Source: thehackernews.com - Author: . Sep 26, 2023THNEndpoint Security / Password Microsoft is officially rolling out...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Cybersecurity experts have shed light on a new cybercrime group known...
Source: thehackernews.com - Author: . SOC 2, ISO, HIPAA, Cyber Essentials – all the security frameworks...
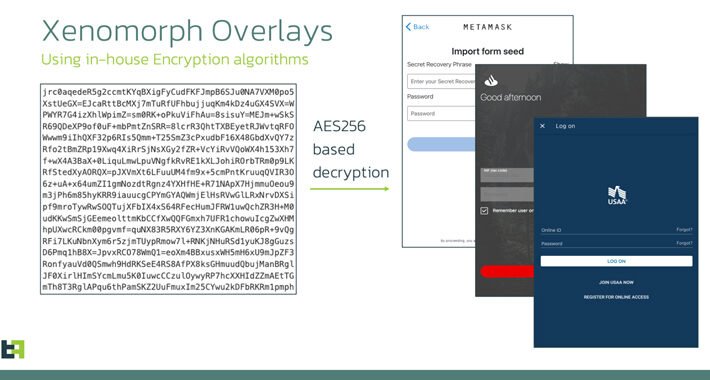
Source: thehackernews.com - Author: . Sep 26, 2023THNMobile Security / Malware An updated version of an...
Source: thehackernews.com - Author: . How To Use This Report Enhance situational awareness of techniques used...
Source: thehackernews.com - Author: . Sep 26, 2023THNCyber Espionage / Malware A "multi-year" Chinese state-sponsored cyber...
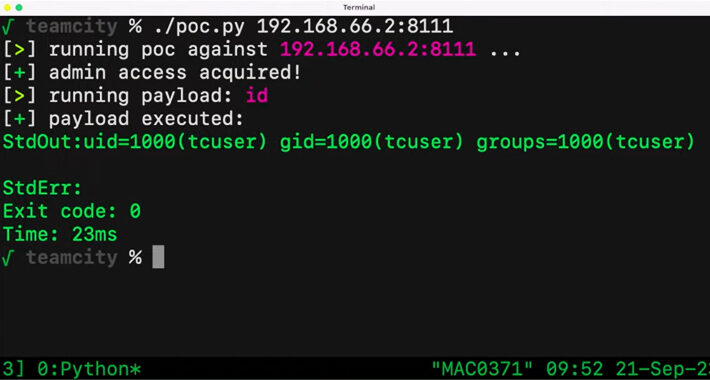
Source: thehackernews.com - Author: . Sep 26, 2023THNVulnerability / Source Code A critical security vulnerability in...
Ukrainian Military Targeted in Phishing Campaign Leveraging Drone Manuals – Source:thehackernews.com
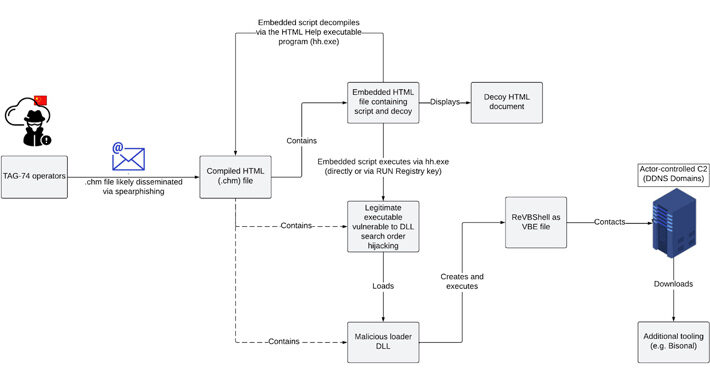
Source: thehackernews.com - Author: . Sep 25, 2023THNCyber Attack / Phishing Ukrainian military entities are the...
Source: thehackernews.com - Author: . Sep 25, 2023The Hacker NewsPassword Security / Cybersecurity Weak password policies...
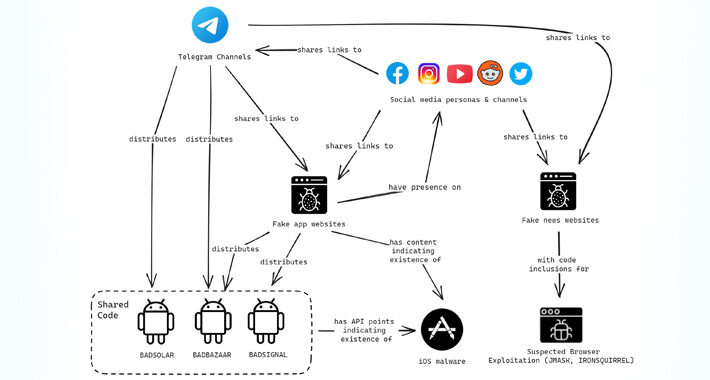
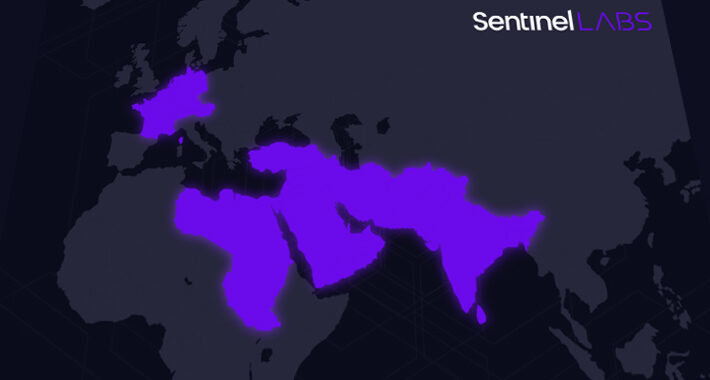
Source: thehackernews.com - Author: . Sep 25, 2023THNSpyware / Cyber Espionage Tibetan, Uyghur, and Taiwanese individuals...
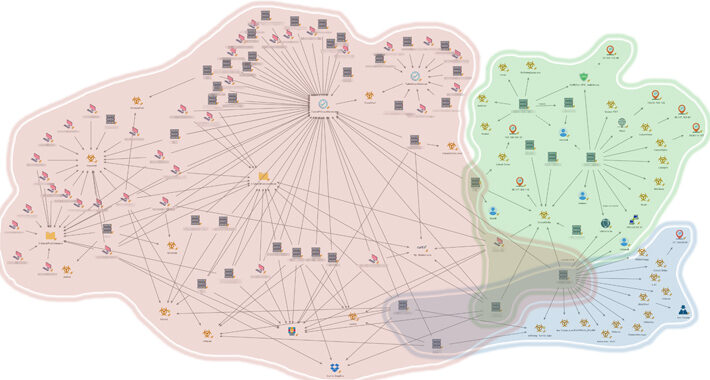
Source: thehackernews.com - Author: . An unnamed Southeast Asian government has been targeted by multiple China-nexus...
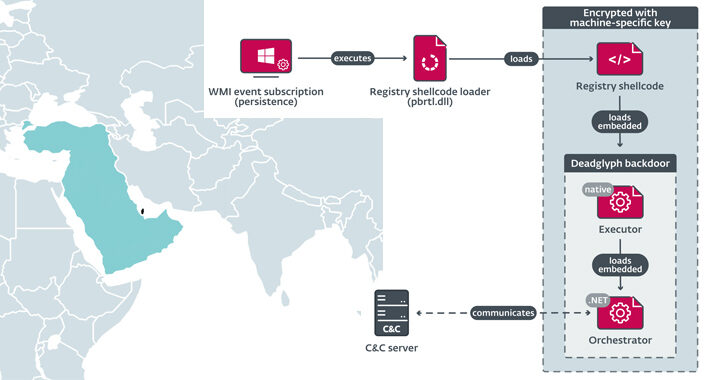
Source: thehackernews.com - Author: . Cybersecurity researchers have discovered a previously undocumented advanced backdoor dubbed Deadglyph...
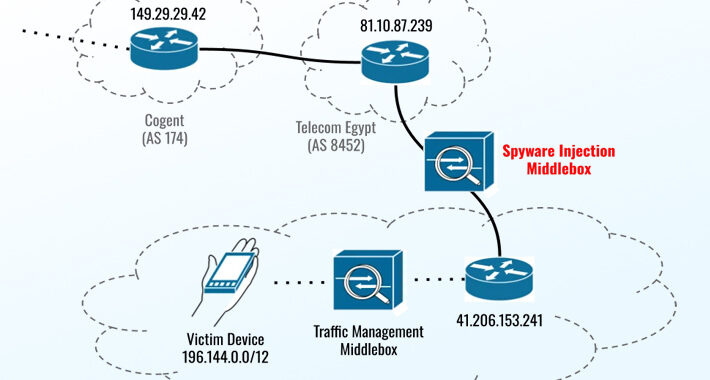
Source: thehackernews.com - Author: . The three zero-day flaws addressed by Apple on September 21, 2023,...
Source: thehackernews.com - Author: . Sep 22, 2023THNMalware / Cyber Threat An active malware campaign targeting...
Source: thehackernews.com - Author: . Thorough, independent tests are a vital resource for analyzing provider's capabilities...
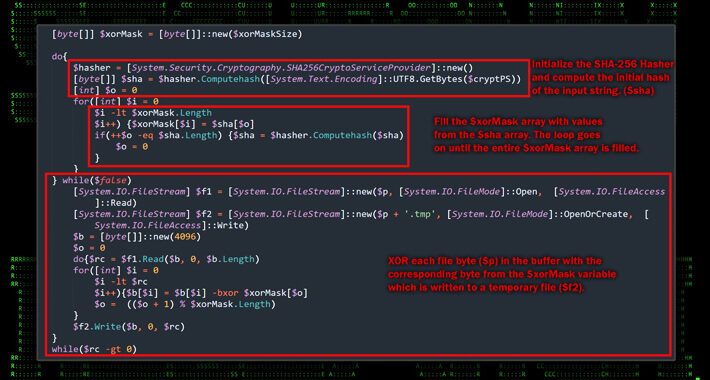
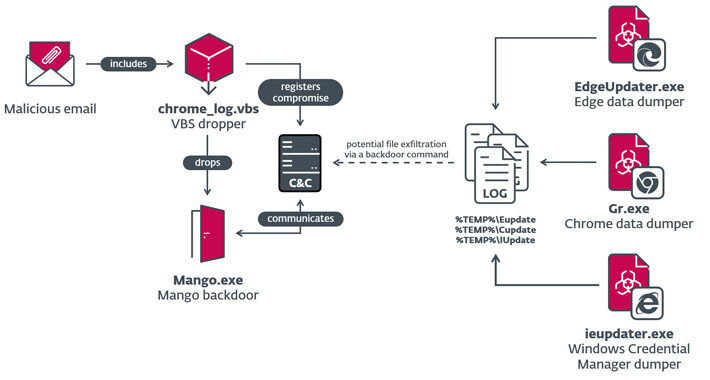
Source: thehackernews.com - Author: . Sep 22, 2023THNCyber Attack / Malware Israeli organizations were targeted as...
Source: thehackernews.com - Author: . Sep 22, 2023THNServer Security / Vulnerability Atlassian and the Internet Systems...
Source: thehackernews.com - Author: . Sep 22, 2023THNZero Day / Vulnerability Apple has released yet another...
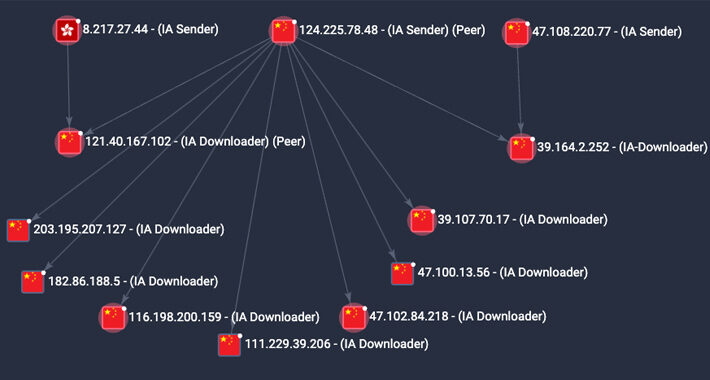
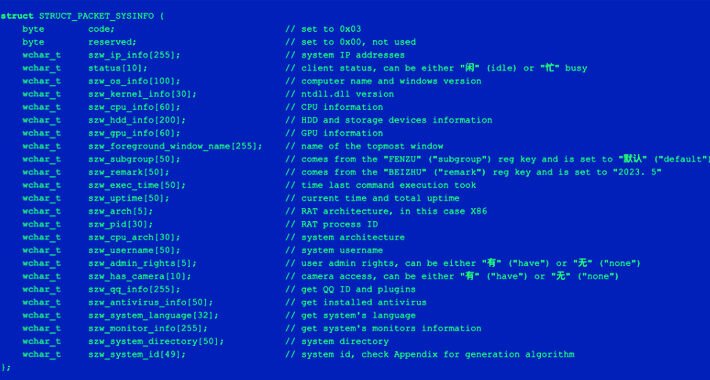
Source: thehackernews.com - Author: . Sep 21, 2023THNTelecom Security / Cyber Attack A previously undocumented threat...
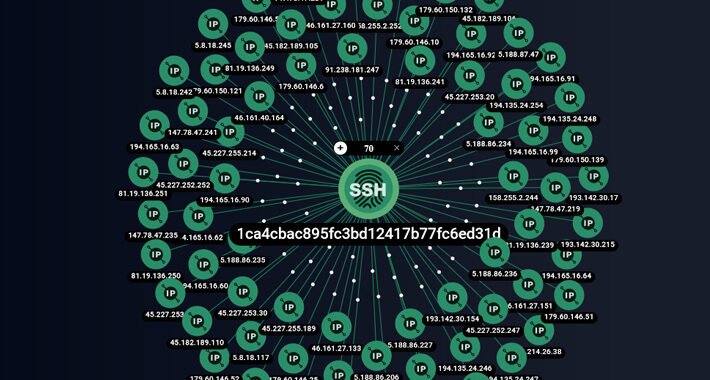
Source: thehackernews.com - Author: . Sep 21, 2023THNBotnet / Cyber Threat The peer-to-peer (P2) worm known...
Source: thehackernews.com - Author: . Sep 21, 2023The Hacker NewsSaaS Security / App Security Security teams...
Source: thehackernews.com - Author: . Sep 21, 2023THNCyber Espionage / Spyware China's Ministry of State Security...
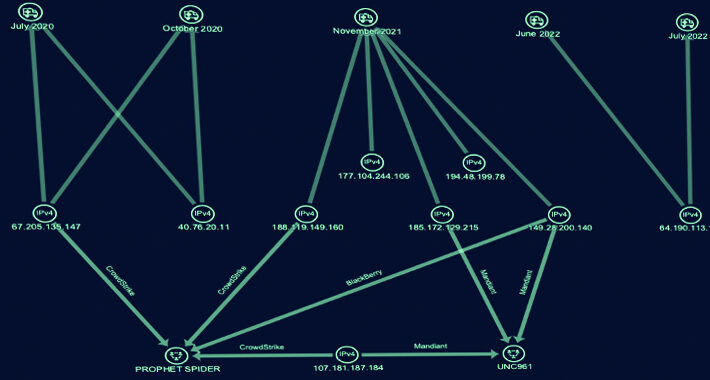
Source: thehackernews.com - Author: . Sep 21, 2023THNCyber Threat / Ransomware A financially motivated threat actor...
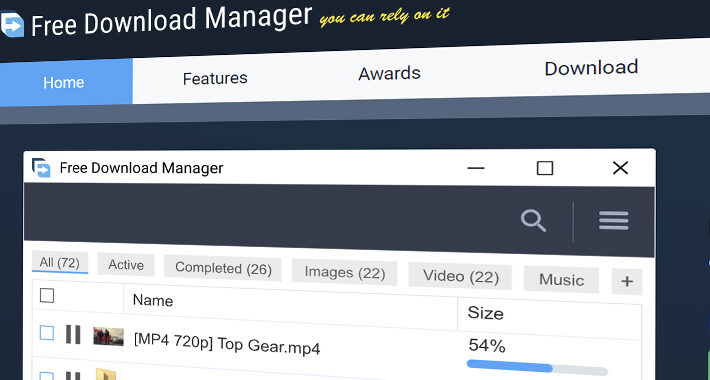
Source: thehackernews.com - Author: . Sep 21, 2023THNSupply Chain / Malware The maintainers of Free Download...
Source: thehackernews.com - Author: . Sep 21, 2023THNVulnerability / Exploit A malicious actor released a fake...
Source: thehackernews.com - Author: . Sep 20, 2023THNCyber Crime / Dark Web Finnish law enforcement authorities...
Source: thehackernews.com - Author: . Sep 20, 2023THNNetwork Security / Vulnerability Multiple security flaws have been...
Source: thehackernews.com - Author: . Sep 20, 2023The Hacker NewsWeb Application Security Well, you shouldn't. It...
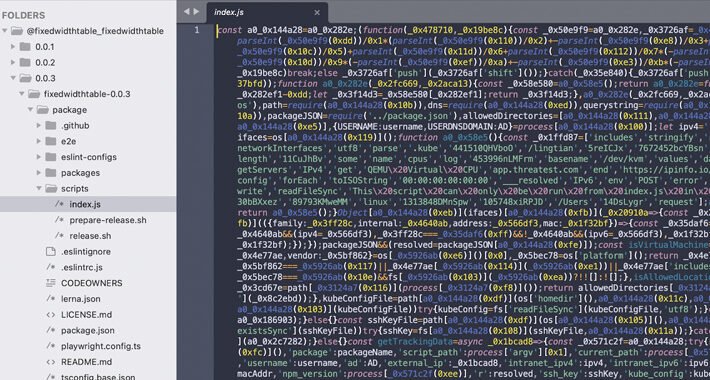
Source: thehackernews.com - Author: . Sep 20, 2023THNKubernetes / Supply Chain Attack Cybersecurity researchers have discovered...
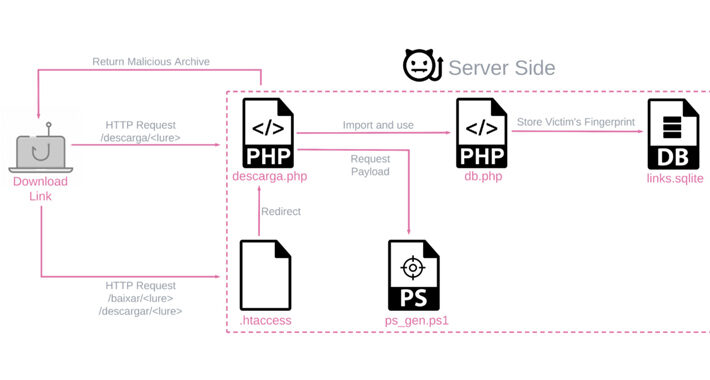
Source: thehackernews.com - Author: . Sep 20, 2023THNMalware Attack / Cyber Threat Chinese-language speakers have been...