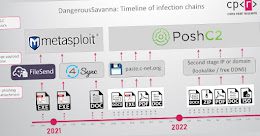
Hackers Repeatedly Targeting Financial Services in French-Speaking African Countries Major financial and insurance companies located in...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Microsoft Warns of Ransomware Attacks by Iranian Phosphorus Hacker Group Microsoft’s threat intelligence division on Wednesday...
Chinese Hackers Target Government Officials in Europe, South America, and Middle East A Chinese hacking group...
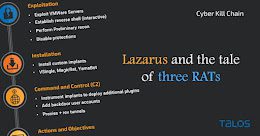
North Korean Lazarus Hackers Targeting Energy Providers Around the World A malicious campaign mounted by the...
What Is Your Security Team Profile? Prevention, Detection, or Risk Management Not all security teams are...
QNAP Warns of New DeadBolt Ransomware Attacks Exploiting Photo Station Flaw QNAP has issued a new...
TikTok Denies Data Breach Reportedly Exposing Over 2 Billion Users’ Information Popular short-form social video service...
New EvilProxy Phishing Service Allowing Cybercriminals to Bypass 2-Factor Security A new phishing-as-a-service (PhaaS) toolkit dubbed...
Researchers Find New Android Spyware Campaign Targeting Uyghur Community A previously undocumented strain of Android spyware...
Worok Hackers Target High-Profile Asian Companies and Governments High-profile companies and local governments located primarily in...
TA505 Hackers Using TeslaGun Panel to Manage ServHelper Backdoor Attacks Cybersecurity researchers have offered fresh insight...
Integrating Live Patching in SecDevOps Workflows SecDevOps is, just like DevOps, a transformational change that organizations...
Mirai Variant MooBot Botnet Exploiting D-Link Router Vulnerabilities A variant of the Mirai botnet known as...
Critical RCE Vulnerability Affects Zyxel NAS Devices — Firmware Patch Released Networking equipment maker Zyxel has...
New Stealthy Shikitega Malware Targeting Linux Systems and IoT Devices A new piece of stealthy Linux...
North Korean Hackers Deploying New MagicRAT Malware in Targeted Campaigns The prolific North Korean nation-state actor...
4 Key Takeaways from “XDR is the Perfect Solution for SMEs” webinar Cyberattacks on large organizations...
Some Members of Conti Group Targeting Ukraine in Financially Motivated Attacks Former members of the Conti...
Authorities Shut Down WT1SHOP Site for Selling Stolen Credentials and Credit Cards An international law enforcement...
Ransomware Attackers Abuse Genshin Impact Anti-Cheat System to Disable Antivirus A vulnerable anti-cheat driver for the...
Fake Antivirus and Cleaner Apps Caught Installing SharkBot Android Banking Trojan The notorious Android banking trojan...
Researchers Detail Emerging Cross-Platform BianLian Ransomware Attacks The operators of the emerging cross-platform BianLian ransomware have...
New Evidence Links Raspberry Robin Malware to Dridex and Russian Evil Corp Hackers Researchers have identified...
Google Chrome Bug Lets Sites Silently Overwrite System Clipboard Content A “major” security issue in the...
Stop Worrying About Passwords Forever So far 2022 confirms that passwords are not dead yet. Neither...
The Ultimate Security Blind Spot You Don’t Know You Have How much time do developers spend...
Warning: PyPI Feature Executes Code Automatically After Python Package Download In another finding that could expose...
Google Releases Urgent Chrome Update to Patch New Zero-Day Vulnerability Google on Friday shipped emergency fixes...
Prynt Stealer Contains a Backdoor to Steal Victims’ Data Stolen by Other Cybercriminals Researchers discovered a...
JuiceLedger Hackers Behind the Recent Phishing Attacks Against PyPI Users More details have emerged about the...