Sam Bankman-Fried's Terrible, Horrible, Very Bad DayFormer FTX CEO Will Stay in Bahamas Jail Pending Extradition to USThe many alleged failures of former FTX CEO Sam...
Month: December 2022
K45012151: Layer 2 security bypass issue CVE-2021-27861, CVE-2021-27862, CVE-2021-27853, CVE-2021-27854
K45012151: Layer 2 security bypass issue CVE-2021-27861, CVE-2021-27862, CVE-2021-27853, CVE-2021-27854Layer 2 security bypass issue CVE-2021-27861, CVE-2021-27862, CVE-2021-27853, CVE-2021-27854 Security Advisory Security Advisory Description CVE-2021-27861 Layer 2...
K87046687: VMware Tools vulnerability CVE-2022-31676
K87046687: VMware Tools vulnerability CVE-2022-31676VMware Tools vulnerability CVE-2022-31676 Security Advisory Security Advisory Description VMware Tools (12.0.0, 11.x.y and 10.x.y) contains a local privilege escalation vulnerability. A...
K37923932: libTIFF vulnerability CVE-2022-3970
K37923932: libTIFF vulnerability CVE-2022-3970libTIFF vulnerability CVE-2022-3970 Security Advisory Security Advisory Description A vulnerability was found in LibTIFF. It has been classified as critical. This affects the...
K17011311: NodeJS vulnerability CVE-2022-35256
K17011311: NodeJS vulnerability CVE-2022-35256NodeJS vulnerability CVE-2022-35256 Security Advisory Security Advisory Description The llhttp parser in the http module in Node v18.7.0 does not correctly handle header...
15 seasonal cyber security shopping tips, keep your celebrations bright
15 seasonal cyber security shopping tips, keep your celebrations brightEXECUTIVE SUMMARY: Many people are eager to celebrate the beauty of the holiday season with parties, parades,...
Malware Strains Targeting Python and JavaScript Developers Through Official Repositories
Malware Strains Targeting Python and JavaScript Developers Through Official RepositoriesAn active malware campaign is targeting the Python Package Index (PyPI) and npm repositories for Python and...
Proofpoint to Buy Deception Firm Illusive, Boost Offerings
Proofpoint to Buy Deception Firm Illusive, Boost OfferingsContenido de la entradaLeer másProofpoint News Feed
Microsoft-signed malicious Windows drivers used in ransomware attacks
Microsoft-signed malicious Windows drivers used in ransomware attacksMicrosoft has revoked several Microsoft hardware developer accounts after drivers signed through their profiles were used in cyberattacks, including...
Are robots too insecure for lethal use by law enforcement?
Are robots too insecure for lethal use by law enforcement?In late November, the San Francisco Board of Supervisors voted 8-3 to give the police the option...
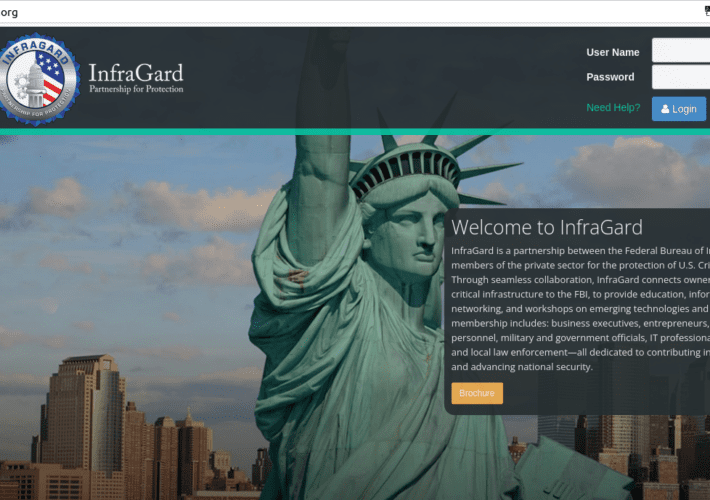
FBI’s Vetted Info Sharing Network ‘InfraGard’ Hacked
FBI’s Vetted Info Sharing Network ‘InfraGard’ HackedInfraGard, a program run by the U.S. Federal Bureau of Investigation (FBI) to build cyber and physical threat information sharing...
Twitter Addresses November Data Leak Claims
Twitter Addresses November Data Leak ClaimsNo passwords were reportedly exposed, but Twitter prompted users to enable 2FA to protect accountsLeer másNo passwords were reportedly exposed, but...
PCI Secure Software Standard version 1.2 sets out new payment security requirements
PCI Secure Software Standard version 1.2 sets out new payment security requirementsThe Payment Card Industry Security Standards Council (PCI SSC) has published version 1.2 of the...
European Commission takes step toward approving EU-US data privacy pact
European Commission takes step toward approving EU-US data privacy pactThe EU-US Data Privacy Framework—drafted to allow the flow of data between the US and the European...
Palo Alto Networks flags top cyberthreats, offers new zero-day protections
Palo Alto Networks flags top cyberthreats, offers new zero-day protectionsFirewall and security software vendor Palo Alto Network’s annual Ignite conference kicked off Tuesday, highlighted by several...
BrandPost: Securing Operational Technology Environments for Critical Infrastructure
BrandPost: Securing Operational Technology Environments for Critical InfrastructureJuniper Networks is applying its industry leading AI-driven capabilities and cloud-native architectures to Critical Infrastructure (CI) networks. We’re directly...
FBI’s Vetted Info Sharing Network ‘InfraGard’ Hacked
FBI’s Vetted Info Sharing Network ‘InfraGard’ HackedInfraGard, a program run by the U.S. Federal Bureau of Investigation (FBI) to build cyber and physical threat information sharing...
COVID-bit: the wireless spyware trick with an unfortunate name
COVID-bit: the wireless spyware trick with an unfortunate nameIt's not the switching that's the problem, it's the switching of the switching!Leer másNaked SecurityIt's not the switching...
Apple patches everything, finally reveals mystery of iOS 16.1.2
Apple patches everything, finally reveals mystery of iOS 16.1.2There's an update for everything this time, not just for iOS.Leer másNaked SecurityThere's an update for everything this...
How Amazon’s new Identity Verification System authenticates Seller Identity
How Amazon’s new Identity Verification System authenticates Seller IdentityAs a new alternative to offline seller onboarding, a new digital onboarding method is being tested by amazon...
Patch Tuesday: 0-days, RCE bugs, and a curious tale of signed malware
Patch Tuesday: 0-days, RCE bugs, and a curious tale of signed malwareTales of derring-do in the cyberunderground! (And some zero-days.)Leer másNaked SecurityTales of derring-do in the...
Google Adds Passkey Support to Chrome for Windows, macOS and Android
Google Adds Passkey Support to Chrome for Windows, macOS and AndroidGoogle has officially begun rolling out support for passkeys, the next-generation passwordless login standard, to its stable...
USENIX Security ’22 – ‘Pool Inference Attacks On Local Differential Privacy: Quantifying The Privacy Guarantees Of Apple’s Count Mean Sketch In Practice’
USENIX Security ’22 – ‘Pool Inference Attacks On Local Differential Privacy: Quantifying The Privacy Guarantees Of Apple’s Count Mean Sketch In Practice’Complete Title: USENIX Security '22...
Nosey Parker RegEx: A Positive Community Response
Nosey Parker RegEx: A Positive Community ResponseOn December 7, 2022, Praetorian Labs released a regular expression-based (RegEx) version of our Nosey Parker secrets scanning tool (see...
New wind powered land speed world record
New wind powered land speed world recordTeam New Zealand have recorded the fastest wind powered land speed yet. ‘Horonuku’ named by Ngati Whatua Orakei meaning ‘gliding...
BH EU 2022 and BSides London
BH EU 2022 and BSides LondonAs I wandered through the psychedelic chaos of Black Hat Europe 2022, I couldn’t help but feel like I had stumbled...
The LinkedIn Data Scraping Verdict — and Its Reversal
The LinkedIn Data Scraping Verdict — and Its ReversalIn October of last year, a ruling against LinkedIn by The United States Court of Appeals for the...
Top 4 SaaS Security Threats for 2023
Top 4 SaaS Security Threats for 2023With 2022 coming to a close, there is no better time to buckle down and prepare to face the security...
Daniel Stori’s ‘Oracle Downloads Page’
Daniel Stori’s ‘Oracle Downloads Page’ via the webcomic talent of the inimitable Daniel Stori at Turnoff.US! Permalink The post Daniel Stori’s ‘Oracle Downloads Page’ appeared first...
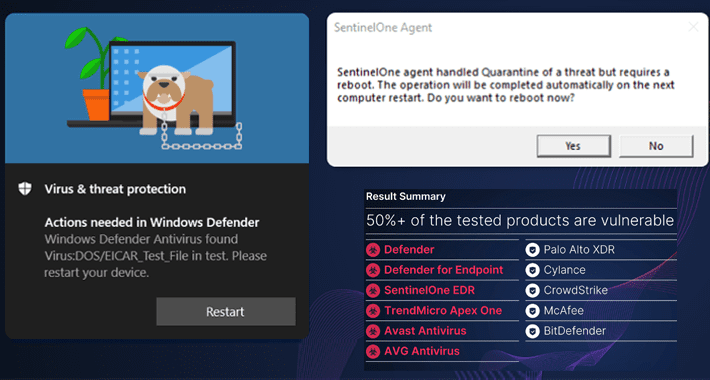
Researchers Demonstrate How EDR and Antivirus Can Be Weaponized Against Users
Researchers Demonstrate How EDR and Antivirus Can Be Weaponized Against UsersHigh-severity security vulnerabilities have been disclosed in different endpoint detection and response (EDR) and antivirus (AV)...