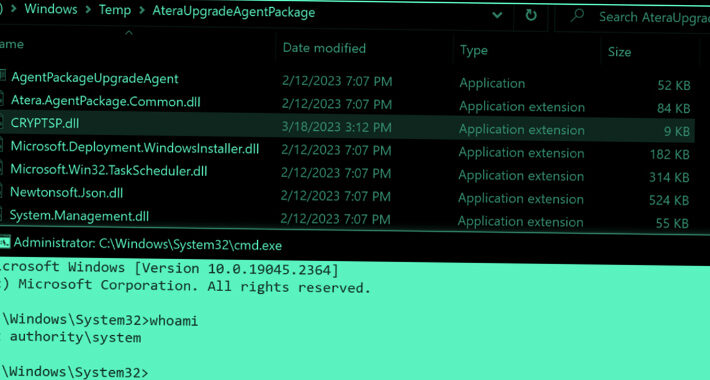
Source: thehackernews.com - Author: . Jul 24, 2023THNWindows Security / Zero-Day Zero-day vulnerabilities in Windows Installers...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Jul 24, 2023THNMobile Security / Privacy Google has announced that it...
Source: thehackernews.com - Author: . The healthcare industry is under a constant barrage of cyberattacks. It...
Source: thehackernews.com - Author: . Jul 24, 2023THNLinux / Network Security Details have emerged about a...
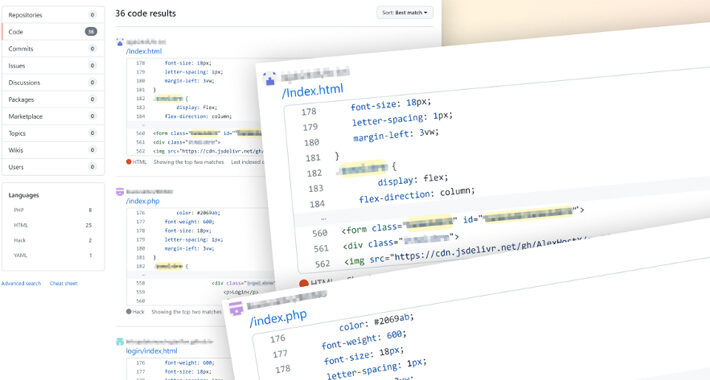
Source: thehackernews.com - Author: . Cybersecurity researchers said they have discovered what they say is the...
Source: thehackernews.com - Author: . Jul 22, 2023THNEncryption / Privacy Apple has warned that it would...
Source: thehackernews.com - Author: . Jul 21, 2023THNEmail Security / Cyber Attack The recent attack against...
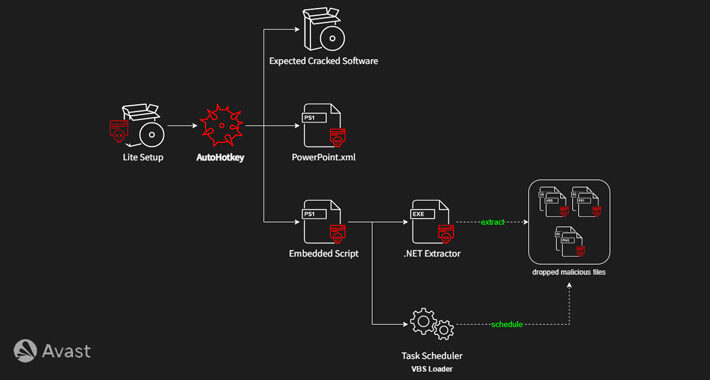
Source: thehackernews.com - Author: . Jul 21, 2023THNMalware / Software Security A new variant of AsyncRAT...
Source: thehackernews.com - Author: . Jul 21, 2023THNCyber Threat / Malware A new malware strain known...
Local Governments Targeted for Ransomware – How to Prevent Falling Victim – Source:thehackernews.com
Source: thehackernews.com - Author: . Jul 21, 2023The Hacker NewsPassword Security / Cybersecurity Regardless of the...
Source: thehackernews.com - Author: . Jul 21, 2023THNVulnerability / Botnet Several distributed denial-of-service (DDoS) botnets have...
Source: thehackernews.com - Author: . Jul 21, 2023THNVulnerability / Cyber Threat The U.S. Cybersecurity and Infrastructure...
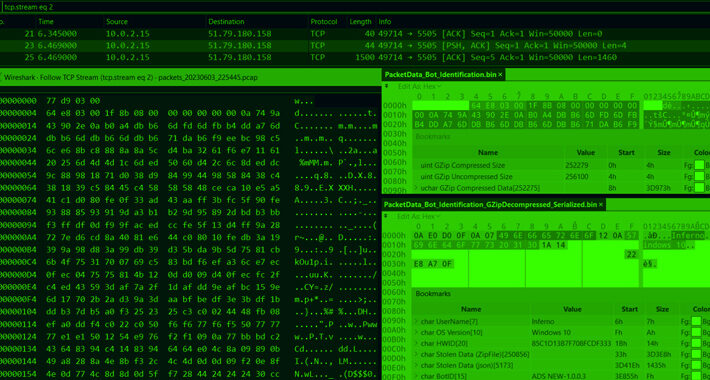
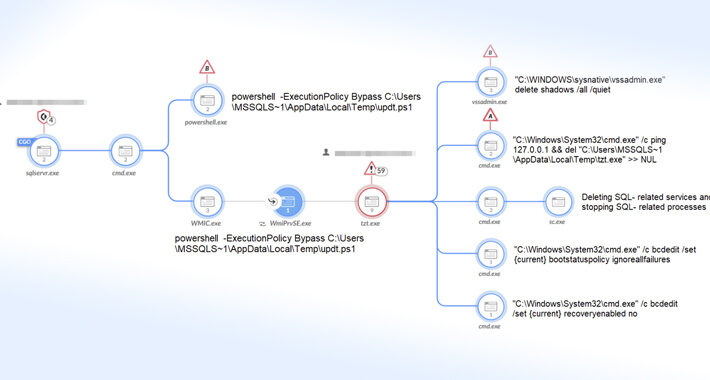
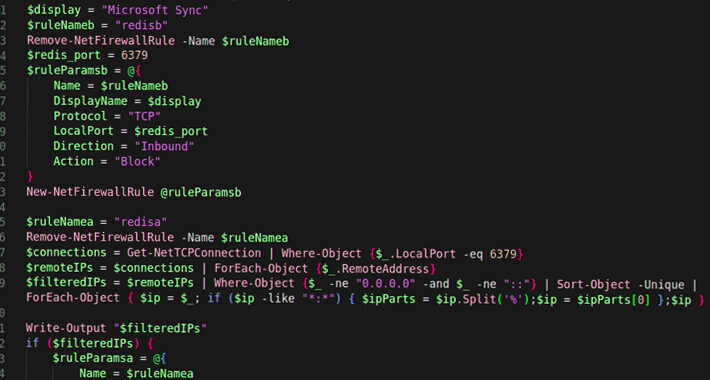
Source: thehackernews.com - Author: . Jul 20, 2023THNEndpoint Security / Data Safety Mallox ransomware activities in...
Source: thehackernews.com - Author: . Jul 20, 2023THNHardware Security / SysAdmin Two more security flaws have...
Source: thehackernews.com - Author: . Jul 20, 2023THNVulnerability / Software Security Multiple security flaws have been...
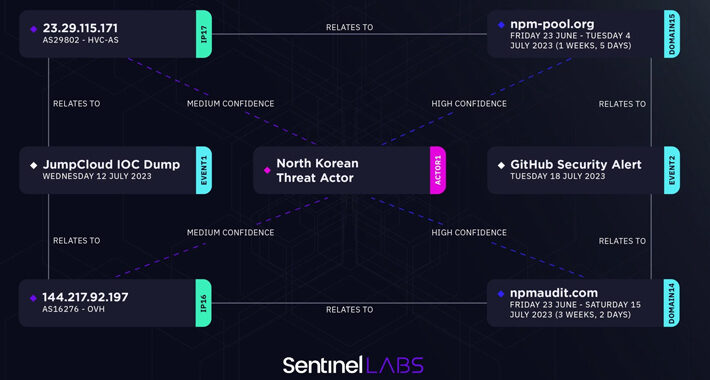
Source: thehackernews.com - Author: . Jul 20, 2023THNCyber Attack / Supply Chain An analysis of the...
Source: thehackernews.com - Author: . Jul 20, 2023The Hacker News If it seems like Remote Desktop...
Source: thehackernews.com - Author: . Jul 20, 2023THNCyber Attack / Malware The defense sector in Ukraine...
Source: thehackernews.com - Author: . Jul 20, 2023THNMalware / Cyber Threat Cybersecurity researchers have uncovered a...
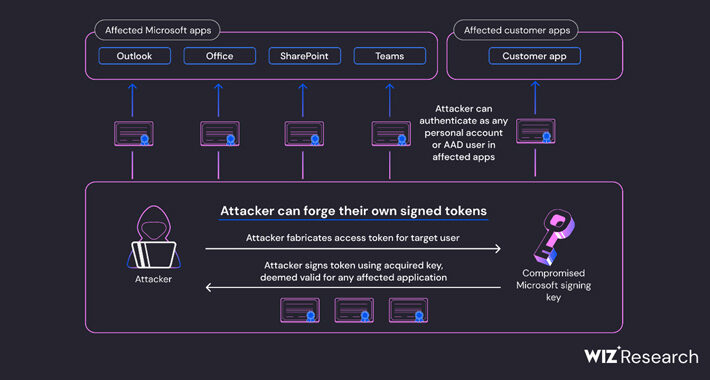
Source: thehackernews.com - Author: . Jul 20, 2023THNCloud Security / Cyber Espionage Microsoft on Wednesday announced...
Source: thehackernews.com - Author: . Jul 20, 2023THNSoftware Security / Vulnerability Adobe has released a fresh...
Source: thehackernews.com - Author: . Jul 13, 2023THNOT/ICS, SCADA Cybersecurity The U.S. Cybersecurity and Infrastructure Security...
U.S. Government Agencies’ Emails Compromised in China-Backed Cyber Attack – Source:thehackernews.com
Source: thehackernews.com - Author: . Jul 13, 2023THNCyber Espionage / Email Security An unnamed Federal Civilian...
Source: thehackernews.com - Author: . Jul 13, 2023THNNetwork Security / Vulnerability SonicWall on Wednesday urged customers...
Source: thehackernews.com - Author: . Attack surfaces are growing faster than security teams can keep up....
Source: thehackernews.com - Author: . Jul 19, 2023THNNetwork Security U.S. cybersecurity and intelligence agencies have released...
Source: thehackernews.com - Author: . Jul 19, 2023THNSpyware / Mobile Security The prolific China-linked nation-state actor...
Source: thehackernews.com - Author: . On April 5, 2023, the FBI and Dutch National Police announced...
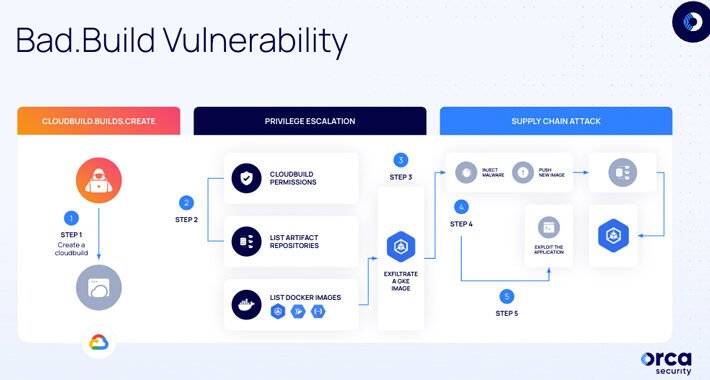
Source: thehackernews.com - Author: . Jul 19, 2023THNCloud Security / Vulnerability Cybersecurity researchers have uncovered a...
Source: thehackernews.com - Author: . Jul 19, 2023THNCyber Espionage / Spyware The U.S. government on Tuesday...