North Korea Hackers Using New “Dolphin” Backdoor to Spy on South Korean Targets The North Korea-linked ScarCruft group...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
LastPass Suffers Another Security Breach; Exposed Some Customers Information Popular password management service LastPass said it’s...
Schoolyard Bully Trojan Apps Stole Facebook Credentials from Over 300,000 Android Users More than 300,000 users...
Researchers ‘Accidentally’ Crash KmsdBot Cryptocurrency Mining Botnet Network An ongoing analysis into an up-and-coming cryptocurrency mining...
Hackers Leak Another Set of Medibank Customer Data on the Dark Web Medibank on Thursday confirmed...
Researchers Disclose Critical RCE Vulnerability Affecting Quarkus Java Framework A critical security vulnerability has been disclosed...
What Developers Need to Fight the Battle Against Common Vulnerabilities Today’s threat landscape is constantly evolving,...
Cuba Ransomware Extorted Over $60 Million in Ransom Fees from More than 100 Entities The threat...
Google Accuses Spanish Spyware Vendor of Exploiting Chrome, Firefox, & Windows Zero-Days A Barcelona-based surveillanceware vendor...
Hackers Exploiting Redis Vulnerability to Deploy New Redigo Malware on Servers A previously undocumented Go-based malware...
What the CISA Reporting Rule Means for Your IT Security Protocol The new Cyber Incident Reporting for...
Watch Out! These Android Keyboard Apps With 2 Million Installs Can be Hacked Remotely Multiple unpatched...
The Value of Old Systems Old technology solutions – every organization has a few of them...
Researchers Disclose Supply-Chain Flaw Affecting IBM Cloud Databases for PostgreSQL IBM has fixed a high-severity security...
Hackers Sign Android Malware Apps with Compromised Platform Certificates Platform certificates used by Android smartphone vendors...
CISA Warns of Multiple Critical Vulnerabilities Affecting Mitsubishi Electric PLCs The U.S. Cybersecurity and Infrastructure Security...
Critical Ping Vulnerability Allows Remote Attackers to Take Over FreeBSD Systems The maintainers of the FreeBSD...
Google Rolls Out New Chrome Browser Update to Patch Yet Another Zero-Day Vulnerability Search giant Google...
When Being Attractive Gets Risky – How Does Your Attack Surface Look to an Attacker? In...
SiriusXM Vulnerability Lets Hackers Remotely Unlock and Start Connected Cars Cybersecurity researchers have discovered a security...
North Korean Hackers Spread AppleJeus Malware Disguised as Cryptocurrency Apps The Lazarus Group threat actor has...
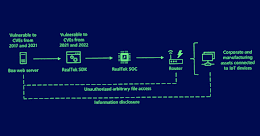
New BMC Supply Chain Vulnerabilities Affect Servers from Dozens of Manufacturers Three different security flaws have...
Russian Courts Targeted by New CryWiper Data Wiper Malware Posing as Ransomware A new data wiper...
This Malware Installs Malicious Browser Extensions to Steal Users’ Passwords and Cryptos A malicious extension for...
Nighthawk Likely to Become Hackers’ New Post-Exploitation Tool After Cobalt Strike A nascent and legitimate penetration...
Meta Takes Down Fake Facebook and Instagram Accounts Linked to Pro-U.S. Influence Operation Meta Platforms on...
Top Cyber Threats Facing E-Commerce Sites This Holiday Season Delivering a superior customer experience is essential...
Hackers Exploiting Abandoned Boa Web Servers to Target Critical Industries Microsoft on Tuesday disclosed the intrusion...
34 Russian Cybercrime Groups Stole Over 50 Million Passwords with Stealer Malware As many as 34...
Ducktail Malware Operation Evolves with New Malicious Capabilities The operators of the Ducktail information stealer have...