Source: thehackernews.com - Author: . Jul 29, 2023THNEmail Security / Vulnerability The U.S. Cybersecurity and Infrastructure...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Jul 29, 2023THNVulnerability / Enterprise Security Ivanti has disclosed yet another...
Source: thehackernews.com - Author: . Jul 28, 2023THNMalware / Cyber Threat The threat actors linked to...
Source: thehackernews.com - Author: . Jul 28, 2023THNCyber Attack / Malware An ongoing cyber attack campaign...
Source: thehackernews.com - Author: . As part of Checkmarx's mission to help organizations develop and deploy...
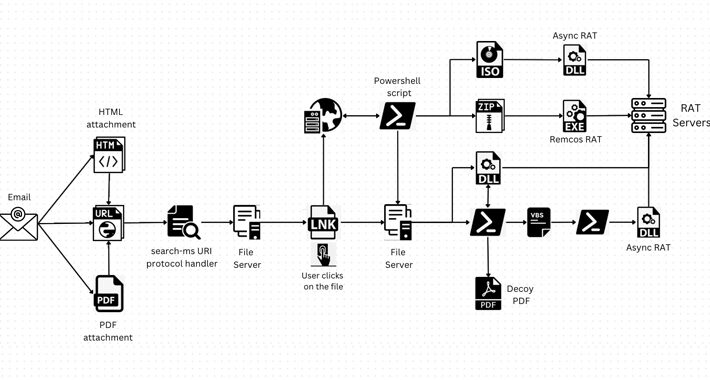
Source: thehackernews.com - Author: . Jul 28, 2023THNMalware / Cyber Threat A legitimate Windows search feature...
Source: thehackernews.com - Author: . Jul 28, 2023THNCyber Espionage / Malware The Russian nation-state actor known...
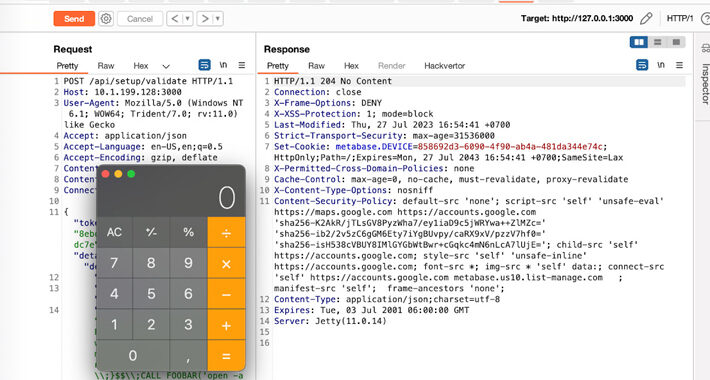
Source: thehackernews.com - Author: . Jul 28, 2023THNSoftware Security / Zero Day Users of Metabase, a...
Cybersecurity Agencies Warn Against IDOR Bugs Exploited for Data Breaches – Source:thehackernews.com
Source: thehackernews.com - Author: . Jul 28, 2023THNSoftware Security / Data Safety Cybersecurity agencies in Australia...
Source: thehackernews.com - Author: . Jul 27, 2023THNLinux / Endpoint Security Cybersecurity researchers have disclosed two...
Source: thehackernews.com - Author: . Jul 27, 2023THNMalvertising / Software Security A new malvertising campaign has...
Source: thehackernews.com - Author: . As cloud applications are built, tested and updated, they wind their...
Source: thehackernews.com - Author: . Jul 27, 2023THNServer Security / Cryptocurrency Misconfigured and poorly secured Apache...
Source: thehackernews.com - Author: . Jul 27, 2023THNCybersecurity / Infosec A city court in Moscow on...
Source: thehackernews.com - Author: . The U.S. Securities and Exchange Commission (SEC) on Wednesday approved new...
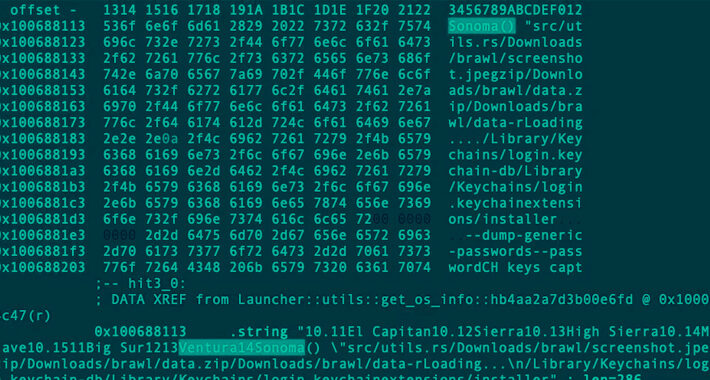
Source: thehackernews.com - Author: . Jul 26, 2023THNMalware / Cyber Threat A deeper analysis of a...
Source: thehackernews.com - Author: . A new study conducted by Uptycs has uncovered a stark increase...
Source: thehackernews.com - Author: . Jul 26, 2023THNOnline Security / Malware Tax-paying individuals in Mexico and...
Source: thehackernews.com - Author: . Jul 26, 2023THNCyber Crime / Artificial Intelligence Following the footsteps of...
Source: thehackernews.com - Author: . Jul 26, 2023THNCryptocurrency / Endpoint Security A new malware family called...
Source: thehackernews.com - Author: . Jul 26, 2023THNNetwork Security / Vulnerability A severe privilege escalation issue...
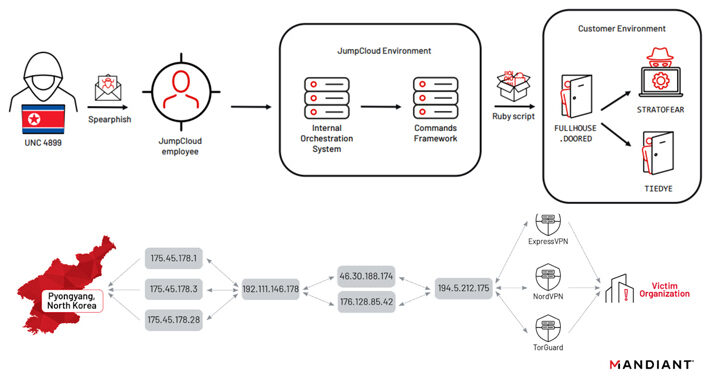
Source: thehackernews.com - Author: . North Korean nation-state actors affiliated with the Reconnaissance General Bureau (RGB)...
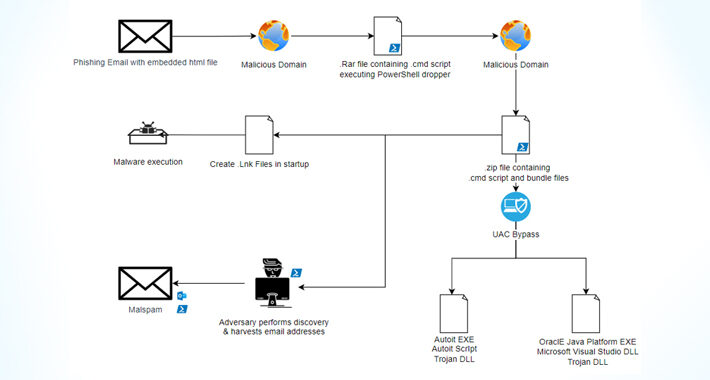
Casbaneiro Banking Malware Goes Under the Radar with UAC Bypass Technique – Source:thehackernews.com
Source: thehackernews.com - Author: . Jul 25, 2023THNMalware / Cyber Threat The financially motivated threat actors...
Source: thehackernews.com - Author: . Jul 25, 2023The Hacker NewsEndpoint Security / macOS As the number...
Source: thehackernews.com - Author: . Jul 25, 2023THNNetwork Security / Vulnerability A set of five security...
Source: thehackernews.com - Author: . Jul 25, 2023The Hacker NewsCyber Threat Intelligence How do you overcome...
Source: thehackernews.com - Author: . Jul 25, 2023THNHardware Security / Encryption A new security vulnerability has...
Source: thehackernews.com - Author: . Jul 25, 2023THNServer Security / Zero Day Atlassian has released updates...
Source: thehackernews.com - Author: . Jul 25, 2023THNEnterprise Security / Zero Day Ivanti is warning users...
Source: thehackernews.com - Author: . Jul 25, 2023THNEndpoint Security / Zero Day Apple has rolled out...