Source: thehackernews.com - Author: . Sep 13, 2023THNRansomware / Malware A new ransomware family called 3AM...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . There is a new battlefield. It is global and challenging to...
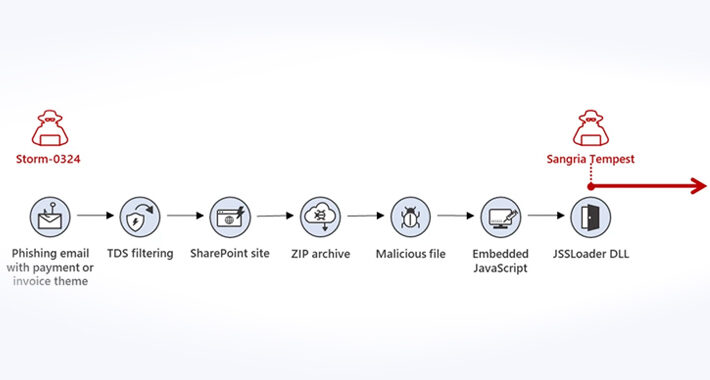
Source: thehackernews.com - Author: . Microsoft is warning of a new phishing campaign undertaken by an...
Source: thehackernews.com - Author: . Sep 13, 2023THNEndpoint Security / Zero Day Microsoft has released software...
Update Adobe Acrobat and Reader to Patch Actively Exploited Vulnerability – Source:thehackernews.com
Source: thehackernews.com - Author: . Sep 13, 2023THNVulnerability / Zero Day Adobe's Patch Tuesday update for...
Source: thehackernews.com - Author: . Sep 13, 2023THNVulnerability / Browser Security Mozilla on Tuesday released security...
Source: thehackernews.com - Author: . Sep 12, 2023THNSoftware Security / Vulnerability A new vulnerability disclosed in...
Source: thehackernews.com - Author: . SaaS applications are the backbone of modern businesses, constituting a staggering...
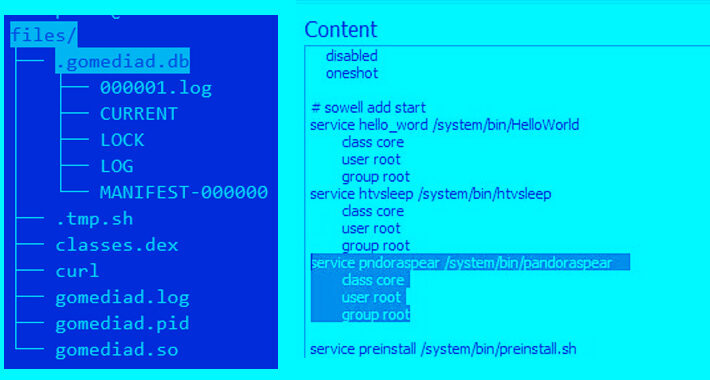
Source: thehackernews.com - Author: . Sep 12, 2023THNCritical Infrastructure Security A threat actor called Redfly has...
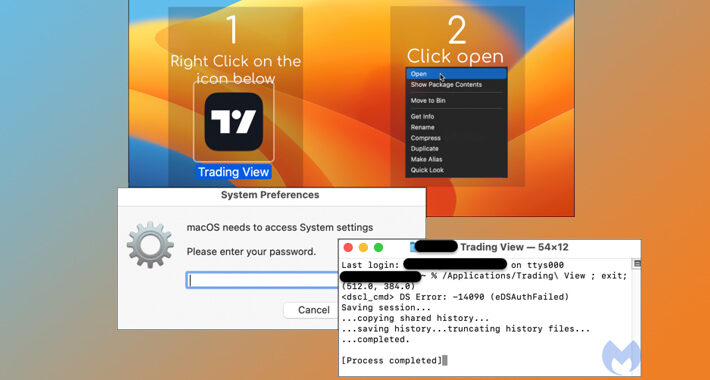
Source: thehackernews.com - Author: . Sep 12, 2023THNEndpoint Security / Malware A sophisticated phishing campaign is...
Source: thehackernews.com - Author: . Sep 12, 2023THNEndpoint Security / Data Security A new information stealer...
Source: thehackernews.com - Author: . Sep 12, 2023THNBrowser Security / Zero Day Google on Monday rolled...
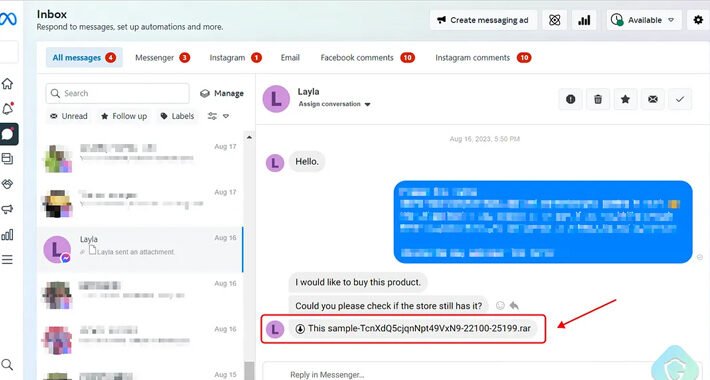
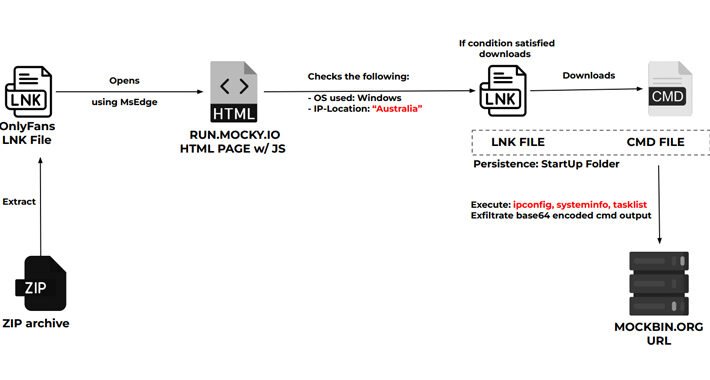
Source: thehackernews.com - Author: . Sep 11, 2023THNMalware / Social Media A new phishing attack is...
Source: thehackernews.com - Author: . Sep 11, 2023THNCyber Espionage / Malware The Iranian threat actor known...
Source: thehackernews.com - Author: . With the growing reliance on web applications and digital platforms, the...
Source: thehackernews.com - Author: . Sep 11, 2023THNPrivacy / Online Security Google has officially begun its...
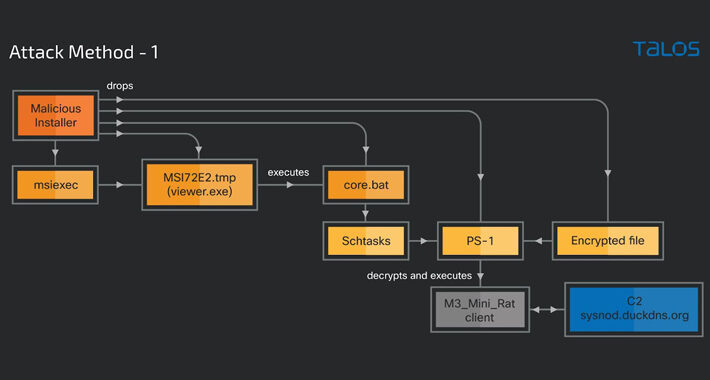
Source: thehackernews.com - Author: . Sep 11, 2023THNEndpoint Security / Malware A new cyber attack campaign...
Source: thehackernews.com - Author: . Sep 11, 2023THNCyber Crime / Malware A new malware loader called...
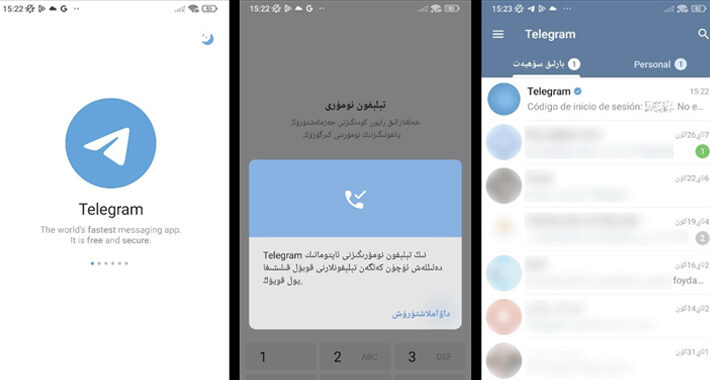
Source: thehackernews.com - Author: . Sep 09, 2023THNMobile Security / Spyware Spyware masquerading as modified versions...
Source: thehackernews.com - Author: . Sep 09, 2023THNMalware / Hacking A legitimate Windows tool used for...
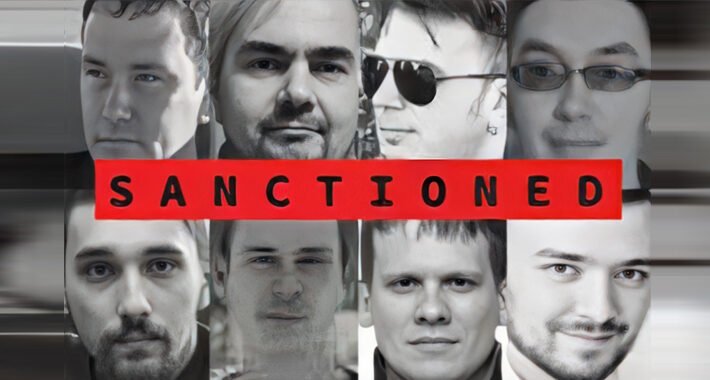
Source: thehackernews.com - Author: . Sep 08, 2023THNCybercrime / Malware The U.K. and U.S. governments on...
Source: thehackernews.com - Author: . Cisco has released security fixes to address multiple security flaws, including...
Source: thehackernews.com - Author: . Microsoft Internet Information Services (IIS) is a web server software package...
Source: thehackernews.com - Author: . Threat actors associated with North Korea are continuing to target the...
Source: thehackernews.com - Author: . Sep 08, 2023THNEndpoint Security / Exploit The U.S. Cybersecurity and Infrastructure...
Source: thehackernews.com - Author: . Sep 08, 2023THNSpyware / Vulnerability Apple on Thursday released emergency security...
Source: thehackernews.com - Author: . Sep 07, 2023THNMalvertising / Endpoint Security A new malvertising campaign has...
Source: thehackernews.com - Author: . By the end of 2024, the number of MSPs and MSSPs...
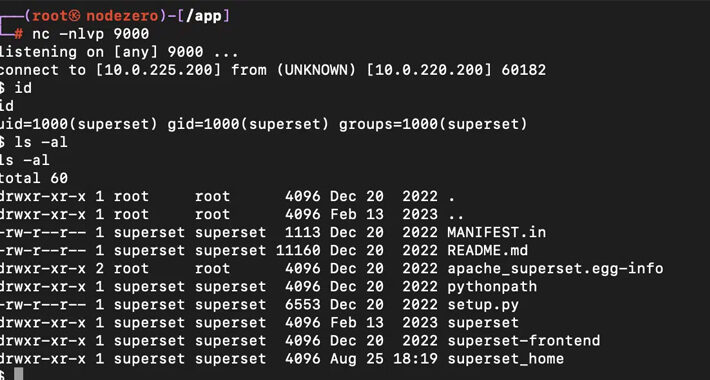
Source: thehackernews.com - Author: . Sep 07, 2023THNServer Security / Vulnerability Patches have been released to...
Source: thehackernews.com - Author: . Sep 07, 2023THNBotnet / Cyber Threat A Mirai botnet variant called...