Source: thehackernews.com - Author: . May 24, 2023Ravie LakshmananMobile Security / Data Safety Google has removed...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
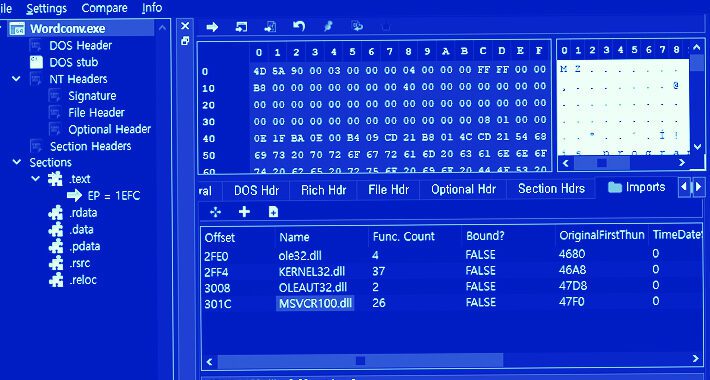
Source: thehackernews.com - Author: . May 24, 2023Ravie LakshmananServer Security / Malware An updated version of...
Source: thehackernews.com - Author: . May 24, 2023Ravie LakshmananCyber Espionage / Server Security The infamous Lazarus...
Source: thehackernews.com - Author: . May 24, 2023Ravie LakshmananCyber War / Threat Intel The Computer Emergency...
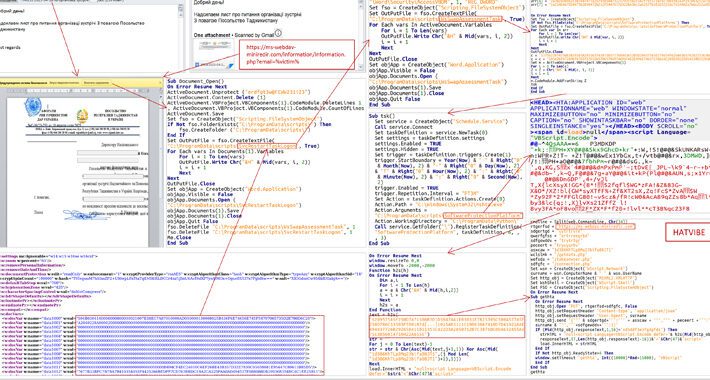
Source: thehackernews.com - Author: . May 23, 2023Ravie LakshmananCyber Threat / APT Government and diplomatic entities...
Source: thehackernews.com - Author: . May 23, 2023Ravie LakshmananCyber Threat / Malware The North Korean advanced...
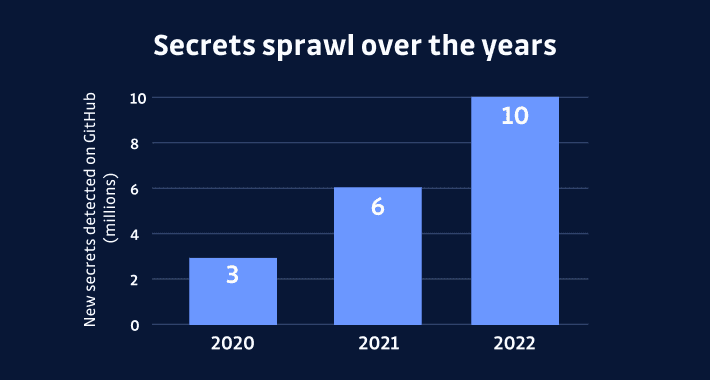
Source: thehackernews.com - Author: . The most precious asset in today's information age is the secret...
New WinTapix.sys Malware Engages in Multi-Stage Attack Across Middle East – Source:thehackernews.com
Source: thehackernews.com - Author: . May 23, 2023Ravie LakshmananEndpoint Security/ Malware An unknown threat actor has...
Source: thehackernews.com - Author: . May 23, 2023Ravie LakshmananNational Security / Hardware China has banned U.S....
Source: thehackernews.com - Author: . May 22, 2023Ravie LakshmananData Protection / Privacy Facebook's parent company Meta...
Source: thehackernews.com - Author: . May 22, 2023Ravie LakshmananCryptocurrency / Cloud Security A financially motivated threat...
Source: thehackernews.com - Author: . A new stealthy information stealer malware called Bandit Stealer has caught...
Source: thehackernews.com - Author: . May 27, 2023Ravie LakshmananAPI Security / Vulnerability A critical security vulnerability...
Severe Flaw in Google Cloud’s Cloud SQL Service Exposed Confidential Data – Source:thehackernews.com
Source: thehackernews.com - Author: . May 26, 2023Ravie LakshmananData Safety / Cloud Security A new security...
Predator Android Spyware: Researchers Uncover New Data Theft Capabilities – Source:thehackernews.com
Source: thehackernews.com - Author: . Security researchers have detailed the inner workings of the commercial Android...
Source: thehackernews.com - Author: . 5G is a game changer for mobile connectivity, including mobile connectivity...
Source: thehackernews.com - Author: . May 26, 2023Ravie LakshmananICS/SCADA Security A new strain of malicious software...
Source: thehackernews.com - Author: . May 26, 2023Ravie LakshmananEmail Security / Zero-Day Email protection and network...
Source: thehackernews.com - Author: . May 25, 2023Ravie LakshmananGaming / Server Security A new botnet called...
Source: thehackernews.com - Author: . May 25, 2023Ravie LakshmananNetwork Security / Vulnerability Zyxel has released software...
Source: thehackernews.com - Author: . May 25, 2023The Hacker NewsIncident Response A hospital with 2,000 employees...
New PowerExchange Backdoor Used in Iranian Cyber Attack on UAE Government – Source:thehackernews.com
Source: thehackernews.com - Author: . May 25, 2023Ravie LakshmananEmail Security / Exploit An unnamed government entity...
Source: thehackernews.com - Author: . May 25, 2023Ravie LakshmananFinancial Security / Cyber Threat A Brazilian threat...
Source: thehackernews.com - Author: . May 25, 2023The Hacker NewsBrowser Security / Tech In today's digital...
Source: thehackernews.com - Author: . May 25, 2023Ravie LakshmananEndpoint Security / Cyber Threat The threat actors...
Source: thehackernews.com - Author: . May 25, 2023Ravie LakshmananCyber Threat / Espionage A stealthy China-based group...
Microsoft Fixes New Azure AD Vulnerability Impacting Bing Search and Major Apps Microsoft has patched a...
3CX Supply Chain Attack — Here’s What We Know So Far Enterprise communications software maker 3CX...
Deep Dive Into 6 Key Steps to Accelerate Your Incident Response Organizations rely on Incident response to ensure...
Cyber Police of Ukraine Busted Phishing Gang Responsible for $4.33 Million Scam The Cyber Police of...