Linguistic Style Manipulation’
USENIX Security ’22 – Xudong Pan, Mi Zhang, Beina Sheng, Jiaming Zhu, Min Yang – ‘Hidden Trigger Backdoor Attack On NLP Models Via Linguistic Style Manipulation’Our...