LockBit Dominates Ransomware Campaigns in 2022: Deep InstinctThe figures come from the 2022 Interim Cyber Threat Report by Deep InstinctLeer másThe figures come from the 2022...
Month: November 2022
CISA Publishes Multi-Factor Authentication Guidelines to Tackle Phishing
CISA Publishes Multi-Factor Authentication Guidelines to Tackle PhishingThe guidelines describe methods threat actors use to steal MFA credentials and how to defend against themLeer másThe guidelines...
Osaka Hospital Halts Services After Ransomware Attack
Osaka Hospital Halts Services After Ransomware AttackEmergency operations are continuing, but the hospital system failed and cannot be accessedLeer másEmergency operations are continuing, but the hospital...
Instagram Bug Causes Users’ Accounts Suspension
Instagram Bug Causes Users’ Accounts SuspensionInstagram users might have taken the greatest Halloween scare ever yesterday after they found themselves unable to access their accounts for...
Samsung Galaxy Store flaw could have allowed installing malicious apps on target devices
Samsung Galaxy Store flaw could have allowed installing malicious apps on target devicesA security flaw in the Galaxy Store app for Samsung devices could have potentially...
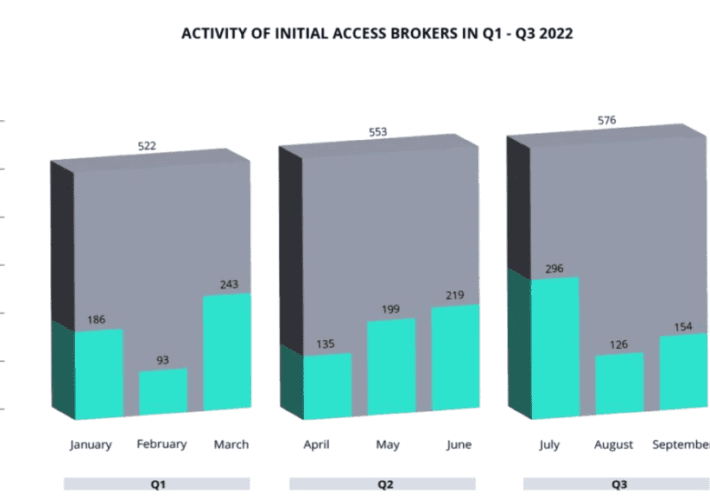
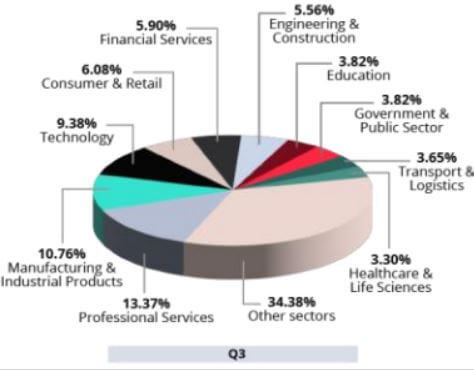
Ransomware activity and network access sales in Q3 2022
Ransomware activity and network access sales in Q3 2022Ransomware activity report: Threat actors are selling access to hundreds of organizations, with a cumulative requested price of...
Multiple Vulnerabilities Discovered in Juniper Junos OS
Multiple Vulnerabilities Discovered in Juniper Junos OSA series of severe security flaws have been disclosed to affect Juniper Networks devices, some of which might end up being...
Experts warn of critical RCE in ConnectWise Server Backup Solution
Experts warn of critical RCE in ConnectWise Server Backup SolutionConnectWise has addressed a critical remote code execution vulnerability impacting Recover and R1Soft Server Backup Manager (SBM)....
Denmark’s Journey to Becoming the Most Cyber-Secure Country
Denmark’s Journey to Becoming the Most Cyber-Secure CountryDenmark is one of the most digitalized countries worldwide, with technologies used in the private and public sectors as...
$4 Million in Exchange for Access to 576 Corporate Networks
$4 Million in Exchange for Access to 576 Corporate NetworksAccording to a new report published by cybersecurity researchers, hackers are selling access to 576 corporate networks...
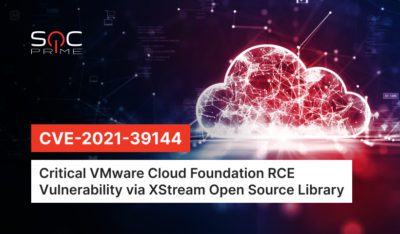
Detect CVE-2021-39144: Critical Remote Code Execution Vulnerability in VMware Cloud Foundation via XStream Open Source Library
Detect CVE-2021-39144: Critical Remote Code Execution Vulnerability in VMware Cloud Foundation via XStream Open Source Library Another day, another exploit emerges in the wild to cause...
Actively exploited Windows MoTW zero-day gets unofficial patch
Actively exploited Windows MoTW zero-day gets unofficial patchA free unofficial patch has been released for an actively exploited zero-day that allows files signed with malformed signatures...
Iran’s Digital Surveillance Tools Leaked
Iran’s Digital Surveillance Tools LeakedIt’s Iran’s turn to have its digital surveillance tools leaked: According to these internal documents, SIAM is a computer system that works...
New Azov data wiper tries to frame researchers and BleepingComputer
New Azov data wiper tries to frame researchers and BleepingComputerA new and destructive 'Azov Ransomware' data wiper is being heavily distributed through pirated software, key generators,...
Google ad for GIMP.org served info-stealing malware via lookalike site
Google ad for GIMP.org served info-stealing malware via lookalike siteSearching for 'GIMP' on Google as recently as last week would show visitors an ad for 'GIMP.org,' the official website of...
The Worst Black Friday and Cyber Monday Scams – And How to Avoid Them
The Worst Black Friday and Cyber Monday Scams – And How to Avoid Them On Black Friday and Cyber Monday, the deals roll out. So do...
Microsoft fixes critical RCE flaw affecting Azure Cosmos DB
Microsoft fixes critical RCE flaw affecting Azure Cosmos DBAnalysts at Orca Security have found a critical vulnerability affecting Azure Cosmos DB that allowed unauthenticated read and...
Using Regex to Implement Passphrases in Your Active Directory
Using Regex to Implement Passphrases in Your Active DirectoryPassphrases provide a superior type of password for authentication as they allow you to create strong passwords you...
New SandStrike spyware infects Android devices via malicious VPN app
New SandStrike spyware infects Android devices via malicious VPN appThreat actors are using a newly discovered spyware known as SandStrike and delivered via a malicious VPN...
OpenSSL fixes two high severity vulnerabilities, what you need to know
OpenSSL fixes two high severity vulnerabilities, what you need to knowThe OpenSSL Project has patched two high-severity security flaws in its open-source cryptographic library used to...
For $4M, hackers buy access to corporate networks; possibly yours
For $4M, hackers buy access to corporate networks; possibly yoursEXECUTIVE SUMMARY: Cyber criminals are selling access to more than 500 corporate networks worldwide. For the price...
Should Australia’s Medibank Give in to Extortionists?
Should Australia's Medibank Give in to Extortionists?Australia's Most Severe Cybercriminal Incident Has No Good SolutionShould Australia's Medibank health insurer pay extortionists to prevent the release of...
Hacking with your Browser
Hacking with your BrowserToday I rebuilt my Windows 7 partition. Amidst flurry of backing up I forgot to save my Firefox profiles. I figured this was...
Metasploit Buyout
Metasploit BuyoutToday HD Moore and Rapid7 announced that Rapid7 has purchased the Metasploit Framework Project. The speculation around this has taken the pentest and vulnerability scanning...
Network Pentest Lab
Network Pentest LabRemember those good ole days in the sandbox? Where you threw stuff around learned where the sand goes and… doesn’t go? Well we’ve graduated...
New to reversing? The differences between IDA Pro, ImmDBG and OllyDBG
New to reversing? The differences between IDA Pro, ImmDBG and OllyDBGIntroduction In this blog post we will look at some of the differences between a several...
More API Inventory Auditing Necessary to Limit Incidents
More API Inventory Auditing Necessary to Limit Incidents The API industry is booming. Development of application programming interfaces has outpaced many areas of IT as APIs...
Hacking with your Browser
Hacking with your BrowserToday I rebuilt my Windows 7 partition. Amidst flurry of backing up I forgot to save my Firefox profiles. I figured this was...
Metasploit Buyout
Metasploit BuyoutToday HD Moore and Rapid7 announced that Rapid7 has purchased the Metasploit Framework Project. The speculation around this has taken the pentest and vulnerability scanning...
Network Pentest Lab
Network Pentest LabRemember those good ole days in the sandbox? Where you threw stuff around learned where the sand goes and… doesn’t go? Well we’ve graduated...