SOC Prime Threat Bounty — November 2022 Results November ‘22 Publications During the previous month, members of Threat Bounty community submitted 433 rules for publication to...
Day: December 15, 2022
What Is CARTA? Continuous Adaptive Risk and Trust Assessment Explained
What Is CARTA? Continuous Adaptive Risk and Trust Assessment ExplainedDigital services made for consumers are opening up new opportunities and vulnerabilities. With more employees bringing unmanaged...
The Volume and Pace of Cyberattacks is Radically Increasing – Are U.S. Businesses Prepared?
The Volume and Pace of Cyberattacks is Radically Increasing – Are U.S. Businesses Prepared?By Darren Guccione, CEO and Co-Founder, Keeper Security Major shifts in workplace models...
Threats Hackers Pose to the U.S. Military
Threats Hackers Pose to the U.S. MilitaryBy Jacob Hess, CAO & Co-Founder, NGT Academy While digital transformation and adoption of technology are critical to […] The...
Detecting Fantasy Data Wiper Leveraged by Agrius APT in a Supply-Chain Attack
Detecting Fantasy Data Wiper Leveraged by Agrius APT in a Supply-Chain Attack Security experts from ESET revealed a destructive operation launched by Iran-backed Agrius APT to...
Wiz debuts PEACH tenant isolation framework for cloud applications
Wiz debuts PEACH tenant isolation framework for cloud applicationsCloud security vendor Wiz has announced PEACH, a tenant isolation framework for cloud applications designed to evaluate security...
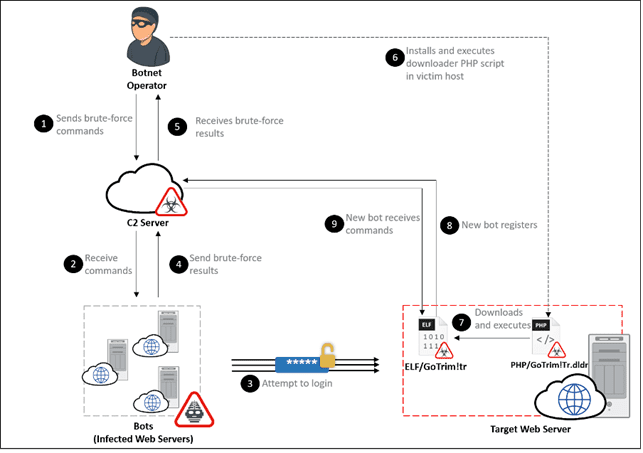
GoTrim botnet actively brute forces WordPress and OpenCart sites
GoTrim botnet actively brute forces WordPress and OpenCart sitesResearchers discovered a new Go-based botnet, dubbed GoTrim, attempting to brute force WordPress websites. Fortinet FortiGuard Labs researchers...
Crooks use HTML smuggling to spread QBot malware via SVG files
Crooks use HTML smuggling to spread QBot malware via SVG filesTalos researchers uncovered a phishing campaign distributing the QBot malware to Windows systems using SVG files....
Social Blade Suffers Data Breach
Social Blade Suffers Data BreachOn December 14th, Social Blade, a statistics website that allows its users to track statistics and measure growth across multiple Social Media...
Signed Microsoft Drivers Used in Attacks Against Businesses
Signed Microsoft Drivers Used in Attacks Against BusinessesIn some cases, the threat actor's intent was to ultimately provide SIM-swapping servicesLeer másIn some cases, the threat actor's...
Platforms Flooded with 144,000 Phishing Packages
Platforms Flooded with 144,000 Phishing PackagesNuGet, PyPi and npm inundated with malicious packagesLeer másNuGet, PyPi and npm inundated with malicious packages
Lacework adds new capabilities to its CSPM solution
Lacework adds new capabilities to its CSPM solutionLacework on Wednesday released new cloud security posture management (CSPM) capabilities, designed to help organizations create custom policies for...
FBI seized 48 domains linked to DDoS-for-Hire service platforms
FBI seized 48 domains linked to DDoS-for-Hire service platformsThe U.S. Department of Justice (DoJ) seized forty-eight domains that offered DDoS-for-Hire Service Platforms to crooks. The U.S....
Over 85% of Attacks Hide in Encrypted Channels
Over 85% of Attacks Hide in Encrypted ChannelsZscaler reveals 20% increase in malicious use of encryptionLeer másZscaler reveals 20% increase in malicious use of encryption
Patch Tuesday Update – Dec 2022
Patch Tuesday Update – Dec 2022‘Tis the Season, and well, this month we continue to get the gift that keeps on giving, Microsoft Patch Tuesday! Yes,...
December 2022 Patch Tuesday: Get Latest Security Updates from Microsoft and More
December 2022 Patch Tuesday: Get Latest Security Updates from Microsoft and MoreTech giant Microsoft released its last set of monthly security updates for 2022 with fixes for...
Cuba ransomware group used Microsoft developer accounts to sign malicious drivers
Cuba ransomware group used Microsoft developer accounts to sign malicious driversMicrosoft suspended several accounts on its hardware developer program that signed malicious drivers used by a...
Building a business case for your SIEM Investment
Building a business case for your SIEM InvestmentChief information security officers (CISOs) are wasting millions of dollars on security products they don’t use – or they...
Feds Hit DDoS-for-Hire Services with 48 Domain Seizures
Feds Hit DDoS-for-Hire Services with 48 Domain SeizuresSix also charged in connection with booter servicesLeer másSix also charged in connection with booter services
Organizations Are Banning TikTok. Should You Do the Same? | Lookout
Organizations Are Banning TikTok. Should You Do the Same? | LookoutIn today's security conscious climate, countries and organizations worldwide waste little time debating whether a risky...
Microsoft Exchange ProxyNotShell vulnerability explained and how to mitigate it
Microsoft Exchange ProxyNotShell vulnerability explained and how to mitigate itLast year, two high severity, easily exploitable Microsoft Exchange vulnerabilities dubbed ProxyLogon and ProxyShell made waves in...
Reimagining Democracy
Reimagining DemocracyLast week, I hosted a two-day workshop on reimagining democracy. The idea was to bring together people from a variety of disciplines who are all...
Microsoft’s EU data boundary plan to take effect Jan. 1
Microsoft’s EU data boundary plan to take effect Jan. 1The plan, which covers Microsoft products and services such as Azure, Power BI, Dynamics 365 and Office...
How Financial Institutions can use PAN verification APIs for Remote Client Onboarding
How Financial Institutions can use PAN verification APIs for Remote Client OnboardingFor FIs, onboarding is a significant new hurdle. Banks still struggle to properly integrate clients...