Source: thehackernews.com - Author: . The Quick Serve Restaurant (QSR) industry is built on consistency and...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Jun 20, 2023Ravie Lakshmanan A highly targeted cyber attack against an...
Source: thehackernews.com - Author: . Jun 20, 2023Ravie LakshmananNetwork Security / Vulnerability Taiwanese company ASUS on...
Source: thehackernews.com - Author: . Jun 20, 2023Ravie LakshmananEndpoint Security / Password Over 101,100 compromised OpenAI...
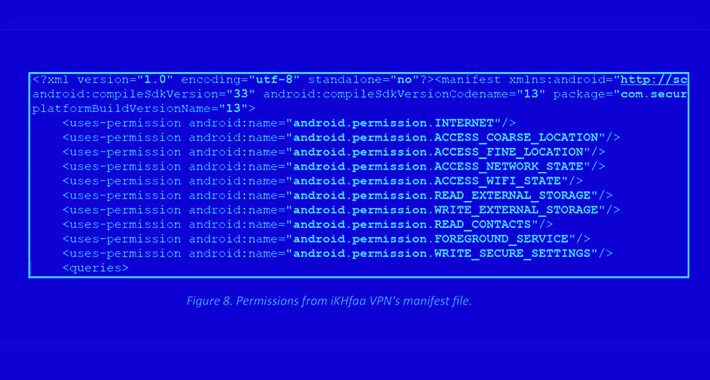
Source: thehackernews.com - Author: . Jun 20, 2023Ravie LakshmananCyber Espionage / Mobile Security Individuals in the...
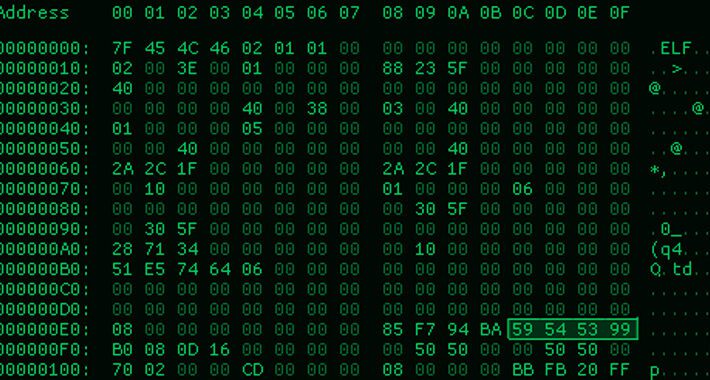
Source: thehackernews.com - Author: . A new information-stealing malware called Mystic Stealer has been found to...
Source: thehackernews.com - Author: . Jun 19, 2023Ravie LakshmananEndpoint Security / Hacking Cybersecurity researchers have uncovered...
Source: thehackernews.com - Author: . Jun 19, 2023The Hacker NewsDevSecOps / AppSec While the use of...
Source: thehackernews.com - Author: . Jun 19, 2023Ravie LakshmananCyber Attack / Hacking Governmental entities in the...
Source: thehackernews.com - Author: . Jun 19, 2023Ravie LakshmananNetwork and Cloud Security Microsoft on Friday attributed...
Source: thehackernews.com - Author: . Jun 17, 2023Ravie LakshmananCryptojacking / Network Security Cybersecurity researchers have discovered...
Source: thehackernews.com - Author: . Jun 16, 2023Ravie LakshmananEndpoint Security / Network Security The threat actor...
Source: thehackernews.com - Author: . As Threat Actors Continuously Adapt their TTPs in Today's Threat Landscape,...
Source: thehackernews.com - Author: . Jun 16, 2023Ravie LakshmananRansomware / Cyber Crime The U.S. Department of...
Source: thehackernews.com - Author: . Jun 16, 2023Ravie LakshmananCyber Attack / Ransomware Progress Software on Thursday...
Source: thehackernews.com - Author: . Jun 15, 2023Ravie LakshmananCryptocurrency / Ransomware Ransomware actors and cryptocurrency scammers...
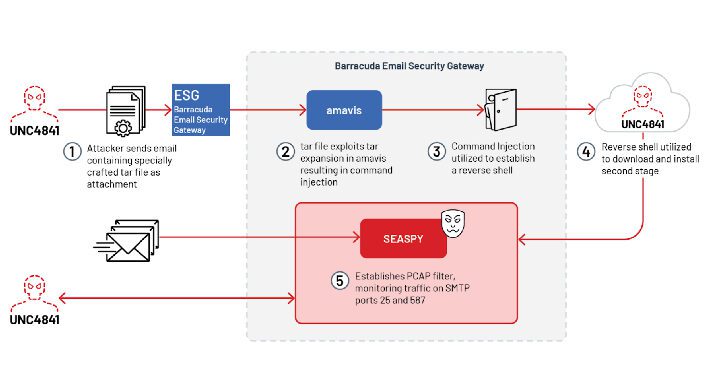
Source: thehackernews.com - Author: . Jun 15, 2023Ravie Lakshmanan A suspected China-nexus threat actor dubbed UNC4841...
Source: thehackernews.com - Author: . Jun 15, 2023Ravie LakshmananMalware / Cyber Threat The threat actors behind...
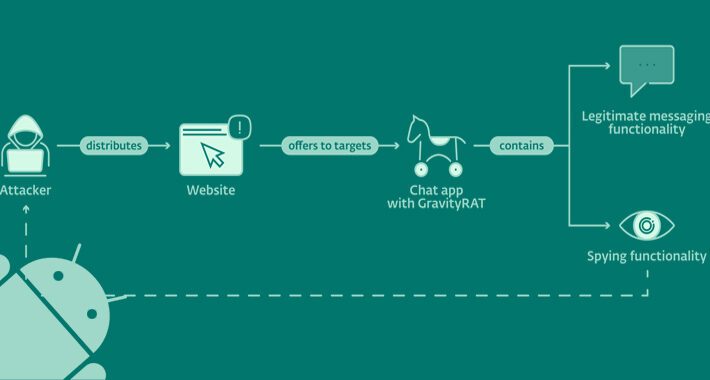
Source: thehackernews.com - Author: . Jun 15, 2023Ravie LakshmananMobile Security / Privacy An updated version of...
Source: thehackernews.com - Author: . Jun 15, 2023The Hacker NewsBrowser Security / Data Security The revolutionary...
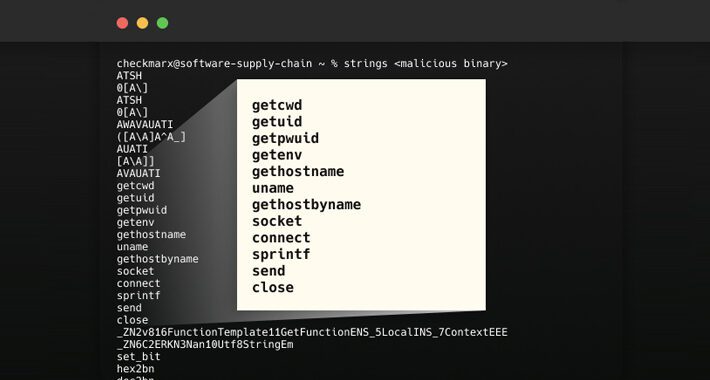
Source: thehackernews.com - Author: . Jun 15, 2023Ravie LakshmananSoftware Supply Chain In what's a new kind...
Source: thehackernews.com - Author: . Jun 15, 2023Ravie LakshmananCyber War / Threat Intel The Russian threat...
Source: thehackernews.com - Author: . Jun 15, 2023Ravie Lakshmanan Microsoft on Wednesday took the lid off...
Source: thehackernews.com - Author: . The threat actors behind the LockBit ransomware-as-a-service (RaaS) scheme have extorted...
Source: thehackernews.com - Author: . Jun 14, 2023Ravie LakshmananZero-Day / Network Security The Chinese state-sponsored group...
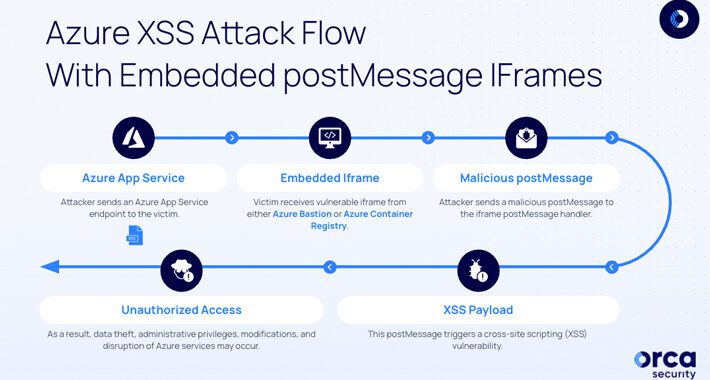
Source: thehackernews.com - Author: . Jun 14, 2023Ravie LakshmananCloud Security / Vulnerability Two "dangerous" security vulnerabilities...
Source: thehackernews.com - Author: . Jun 14, 2023Ravie LakshmananCyber Threat / Malware A new Golang-based information...
Source: thehackernews.com - Author: . Jun 14, 2023The Hacker NewsThreat Intel / Network Security For the...
Source: thehackernews.com - Author: . Jun 14, 2023Ravie LakshmananMalware / Zero-Day At least half of dozen...
Source: thehackernews.com - Author: . Jun 14, 2023Ravie LakshmananWebsite Security / Hacking A security flaw has...