Samsung Admits Data Breach that Exposed Details of Some U.S. Customers South Korean chaebol Samsung on...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Microsoft Discover Severe ‘One-Click’ Exploit for TikTok Android App Microsoft on Wednesday disclosed details of a...
Apple Releases iOS Update for Older iPhones to Fix Actively Exploited Vulnerability Apple on Wednesday backported...
Over 1,800 Android and iOS Apps Found Leaking Hard-Coded AWS Credentials Researchers have identified 1,859 apps...
Infra Used in Cisco Hack Also Targeted Workforce Management Solution The attack infrastructure used to target Cisco in...
Chinese Hackers Used ScanBox Framework in Recent Cyber Espionage Attacks A months-long cyber espionage campaign undertaken...
Interested in Reducing Your Risk Profile? Jamf Has a Solution for That The threat landscape has...
Google Launches New Open Source Bug Bounty to Tackle Supply Chain Attacks Google on Monday introduced...
Experts Find Malicious Cookie Stuffing Chrome Extensions Used by 1.4 Million Users Five imposter extensions for...
Hackers Hide Malware in Stunning Images Taken by James Webb Space Telescope A persistent Golang-based malware...
Hands-on Review: Stellar Cyber Security Operations Platform for MSSPs As threat complexity increases and the boundaries...
Hackers Use ModernLoader to Infect Systems with Stealers and Cryptominers As many as three disparate but...
New Golang-based ‘Agenda Ransomware’ Can Be Customized For Each Victim A new ransomware strain written in...
FBI Warns Investors to Take Precautions with Decentralized Financial Platforms The U.S. Federal Bureau of Investigation...
FTC Sues Data Broker Over Selling Location Data for Hundreds of Millions of Phones The U.S....
India’s Newest Airline Akasa Air Found Leaking Passengers’ Personal Information Akasa Air, India’s newest commercial airline,...
CISA Adds 10 New Known Actively Exploited Vulnerabilities to its Catalog The U.S. Cybersecurity and Infrastructure...
A CISO’s Ultimate Security Validation Checklist If you’re heading out of the office on a well-deserved...
Twilio Breach Also Compromised Authy Two-Factor Accounts of Some Users Twilio, which earlier this month became...
Nitrokod Crypto Miner Infected Over 111,000 Users with Copies of Popular Software A Turkish-speaking entity called...
Critical Vulnerability Discovered in Atlassian Bitbucket Server and Data Center Atlassian has rolled out fixes for...
Iranian Hackers Exploiting Unpatched Log4j 2 Bugs to Target Israeli Organizations Iranian state-sponsored actors are leaving...
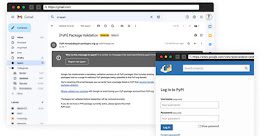
PyPI Repository Warns Python Project Maintainers About Ongoing Phishing Attacks The Python Package Index, PyPI, on...
U.S. Government Spending Billions on Cybersecurity In recent months, the House of Representatives has been hard...
Researchers Uncover Kimusky Infra Targeting South Korean Politicians and Diplomats The North Korean nation-state group Kimusky...
Cybercrime Groups Increasingly Adopting Sliver Command-and-Control Framework Nation-state threat actors are increasingly adopting and integrating the Sliver command-and-control...
Okta Hackers Behind Twilio and Cloudflare Breach Hit Over 130 Organizations The threat actor behind the...
Microsoft Uncovers New Post-Compromise Malware Used by Nobelium Hackers The threat actor behind the SolarWinds supply...
Hackers Breach LastPass Developer System to Steal Source Code Password management service LastPass confirmed a security...
PyPI Repository Warns Python Project Maintainers About Ongoing Phishing Attacks The Python Package Index, PyPI, on...