Microsoft fixes critical RCE flaw affecting Azure Cosmos DBAnalysts at Orca Security have found a critical vulnerability affecting Azure Cosmos DB that allowed unauthenticated read and...
Day: November 1, 2022
Using Regex to Implement Passphrases in Your Active Directory
Using Regex to Implement Passphrases in Your Active DirectoryPassphrases provide a superior type of password for authentication as they allow you to create strong passwords you...
New SandStrike spyware infects Android devices via malicious VPN app
New SandStrike spyware infects Android devices via malicious VPN appThreat actors are using a newly discovered spyware known as SandStrike and delivered via a malicious VPN...
OpenSSL fixes two high severity vulnerabilities, what you need to know
OpenSSL fixes two high severity vulnerabilities, what you need to knowThe OpenSSL Project has patched two high-severity security flaws in its open-source cryptographic library used to...
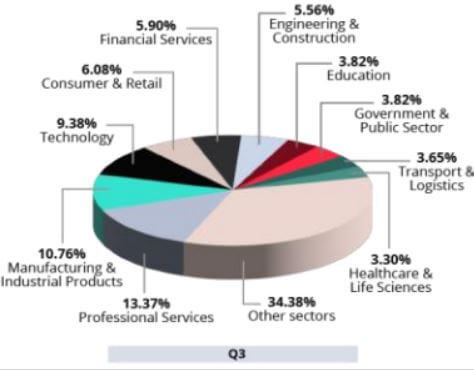
For $4M, hackers buy access to corporate networks; possibly yours
For $4M, hackers buy access to corporate networks; possibly yoursEXECUTIVE SUMMARY: Cyber criminals are selling access to more than 500 corporate networks worldwide. For the price...
Should Australia’s Medibank Give in to Extortionists?
Should Australia's Medibank Give in to Extortionists?Australia's Most Severe Cybercriminal Incident Has No Good SolutionShould Australia's Medibank health insurer pay extortionists to prevent the release of...
Hacking with your Browser
Hacking with your BrowserToday I rebuilt my Windows 7 partition. Amidst flurry of backing up I forgot to save my Firefox profiles. I figured this was...
Metasploit Buyout
Metasploit BuyoutToday HD Moore and Rapid7 announced that Rapid7 has purchased the Metasploit Framework Project. The speculation around this has taken the pentest and vulnerability scanning...
Network Pentest Lab
Network Pentest LabRemember those good ole days in the sandbox? Where you threw stuff around learned where the sand goes and… doesn’t go? Well we’ve graduated...
New to reversing? The differences between IDA Pro, ImmDBG and OllyDBG
New to reversing? The differences between IDA Pro, ImmDBG and OllyDBGIntroduction In this blog post we will look at some of the differences between a several...
More API Inventory Auditing Necessary to Limit Incidents
More API Inventory Auditing Necessary to Limit Incidents The API industry is booming. Development of application programming interfaces has outpaced many areas of IT as APIs...
Hacking with your Browser
Hacking with your BrowserToday I rebuilt my Windows 7 partition. Amidst flurry of backing up I forgot to save my Firefox profiles. I figured this was...
Metasploit Buyout
Metasploit BuyoutToday HD Moore and Rapid7 announced that Rapid7 has purchased the Metasploit Framework Project. The speculation around this has taken the pentest and vulnerability scanning...
Network Pentest Lab
Network Pentest LabRemember those good ole days in the sandbox? Where you threw stuff around learned where the sand goes and… doesn’t go? Well we’ve graduated...
New to reversing? The differences between IDA Pro, ImmDBG and OllyDBG
New to reversing? The differences between IDA Pro, ImmDBG and OllyDBGIntroduction In this blog post we will look at some of the differences between a several...
Secure Software Development Compliance for OMB’s M-22-18 Memo | Code Patrol Podcast | Contrast Security
Secure Software Development Compliance for OMB’s M-22-18 Memo | Code Patrol Podcast | Contrast Security Do you swear to tell the truth about your secure software...
A False Assumption of Trust in Business APIs
A False Assumption of Trust in Business APIs Digital business is driving significant levels of growth and effectiveness for companies in a way that is becoming...
More API Inventory Auditing Necessary to Limit Incidents
More API Inventory Auditing Necessary to Limit Incidents The API industry is booming. Development of application programming interfaces has outpaced many areas of IT as APIs...
SuperTravel Protects its Proprietary Data From Scraping With DataDome
SuperTravel Protects its Proprietary Data From Scraping With DataDomeAfter testing multiple bot protection technologies, SuperTravel selected DataDome to protect it's valuable content from malicious actors. The...
How to protect against CVE-2022-42889 | Text4Shell vulnerability protection | Contrast Security
How to protect against CVE-2022-42889 | Text4Shell vulnerability protection | Contrast Security A new Common Vulnerability and Exposure (CVE) — CVE-2022-42889, aka Text4Shell — was recently...
Hard Truths About Driving a Security Mindset
Hard Truths About Driving a Security Mindset Working in cybersecurity as a consultant can be eye-opening. We regularly see clients who, despite knowing they need cybersecurity,...
Secure Software Development Compliance for OMB’s M-22-18 Memo | Code Patrol Podcast | Contrast Security
Secure Software Development Compliance for OMB’s M-22-18 Memo | Code Patrol Podcast | Contrast Security Do you swear to tell the truth about your secure software...
A False Assumption of Trust in Business APIs
A False Assumption of Trust in Business APIs Digital business is driving significant levels of growth and effectiveness for companies in a way that is becoming...
SuperTravel Protects its Proprietary Data From Scraping With DataDome
SuperTravel Protects its Proprietary Data From Scraping With DataDomeAfter testing multiple bot protection technologies, SuperTravel selected DataDome to protect it's valuable content from malicious actors. The...
How to protect against CVE-2022-42889 | Text4Shell vulnerability protection | Contrast Security
How to protect against CVE-2022-42889 | Text4Shell vulnerability protection | Contrast Security A new Common Vulnerability and Exposure (CVE) — CVE-2022-42889, aka Text4Shell — was recently...
Hard Truths About Driving a Security Mindset
Hard Truths About Driving a Security Mindset Working in cybersecurity as a consultant can be eye-opening. We regularly see clients who, despite knowing they need cybersecurity,...
BSidesLV 2022 Lucky13 I Am The Cavalry (IATC) – Josh Corman’s ‘Day One Feedback Loop: What Did We Hear?’
BSidesLV 2022 Lucky13 I Am The Cavalry (IATC) – Josh Corman’s ‘Day One Feedback Loop: What Did We Hear?’Our sincere thanks to BSidesLV for publishing their...
Chinese Tech: Banned in DC, but not in the States
Chinese Tech: Banned in DC, but not in the States There’s a massive loophole in the federal ban on Chinese technology from sus firms such as Huawei...
What You Should Know about the New OpenSSL Vulnerability
What You Should Know about the New OpenSSL VulnerabilityFind out how to detect which OpenSSL version you’re running and if your organization is exposed to the...
Accused ‘Raccoon’ Malware Developer Fled Ukraine After Russian Invasion
Accused ‘Raccoon’ Malware Developer Fled Ukraine After Russian InvasionA 26-year-old Ukrainian man is awaiting extradition to the United States on charges that he acted as a...