Cybersecurity News Round-Up: Week of August 22, 2022Twitter's Ex-CSO accuses the company of cybersecurity negligence, Hackers continue to attack hospitals and critical infrastructure The post Cybersecurity...
Year: 2022
S3 Ep97: Did your iPhone get pwned? How would you know? [Audio + Text]
S3 Ep97: Did your iPhone get pwned? How would you know? [Audio + Text]Latest episode - listen now! (Or read the transcript if you prefer the...
Firefox 104 is out – no critical bugs, but update anyway
Firefox 104 is out – no critical bugs, but update anywayTwo trust-spoofing bugs were the main culprits this month - but neither one was a zero-day.Leer...
LastPass attackers steal source code, no evidence users’ passwords compromised
LastPass attackers steal source code, no evidence users’ passwords compromisedLastPass, the popular password manager used by millions of people around the world, has announced that it...
The 4 Best Open Source PKI Software Solutions (And Choosing the Right One)
The 4 Best Open Source PKI Software Solutions (And Choosing the Right One)In the never-ending battle between business success and cybersecurity threats, enterprises have discovered a...
TSA Requirements: A Snapshot of Growing Attention to Pipeline Cybersecurity
TSA Requirements: A Snapshot of Growing Attention to Pipeline CybersecurityThe post TSA Requirements: A Snapshot of Growing Attention to Pipeline Cybersecurity appeared first on Nozomi Networks....
What Is a TLS/SSL Port?
What Is a TLS/SSL Port?What Is a TLS/SSL Port? 97thfloor Fri, 08/26/2022 - 09:15 1 view What TCP Ports Are Used Most Frequently? Managing TLS/SSL...
DNS data indicates increased malicious domain activity, phishing toolkit reuse
DNS data indicates increased malicious domain activity, phishing toolkit reuseNew research from cybersecurity vendor Akamai has revealed that 12.3% of monitored devices communicated with domains associated...
Up to 35% more CVEs published so far this year compared to 2021
Up to 35% more CVEs published so far this year compared to 2021A new report from Trustwave SpiderLabs has revealed that the number of CVEs published...
What is doxing and how to protect yourself
What is doxing and how to protect yourselfDoxing can happen to anyone – here’s how you can reduce the odds that your personal information will be...
French hospital crippled by cyberattack – Week in security with Tony Anscombe
French hospital crippled by cyberattack – Week in security with Tony AnscombeAs another hospital falls victim to ransomware, Tony weighs in on the much-debated issue of...
Ransomware Attack Forces French Hospital to Transfer Patients to Other Facilities
Ransomware Attack Forces French Hospital to Transfer Patients to Other FacilitiesCenter Hospitalier Sud Francilien (CHSF), was the victim of a ransomware attack that forced the medical...
Iran-linked Mercury APT exploited Log4Shell in SysAid Apps for initial access
Iran-linked Mercury APT exploited Log4Shell in SysAid Apps for initial accessAn Iran-linked Mercury APT group exploited the Log4Shell vulnerability in SysAid applications for initial access to...
Massive “0ktapus” Phishing Attack Hits Over 130 Organizations
Massive “0ktapus” Phishing Attack Hits Over 130 OrganizationsOver 130 organizations were compromised in the “0ktapus” phishing campaign and the credential of 9,931 employees were stolen. Hackers...
Cyber EO One Year Later: Feds Weigh in On Progress, Areas For Improvement
Cyber EO One Year Later: Feds Weigh in On Progress, Areas For ImprovementBy Brittany Johnston, Research Director, MeriTalk In May 2021, President Biden issued the Executive...
Cyber Risk Management: The Right Approach Is a Business-Oriented Approach
Cyber Risk Management: The Right Approach Is a Business-Oriented ApproachBy Michael Maggio, CEO & Chief Product Officer of Reciprocity As rates of cyberattacks continue to increase...
LastPass hackers steal source code, no evidence of users’ passwords compromised
LastPass hackers steal source code, no evidence of users’ passwords compromisedLastPass, the popular password manager trusted by millions of people around the world, has announced that...
Man-in-the-Middle Phishing Attack
Man-in-the-Middle Phishing AttackHere’s a phishing campaign that uses a man-in-the-middle attack to defeat multi-factor authentication: Microsoft observed a campaign that inserted an attacker-controlled proxy site between...
Security and Cheap Complexity
Security and Cheap ComplexityI’ve been saying that complexity is the worst enemy of security for a long time now. (Here’s me in 1999.) And it’s been...
Our Quest: Advancing Product Labels to Help Consumers Consider Cybersecurity
Our Quest: Advancing Product Labels to Help Consumers Consider CybersecurityFor many decades, consumers have relied on labels to help them make decisions about which products to...
Addressing Multiple Concerns with a Single Solution
Addressing Multiple Concerns with a Single SolutionOrganizations have been steadily implementing digital innovations for years, but recently the pace of implementation has greatly accelerated. Although the...
A Dramatic Shift in Network Security with Zero Trust Edge Strategy
A Dramatic Shift in Network Security with Zero Trust Edge StrategyMost organizations are deep into a phase of major growth and evolution that’s called “digital acceleration.”...
The Threat That Never Goes Away
The Threat That Never Goes AwayWhile digital acceleration and work-from-anywhere strategies may have been driven by the uncertain times brought about by the global pandemic, they...
Cyberthreats Racing Ahead of Your Defenses? Security-Driven Networking Can Put a Stop to That
Cyberthreats Racing Ahead of Your Defenses? Security-Driven Networking Can Put a Stop to ThatEnterprises of all shapes and sizes were deep into the process called digital...
Required Capabilities for Effective and Secure SD-WAN: The Network Leader’s Guide
Required Capabilities for Effective and Secure SD-WAN: The Network Leader’s GuideThere are three main trends driving organizations to replace outdated wide-area networking (WAN) infrastructures with a...
Ransomware Actor Abuses Genshin Impact Anti-Cheat Driver to Kill Antivirus
Ransomware Actor Abuses Genshin Impact Anti-Cheat Driver to Kill AntivirusWe investigate mhyprot2.sys, a vulnerable anti-cheat driver for the popular role-playing game Genshin Impact. The driver is...
Considerations for Evaluating Endpoint Detection and Response (EDR) Solutions
Considerations for Evaluating Endpoint Detection and Response (EDR) SolutionsEndpoint security solutions range from signature-based endpoint protection platform (EPP) or antivirus (AV) solutions to extended detection and...
Fortinet Secure SD-WAN Continually Received Analyst and Peer Recognition
Fortinet Secure SD-WAN Continually Received Analyst and Peer RecognitionFortinet Secure SD-WAN has caught the attention of industry analysts. Our unique Security-Driven Networking solution consolidates security and...
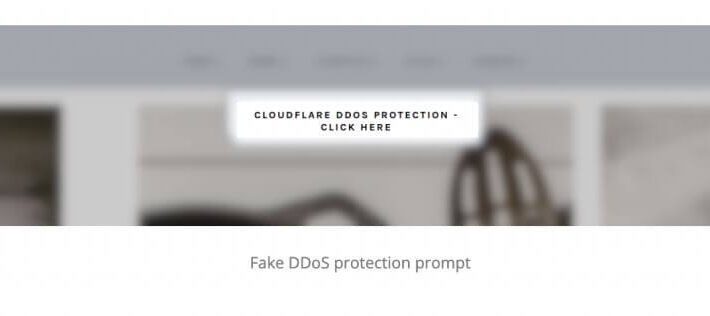
Fake DDoS pages on WordPress install the following…
Fake DDoS pages on WordPress install the following…EXECUTIVE SUMMARY: WordPress-based sites hacked? Security researchers say that WordPress pages are being hacked to display spoofed Cloudflare DDoS...
Infosec4TC Platinum Membership: Cyber Security Training Lifetime Access
Infosec4TC Platinum Membership: Cyber Security Training Lifetime AccessBe an Expert on Infosec4TC with Unlimited Access to Self-Paced Courses on GSEC, CISSP & More Infosec4TC understands the...