CISA Warns of Active Exploitation of Palo Alto Networks' PAN-OS VulnerabilityThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a security flaw impacting Palo Alto Networks...
Month: August 2022
Researchers Find Counterfeit Phones with Backdoor to Hack WhatsApp Accounts
Researchers Find Counterfeit Phones with Backdoor to Hack WhatsApp AccountsBudget Android device models that are counterfeit versions associated with popular smartphone brands are harboring multiple trojans...
“As Nasty as Dirty Pipe” — 8 Year Old Linux Kernel Vulnerability Uncovered
"As Nasty as Dirty Pipe" — 8 Year Old Linux Kernel Vulnerability UncoveredDetails of an eight-year-old security vulnerability in the Linux kernel have emerged that the...
The Rise of Data Exfiltration and Why It Is a Greater Risk Than Ransomware
The Rise of Data Exfiltration and Why It Is a Greater Risk Than RansomwareRansomware is the de facto threat organizations have faced over the past few...
Suspected Iranian Hackers Targeted Several Israeli Organizations for Espionage
Suspected Iranian Hackers Targeted Several Israeli Organizations for EspionageA suspected Iranian threat activity cluster has been linked to attacks aimed at Israeli shipping, government, energy, and...
New Air-Gap Attack Uses MEMS Gyroscope Ultrasonic Covert Channel to Leak Data
New Air-Gap Attack Uses MEMS Gyroscope Ultrasonic Covert Channel to Leak DataA novel data exfiltration technique has been found to leverage a covert ultrasonic channel to...
XCSSET Malware Updates with Python 3 to Target macOS Monterey Users
XCSSET Malware Updates with Python 3 to Target macOS Monterey UsersThe operators of the XCSSET macOS malware have upped the stakes by making iterative improvements that...
Researchers Warn of AiTM Attack Targeting Google G-Suite Enterprise Users
Researchers Warn of AiTM Attack Targeting Google G-Suite Enterprise UsersThe threat actors behind a large-scale adversary-in-the-middle (AiTM) phishing campaign targeting enterprise users of Microsoft email services have also...
GitLab Issues Patch for Critical Flaw in its Community and Enterprise Software
GitLab Issues Patch for Critical Flaw in its Community and Enterprise SoftwareDevOps platform GitLab this week issued patches to address a critical security flaw in its...
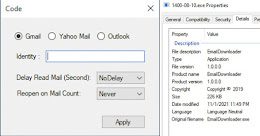
Google Uncovers Tool Used by Iranian Hackers to Steal Data from Email Accounts
Google Uncovers Tool Used by Iranian Hackers to Steal Data from Email AccountsThe Iranian government-backed actor known as Charming Kitten has added a new tool to...
Guide: How Service Providers can Deliver vCISO Services at Scale
Guide: How Service Providers can Deliver vCISO Services at ScaleFrom ransomware to breaches, from noncompliance penalties to reputational damage – cyberthreats pose an existential risk to...
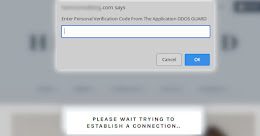
Hackers Using Fake DDoS Protection Pages to Distribute Malware
Hackers Using Fake DDoS Protection Pages to Distribute MalwareWordPress sites are being hacked to display fraudulent Cloudflare DDoS protection pages that lead to the delivery of...
Air-Gapped Devices Can Send Covert Morse Signals via Network Card LEDs
Air-Gapped Devices Can Send Covert Morse Signals via Network Card LEDsA security researcher who has a long line of work demonstrating novel data exfiltration methods from...
Bitcoin ATMs leeched by attackers who created fake admin accounts
Bitcoin ATMs leeched by attackers who created fake admin accountsThe criminals didn't implant any malware. The attack was orchestrated via malevolent configuration changes.Leer másNaked SecurityThe criminals...
Laptop denial-of-service via music: the 1980s R&B song with a CVE!
Laptop denial-of-service via music: the 1980s R&B song with a CVE!We haven't validated this vuln ourselves... but the source of the story is impeccable. (Impeccably dressed,...
Crypto Miners Using Tox P2P Messenger as Command and Control Server
Crypto Miners Using Tox P2P Messenger as Command and Control ServerThreat actors have begun to use the Tox peer-to-peer instant messaging service as a command-and-control method,...
Breaching airgap security: using your phone’s compass as a microphone!
Breaching airgap security: using your phone’s compass as a microphone!One bit per second makes the Voyager probe data rate seem blindingly fast. But it's enough to...
CEO of Israeli Pegasus spyware firm NSO to step down
CEO of Israeli Pegasus spyware firm NSO to step downCEO Shalev Hulio is stepping down as part of NSO reorganisation that will see it focus on...
How Twitter’s whistleblower could boost Elon Musk’s legal battle
How Twitter’s whistleblower could boost Elon Musk’s legal battlePeiter Zatko, former security chief, brought allegations of widespread security threats and spam concerns against the company New...
Mudge Blows Whistle on Alleged Twitter Security Nightmare
Mudge Blows Whistle on Alleged Twitter Security NightmareLawmakers and cybersecurity insiders are reacting to a bombshell report from former Twitter security head Mudge Zatko, alleging reckless...
Black Mail review – Nollywood’s finest head for London with cybercrime thriller
Black Mail review – Nollywood’s finest head for London with cybercrime thrillerA film star faces financial and family ruin as sleazy Russian mobsters blackmail him after...
Thoma Bravo Buying Spree Highlights Hot Investor Interest in IAM Market
Thoma Bravo Buying Spree Highlights Hot Investor Interest in IAM MarketM&A activity in the identity and access management (IAM) space has continued at a steady clip...
Experts question security of online vote to pick Tory leader
Experts question security of online vote to pick Tory leaderTechnology should not be used as it is unproven for such high-stakes elections, one security specialist says...
DevSecOps Gains Traction — but Security Still Lags
DevSecOps Gains Traction — but Security Still LagsAlmost half of teams develop and deploy software using a DevSecOps approach, but security remains the top area of...
Become a Cybersecurity Expert with 18 New Online Courses @ 98% OFF
Become a Cybersecurity Expert with 18 New Online Courses @ 98% OFFWith more data stored in the cloud than ever before, now is a good time...
CISA Adds 7 New Actively Exploited Vulnerabilities to Catalog
CISA Adds 7 New Actively Exploited Vulnerabilities to CatalogThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday moved to add a critical SAP security flaw to its Known...
Hackers Stole Crypto from Bitcoin ATMs by Exploiting Zero-Day Vulnerability
Hackers Stole Crypto from Bitcoin ATMs by Exploiting Zero-Day VulnerabilityBitcoin ATM manufacturer General Bytes confirmed that it was a victim of a cyberattack that exploited a...
New Grandoreiro Banking Malware Campaign Targeting Spanish Manufacturers
New Grandoreiro Banking Malware Campaign Targeting Spanish ManufacturersOrganizations in the Spanish-speaking nations of Mexico and Spain are in the crosshairs of a new campaign designed to...
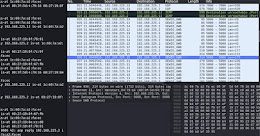
RTLS Systems Found Vulnerable to MiTM Attacks and Location Tampering
RTLS Systems Found Vulnerable to MiTM Attacks and Location TamperingResearchers have disclosed multiple vulnerabilities impacting Ultra-wideband (UWB) Real-time Locating Systems (RTLS), enabling threat actors to launch...
BSidesTLV 2022 – Gal Bitensky’s ‘SS-Oh No!’
BSidesTLV 2022 – Gal Bitensky’s ‘SS-Oh No!’Our thanks to BSidesTLV for publishing their outstanding conference videos on the organization's YouTube channel. Permalink The post BSidesTLV 2022...