Windows 11 22H2: Here are the new features coming later this monthWindows 11 version 22H2 aka Sun Valley 2 is set to launch later this month....
Year: 2022
Impact of Samsung’s most recent data breach unknown
Impact of Samsung’s most recent data breach unknownThe lack of transparency could be cause for concern, but the data stolen is not high value. The post...
Cisco confirms Yanluowang ransomware leaked stolen company data
Cisco confirms Yanluowang ransomware leaked stolen company dataCisco has confirmed that the data leaked yessterday by the Yanluowang ransomware gang was stolen from the company network...
7 CISO succession planning best practices
7 CISO succession planning best practicesEXECUTIVE SUMMARY: Given the volume and complexity of security incidents, the need for a highly effective CISO is obvious and nearly...
Becoming anti-fragile: Going beyond resilience to prevent ransomware
Becoming anti-fragile: Going beyond resilience to prevent ransomwareCindi Carter, Field CISO Americas, Check Point Software Ransomware attacks are increasing in frequency, ferocity and brutality. In 2021,...
Monti, the New Conti: Ransomware Gang Uses Recycled Code
Monti, the New Conti: Ransomware Gang Uses Recycled CodeA new group, Monti, appears to have used leaked Conti code, TTPs, and infrastructure approaches to launch its...
Zane Lackey: ‘Technology Is the Easy Bit’
Zane Lackey: 'Technology Is the Easy Bit'Security Pro File: The DevOps evangelist and angel investor shares his expertise with the next generation of startups. If you're...
Report Highlights Prevalence of Software Supply Chain Risks
Report Highlights Prevalence of Software Supply Chain RisksMulticlient research report shows organizations are significantly increasing efforts to secure their supply chains in response to software supply...
Unlocking Your E5 Investment with MDR for Microsoft
Unlocking Your E5 Investment with MDR for Microsoft Contenido de la entradaLeer másDataBreachToday.com RSS Syndication
Latest Lazarus Campaign Targets Energy Companies
Latest Lazarus Campaign Targets Energy CompaniesLog4Shell Vulnerability on VMWare Horizon Servers ExploitedThe Lazarus Group, a North Korean advanced persistent threat gang, recently targeted energy companies in...
John Watters on Why Google and Mandiant Are Better Together
John Watters on Why Google and Mandiant Are Better TogetherWatters Can't Wait To Combine Google's Analytics and Mandiant's Intelligence EngineCombining the back-end data analytics of Google...
6 Top API Security Risks! Favored Targets for Attackers If Left Unmanaged
6 Top API Security Risks! Favored Targets for Attackers If Left UnmanagedSecurity threats are always a concern when it comes to APIs. API security can be...
U.S. Seizes Cryptocurrency Worth $30 Million Stolen by North Korean Hackers
U.S. Seizes Cryptocurrency Worth $30 Million Stolen by North Korean HackersMore than $30 million worth of cryptocurrency plundered by the North Korea-linked Lazarus Group from online...
IronNet’s September Threat Intelligence Brief 2022
IronNet’s September Threat Intelligence Brief 2022 Microsoft releases a report on its disruption of a Russian cyber-espionage group called SEABORGIUM (COLDRIVER) that has targeted over 30...
BSides Vancouver 2022 – Shelly Giesbrecht’s ‘Tailoring Evidence Preservation For Incident Objectives’
BSides Vancouver 2022 – Shelly Giesbrecht’s ‘Tailoring Evidence Preservation For Incident Objectives’Our sincere thanks to BSides Vancouver for publishing their outstanding conference videos on the organization's...
Albania Breaks Ties With Iran After 2022 Microsoft Investigation of CVE-2019-0604
Albania Breaks Ties With Iran After 2022 Microsoft Investigation of CVE-2019-0604The U.S. is very confidently accusing Iran of attacking Albania, based on yesterday’s report by Microsoft...
National Critical Infrastructure Under Attack: Clop Ransomware
National Critical Infrastructure Under Attack: Clop Ransomware National Critical Infrastructure Under Attack: Clop Ransomware On August 15, 2022, a U.K. water supplier suffered disrupted essential services...
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel Sectors
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel SectorsContenido de la entradaLeer másProofpoint News Feed
Fall Foliage: JavaScript/OJS Edition
Fall Foliage: JavaScript/OJS EditionI’ve been (mostly) keeping up with annual updates for my R/{sf} U.S. foliage post which you can find on GH. This year, we...
A Peek at Privacy: Where We Started, Where We are Now, and What’s Next
A Peek at Privacy: Where We Started, Where We are Now, and What’s NextAs part of NIST’s 50th anniversary of cybersecurity, this month’s blog post is...
Cloud attacks on the supply chain are a huge concern
Cloud attacks on the supply chain are a huge concernContenido de la entradaLeer másProofpoint News Feed
Medical device vulnerability could let hackers steal Wi-Fi credentials
Medical device vulnerability could let hackers steal Wi-Fi credentialsA vulnerability found in an interaction between a Wi-Fi-enabled battery system and an infusion pump for the delivery...
Cybercrime Group TA558 Ramps Up Email Attacks Against Hotels
Cybercrime Group TA558 Ramps Up Email Attacks Against HotelsContenido de la entradaLeer másProofpoint News Feed
Cloud security: Increased concern about risks from partners, suppliers
Cloud security: Increased concern about risks from partners, suppliersContenido de la entradaLeer másProofpoint News Feed
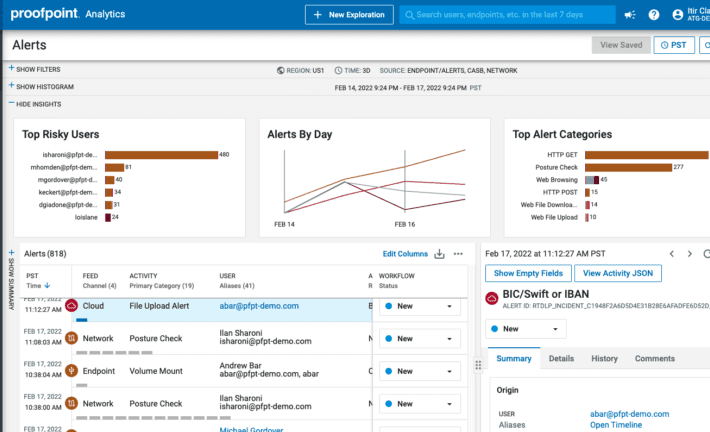
Best Data Security Solution | Proofpoint Information Protection
Best Data Security Solution | Proofpoint Information ProtectionContenido de la entradaLeer másProofpoint News Feed
Best Data Security Solution | Proofpoint Information Protection
Best Data Security Solution | Proofpoint Information ProtectionContenido de la entradaLeer másProofpoint News Feed
Triple Extortion Ransomware: A New Trend Among Cybercriminals
Triple Extortion Ransomware: A New Trend Among CybercriminalsEven though companies now understand the necessity of cybersecurity in the face of ransomware attacks, and started to take...
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance Platform
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance PlatformContenido de la entradaLeer másProofpoint News Feed
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance Platform
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance PlatformContenido de la entradaLeer másProofpoint News Feed
Chinese hackers tied to attacks on South China Sea energy firms
Chinese hackers tied to attacks on South China Sea energy firmsContenido de la entradaLeer másProofpoint News Feed