Google Adds Passkey Support to Chrome for Windows, macOS and AndroidGoogle has officially begun rolling out support for passkeys, the next-generation passwordless login standard, to its stable...
Day: December 12, 2022
USENIX Security ’22 – ‘Pool Inference Attacks On Local Differential Privacy: Quantifying The Privacy Guarantees Of Apple’s Count Mean Sketch In Practice’
USENIX Security ’22 – ‘Pool Inference Attacks On Local Differential Privacy: Quantifying The Privacy Guarantees Of Apple’s Count Mean Sketch In Practice’Complete Title: USENIX Security '22...
Nosey Parker RegEx: A Positive Community Response
Nosey Parker RegEx: A Positive Community ResponseOn December 7, 2022, Praetorian Labs released a regular expression-based (RegEx) version of our Nosey Parker secrets scanning tool (see...
New wind powered land speed world record
New wind powered land speed world recordTeam New Zealand have recorded the fastest wind powered land speed yet. ‘Horonuku’ named by Ngati Whatua Orakei meaning ‘gliding...
BH EU 2022 and BSides London
BH EU 2022 and BSides LondonAs I wandered through the psychedelic chaos of Black Hat Europe 2022, I couldn’t help but feel like I had stumbled...
The LinkedIn Data Scraping Verdict — and Its Reversal
The LinkedIn Data Scraping Verdict — and Its ReversalIn October of last year, a ruling against LinkedIn by The United States Court of Appeals for the...
Top 4 SaaS Security Threats for 2023
Top 4 SaaS Security Threats for 2023With 2022 coming to a close, there is no better time to buckle down and prepare to face the security...
Daniel Stori’s ‘Oracle Downloads Page’
Daniel Stori’s ‘Oracle Downloads Page’ via the webcomic talent of the inimitable Daniel Stori at Turnoff.US! Permalink The post Daniel Stori’s ‘Oracle Downloads Page’ appeared first...
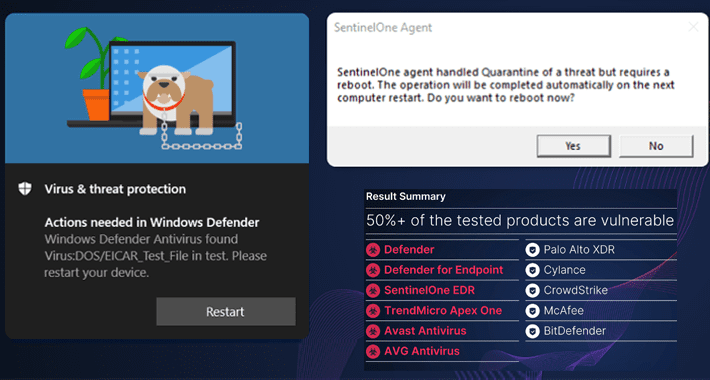
Researchers Demonstrate How EDR and Antivirus Can Be Weaponized Against Users
Researchers Demonstrate How EDR and Antivirus Can Be Weaponized Against UsersHigh-severity security vulnerabilities have been disclosed in different endpoint detection and response (EDR) and antivirus (AV)...
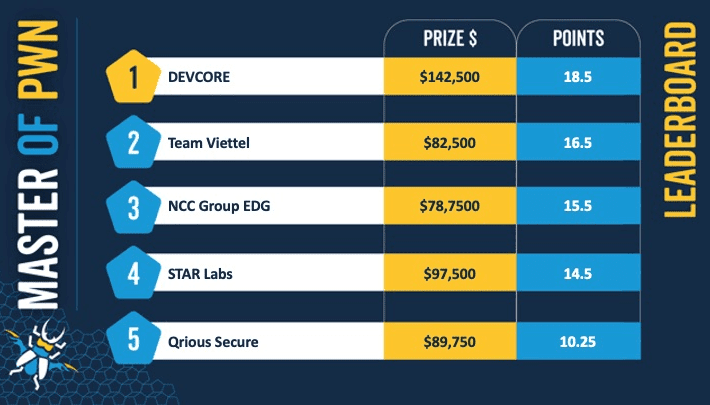
Pwn2Own Toronto: 54 hacks, 63 new bugs, $1 million in bounties
Pwn2Own Toronto: 54 hacks, 63 new bugs, $1 million in bountiesThat's a mean average of $15,710 per bug... and 63 fewer bugs out there for crooks...
Sourcepass Acquires CCSI, A Leading Enterprise IT Services Provider
Sourcepass Acquires CCSI, A Leading Enterprise IT Services ProviderCCSI motivated by Sourcepass’ innovative service delivery model that leverages advanced AI and RPA workflows Sourcepass announced its...
USENIX Security ’22 – ‘Poisoning Attacks to Local Differential Privacy Protocols for Key-Value Data’
USENIX Security ’22 – ‘Poisoning Attacks to Local Differential Privacy Protocols for Key-Value Data’Complete Title: USENIX Security '22 - Yongji Wu, Xiaoyu Cao, Jinyuan Jia, Neil...
US HHS warns healthcare orgs of Royal Ransomware attacks
US HHS warns healthcare orgs of Royal Ransomware attacksThe US Department of Health and Human Services (HHS) warns healthcare organizations of Royal ransomware attacks. The human-operated...
Log4Shell Vulnerabilities Still Plague Organizations
Log4Shell Vulnerabilities Still Plague Organizations Almost exactly one year after Log4Shell sent security teams scrambling to patch, more than seven in 10 (72%) of organizations are...
At least 4,460 vulnerable Pulse Connect Secure hosts are exposed to the Internet
At least 4,460 vulnerable Pulse Connect Secure hosts are exposed to the InternetCensys researchers warn of more than 4,000 vulnerable Pulse Connect Secure hosts exposed to...
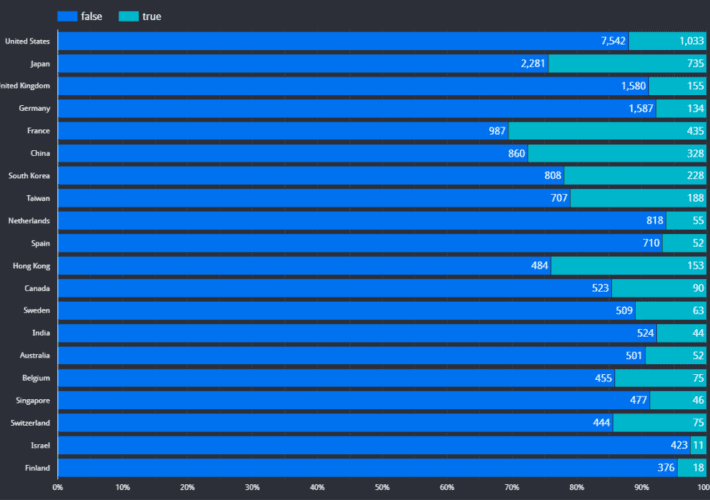
MuddyWater APT group is back with updated TTPs
MuddyWater APT group is back with updated TTPsThe Iran-linked MuddyWater APT is targeting countries in the Middle East as well as Central and West Asia in a new...
Security Affairs newsletter Round 397
Security Affairs newsletter Round 397A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs free for you in...
Pwn2Own Toronto 2022 Day 4: $989K awarded for 63 unique zero-days
Pwn2Own Toronto 2022 Day 4: $989K awarded for 63 unique zero-daysThe Pwn2Own Toronto 2022 is ended, and the participants earned a total of $989,750 for 63...
Government to Fund Security Studies for Hundreds of Students
Government to Fund Security Studies for Hundreds of StudentsLatest move shows urgent need to nurture skills pipelineLeer másLatest move shows urgent need to nurture skills pipeline
Cobalt Mirage Affiliate Uses GitHub to Relay Drokbk Malware Instructions
Cobalt Mirage Affiliate Uses GitHub to Relay Drokbk Malware InstructionsSecureworks said the malicious code is written in .NET and comprises a dropper and a payloadLeer másSecureworks...
Software Supply Chain Attacks Leveraging Open-Sources Repos Growing
Software Supply Chain Attacks Leveraging Open-Sources Repos GrowingReversingLabs found an increasing number of malicious packages in three popular repositoriesLeer másReversingLabs found an increasing number of malicious...
#BHEU: UK Government Calls for Industry Input on its Cybersecurity Strategy
#BHEU: UK Government Calls for Industry Input on its Cybersecurity StrategyA DCMS official sets out the UK government's cybersecurity strategy during Black Hat Europe 2022Leer másA...
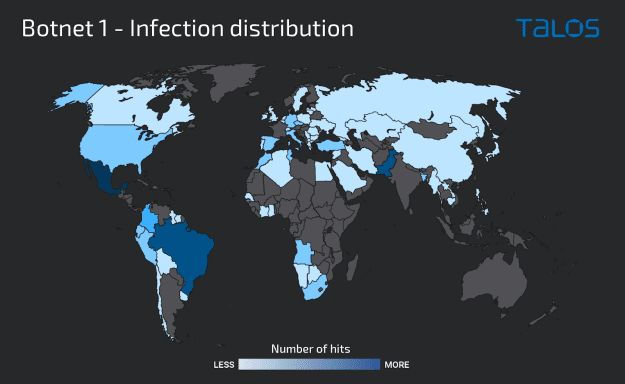
Truebot Malware Activity Increases With Possible Evil Corp Connections
Truebot Malware Activity Increases With Possible Evil Corp ConnectionsThe campaigns observed by Cisco Talos have resulted in the creation of two botnetsLeer másThe campaigns observed by...
BEC Attacks Expand Beyond Email and Toward Mobile Devices
BEC Attacks Expand Beyond Email and Toward Mobile DevicesScammers typically obtain mobile numbers from data breaches, social media and data brokersLeer másScammers typically obtain mobile numbers...
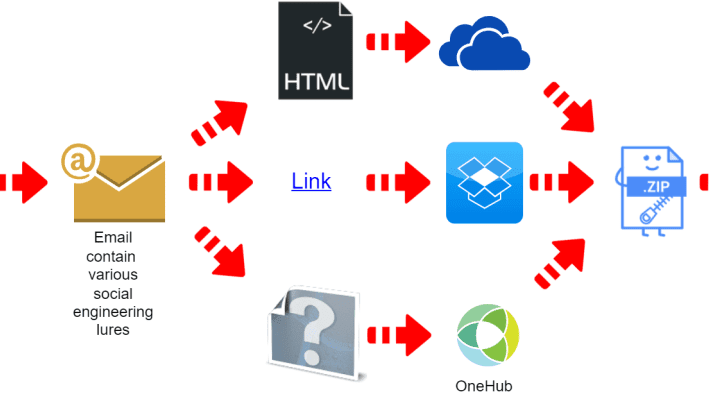
TrueBot infections were observed in Clop ransomware attacks
TrueBot infections were observed in Clop ransomware attacksResearchers reported an increase in TrueBot infections, attackers have shifted from using malicious emails as their primary delivery method to other...
North Korean Hackers Impersonate Researchers to Steal Intel
North Korean Hackers Impersonate Researchers to Steal IntelReport associates new intelligence-gathering tactic with Kimsuky groupLeer másReport associates new intelligence-gathering tactic with Kimsuky group
Researchers Find 63 Zero-Day Bugs at Latest Pwn2Own
Researchers Find 63 Zero-Day Bugs at Latest Pwn2OwnCompetition awards winning participants nearly $1mLeer másCompetition awards winning participants nearly $1m
Royal Ransomware Targets US Healthcare
Royal Ransomware Targets US HealthcareRequested ransom payment demands ranged from $250,000 to over $2mLeer másRequested ransom payment demands ranged from $250,000 to over $2m
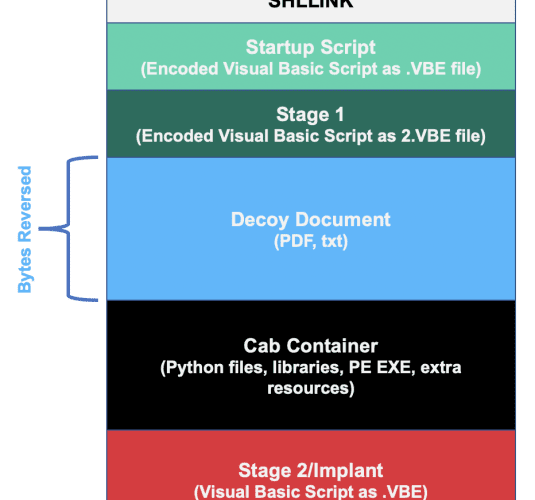
Evilnum group targets legal entities with a new Janicab variant
Evilnum group targets legal entities with a new Janicab variantA hack-for-hire group dubbed Evilnum is targeting travel and financial entities with the new Janicab malware variant. Kaspersky...
Transitive Dependencies Account for 95% of Bugs
Transitive Dependencies Account for 95% of BugsEndor Labs warns of dangerous complexities in open sourceLeer másEndor Labs warns of dangerous complexities in open source