Source: thehackernews.com - Author: . Jan 08, 2024NewsroomCryptocurrency / Financial Crime Threat actors affiliated with the...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Jan 06, 2024NewsroomCyber Espionage / Supply Chain Attack Telecommunication, media, internet...
Source: thehackernews.com - Author: . Jan 06, 2024NewsroomMalware / Cyber Attack The recent wave of cyber...
Source: thehackernews.com - Author: . Jan 05, 2024NewsroomEndpoint Security / Malware Cybersecurity researchers have discovered a...
Source: thehackernews.com - Author: . Picture this: you stumble upon a concealed secret within your company's...
Source: thehackernews.com - Author: . Jan 05, 2024NewsroomNetwork Security / Malware Mobile network operator Orange Spain...
Source: thehackernews.com - Author: . Jan 05, 2024NewsroomVulnerability / Network Security Ivanti has released security updates...
Source: thehackernews.com - Author: . Jan 05, 2024NewsroomCyber Attack / Data Breach Ukrainian cybersecurity authorities have...
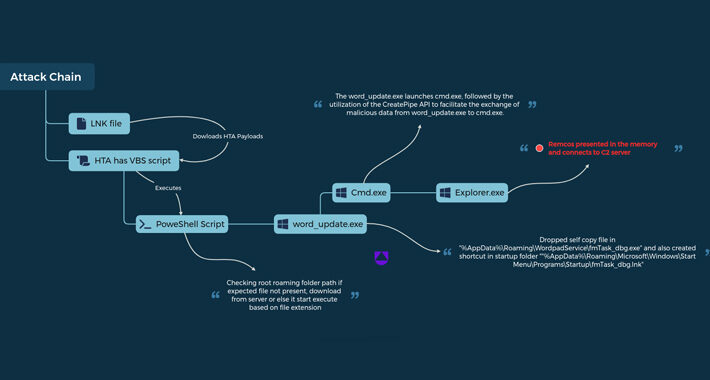
Source: thehackernews.com - Author: . Jan 05, 2024NewsroomMalware / Cyber Espionage A new variant of remote...
Source: thehackernews.com - Author: . Section four of the "Executive Order on Improving the Nation's Cybersecurity"...
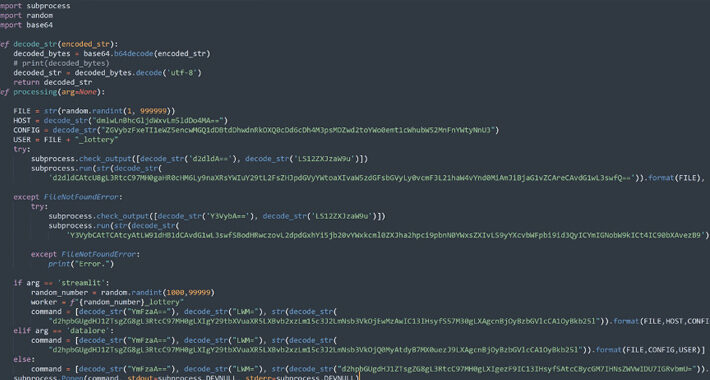
Source: thehackernews.com - Author: . Jan 04, 2024NewsroomCryptocurrency Miner / Malware Three new malicious packages have...
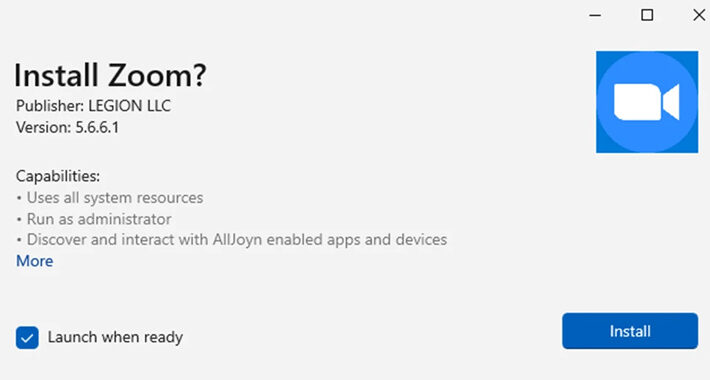
Source: thehackernews.com - Author: . Jan 04, 2024NewsroomSoftware Security / Malware The threat actor known as...
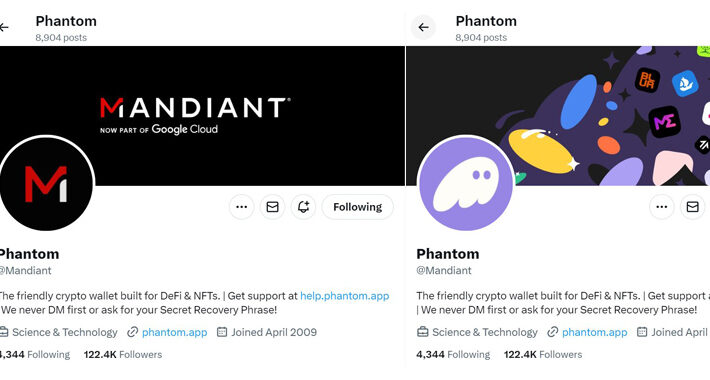
Source: thehackernews.com - Author: . Jan 04, 2024NewsroomCryptocurrency / Social Media American cybersecurity firm and Google...
Source: thehackernews.com - Author: . Jan 03, 2024NewsroomMalware / Data Theft Information stealing malware are actively...
Source: thehackernews.com - Author: . As technology adoption has shifted to be employee-led, just in time,...
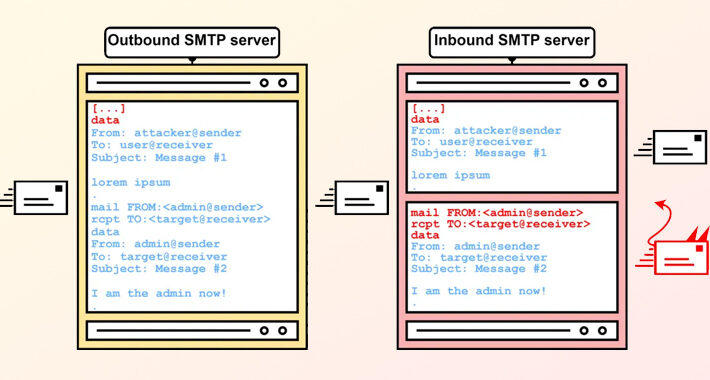
Source: thehackernews.com - Author: . Jan 03, 2024NewsroomCyber Threat / Email Security A new exploitation technique...
Source: thehackernews.com - Author: . Jan 03, 2024NewsroomVoIP Service / Regulatory Compliance The U.S. Department of...
Source: thehackernews.com - Author: . Security stakeholders have come to realize that the prominent role the...
Source: thehackernews.com - Author: . Jan 02, 2024NewsroomData Privacy / Online Tracking Google has agreed to...
Source: thehackernews.com - Author: . Jan 01, 2024NewsroomWindows Security / Vulnerability Security researchers have detailed a...
Source: thehackernews.com - Author: . Jan 01, 2024NewsroomEncryption / Network Security Security researchers from Ruhr University...
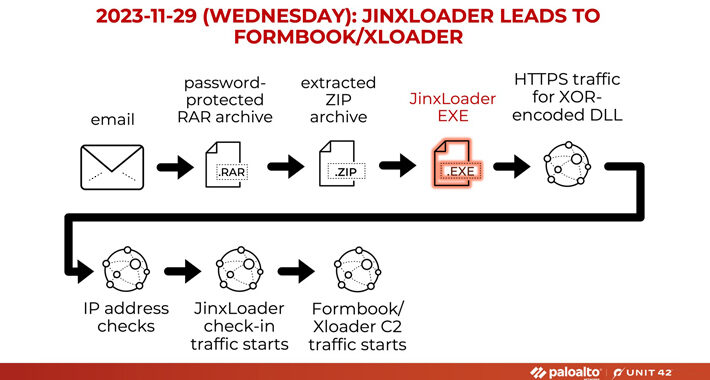
Source: thehackernews.com - Author: . Jan 01, 2024NewsroomMalware / Dark Web A new Go-based malware loader...
Source: thehackernews.com - Author: . Dec 30, 2023NewsroomCryptocurrency / Phishing Scam Cybersecurity researchers are warning about...
Source: thehackernews.com - Author: . Dec 29, 2023NewsroomCyber Attack / Web Security The Assembly of the...
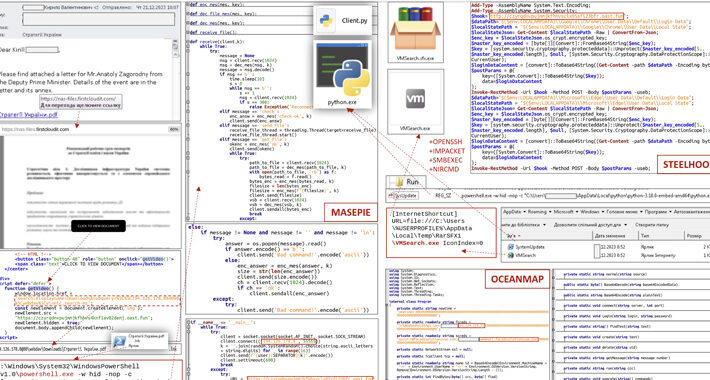
Source: thehackernews.com - Author: . Dec 29, 2023NewsroomEmail Security / Malware The Computer Emergency Response Team...
Source: thehackernews.com - Author: . Dec 29, 2023NewsroomMalware / Cyber Threat Nation-state actors affiliated to North...
Source: thehackernews.com - Author: . Dec 29, 2023NewsroomMalware / Endpoint Security Microsoft on Thursday said it's...
Source: thehackernews.com - Author: . Dec 28, 2023NewsroomCloud Security / Data Protection Google Cloud has addressed...
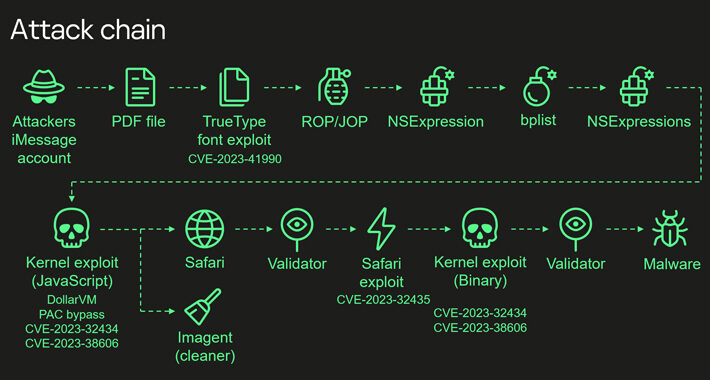
Source: thehackernews.com - Author: . Dec 28, 2023NewsroomSpyware / Hardware Security The Operation Triangulation spyware attacks...
Source: thehackernews.com - Author: . Dec 28, 2023NewsroomMalware / Cyber Threat A new malware loader is...