Digital Trust Digest: This Week’s Must-Know News (Nov. 14-18)The Digital Trust Digest is a curated overview of the week’s top cybersecurity news. Here's what happened the...
Day: November 18, 2022
BSidesKC 2022 – Grant Shanklin’s ‘Trouble With The Troubleshooter; A Primer On CVE-2022-30190’
BSidesKC 2022 – Grant Shanklin’s ‘Trouble With The Troubleshooter; A Primer On CVE-2022-30190’Our sincere thanks to BSidesKC 2022 for publishing their outstanding conference videos on the...
S3 Ep109: How one leaked email password could drain your business [Audio + Transcript]
S3 Ep109: How one leaked email password could drain your business [Audio + Transcript]Latest episode - listen now! Cybersecurity news plus loads of great advice...Leer másNaked...
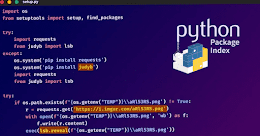
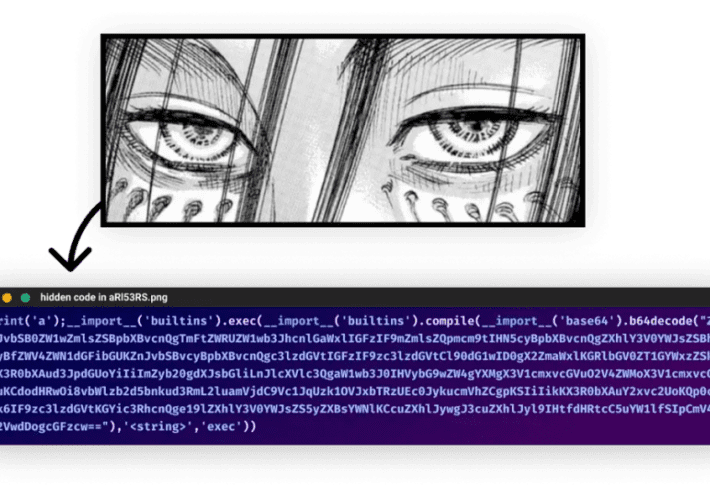
W4SP Stealer Constantly Targeting Python Developers in Ongoing Supply Chain Attack
W4SP Stealer Constantly Targeting Python Developers in Ongoing Supply Chain AttackAn ongoing supply chain attack has been leveraging malicious Python packages to distribute malware called W4SP...
Threat hunting with MITRE ATT&CK and Wazuh
Threat hunting with MITRE ATT&CK and WazuhThreat hunting is the process of looking for malicious activity and its artifacts in a computer system or network. Threat...
Hive Ransomware Attackers Extorted $100 Million from Over 1,300 Companies Worldwide
Hive Ransomware Attackers Extorted $100 Million from Over 1,300 Companies WorldwideThe threat actors behind the Hive ransomware-as-a-service (RaaS) scheme have launched attacks against over 1,300 companies...
Meta Reportedly Fires Dozens of Employees for Hijacking Users’ Facebook and Instagram Accounts
Meta Reportedly Fires Dozens of Employees for Hijacking Users' Facebook and Instagram AccountsMeta Platforms is said to have fired or disciplined over two dozen employees and...
LodaRAT Malware Resurfaces with New Variants Employing Updated Functionalities
LodaRAT Malware Resurfaces with New Variants Employing Updated FunctionalitiesThe LodaRAT malware has resurfaced with new variants that are being deployed in conjunction with other sophisticated malware,...
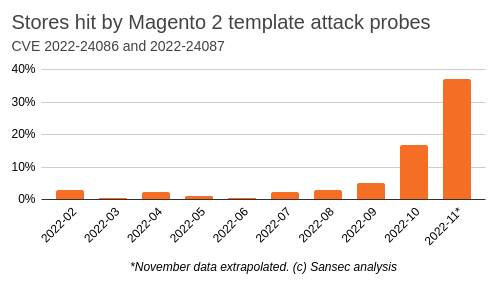
Magento and Adobe Commerce websites under attack
Magento and Adobe Commerce websites under attackResearchers warn of a surge in cyberattacks targeting CVE-2022-24086, a pre-authentication issue impacting Adobe Commerce and Magento stores. In September 2022,...
Two public schools in Michigan hit by a ransomware attack
Two public schools in Michigan hit by a ransomware attackPublic schools in two Michigan counties were forced to halt their activities, including the lessons, after a...
Russian Duo Indicted Over E-Book Piracy
Russian Duo Indicted Over E-Book PiracySt Petersburg couple were arrested in ArgentinaLeer másSt Petersburg couple were arrested in Argentina
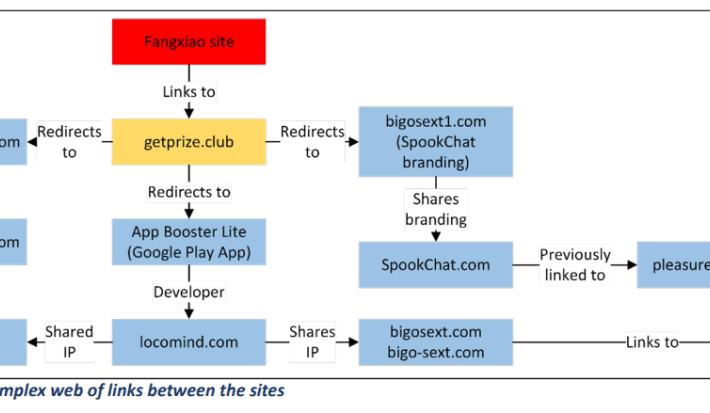
China-based Fangxiao group behind a long-running phishing campaign
China-based Fangxiao group behind a long-running phishing campaignA China-based financially motivated group, tracked as Fangxiao, is behind a large-scale phishing campaign dating back as far as 2019....
Telemedicine Companies Jeopardize Patients` Private Data
Telemedicine Companies Jeopardize Patients` Private DataWebsites offering treatment and support for people dealing with substance use disorders should try harder to protect patients’ data privacy. After conducting...
Noname Security releases Recon attack simulator
Noname Security releases Recon attack simulatorAs breaches increase and companies scramble to go from a defensive to an offensive approach, API-focused Noname Security has launched Recon,...
Python Developers Targeted by W4SP Stealer in an Ongoing Supply Chain Attack
Python Developers Targeted by W4SP Stealer in an Ongoing Supply Chain AttackMalicious Python packages have been used in an ongoing supply chain attack to spread the...
New Shopping Phishing Scam Uses URI Fragmentation to Target U.S. and Canadian Users
New Shopping Phishing Scam Uses URI Fragmentation to Target U.S. and Canadian UsersA highly efficient phishing kit spreads the most among users from the United States...
Heimdal® Recognized as Top Cybersecurity Software by Software Advice in 2022
Heimdal® Recognized as Top Cybersecurity Software by Software Advice in 2022Copenhagen, November 18, 2022 — Heimdal® announced today that Heimdal® Threat Prevention has been recently recognized as a Top Cybersecurity...
Hive Ransomware extorted over $100M in ransom payments from over 1,300 companies
Hive Ransomware extorted over $100M in ransom payments from over 1,300 companiesHive ransomware operators have extorted over $100 million in ransom payments from over 1,300 companies...
Ongoing supply chain attack targets Python developers with WASP Stealer
Ongoing supply chain attack targets Python developers with WASP StealerA threat actor tracked as WASP is behind an ongoing supply chain attack targeting Python developers with...
FBI Reveals: Hive Ransomware Extorted $100M from 1,300 Companies
FBI Reveals: Hive Ransomware Extorted $100M from 1,300 CompaniesThe Federal Bureau of Investigation (FBI) stated that as of November 2022, the infamous Hive ransomware gang has...
What Is Patch Management as a Service? (PMaaS)
What Is Patch Management as a Service? (PMaaS)In today’s business world, data security is more important than ever. With the rise of data breaches and cyberattacks,...
Privileged Access Management (PAM) – PAM in the Cloud vs PAM for the Cloud
Privileged Access Management (PAM) – PAM in the Cloud vs PAM for the CloudIT security teams have always been tasked with securing the on-premises infrastructure or...
4,500 Emails Exposed by AI-powered Platform
4,500 Emails Exposed by AI-powered PlatformAn unprotected Cassandra instance containing user emails, SIP tokens, and physical locations was discovered on October 6th by Cybernews researchers. The...
QBot phishing abuses Windows Control Panel EXE to infect devices
QBot phishing abuses Windows Control Panel EXE to infect devicesPhishing emails distributing the QBot malware are using a DLL hijacking flaw in the Windows 10 Control...
Shop But Don’t Click: Analyst Warns Thanksgiving Con Artists Lurking In Consumer Inboxes
Shop But Don’t Click: Analyst Warns Thanksgiving Con Artists Lurking In Consumer InboxesAccording to Avanan, cybercriminals don’t need an excuse to try and con people out...
Blockchain in Retail Will Soon Become a Universal Concept- Explore the Scenario
Blockchain in Retail Will Soon Become a Universal Concept- Explore the ScenarioBy Koyel Ghosh, Sr. Specialist Content Writer, Allied Market Research, India In the last few...
Top Legacy Active Directory Infrastructure Vulnerabilities and How Attackers See Them
Top Legacy Active Directory Infrastructure Vulnerabilities and How Attackers See ThemBy Tammy Mindel, Security Product Manager at Semperis Microsoft Active Directory (AD) has become a highly...
FBI: Hive ransomware extorted $100M from over 1,300 victims
FBI: Hive ransomware extorted $100M from over 1,300 victimsThe Federal Bureau of Investigation (FBI) said today that the notorious Hive ransomware gang has successfully extorted roughly...
The Numbers Are In: Identity-Based Attacks (Still) Reign Supreme in 2022
The Numbers Are In: Identity-Based Attacks (Still) Reign Supreme in 2022By Greg Notch, CISO, Expel The list of challenges security professionals face will not let up,...
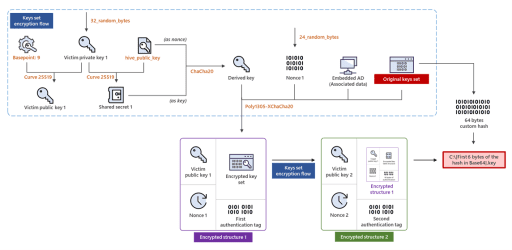
Previously unidentified ARCrypter ransomware expands worldwide
Previously unidentified ARCrypter ransomware expands worldwideA previously unknown 'ARCrypter' ransomware that compromised key organizations in Latin America is now expanding its attacks worldwide. [...]Leer másBleepingComputerA previously...