CISA Releases SSVC Guide to Help Companies Prioritize VulnerabilitiesRemediation efforts are prioritized based on exploitation status, safety impact and prevalence criteriaLeer másRemediation efforts are prioritized based...
Year: 2022
Grip Security Blog 2022-11-15 06:32:47
Grip Security Blog 2022-11-15 06:32:47 Why SSCP is Essential for SaaS Security Benefits of SaaS Security Control Plane for SaaS Security For CISOs, security managers, and similar...
French Furnishing Retail Giant Allegedly Hit With Ransomware
French Furnishing Retail Giant Allegedly Hit With RansomwareThe group of hackers ALPHV, also known as BlackCat, claimed to have stolen more than one terabyte of data...
New York-barred attorneys required to complete cybersecurity, privacy, and data protection training
New York-barred attorneys required to complete cybersecurity, privacy, and data protection trainingNew York-barred attorneys will be required to complete one continuing legal education (CLE) credit hour...
IT Leaders Adopting Threat Intelligence, But Challenges Persist
IT Leaders Adopting Threat Intelligence, But Challenges Persist While the majority of enterprise IT security managers rely on threat intelligence to reduce cybersecurity risk, many still...
DNS Logging: What It Is and How Can It Help in Preventing DNS Attacks?
DNS Logging: What It Is and How Can It Help in Preventing DNS Attacks?DNS logging is the process of gathering detailed data on DNS traffic (all...
Ukrainian CERT Discloses New Data-Wiping Campaign
Ukrainian CERT Discloses New Data-Wiping CampaignSomnia malware hijacks Telegram and VPN accountsLeer másSomnia malware hijacks Telegram and VPN accounts
Build a mature approach for better cybersecurity vendor evaluation
Build a mature approach for better cybersecurity vendor evaluationSeasoned CISO Mike Manrod knows the value of a good cybersecurity vendor evaluation. He recalls that in a...
UK Shoppers Lost £15m+ to Scammers Last Winter
UK Shoppers Lost £15m+ to Scammers Last WinterCyber experts urge consumers to improve online safetyLeer másCyber experts urge consumers to improve online safety
Chinese Cyberspies Responsible for BadBazaar Android Malware
Chinese Cyberspies Responsible for BadBazaar Android MalwareA spyware tool known as BadBazaar, has been discovered targeting ethnic and religious minorities in China, mainly the Uyghurs in...
Microsoft Defender network protection generally available on iOS, Android
Microsoft Defender network protection generally available on iOS, AndroidMicrosoft announced that the Mobile Network Protection feature is generally available to help organizations detect network weaknesses affecting...
New Extortion Scam Threatens Victims with Data Leak
New Extortion Scam Threatens Victims with Data LeakA new extortion scam is aimed at website owners and admins all over the world. The scam claims that...
Mass Email Extortion Campaign Claims Server Hack
Mass Email Extortion Campaign Claims Server HackThreat actors claim they’ll destroy victims' reputation if they don't payLeer másThreat actors claim they’ll destroy victims' reputation if they...
Ukrainian Organizations Infected by Russian Hacktivists
Ukrainian Organizations Infected by Russian HacktivistsA new ransomware strain called Somnia has affected multiple Ukrainian organizations lately, encrypting their systems and causing operational problems. The Computer...
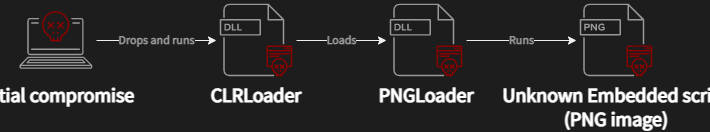
Worok Hackers Abuse Dropbox API to Leak Data via Backdoor Hidden in Images
Worok Hackers Abuse Dropbox API to Leak Data via Backdoor Hidden in ImagesWorok, a newly discovered cyber espionage group, has been hiding malware in seemingly innocuous...
Australia Considers Ban on Ransomware Payments After Medibank Breach
Australia Considers Ban on Ransomware Payments After Medibank BreachHome affairs minister Clare O'Neil made the announcement on ABC television on SundayLeer másHome affairs minister Clare O'Neil...
The Week in Ransomware – November 11th 2022 – LockBit feeling the heat
The Week in Ransomware - November 11th 2022 - LockBit feeling the heatThis 'Week in Ransomware' covers the last two weeks of ransomware news, with new...
Australia Is Forming a Squad for Combating Cyber Threat Groups
Australia Is Forming a Squad for Combating Cyber Threat GroupsIn the previous months, threat actors have been heavily targeting Australian companies, two of the most notorious...
NSA Guide Helps Firms Protect Against Memory Safety Vulnerabilities
NSA Guide Helps Firms Protect Against Memory Safety VulnerabilitiesThe document describes situations where cyber actors steal sensitive information and other negative impactsLeer másThe document describes situations...
Android phone owner accidentally finds a way to bypass lock screen
Android phone owner accidentally finds a way to bypass lock screenCybersecurity researcher David Schütz accidentally found a way to bypass the lock screen on his fully...
Giant Canadian Food Retailer Sobeys: A Victim of Ransomware?
Giant Canadian Food Retailer Sobeys: A Victim of Ransomware?Sobeys, a major grocery retailer in Canada, published an official statement announcing it has been affected by a...
GitHub Now Supports Private Vulnerability Reporting For Public Repositories
GitHub Now Supports Private Vulnerability Reporting For Public RepositoriesThe feature needs to be manually enabled by repository maintainersLeer másThe feature needs to be manually enabled by...
Turkey Restricts Social Media Channels After Blast in Taksim, Istanbul
Turkey Restricts Social Media Channels After Blast in Taksim, IstanbulWhat happened in Turkey, on November 13th? On Sunday, November 13th, reports of a bomb blast on...
New extortion scam threatens to damage sites’ reputation, leak data
New extortion scam threatens to damage sites’ reputation, leak dataAn active extortion scam is targeting website owners and admins worldwide, claiming to have hacked their servers and...
Google to Pay $392m in Landmark Privacy Case
Google to Pay $392m in Landmark Privacy CaseMulti-state settlement is largest in US historyLeer másMulti-state settlement is largest in US history
Ukraine says Russian hacktivists use new Somnia ransomware
Ukraine says Russian hacktivists use new Somnia ransomwareRussian hacktivists have infected multiple organizations in Ukraine with a new ransomware strain called 'Somnia,' encrypting their systems and causing operational...
Police Celebrate Arrest of 59 Suspected Scammers
Police Celebrate Arrest of 59 Suspected ScammersMonth-long European operation focused on online fraudstersLeer másMonth-long European operation focused on online fraudsters
Avast details Worok espionage group’s compromise chain
Avast details Worok espionage group’s compromise chainCyber espionage group Worok abuses Dropbox API to exfiltrate data via using a backdoor hidden in apparently innocuous image files. Researchers...
Microsoft’s New Patch Tuesday Updates Causes Windows Kerberos Authentication to Break
Microsoft’s New Patch Tuesday Updates Causes Windows Kerberos Authentication to BreakAn issue that is causing Kerberos sign-in failures has been reported by multiple enterprise domain controllers....
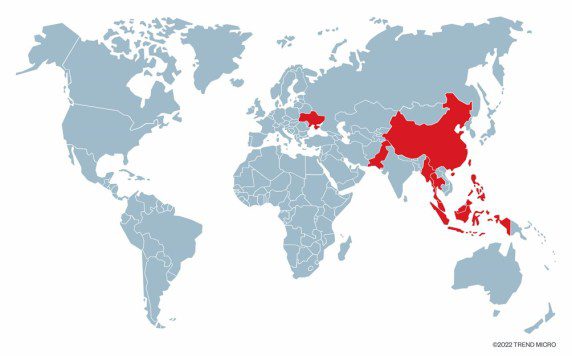
Previously undetected Earth Longzhi APT group is a subgroup of APT41
Previously undetected Earth Longzhi APT group is a subgroup of APT41Trend Micro reported that the Earth Longzhi group, a previously undocumented subgroup of APT41, targets Ukraine and Asian...