Suspected Russian Money Launderer Extradited to USMan allegedly handled over $400,000 in Ryuk proceedsLeer másMan allegedly handled over $400,000 in Ryuk proceeds
Year: 2022
ÆPIC Leak is the first CPU flaw able to architecturally disclose sensitive data
ÆPIC Leak is the first CPU flaw able to architecturally disclose sensitive dataResearchers uncovered a new flaw, dubbed ÆPIC, in Intel CPUs that enables attackers to obtain encryption...
North Korea-linked APT targets Job Seekers with macOS malware
North Korea-linked APT targets Job Seekers with macOS malwareThe North Korea-linked Lazarus Group has been observed targeting job seekers with macOS malware working also on Intel...
DEF CON – “don’t worry, the elections are safe” edition
DEF CON – “don’t worry, the elections are safe” editionDon't worry, elections are safe. Our Security Researcher Cameron Camp provide us highlights from the DEF CON...
ÆPIC Leak is the first CPU flaw able to architecturally disclose sensitive data
ÆPIC Leak is the first CPU flaw able to architecturally disclose sensitive dataResearchers uncovered a new flaw, dubbed ÆPIC, in Intel CPUs that enables attackers to obtain encryption...
Researchers Find 35 Adware Apps on Google Play
Researchers Find 35 Adware Apps on Google PlayApps have millions of downloads, says BitdefenderLeer másApps have millions of downloads, says Bitdefender
Google fixed a new Chrome Zero-Day actively exploited in the wild
Google fixed a new Chrome Zero-Day actively exploited in the wildGoogle addressed a dozen vulnerabilities in the Chrome browser, including the fifth Chrome zero-day flaw exploited...
Google fixed a new Chrome Zero-Day actively exploited in the wild
Google fixed a new Chrome Zero-Day actively exploited in the wildGoogle addressed a dozen vulnerabilities in the Chrome browser, including the fifth Chrome zero-day flaw exploited...
Bugdrop dropper includes features to circumvent Google’s security Controls
Bugdrop dropper includes features to circumvent Google’s security ControlsResearchers have discovered a previously undocumented Android dropper, dubbed BugDrop, that’s still under development. Recently, researchers from ThreatFabric...
Bugdrop dropper includes features to circumvent Google’s security Controls
Bugdrop dropper includes features to circumvent Google’s security ControlsResearchers have discovered a previously undocumented Android dropper, dubbed BugDrop, that’s still under development. Recently, researchers from ThreatFabric...
PoC exploit code for critical Realtek RCE flaw released online
PoC exploit code for critical Realtek RCE flaw released onlineExploit code for a critical vulnerability affecting networking devices using Realtek RTL819x system on a chip released...
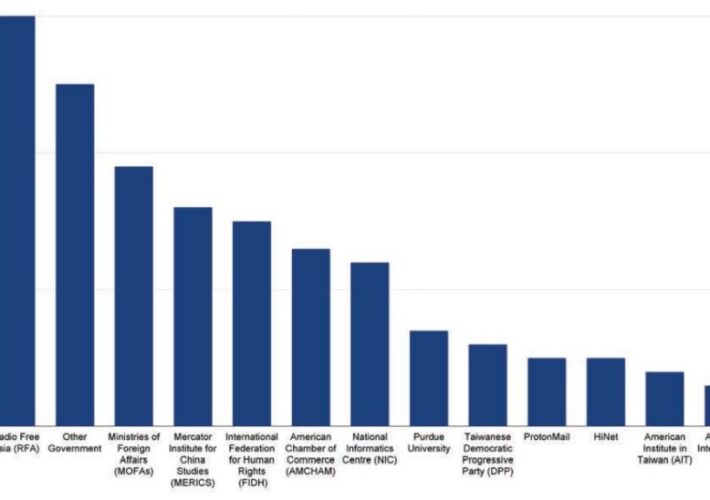
China-linked RedAlpha behind multi-year credential theft campaign
China-linked RedAlpha behind multi-year credential theft campaignA China-linked APT group named RedAlpha is behind a long-running mass credential theft campaign aimed at organizations worldwide. Recorded Future researchers attributed...
China-linked RedAlpha behind multi-year credential theft campaign
China-linked RedAlpha behind multi-year credential theft campaignA China-linked APT group named RedAlpha is behind a long-running mass credential theft campaign aimed at organizations worldwide. Recorded Future researchers attributed...
Apple fixed two new zero-day flaws exploited by threat actors
Apple fixed two new zero-day flaws exploited by threat actorsApple addressed two zero-day vulnerabilities, exploited by threat actors, affecting iOS, iPadOS, and macOS devices. Apple this week released security...
PoC exploit code for critical Realtek RCE flaw released online
PoC exploit code for critical Realtek RCE flaw released onlineExploit code for a critical vulnerability affecting networking devices using Realtek RTL819x system on a chip released...
Apple fixed two new zero-day flaws exploited by threat actors
Apple fixed two new zero-day flaws exploited by threat actorsApple addressed two zero-day vulnerabilities, exploited by threat actors, affecting iOS, iPadOS, and macOS devices. Apple this week released security...
BlueSky Ransomware Detection: Targets Windows Hosts and Leverages Multithreading for Faster Encryption
BlueSky Ransomware Detection: Targets Windows Hosts and Leverages Multithreading for Faster Encryption BlueSky ransomware represents a rapidly evolving malware family that involves sophisticated anti-analysis capabilities and...
Zeppelin Ransomware Detection: CISA and FBI Issue a Joint Advisory for Enhanced Protection Against RaaS Threats
Zeppelin Ransomware Detection: CISA and FBI Issue a Joint Advisory for Enhanced Protection Against RaaS Threats According to SOC Prime’s Detection as Code Innovation Report covering...
Product Adoption Specialist (US)
Product Adoption Specialist (US)Our Perfect Candidate You are highly disciplined, self-motivated, and influential. You have confidence in prospecting and communicating with C-level executives and advanced technical...
Detecting SEABORGIUM Campaigns: A Cyberespionage Group Targeting Governments, Military, and NGOs Across Europe
Detecting SEABORGIUM Campaigns: A Cyberespionage Group Targeting Governments, Military, and NGOs Across Europe Cybersecurity experts from Microsoft Threat Intelligence Center (MSTIC) have disrupted the infrastructure of...
South Staffordshire Water Confirms Cyberattack
South Staffordshire Water Confirms CyberattackSouth Staffordshire Water, a company that provides 1.6 consumers daily with 330 million liters of drinking water, has confirmed an IT outage...
Safeguarding Industrial Control Systems Environments
Safeguarding Industrial Control Systems EnvironmentsPreventing internal & external cybersecurity breaches with zero trust OT network segmentation By Ryan Lung, Senior product manager […] The post Safeguarding...
Here Comes BlackByte Ransomware 2.0
Here Comes BlackByte Ransomware 2.0The BlackByte ransomware has returned with an advanced version of its operation, including a new data leak website using novel extortion strategies...
It’s Time to Rethink Endpoint Security
It’s Time to Rethink Endpoint SecurityBy Carolyn Crandall, Chief Security Advocate, Attivo Networks Sometimes, organizations change from within, while other times change is […] The post...
SOC Prime Threat Bounty — July 2022 Results
SOC Prime Threat Bounty — July 2022 Results July ‘22 Updates During the previous month, we introduced several improvements to content validation and Sigma Rules Bot...
The Emergence of Dynamic Threat Hunting
The Emergence of Dynamic Threat HuntingA review of the evolving cyber security industry over 15 years in business By James “Jim” McMurry, CEO […] The post...
Securing Your Organization During Global Turmoil
Securing Your Organization During Global TurmoilRepelling Cyber Criminals Trying to Capitalize on a Crisis By Kevin Orr, President, RSA Federal Current geopolitical crises […] The post...
What is Cyber Threat Hunting? The Ultimate Guide
What is Cyber Threat Hunting? The Ultimate Guide Cyber Threat Hunting is a novel approach to Threat Detection which is aimed at finding cyber threats within...
Remotely Controlling Touchscreens
Remotely Controlling TouchscreensThis is more of a demonstration than a real-world vulnerability, but researchers can use electromagnetic interference to remotely control touchscreens. From a news article:...
Zoom Exploit on MacOS
Zoom Exploit on MacOSThis vulnerability was reported to Zoom last December: The exploit works by targeting the installer for the Zoom application, which needs to run...