Source: www.lastwatchdog.com - Author: bacohido By Andrey KarpovIn the modern world of software development, code quality...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Last Watchdog
Source: www.lastwatchdog.com - Author: cybernewswire Tel Aviv, Israel, Dec. 3, 2024, CyberNewswire — With Sweet, customers...
Source: www.lastwatchdog.com - Author: bacohido By Byron V. AcohidoThe compliance variable has come into play in...
Source: www.lastwatchdog.com - Author: bacohido By Iam WaqasAugmented reality use cases have become prevalent in our...
Source: www.lastwatchdog.com - Author: cybernewswire Tel Aviv, Israel, Nov. 11, 2024, CyberNewswire — Sweet Security today...
Source: www.lastwatchdog.com - Author: bacohido By Byron V. AcohidoThe Internet of Things is growing apace.Related: The...
Source: www.lastwatchdog.com - Author: bacohido By Byron V. AcohidoForeign adversaries proactively interfering in U.S. presidential elections...
Source: www.lastwatchdog.com - Author: cybernewswire Atlanta, GA, Oct. 30, 2024, CyberNewswire — The American Transaction Processors...
Source: www.lastwatchdog.com - Author: bacohido By Ivan NovikovApplication Programming Interfaces (APIs) have become the backbone of...
Source: www.lastwatchdog.com - Author: cybernewswire Cary, NC, Oct. 28, 2024, CyberNewswire — As the year-end approaches,...
Source: www.lastwatchdog.com - Author: cybernewswire Cary, NC, Oct. 22, 2024, CyberNewswire — INE Security offers essential...
Source: www.lastwatchdog.com - Author: bacohido By Ravi SrivatsavEveryone knows the cost and frequency of data breaches...
Source: www.lastwatchdog.com - Author: cybernewswire Austin, TX, Oct. 10th, 2024, CyberNewswire — SpyCloud, the leader in...
Source: www.lastwatchdog.com - Author: cybernewswire Torrance, Calif., Oct. 7, 2024, CyberNewswire — Criminal IP, a renowned Cyber...
Source: www.lastwatchdog.com - Author: cybernewswire San Francisco, Calif., Oct. 3, 2024, CyberNewswire — Doppler, the leading...
Source: www.lastwatchdog.com - Author: cybernewswire Singapore, Oct. 3, 2024, CyberNewswire — At DEF CON 32, the...
Source: www.lastwatchdog.com - Author: cybernewswire Torrance, Calif., Oct. 3, 2024, CyberNewswire — An exclusive live webinar...
Source: www.lastwatchdog.com - Author: cybernewswire Silver Spring, MD, Oct. 2, 2024, CyberNewswire — Aembit, the non-human...
Source: www.lastwatchdog.com - Author: bacohido Pittsburgh, PA, Oct. 1, 2024 — ForAllSecure, the world’s most advanced application...
Source: www.lastwatchdog.com - Author: cybernewswire Cary, NC, Sept. 27, 2024, CyberNewswire — INE, a global leader...
Source: www.lastwatchdog.com - Author: bacohido By Ambuj KumarEver since the massive National Public Data (NPD) breach...
Source: www.lastwatchdog.com - Author: cybernewswire Cary, NC, May 28, 2024, CyberNewsWire — If there is a...
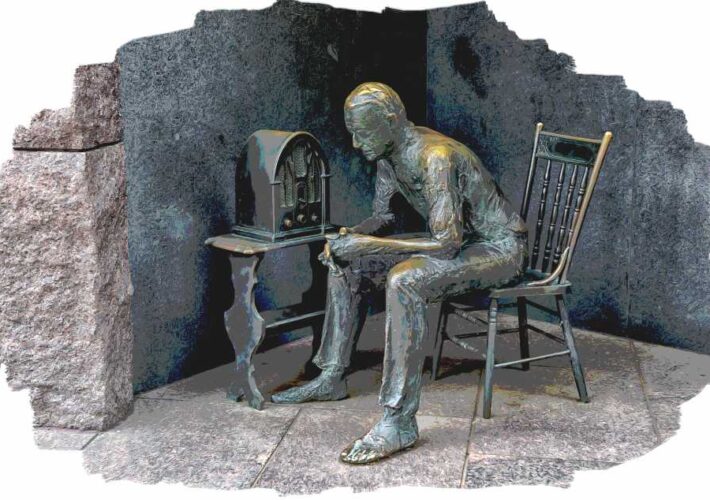
Source: www.lastwatchdog.com - Author: bacohido By Byron V. AcohidoSpread spectrum technology helped prevent the jamming of...
Source: www.lastwatchdog.com - Author: bacohido By Byron V. AcohidoAppSec has never been more challenging.By the same...
Source: www.lastwatchdog.com - Author: bacohido By Byron V. AcohidoIt’s easy to compile a checklist on why...
Source: www.lastwatchdog.com - Author: cybernewswire Torrance,Calif., May 22, 2024, CyberNewsWire — AI SPERA, a leader in...
Source: www.lastwatchdog.com - Author: cybernewswire New York, NY, May 21, 2024, CyberNewsWire — Memcyco Inc., provider...
Source: www.lastwatchdog.com - Author: bacohido By Byron V. AcohidoThere was a lot of buzz at RSAC...
Source: www.lastwatchdog.com - Author: bacohido The open-source Chromium project seeded by Google more than a decade...
Source: www.lastwatchdog.com - Author: bacohido By Brian SibleyMeeting the demands of the modern-day SMB is one...