Source: thehackernews.com - Author: . Jan 20, 2024NewsroomCyber Espionage / Emails Security Microsoft on Friday revealed...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . The threat actor tracked as TA866 has resurfaced after a nine-month...
Source: thehackernews.com - Author: . Jan 19, 2024NewsroomMalware / Endpoint Security Pirated applications targeting Apple macOS...
Source: thehackernews.com - Author: . Jan 19, 2024NewsroomSoftware Security / Spyware A malicious package uploaded to...
Source: thehackernews.com - Author: . Jan 19, 2024NewsroomCyber Theat / Zero-Day The U.S. Cybersecurity and Infrastructure...
Source: thehackernews.com - Author: . Jan 18, 2024NewsroomServer Security / Cryptocurrency Vulnerable Docker services are being...
Source: thehackernews.com - Author: . The Russia-linked threat actor known as COLDRIVER has been observed evolving...
Source: thehackernews.com - Author: . Jan 18, 2024NewsroomSupply Chain Attacks / AI Security Continuous integration and...
Source: thehackernews.com - Author: . Jan 18, 2024The Hacker NewsAuthentication Security / Passwords In today's digital...
Source: thehackernews.com - Author: . Jan 18, 2024NewsroomFirmware Security / Vulnerability Multiple security vulnerabilities have been...
Source: thehackernews.com - Author: . Jan 18, 2024NewsroomCyber Espionage / Threat Intelligence High-profile individuals working on...
Source: thehackernews.com - Author: . Jan 17, 2024NewsroomFinancial Data / Vulnerability The point-of-sale (PoS) terminals from...
Source: thehackernews.com - Author: . Wing Security announced today that it now offers free discovery and...
Source: thehackernews.com - Author: . Jan 17, 2024NewsroomBotnet / Cloud Security The U.S. Cybersecurity and Infrastructure...
Source: thehackernews.com - Author: . Jan 17, 2024The Hacker NewsCyber Threat / Live Webinar In the...
Source: thehackernews.com - Author: . Jan 17, 2024NewsroomSpyware / Forensic Analysis Cybersecurity researchers have identified a...
GitHub Rotates Keys After High-Severity Vulnerability Exposes Credentials – Source:thehackernews.com
Source: thehackernews.com - Author: . Jan 17, 2024NewsroomVulnerability / Software Security GitHub has revealed that it...
Source: thehackernews.com - Author: . Jan 17, 2024NewsroomVulnerability / Cyber Threat Citrix is warning of two...
Source: thehackernews.com - Author: . Jan 17, 2024NewsroomBrowser Security / Vulnerability Google on Tuesday released updates...
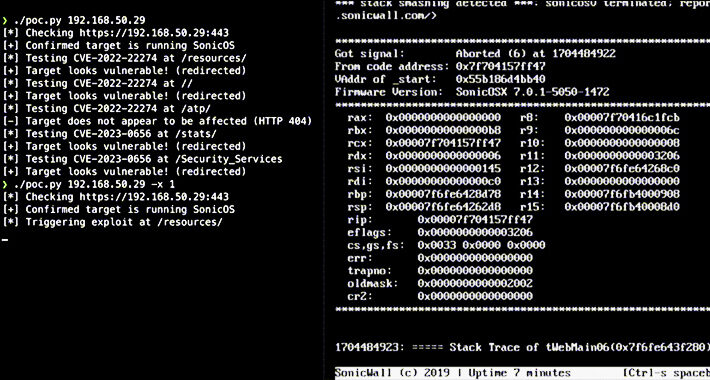
Source: thehackernews.com - Author: . Jan 16, 2024NewsroomVulnerability / Network Security Over 178,000 SonicWall firewalls exposed...
Source: thehackernews.com - Author: . Jan 16, 2024NewsroomBotnet / Malware The remote access trojan (RAT) known...
Source: thehackernews.com - Author: . Explore how an advanced exposure management solution saved a major retail...
Source: thehackernews.com - Author: . Jan 16, 2024NewsroomCryptocurrency / Cyber Threat The operators behind the now-defunct...
Source: thehackernews.com - Author: . Jan 16, 2024NewsroomCryptocurrency / Windows Security Threat actors have been observed...
Source: thehackernews.com - Author: . The ransomware industry surged in 2023 as it saw an alarming...
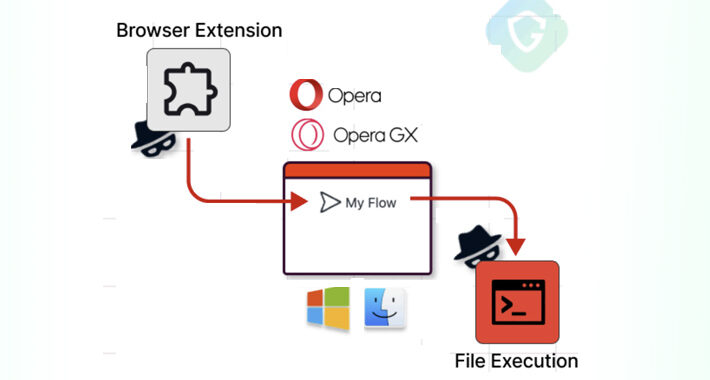
Source: thehackernews.com - Author: . Jan 15, 2024NewsroomVulnerability / Browser Security Cybersecurity researchers have disclosed a...
Source: thehackernews.com - Author: . Jan 15, 2024NewsroomOperational Technology / Network Security Multiple security vulnerabilities have...
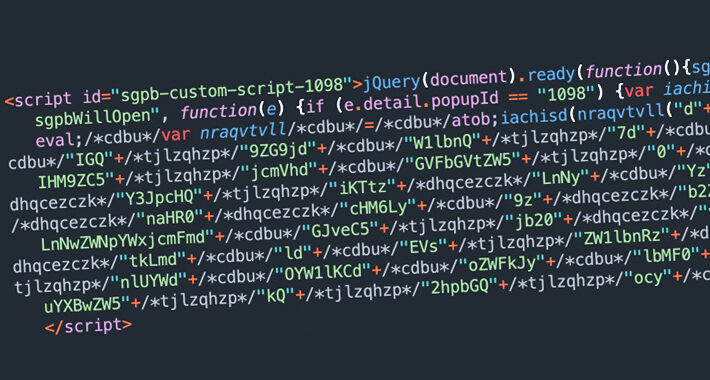
Source: thehackernews.com - Author: . Jan 15, 2024NewsroomWebsite Security / Vulnerability Thousands of WordPress sites using...
Source: thehackernews.com - Author: . Jan 15, 2024NewsroomServer Security / Cyber Attack The environmental services industry...
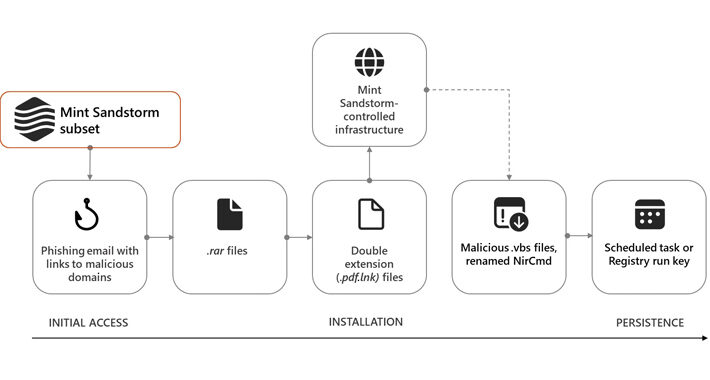
Source: thehackernews.com - Author: . Jan 14, 2024NewsroomCyber Attack / Vulnerability The cyber attacks targeting the...