The document outlines the critical role of a Chief Information Security Officer (CISO) in navigating the...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
SentinelOne
In this special year-end edition of the WatchTower Digest, we discuss the threats we observedand investigated...
Overview In this guide, we’ll cover everything you need to know to understand the strengths and...
90-Days-A-CISOs-Journey-to-Impact-1Descarga
OverviewIn this guide, we’ll cover everything you need to know to understand the strengths and weaknesses...
Here’s a quick breakdown of the most impactful supply chain attacks over the last decade or...
Drive-a-Cybersecurity-Centric-CultureDescarga
Beware-These-6-Common-Cybersecurity-Myths-PDFDownload
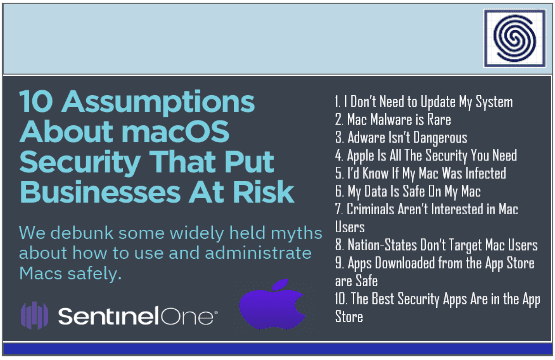
We debunk some widely held myths about how to use and administrate Macs safely. I Don’t...