Outdoor Clothing Brand, The North Face, Hit With Credential Stuffing AttackThe North Face, an outdoor clothing brand, was the victim of a large-scale credential stuffing attack....
Day: September 8, 2022
“Pwned”, the Book, is Finally Here!
"Pwned", the Book, is Finally Here!The first time I ever wrote publicly about a company's security vulnerabilities, my boss came to have a word with me...
Golang-Based Agenda Ransomware Detection: New Strain Began Sweeping Across Asia and Africa
Golang-Based Agenda Ransomware Detection: New Strain Began Sweeping Across Asia and Africa Researchers warn of a new ransomware family: a novel strain called Agenda sails in,...
DangerousSavanna Detection: Attacks Targeting Various Financial Orgs Revealed
DangerousSavanna Detection: Attacks Targeting Various Financial Orgs Revealed Security analysts revealed a two-year-long spear-phishing campaign aimed at entities in the financial sector in French-speaking African countries...
New Mirai Botnet Variant Detection: MooBot Sample Targets D-Link Routers
New Mirai Botnet Variant Detection: MooBot Sample Targets D-Link Routers Security researchers are raising the alarm on a new Mirai botnet variant dubbed MooBot that targets...
Smashing Security podcast #288: Chiquita banana, dumb criminals, and detecting ring binders
Smashing Security podcast #288: Chiquita banana, dumb criminals, and detecting ring bindersStudents learn a valuable lesson when it comes to AI detecting guns on campus, SIM...
Warning issued about Vice Society ransomware gang after attacks on schools
Warning issued about Vice Society ransomware gang after attacks on schoolsA ransomware gang that has been increasingly disproportionately targeting the education sector is the subject of...
Facebook Has No Idea What Data It Has
Facebook Has No Idea What Data It HasThis is from a court deposition: Facebook’s stonewalling has been revealing on its own, providing variations on the same...
Strong Password Ideas to Keep Your Information Safe
Strong Password Ideas to Keep Your Information Safe Password protection is one of the most common security protocols available. By creating a unique password, you are...
What Is Synthetic Identity Theft?
What Is Synthetic Identity Theft? It’s too bad cybercriminals don’t funnel their creativity into productive pursuits because they’re constantly coming up with nefarious new ways to...
A Parent’s Guide To The Metaverse – Part Two
A Parent’s Guide To The Metaverse – Part Two Welcome back to part 2 of my Metaverse series. If you are after tips and strategies to...
Fuzzing beyond memory corruption: Finding broader classes of vulnerabilities automatically
Fuzzing beyond memory corruption: Finding broader classes of vulnerabilities automaticallyPosted by Jonathan Metzman, Dongge Liu and Oliver Chang, Google Open Source Security Team Recently, OSS-Fuzz—our community...
Our Quest: Advancing Product Labels to Help Consumers Consider Cybersecurity
Our Quest: Advancing Product Labels to Help Consumers Consider CybersecurityFor many decades, consumers have relied on labels to help them make decisions about which products to...
Cisco won’t fix authentication bypass zero-day in EoL routers
Cisco won’t fix authentication bypass zero-day in EoL routersCisco says that a new authentication bypass flaw affecting multiple small business VPN routers will not be patched...
HP fixes severe bug in pre-installed Support Assistant tool
HP fixes severe bug in pre-installed Support Assistant toolHP issued a security advisory alerting users about a newly discovered vulnerability in HP Support Assistant, a software...
North Korean Lazarus hackers take aim at U.S. energy providers
North Korean Lazarus hackers take aim at U.S. energy providersThe North Korean APT group 'Lazarus' (APT38) is exploiting VMWare Horizon servers to access the corporate networks...
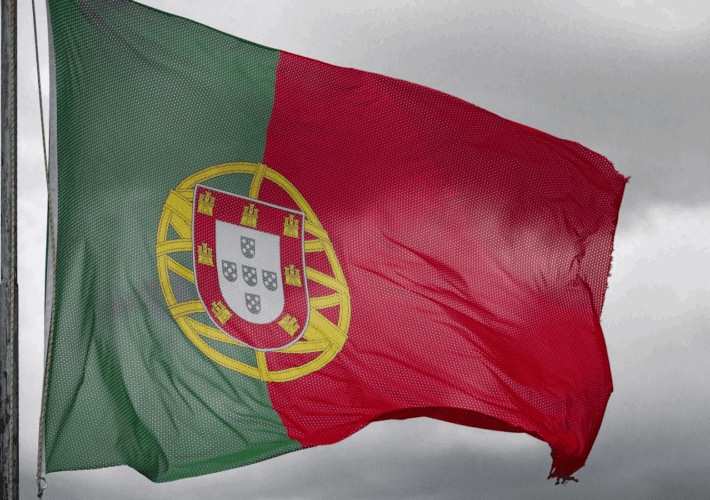
Classified NATO documents stolen from Portugal, now sold on darkweb
Classified NATO documents stolen from Portugal, now sold on darkwebThe Armed Forces General Staff agency of Portugal (EMGFA) has suffered a cyberattack that allegedly allowed the...
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel Sectors
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel SectorsContenido de la entradaLeer másProofpoint News Feed
Over 80% of the top websites leak user searches to advertisers
Over 80% of the top websites leak user searches to advertisersSecurity researchers at Norton Labs have found that roughly eight out of ten websites featuring a...
Cloud attacks on the supply chain are a huge concern
Cloud attacks on the supply chain are a huge concernContenido de la entradaLeer másProofpoint News Feed
iPhone 14 cheat sheet: Everything to know about Apple’s 2022 flagship phones
iPhone 14 cheat sheet: Everything to know about Apple’s 2022 flagship phonesLearn all about the key features, specs, pricing, availability and other details about Apple's 2022...
Cybercrime Group TA558 Ramps Up Email Attacks Against Hotels
Cybercrime Group TA558 Ramps Up Email Attacks Against HotelsContenido de la entradaLeer másProofpoint News Feed
Microsoft: Iranian hackers encrypt Windows systems using BitLocker
Microsoft: Iranian hackers encrypt Windows systems using BitLockerMicrosoft says an Iranian state-sponsored threat group it tracks as DEV-0270 (aka Nemesis Kitten) has been abusing the BitLocker...
PCI DSS compliance improving but still lags highs
PCI DSS compliance improving but still lags highsThe new PCI DSS 4.0 standard means organizations will have to up their game beginning in 2024. The post...
Cloud security: Increased concern about risks from partners, suppliers
Cloud security: Increased concern about risks from partners, suppliersContenido de la entradaLeer másProofpoint News Feed
How Malicious Actors Abuse Native Linux Tools in Attacks
How Malicious Actors Abuse Native Linux Tools in AttacksThrough our honeypots and telemetry, we were able to observe instances in which malicious actors abused native Linux...
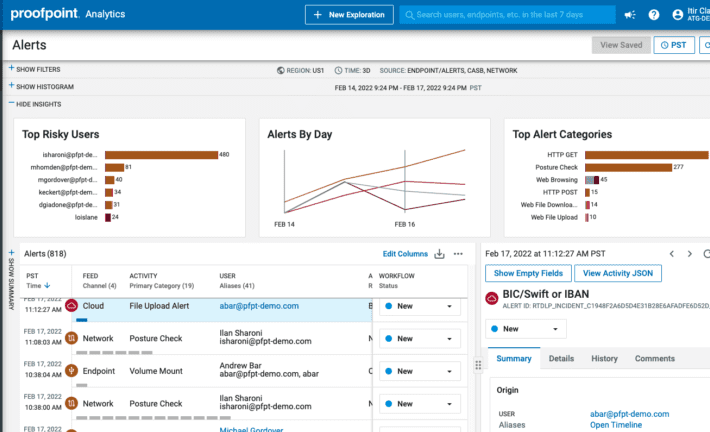
Best Data Security Solution | Proofpoint Information Protection
Best Data Security Solution | Proofpoint Information ProtectionContenido de la entradaLeer másProofpoint News Feed
Microsoft rolls out emergency fix for blocked Windows logins
Microsoft rolls out emergency fix for blocked Windows loginsMicrosoft says a Windows 11 update released in late August is blocking customers from signing in with newly added...
How to manage ad blocking in Opera
How to manage ad blocking in OperaJack Wallen shows you how to take control of online advertisements in the Opera web browser, so you can stop...
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance Platform
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance PlatformContenido de la entradaLeer másProofpoint News Feed