#WSPD Creating hope through action with The Jordan Legacy *TW: Mentions Suicide Our passion for protecting people doesn’t stop with online safety. We deeply care for...
Day: September 21, 2022
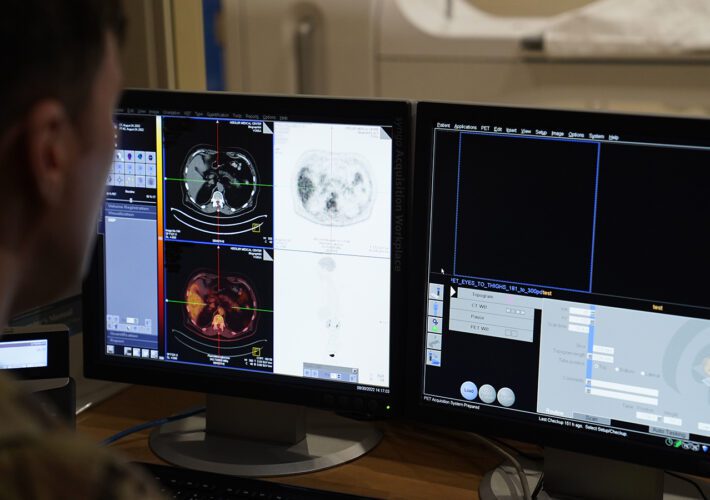
The cyberattack with the most negative impact to patient care: ransomware
The cyberattack with the most negative impact to patient care: ransomwareContenido de la entradaLeer másProofpoint News Feed
Windows 11 22H2 is released, here are the new features
Windows 11 22H2 is released, here are the new featuresMicrosoft has released the next version of Windows 11 called "22H2," otherwise known as the Windows 11 2022...
‘This is the jungle’: Law enforcement slowly waking up to the threat of DeFi exploits
‘This is the jungle’: Law enforcement slowly waking up to the threat of DeFi exploitsContenido de la entradaLeer másProofpoint News Feed
Hive ransomware claims attack on New York Racing Association
Hive ransomware claims attack on New York Racing AssociationThe Hive ransomware operation claimed responsibility for an attack on the New York Racing Association (NYRA), which previously...
Hybrid Cloud Changes the Game for Security
Hybrid Cloud Changes the Game for SecurityEmbracing New Technologies to Gain Agility, Rapid App Delivery Is Good BusinessEmbracing new technologies to gain benefits such as increased...
‘Cyber insecurity’ in healthcare is leading to increased patient mortality rates
‘Cyber insecurity’ in healthcare is leading to increased patient mortality ratesContenido de la entradaLeer másProofpoint News Feed
Phishing scheme targeting Mideast researchers uses ‘herd mentality’ approach to dupe victims
Phishing scheme targeting Mideast researchers uses 'herd mentality' approach to dupe victimsContenido de la entradaLeer másProofpoint News Feed
Windows 11 22H2 adds kernel exploit protection to security baseline
Windows 11 22H2 adds kernel exploit protection to security baselineMicrosoft has released the final version of security configuration baseline settings for Windows 11, version 22H2, downloadable...
Windows 10 KB5017380 preview update released with new FIDO2 features
Windows 10 KB5017380 preview update released with new FIDO2 featuresMicrosoft has released the optional KB5017380 Preview cumulative update for Windows 10 20H2, Windows 10 21H1, and...
A Post-exploitation Look at Coinminers Abusing WebLogic Vulnerabilities
A Post-exploitation Look at Coinminers Abusing WebLogic VulnerabilitiesThis blog entry details how Trend Micro Cloud One™ – Workload Security and Trend Micro Vision One™ effectively detected...
What Industry Is Most Vulnerable to a Cyberattack?
What Industry Is Most Vulnerable to a Cyberattack?Why the Lack of Prioritization, Oversight, and Control of Third-Party Access Impacts EveryoneThe data shows that every industry contains...
Iranian Attackers Upgrade Social Engineering Tactics
Iranian Attackers Upgrade Social Engineering TacticsContenido de la entradaLeer másProofpoint News Feed
Why Would Palo Alto Networks Want Startup Apiiro for $600M?
Why Would Palo Alto Networks Want Startup Apiiro for $600M?Palo Alto Networks' 19-Month Acquisition Dry Spell Soon to Be Over, Calcalist SaysPalo Alto Networks has been...
Security Risks in Logistics APIs Used by E-Commerce Platforms
Security Risks in Logistics APIs Used by E-Commerce PlatformsOur research examines the security flaws that we found in the logistics API implementation of e-commerce platforms that...
NIST’s Expanding International Engagement on Cybersecurity
NIST’s Expanding International Engagement on CybersecurityIn providing a foundation for cybersecurity advancements over the years, NIST has taken the global context into account when determining priorities...
Uber exposes Lapsus$ extortion group for security breach
Uber exposes Lapsus$ extortion group for security breachIn last week’s security breach against Uber, the attackers downloaded internal messages from Slack as well as information from...
2K Games says hacked help desk targeted players with malware
2K Games says hacked help desk targeted players with malwareAmerican video game publisher 2K has confirmed that its help desk platform was hacked and used to...
Iranian cyberspies use multi-persona impersonation in phishing threads
Iranian cyberspies use multi-persona impersonation in phishing threadsContenido de la entradaLeer másProofpoint News Feed
Did hackers gain full access to Uber’s critical IT systems?
Did hackers gain full access to Uber’s critical IT systems?EXECUTIVE SUMMARY: Last week, Uber Technologies Inc. experienced a high-impact cyber attack. “They pretty much have full...
Imperva mitigated long-lasting, 25.3 billion request DDoS attack
Imperva mitigated long-lasting, 25.3 billion request DDoS attackInternet security company Imperva has announced its DDoS (distributed denial of service) mitigation solution has broken a new record,...
Death of Queen Elizabeth II exploited to steal Microsoft credentials
Death of Queen Elizabeth II exploited to steal Microsoft credentialsContenido de la entradaLeer másProofpoint News Feed
The Ransomware Files, Episode 11: The Adult Boutique
The Ransomware Files, Episode 11: The Adult BoutiqueDain Drake was CEO of a steel fabrication factory. In June 2019, Drake found himself standing outside a closed...
The prevention-first approach for SOC that your team needs to adopt
The prevention-first approach for SOC that your team needs to adoptAlon Bar, Product Marketing, Threat Prevention at Check Point Software Technologies Your SOC team works around...
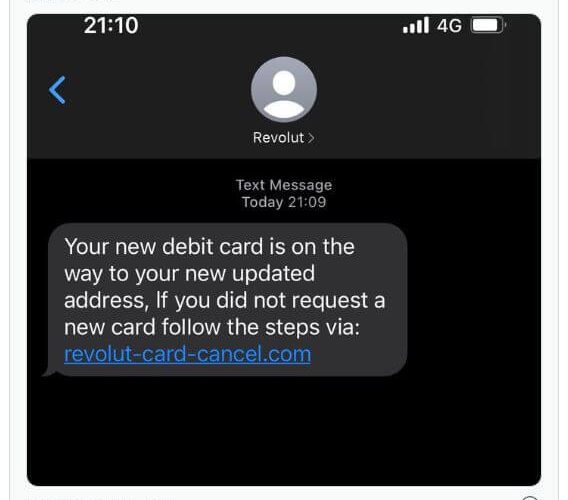
Revolut cyber attack exposes data belonging to thousands of customers
Revolut cyber attack exposes data belonging to thousands of customersEXECUTIVE SUMMARY: The London-based FinTech startup known as Revolut recently confirmed a breach that affected a “small...
Live Webinar | The Privacy and Security Implications of Big Health Data Initiatives
Live Webinar | The Privacy and Security Implications of Big Health Data InitiativesContenido de la entradaLeer másDataBreachToday.com RSS Syndication
SHARED INTEL: Poll highlights the urgency to balance digital resiliency, cybersecurity
SHARED INTEL: Poll highlights the urgency to balance digital resiliency, cybersecurityThe pace and extent of digital transformation that global enterprise organizations have undergone cannot be overstated....
Webinar | The State of Noncompliance in Cyber Risk Management
Webinar | The State of Noncompliance in Cyber Risk ManagementContenido de la entradaLeer másDataBreachToday.com RSS Syndication
K39178480: Perl vulnerability CVE-2018-18311
K39178480: Perl vulnerability CVE-2018-18311Perl vulnerability CVE-2018-18311 Security Advisory Security Advisory Description Perl before 5.26.3 and 5.28.x before 5.28.1 has a buffer overflow via a crafted regular...
MSA-22-0026: No groups filtering in H5P activity attempts report
MSA-22-0026: No groups filtering in H5P activity attempts reportby Michael Hawkins. The H5P activity attempts report did not filter by groups, which in separate groups mode...