K94221585: iControl SOAP vulnerability CVE-2022-41622iControl SOAP vulnerability CVE-2022-41622 Security Advisory Security Advisory Description BIG-IP and BIG-IQ are vulnerable to cross-site request forgery (CSRF) attacks through iControl...
Day: November 20, 2022
K44070243: OpenSSL vulnerability CVE-2019-1549
K44070243: OpenSSL vulnerability CVE-2019-1549OpenSSL vulnerability CVE-2019-1549 Security Advisory Security Advisory Description OpenSSL 1.1.1 introduced a rewritten random number generator (RNG). This was intended to include protection...
OpenSSL Security Advisories – November 2022
OpenSSL Security Advisories - November 2022Initial Publication Date: 2022/11/01 09:00 PDT AWS is aware of the recently reported issues regarding OpenSSL 3.0 (CVE-2022-3602 and CVE-2022-3786). AWS...
K94221585: iControl SOAP vulnerability CVE-2022-41622
K94221585: iControl SOAP vulnerability CVE-2022-41622iControl SOAP vulnerability CVE-2022-41622 Security Advisory Security Advisory Description BIG-IP and BIG-IQ are vulnerable to cross-site request forgery (CSRF) attacks through iControl...
Cyberspace ‘a battleground’ as reports of cybercrime in Australia jump 13%
Cyberspace ‘a battleground’ as reports of cybercrime in Australia jump 13%Fraud, online shopping and banking among most commonly reported crimes, but ransomware ‘most destructive’, ASD says...
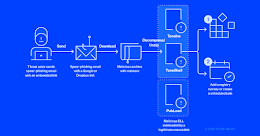
DOJ Charges 10 with BEC Targeting Federal Health Program
DOJ Charges 10 with BEC Targeting Federal Health ProgramSuspects Allegedly Caused More Than $11 Million in Total LossesThe U.S. Department of Justice on Friday charged 10...
New attacks use Windows security bypass zero-day to drop malware
New attacks use Windows security bypass zero-day to drop malwareNew phishing attacks use a Windows zero-day vulnerability to drop the Qbot malware without displaying Mark of...
Medibank hackers release 1,500 more patient records on dark web, including mental health data
Medibank hackers release 1,500 more patient records on dark web, including mental health dataCompany says leak includes details on chronic conditions such as heart disease and...
‘Welcome Back’—Donald Trump returns to Twitter after Elon Musk’s poll
'Welcome Back'—Donald Trump returns to Twitter after Elon Musk's pollIn a surprising move, Twitter has lifted the "permanent suspension" of former U.S. President Donald Trump's account. The move...
Atlassian Releases Patches for Critical Flaws Affecting Crowd and Bitbucket Products
Atlassian Releases Patches for Critical Flaws Affecting Crowd and Bitbucket ProductsAustralian software company Atlassian has rolled out security updates to address two critical flaws affecting Bitbucket Server, Data...
Chinese ‘Mustang Panda’ Hackers Actively Targeting Governments Worldwide
Chinese 'Mustang Panda' Hackers Actively Targeting Governments WorldwideA notorious advanced persistent threat actor known as Mustang Panda has been linked to a spate of spear-phishing attacks targeting government,...
Security Recruiter Directory
Security Recruiter DirectoryLooking for a qualified candidate or new job? CSO's security recruiter directory is your one-stop shop. The recruiters listed below can help you find...
Different Professional Backgrounds Are Key to a Successful Compliance Team
Different Professional Backgrounds Are Key to a Successful Compliance TeamHiring a compliance team with different professional backgrounds is key to building your compliance department. Here’s why....
Microsoft Warns of Hackers Using Google Ads to Distribute Royal Ransomware
Microsoft Warns of Hackers Using Google Ads to Distribute Royal RansomwareA developing threat activity cluster has been found using Google Ads in one of its campaigns...
CISA, NSA, ODNI Publish Software Supply Chain Guidelines For Customers
CISA, NSA, ODNI Publish Software Supply Chain Guidelines For CustomersThe come after the August release of guidance for developers and the October one for suppliersLeer másThe...
Tor vs. VPN: Which should you choose?
Tor vs. VPN: Which should you choose?Both Tor and a VPN can greatly help you keep prying eyes away from your online life, but they’re also...
Holiday Shopping Online: Safety on Black Friday, Cyber Monday
Holiday Shopping Online: Safety on Black Friday, Cyber MondayWhat are the latest online security tips as we head into another holiday season? What’s the best cyber...
Indian Government Publishes Draft of Digital Personal Data Protection Bill 2022
Indian Government Publishes Draft of Digital Personal Data Protection Bill 2022The Indian government on Friday released a draft version of the much-awaited data protection regulation, making...