Why do cyber-attacks increase during holidays?Why do cyber-attacks increase during holidays? Why do cyber-attacks increase during holidays? The holiday season is traditionally a golden opportunity for...
Month: December 2022
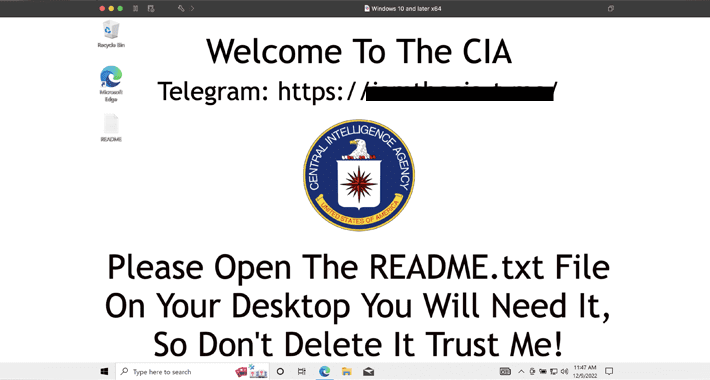
Trojanized Windows 10 Installer Used in Cyberattacks Against Ukrainian Government Entities
Trojanized Windows 10 Installer Used in Cyberattacks Against Ukrainian Government EntitiesGovernment entities in Ukraine have been breached as part of a new campaign that leveraged trojanized...
Facebook Security Failures Fueled Hate-Speech That Exacerbated Violence and Ethiopian Civil War
Facebook Security Failures Fueled Hate-Speech That Exacerbated Violence and Ethiopian Civil WarA recently filed lawsuit exposes the Facebook profit model, once again. Amare’s son, researcher Abrham...
BrandPost: One-Policy Framework, Zero Trust, and Ops teams
BrandPost: One-Policy Framework, Zero Trust, and Ops teamsIn today’s digital era, customers expect information, resources, and services to be readily available from anywhere in the world....
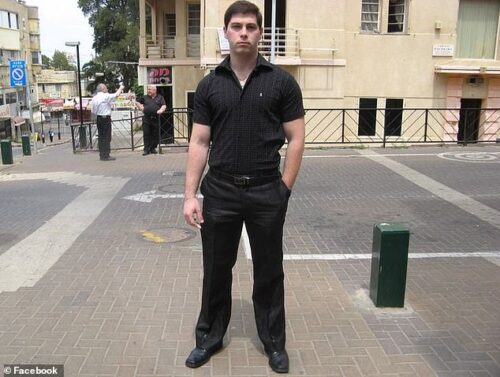
Ukrainian-born Israeli Living in America Arrested for Leaking Weapons Tech to Russia
Ukrainian-born Israeli Living in America Arrested for Leaking Weapons Tech to RussiaIt’s a less complicated story than it probably seems from the headlines. A 35-year-old Israeli...
5 Things Every Organization Should Consider When It Comes to Cybersecurity Awareness Training
5 Things Every Organization Should Consider When It Comes to Cybersecurity Awareness TrainingYour organization is assessing budgets, and security is high on the list. You’ve hired...
Are Technical Support Scams Getting More Advanced?
Are Technical Support Scams Getting More Advanced? Technical support scams (TSS) are responsible for a growing amount of financial losses year after year. Nevertheless, while the...
Samba Issues Security Updates to Patch Multiple High-Severity Vulnerabilities
Samba Issues Security Updates to Patch Multiple High-Severity VulnerabilitiesSamba has released software updates to remediate multiple vulnerabilities that, if successfully exploited, could allow an attacker to...
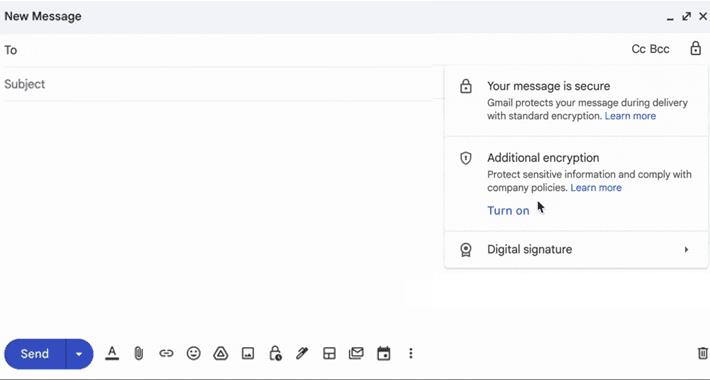
Google Takes Gmail Security to the Next Level with Client-Side Encryption
Google Takes Gmail Security to the Next Level with Client-Side EncryptionGoogle on Friday announced that its client-side encryption for Gmail is in beta for Workspace and...
Fortinet Warns of Active Exploitation of New SSL-VPN Pre-auth RCE Vulnerability
Fortinet Warns of Active Exploitation of New SSL-VPN Pre-auth RCE VulnerabilityFortinet on Monday issued emergency patches for a severe security flaw affecting its FortiOS SSL-VPN product...
Malware Strains Targeting Python and JavaScript Developers Through Official Repositories
Malware Strains Targeting Python and JavaScript Developers Through Official RepositoriesAn active malware campaign is targeting the Python Package Index (PyPI) and npm repositories for Python and...
Reported ECR Public Gallery Issue
Reported ECR Public Gallery IssueInitial Publication Date: 12/13/2022 9:00AM EST On November 14, 2022, a security researcher reported an issue in Amazon Elastic Container Registry (ECR)...
Proofpoint Nabs Illusive, Signaling a Sunset for Deception Tech
Proofpoint Nabs Illusive, Signaling a Sunset for Deception TechContenido de la entradaLeer másProofpoint News Feed
VMware Carbon Black Products and “User-Mode Hooking” Evasion Techniques
VMware Carbon Black Products and “User-Mode Hooking” Evasion TechniquesAttackers are always looking for a single fundamental technique they can use to fully defeat a given security...
December 2022 Patch Tuesday: Get Latest Security Updates from Microsoft and More
December 2022 Patch Tuesday: Get Latest Security Updates from Microsoft and MoreTech giant Microsoft released its last set of monthly security updates for 2022 with fixes for...
A tell-all conversation: The biggest cloud security trends, challenges & solutions
A tell-all conversation: The biggest cloud security trends, challenges & solutionsEXECUTIVE SUMMARY: In this dynamic tell-all conversation, excerpted from The TechArena podcast, VP of Cloud Security...
FuboTV says World Cup streaming outage caused by a cyberattack
FuboTV says World Cup streaming outage caused by a cyberattackFuboTV has confirmed that a streaming outage preventing subscribers from watching the World Cup Qatar 2022 semifinal...
Dozens of cybersecurity efforts included in this year’s US NDAA
Dozens of cybersecurity efforts included in this year’s US NDAALast week, members of the US House of Representatives and Senate reconciled their versions of the annual...
F5 expands security portfolio with App Infrastructure Protection
F5 expands security portfolio with App Infrastructure ProtectionF5 on Thursday announced the launch of F5 Distributed Cloud Services App Infrastructure Protection (AIP), expanding its SaaS-based security...
Microsoft Reclassifies SPNEGO Extended Negotiation Security Vulnerability as ‘Critical’
Microsoft Reclassifies SPNEGO Extended Negotiation Security Vulnerability as 'Critical'Microsoft has revised the severity of a security vulnerability it originally patched in September 2022, upgrading it to "Critical"...
BrandPost: How to Choose Security Technology That Works
BrandPost: How to Choose Security Technology That WorksThe role of a security practitioner is difficult. From operational workflow changes to accommodating the latest application requirement impacting...
Two-Thirds of Security Pros Have Burnt Out in Past Year
Two-Thirds of Security Pros Have Burnt Out in Past YearExcessive workload is the most common contributing factorLeer másExcessive workload is the most common contributing factor
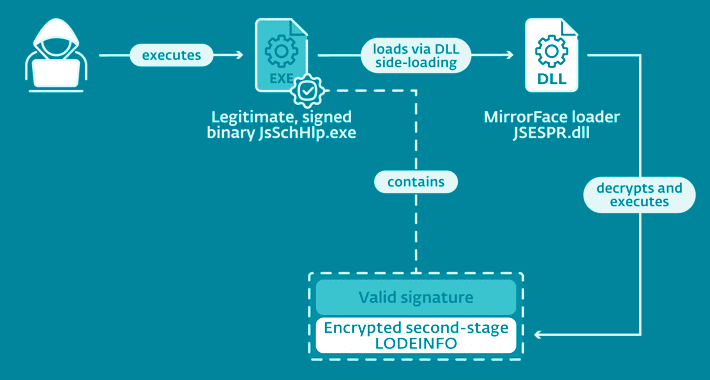
Researchers Uncover MirrorFace Cyber Attacks Targeting Japanese Political Entities
Researchers Uncover MirrorFace Cyber Attacks Targeting Japanese Political EntitiesA Chinese-speaking advanced persistent threat (APT) actor codenamed MirrorFace has been attributed to a spear-phishing campaign targeting Japanese political establishments....
CISA Alert: Veeam Backup and Replication Vulnerabilities Being Exploited in Attacks
CISA Alert: Veeam Backup and Replication Vulnerabilities Being Exploited in AttacksThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two vulnerabilities impacting Veeam Backup & Replication software...
MTTR “not a viable metric” for complex software system reliability and security
MTTR “not a viable metric” for complex software system reliability and securityMean time to resolve (MTTR) isn’t a viable metric for measuring the reliability or security...
Cybersecurity Insights with Contrast CISO David Lindner | 12/16
Cybersecurity Insights with Contrast CISO David Lindner | 12/16 Insight #1 " Lobbying from ITIC has pushed back on the recent OMB 22-18 directive to require...
Minecraft Servers Under Attack: Microsoft Warns About Cross-Platform DDoS Botnet
Minecraft Servers Under Attack: Microsoft Warns About Cross-Platform DDoS BotnetMicrosoft on Thursday flagged a cross-platform botnet that's primarily designed to launch distributed denial-of-service (DDoS) attacks against...
Goodbye SHA-1: NIST Retires 27-Year-Old Widely Used Cryptographic Algorithm
Goodbye SHA-1: NIST Retires 27-Year-Old Widely Used Cryptographic AlgorithmThe U.S. National Institute of Standards and Technology (NIST), an agency within the Department of Commerce, announced Thursday that it's...
S3 Ep113: Pwning the Windows kernel – the crooks who hoodwinked Microsoft [Audio + Text]
S3 Ep113: Pwning the Windows kernel – the crooks who hoodwinked Microsoft [Audio + Text]Return o' the rookit, super-sneaky wireless spyware, credit card skimming, and patches...
Nikesh Arora on Palo Alto’s Approach to Supply Chain Defense
Nikesh Arora on Palo Alto's Approach to Supply Chain DefenseThe $250 million acquisition of Cider Security will allow Palo Alto Networks to secure a piece of...