Lenovo fixes flaws that can be used to disable UEFI Secure BootLenovo has fixed two high-severity vulnerabilities impacting various ThinkBook, IdeaPad, and Yoga laptop models that...
Year: 2022
MSA-22-0024: Remote code execution risk when restoring malformed backup file from Moodle 1.9
MSA-22-0024: Remote code execution risk when restoring malformed backup file from Moodle 1.9от Michael Hawkins. A remote code execution risk when restoring backup files originating from...
China Likely Amasses 0-Days Via Vulnerability Disclosure Law
China Likely Amasses 0-Days Via Vulnerability Disclosure LawMicrosoft Finds Increased Use of Zero-Days by Chinese Hackers Over Past YearIt's been a year since Beijing imposed regulations...
Feds Warn of Iranian Threats to Healthcare Sector
Feds Warn of Iranian Threats to Healthcare SectorTehran Hackers Use Social Engineering to Close Sophistication GapThe healthcare industry should be aware of Iranian hackers using social...
Ransomware group starts publishing Medibank data as company warns customers to be vigilant for scammers
Ransomware group starts publishing Medibank data as company warns customers to be vigilant for scammersHundreds of names, addresses, birthdates and Medicare details posted under ‘good list’...
EU Complicit in Spread of Advanced Spyware, Charges Veld
EU Complicit in Spread of Advanced Spyware, Charges VeldPEGA Committee Rapporteur Sophie in 't Veld Calls for Spyware MoratoriumA Dutch member of the European Parliament accused...
Spotlight: STEM Day 2022
Spotlight: STEM Day 2022DataDome spotlights STEM Day 2022, emphasizing science, technology, engineering, & math education, careers, & women empowerment. The post Spotlight: STEM Day 2022 appeared...
MFA Adoption is Improving, but Cybercriminals are Keeping Up
MFA Adoption is Improving, but Cybercriminals are Keeping Up While multifactor authentication has historically been hailed as one of the most significant forms of defense against...
6 Kubernetes Cost Control Strategies You Need in Place for 2023
6 Kubernetes Cost Control Strategies You Need in Place for 2023 Organizations have moved increasingly to the cloud, adopting containers and Kubernetes to change their infrastructure...
Social Engineering Attacks on New Employees
Social Engineering Attacks on New EmployeesOpportunistic cybercriminals increasingly opt for psychological manipulation over technical hacks to gain entry points into networks. Many personnel – employees, business...
What you should know about cloud workload protection platforms (CWPP)
What you should know about cloud workload protection platforms (CWPP)Learn how to secure web applications with cloud workload protection platforms (CWPP), how these cloud security solutions...
SAP Patch Day: November 2022
SAP Patch Day: November 2022SAP Patch Day: November 2022 Onapsis Tue, 11/08/2022 - 14:46 Critical HotNews for SAP BusinessObjects and SAPUI5 November Summary - 14 new...
Can You Manage Change Management?
Can You Manage Change Management? In a recent podcast interview with Hillarie McClure, Multimedia Director of Cybercrime Magazine, Robert E. Johnson III, Cimcor CEO/President, discusses how...
Hacker Stole $3B of Bitcoin — Because ‘Crypto’ is Garbage
Hacker Stole $3B of Bitcoin — Because ‘Crypto’ is Garbage James Zhong admitted to stealing 50,000 bitcoins from the former dark web market, Silk Road The post...
Vultur Android Banking Trojan Reaches 100,000+ Downloads on Google Play Store
Vultur Android Banking Trojan Reaches 100,000+ Downloads on Google Play StoreThe dropper hides behind a fake utility app with limited permissions and a small footprintLeer másThe...
Silk Road Thief Pleads Guilty to $3.4bn Raid
Silk Road Thief Pleads Guilty to $3.4bn RaidMan stole 50,000 Bitcoin from notorious dark web marketplaceLeer másMan stole 50,000 Bitcoin from notorious dark web marketplace
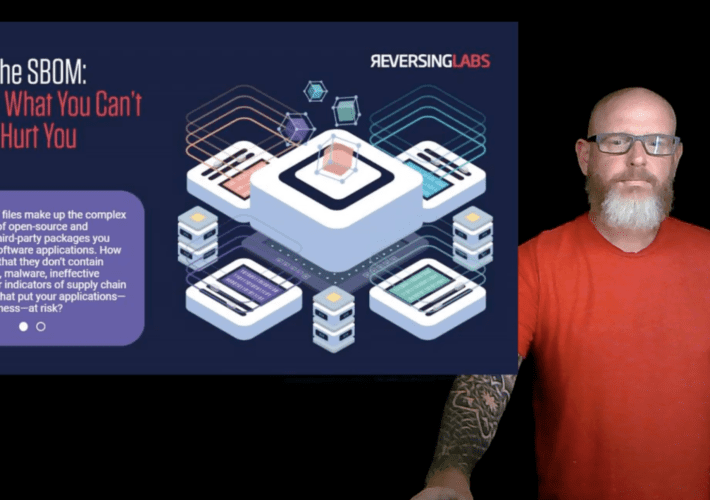
Forrester Security & Risk talk: Go beyond the SBOM for software supply chain security
Forrester Security & Risk talk: Go beyond the SBOM for software supply chain security At the Forrester Security & Risk Forum, ReversingLabs Field CISO Matt Rose talks...
New Laplas Clipper Malware Targeting Cryptocurrency Users via SmokeLoader
New Laplas Clipper Malware Targeting Cryptocurrency Users via SmokeLoaderCryptocurrency users are being targeted with a new clipper malware strain dubbed Laplas by means of another malware known as...
U.S. Seizes Over 50K Bitcoin Worth $3.3 Billion Linked to Silk Road Dark Web
U.S. Seizes Over 50K Bitcoin Worth $3.3 Billion Linked to Silk Road Dark WebThe U.S. Department of Justice (DoJ) on Monday said it seized 50,676 Bitcoin...
Amadey Bot Spotted Deploying LockBit 3.0 Ransomware on Hacked Machines
Amadey Bot Spotted Deploying LockBit 3.0 Ransomware on Hacked MachinesThe Amadey malware is being used to deploy LockBit 3.0 ransomware on compromised systems, researchers have warned. "Amadey bot,...
Silk Road drugs market hacker pleads guilty, faces 20 years inside
Silk Road drugs market hacker pleads guilty, faces 20 years insideJurisprudence isn't like arithmetic... two negatives never make a positive!Leer másNaked SecurityJurisprudence isn't like arithmetic... two...
Digest Stream: Don’t use “pizza123” as a password
Digest Stream: Don’t use “pizza123” as a passwordThe magazine Fast Company was recently hacked. After gaining access, the attackers sent offensive push notifications to users via...
Swiss Re: Cyber-Insurance Industry Must Reform
Swiss Re: Cyber-Insurance Industry Must ReformSome 90% of risk is still uninsured, warns industry giantLeer másSome 90% of risk is still uninsured, warns industry giant
SMBs Fear Security Budget Cuts as Inflation Bites
SMBs Fear Security Budget Cuts as Inflation BitesConcerns come amid worries over ransomware surgeLeer másConcerns come amid worries over ransomware surge
The 15 biggest data breaches of the 21st century
The 15 biggest data breaches of the 21st centuryIn today’s data-driven world, data breaches can affect hundreds of millions or even billions of people at a...
Hacking baby monitors can be child’s play: Here’s how to stay safe
Hacking baby monitors can be child’s play: Here’s how to stay safeMake sure that the device that’s supposed to help you keep tabs on your little...
Conti Affiliates Black Basta, BlackByte Continue to Attack Critical Infrastructure
Conti Affiliates Black Basta, BlackByte Continue to Attack Critical InfrastructureBetween February and July, 81 victim organizations were listed on the groups' data leak sitesLeer másBetween February...
SEC Announces ‘Enforcement Action’ For SolarWinds Over 2020 Hack
SEC Announces 'Enforcement Action' For SolarWinds Over 2020 HackIn a recent 8-K filing with the SEC, the firm said it reached an agreement with shareholdersLeer másIn...
Insider Risk on the Rise: 12% of Employees Take IP When Leaving Jobs
Insider Risk on the Rise: 12% of Employees Take IP When Leaving JobsThe data comes from workforce cyber intelligence and security company DtexLeer másThe data comes...
‘Justice Blade’ Hackers are Targeting Saudi Arabia
‘Justice Blade’ Hackers are Targeting Saudi ArabiaThreats actors calling themselves “Justice Blade” published leaked data from an outsourcing IT vendor. The group of threat actors calling...