Source: www.securityweek.com - Author: Eduard Kovacs Google announced on Wednesday that users can now sign into...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
securityweek.com
Source: www.securityweek.com - Author: Ionut Arghire Google this week announced the release of Chrome 113 to...
Source: www.securityweek.com - Author: AFP Meta on Wednesday warned that hackers are using the promise of...
Source: www.securityweek.com - Author: Kevin Townsend Open banking was born in the EU, flourished in the...
Source: www.securityweek.com - Author: Ionut Arghire A subgroup of the Chinese state-sponsored threat actor known as...
Source: www.securityweek.com - Author: Eduard Kovacs A widely used BGP implementation is affected by three vulnerabilities...
Source: www.securityweek.com - Author: Associated Press Law enforcement agencies around the world seized an online marketplace...
IT Services Firm Bitmarck Takes Systems Offline Following Cyberattack – Source: www.securityweek.com
Source: www.securityweek.com - Author: Ionut Arghire German IT services provider Bitmarck on Monday announced that it...
Source: www.securityweek.com - Author: Ionut Arghire US wireless carrier T-Mobile is informing some customers that their...
Source: www.securityweek.com - Author: Ionut Arghire The US Cybersecurity and Infrastructure Security Agency (CISA) on Monday...
Source: www.securityweek.com - Author: Eduard Kovacs Apple has released its first Rapid Security Response update, but...
Source: www.securityweek.com - Author: Eduard Kovacs Thirty-eight cybersecurity-related merger and acquisition (M&A) deals were announced in...
Source: www.securityweek.com - Author: Eduard Kovacs The US Cybersecurity and Infrastructure Security Agency (CISA) has added...
Source: www.securityweek.com - Author: Ionut Arghire Fortinet warns of a massive spike in exploitation attempts targeting...
Source: www.securityweek.com - Author: Eduard Kovacs A ransomware group has leaked files showing the extent of...
Source: www.securityweek.com - Author: Mike Lennon SecurityWeek’s ICS Cybersecurity Conference is back in Atlanta October 23-26, 2023. Registration...
Source: www.securityweek.com - Author: Ionut Arghire Russian cybercrime group TA505 has been observed using new hVNC...
Source: www.securityweek.com - Author: Matt Wilson Endpoint detection and response (EDR) has demonstrated clear value in...
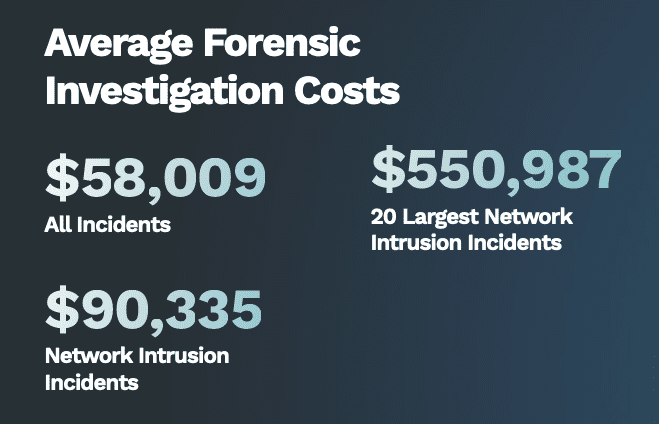
Source: www.securityweek.com - Author: Eduard Kovacs Lawsuits filed against companies that have suffered a data breach...
Source: www.securityweek.com - Author: Ionut Arghire The US Cybersecurity and Infrastructure Security Agency (CISA) has announced...
Source: www.securityweek.com - Author: Ionut Arghire Mobile security firm Lookout has analyzed a piece of Android...
Source: www.securityweek.com - Author: Ionut Arghire Taiwanese network equipment manufacturer Zyxel this week announced patches for...
Source: www.securityweek.com - Author: Ionut Arghire Cybersecurity firm Aadya Security this week announced that it has...
Source: www.securityweek.com - Author: Ionut Arghire A Chinese APT actor tracked as Evasive Panda has been...
Source: www.securityweek.com - Author: Eduard Kovacs A new piece of macOS malware named ‘Atomic macOS Stealer’,...
Source: www.securityweek.com - Author: Ryan Naraine News Analysis: If the winner of the RSA Innovation Sandbox...
Source: www.securityweek.com - Author: Ionut Arghire Google this week announced that it has obtained a court...
Source: www.securityweek.com - Author: Associated Press TikTok, Twitter, Facebook, Google, and Amazon are facing rising pressure...
Source: www.securityweek.com - Author: Ionut Arghire A Cl0p ransomware operator affiliated with the FIN11 and TA505...
Source: www.securityweek.com - Author: Eduard Kovacs Hundreds of companies are showcasing their products and services this...