Source: thehackernews.com - Author: . Jan 13, 2024NewsroomVulnerability / Network Security Juniper Networks has released updates...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Jan 13, 2024NewsroomCryptojacking / Cloud Security A 29-year-old Ukrainian national has...
Source: thehackernews.com - Author: . Jan 12, 2024NewsroomVulnerability / Threat Intelligence As many as five different...
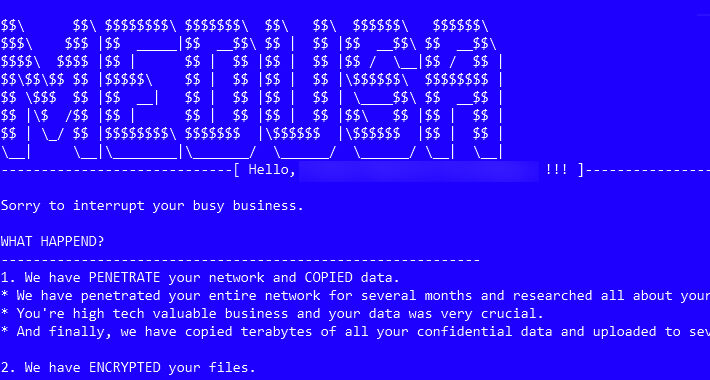
Source: thehackernews.com - Author: . The threat actors associated with the Medusa ransomware have ramped up...
Source: thehackernews.com - Author: . Picture a cybersecurity landscape where defenses are impenetrable, and threats are...
Source: thehackernews.com - Author: . Jan 12, 2024NewsroomDevSecOps / Software security GitLab has released security updates...
Source: thehackernews.com - Author: . Jan 12, 2024NewsroomCryptocurrency / Malware Cybersecurity researchers have identified a new...
Source: thehackernews.com - Author: . Jan 12, 2024NewsroomCyber Attack / Vulnerability The U.S. Cybersecurity and Infrastructure...
Source: thehackernews.com - Author: . Jan 11, 2024NewsroomCybersecurity / Software Security The ubiquity of GitHub in...
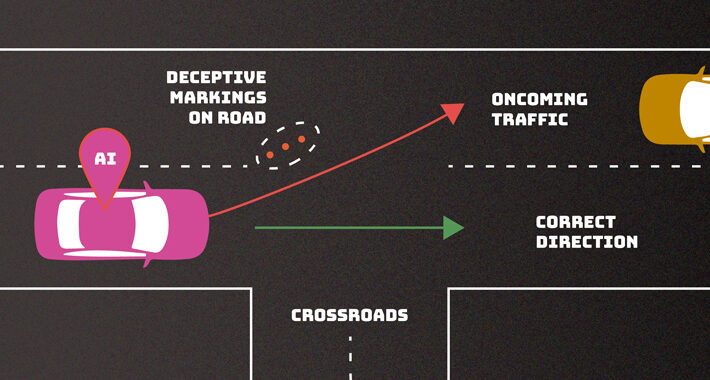
Source: thehackernews.com - Author: . Jan 11, 2024NewsroomVulnerability / Cyber Attack Cybersecurity researchers have developed a...
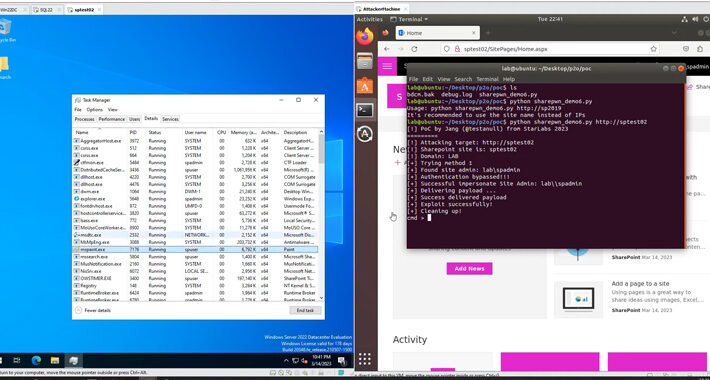
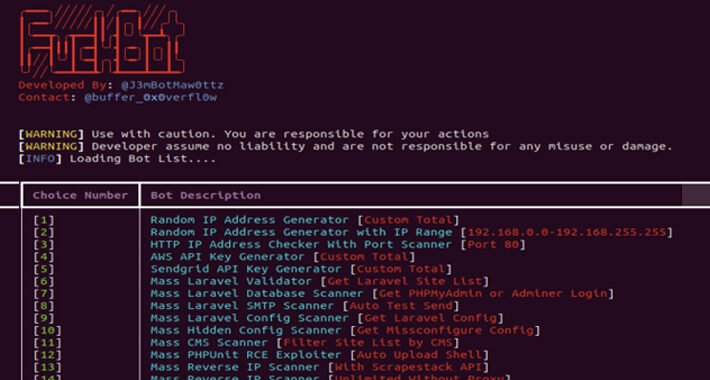
Source: thehackernews.com - Author: . Jan 11, 2024NewsroomCloud Security / Cyber Attacks A new Python-based hacking...
Source: thehackernews.com - Author: . Generative AI will enable anyone to launch sophisticated phishing attacks that...
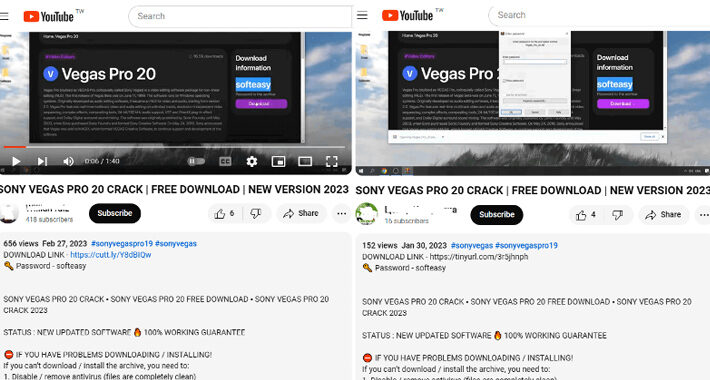
Source: thehackernews.com - Author: . Jan 11, 2024NewsroomMalvertising / Cyber Attacks Cybersecurity researchers have identified an...
Source: thehackernews.com - Author: . Jan 11, 2024NewsroomOnline Security / Cryptocurrency The compromise of Mandiant's X...
Source: thehackernews.com - Author: . Jan 11, 2024NewsroomCybersecurity / Zero-Day A pair of zero-day flaws identified...
Source: thehackernews.com - Author: . Jan 11, 2024NewsroomVulnerability / Patch Management Cisco has released software updates...
NoaBot: Latest Mirai-Based Botnet Targeting SSH Servers for Crypto Mining – Source:thehackernews.com
Source: thehackernews.com - Author: . Jan 10, 2024NewsroomServer Security / Cryptocurrency A new Mirai-based botnet called...
Source: thehackernews.com - Author: . IT professionals have developed a sophisticated understanding of the enterprise attack...
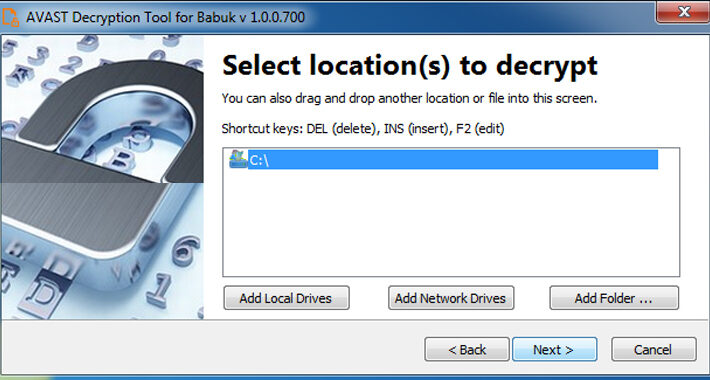
Source: thehackernews.com - Author: . Jan 10, 2024NewsroomRansomware / Data Security A decryptor for the Tortilla...
Source: thehackernews.com - Author: . Jan 10, 2024NewsroomPrivacy / Regulatory Compliance The U.S. Federal Trade Commission...
Source: thehackernews.com - Author: . Jan 10, 2024NewsroomVulnerability / Windows Security Microsoft has addressed a total...
Source: thehackernews.com - Author: . Jan 10, 2024NewsroomPatch Management / Threat Intelligence The U.S. Cybersecurity and...
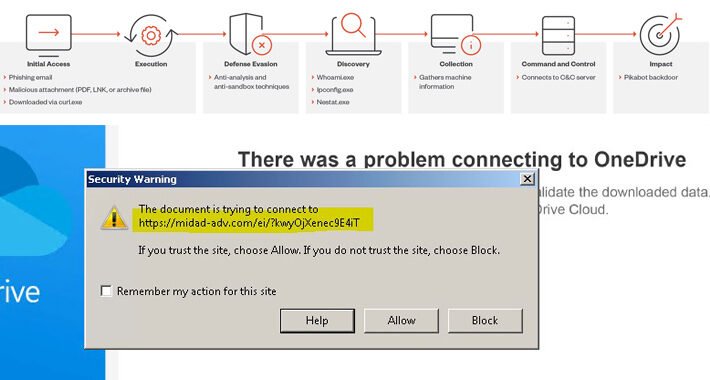
Source: thehackernews.com - Author: . Jan 09, 2024NewsroomMalware / Cyber Threat A threat actor called Water...
Turkish Hackers Exploiting Poorly Secured MS SQL Servers Across the Globe – Source:thehackernews.com
Source: thehackernews.com - Author: . Jan 09, 2024NewsroomData Security / Cyber Attack Poorly secured Microsoft SQL...
Source: thehackernews.com - Author: . Jan 09, 2024The Hacker NewsSaaS Security / Data Security Collaboration is...
Source: thehackernews.com - Author: . Jan 09, 2024NewsroomNetwork Security / Data Protection A security flaw has...
Source: thehackernews.com - Author: . Jan 09, 2024NewsroomMalware / Cyber Threat Threat actors are resorting to...
Source: thehackernews.com - Author: . Jan 08, 2024NewsroomMalware / Cybercrime Threat actors operating under the name...
Source: thehackernews.com - Author: . Jan 08, 2024NewsroomArtificial Intelligence / Cyber Security The U.S. National Institute...
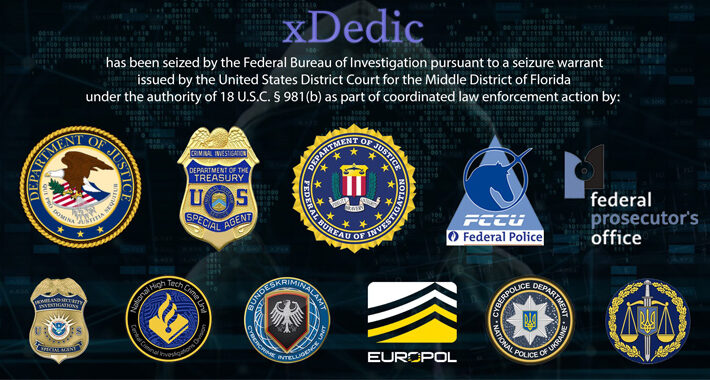
DoJ Charges 19 Worldwide in $68 Million xDedic Dark Web Marketplace Fraud – Source:thehackernews.com
Source: thehackernews.com - Author: . Jan 08, 2024NewsroomFinancial Fraud / Cybercrime The U.S. Department of Justice...