U.S. Authorities Seize Domains Used in 'Pig butchering' Cryptocurrency ScamsThe U.S. Justice Department (DoJ) on Monday announced the takedown of seven domain names in connection to a "pig...
Year: 2022
Thousands of Algolia API Keys Could Expose Users’ Data
Thousands of Algolia API Keys Could Expose Users' DataThe majority were from shopping, education, lifestyle, business and medical firmsLeer másThe majority were from shopping, education, lifestyle,...
Here’s How to Ensure Your Incident Response Strategy is Ready for Holiday Hackers
Here's How to Ensure Your Incident Response Strategy is Ready for Holiday HackersThe best line of defense against holiday hacking schemes is a comprehensive incident response strategy that...
Luna Moth Gang Invests in Call Centers to Target Businesses with Callback Phishing Campaigns
Luna Moth Gang Invests in Call Centers to Target Businesses with Callback Phishing CampaignsThe Luna Moth campaign has extorted hundreds of thousands of dollars from several...
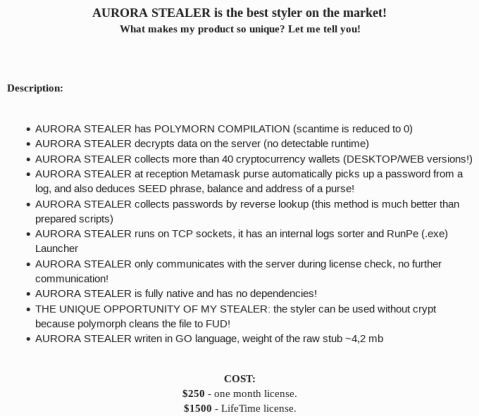
Researchers Warn of Cyber Criminals Using Go-based Aurora Stealer Malware
Researchers Warn of Cyber Criminals Using Go-based Aurora Stealer MalwareA nascent Go-based malware known as Aurora Stealer is being increasingly deployed as part of campaigns designed...
10 Suspects Charged for BEC Scams Targeting Federal Funding Programs
10 Suspects Charged for BEC Scams Targeting Federal Funding ProgramsTen people have been charged by the U.S. Department of Justice (DOJ) for their alleged roles in...
Google Wins Legal Battle Against Glupteba Botnet
Google Wins Legal Battle Against Glupteba BotnetThe tech giant said the court's ruling against the botnet operators set a crucial legal precedentLeer másThe tech giant said...
Vanuatu Government Systems Taken Offline by Hackers
Vanuatu Government Systems Taken Offline by HackersVanuatu’s Government’s servers were taken out on November 4th, leaving 315,000 people unable to pay taxes, invoice bills, get licenses,...
How social media scammers buy time to steal your 2FA codes
How social media scammers buy time to steal your 2FA codesThe warning is hosted on a real Facebook page; the phishing uses HTTPS via a real...
Credential Stuffers Steal $300K from DraftKings Customers
Credential Stuffers Steal $300K from DraftKings CustomersComplaints about poor customer service flood TwitterLeer másComplaints about poor customer service flood Twitter
Luna Moth callback phishing campaign leverages extortion without malware
Luna Moth callback phishing campaign leverages extortion without malwarePalo Alto’s Unit 42 has investigated several incidents linked to the Luna Moth group callback phishing extortion campaign...
FIRESIDE CHAT: Anchoring security on granular visibility, proactive management of all endpoints
FIRESIDE CHAT: Anchoring security on granular visibility, proactive management of all endpointsEndpoints are where all are the connectivity action is. Related: Ransomware bombardments And securing endpoints...
Experts Warn Threat Actors May Abuse Red Team Tool Nighthawk
Experts Warn Threat Actors May Abuse Red Team Tool NighthawkC2 framework could be the next Cobalt Strike, says ProofpointLeer másC2 framework could be the next Cobalt...
New Ransomware Trick: Encrypting Files Then Stealing Discord Accounts
New Ransomware Trick: Encrypting Files Then Stealing Discord AccountsAXLocker is a new strain of ransomware discovered in late November 2022. It encrypts the files of victims...
Know thy enemy: thinking like a hacker can boost cybersecurity strategy
Know thy enemy: thinking like a hacker can boost cybersecurity strategyAs group leader for Cyber Adversary Engagement at MITRE Corp., Maretta Morovitz sees value in getting...
Estonian Duo Arrested for Masterminding $575m Ponzi Scheme
Estonian Duo Arrested for Masterminding $575m Ponzi SchemeUS authorities unseal 18-count indictmentLeer másUS authorities unseal 18-count indictment
A Google Chrome Extension Is Helping Hackers Steal Cryptocurrency Passwords
A Google Chrome Extension Is Helping Hackers Steal Cryptocurrency PasswordsA Google Chrome browser extension named VenomSoftX is being deployed by Windows malware to steal cryptocurrency and...
Firms Spend $1197 Per Employee Yearly to Address Cyber-Attacks
Firms Spend $1197 Per Employee Yearly to Address Cyber-AttacksThe data excludes compliance fines, ransomware costs and losses from non-operational processesLeer másThe data excludes compliance fines, ransomware...
Latest insights on APT activity – Week in security with Tony Anscombe
Latest insights on APT activity – Week in security with Tony AnscombeWhat have some of the world's most notorious APT groups been up to lately? A...
US Takes Down Domains Used in ‘Pig Butchering’ Cryptocurrency Scheme
US Takes Down Domains Used in 'Pig Butchering' Cryptocurrency SchemeThe US Attorney's Office for the Eastern District of Virginia made the announcement on MondayLeer másThe US...
AirAsia Falls Victim to Daixin Ransomware Gang
AirAsia Falls Victim to Daixin Ransomware GangThe Malaysian low-cost airline belonging to AirAsia had some of its data leaked by the cybercrime group known as Daixin Team,...
Expert published PoC exploit code for macOS sandbox escape flaw
Expert published PoC exploit code for macOS sandbox escape flawA researcher published details and proof-of-concept (PoC) code for High-Severity macOS Sandbox escape vulnerability tracked as CVE-2022-26696....
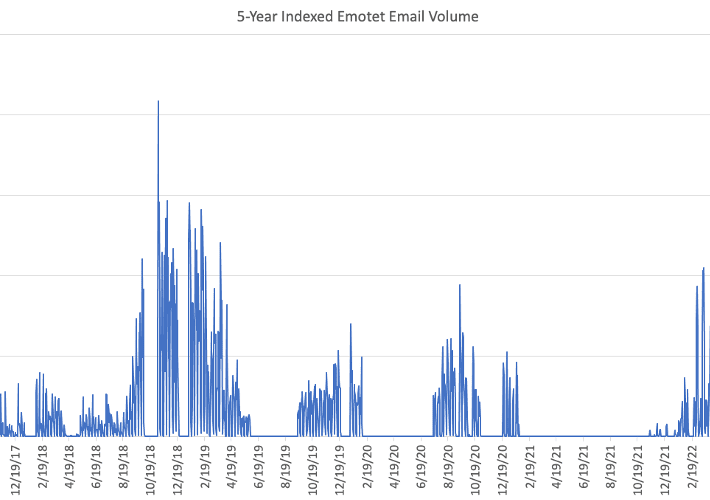
Emotet is back and delivers payloads like IcedID and Bumblebee
Emotet is back and delivers payloads like IcedID and BumblebeeThe Emotet malware is back and experts warn of a high-volume malspam campaign delivering payloads like IcedID...
PII Breach Discovered on Bahmni Hospital Management System
PII Breach Discovered on Bahmni Hospital Management SystemOn September 19th, 2022, a breach affecting Bahmni company was discovered. The Bahmni Hospital Management System was breached exposing...
Two Estonian citizens arrested in $575M cryptocurrency fraud scheme
Two Estonian citizens arrested in $575M cryptocurrency fraud schemeTwo Estonian citizens were arrested in Tallinn for allegedly running a $575 million cryptocurrency fraud scheme. Two Estonian...
Apps with Over 3 Million Downloads Leak Algolia API Keys
Apps with Over 3 Million Downloads Leak Algolia API KeysResearchers found 1,550 mobile apps that were leaking Algolia API credentials, putting private internal services and user...
Apps with over 3 million installs leak ‘Admin’ search API keys
Apps with over 3 million installs leak 'Admin' search API keysResearchers discovered 1,550 mobile apps leaking Algolia API keys, risking the exposure of sensitive internal services...
Aurora Stealer Malware is becoming a prominent threat in the cybercrime ecosystem
Aurora Stealer Malware is becoming a prominent threat in the cybercrime ecosystemResearchers warn of threat actors employing a new Go-based malware dubbed Aurora Stealer in attacks...
Sensitive Data From Nuclear Facilities Leaked on Dark Web
Sensitive Data From Nuclear Facilities Leaked on Dark WebCybercrime activities targeting the nuclear industry worldwide have risen during the past eight months, according to Cyble, a...
Google releases 165 YARA rules to detect Cobalt Strike attacks
Google releases 165 YARA rules to detect Cobalt Strike attacksThe Google Cloud Threat Intelligence team has open-sourced YARA Rules and a VirusTotal Collection of indicators of...